Cutting-edge technology and groundbreaking new innovations are what most SaaS companies work towards to draw more customers. But what is not given enough credit for not only drawing customers but retaining them is good old-fashioned trustworthiness and reliability.
This is where demonstrating a robust security posture plays a crucial role. In this day and age where data breaches and cyber attacks repel customers, enforcing strong security practices will project your company as an organization worthy of doing business with.
In this blog, we will discuss the importance of communicating your organization’s security posture with customers and stakeholders and guide you on best practices to demonstrate trust to various parties.
What does security posture mean?
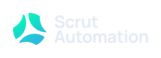
Security posture refers to an organization’s overall approach to managing and safeguarding its information assets, technology infrastructure, and sensitive data. It encompasses a comprehensive set of strategies, policies, and practices designed to protect against various security threats and vulnerabilities.
A robust security posture is crucial for ensuring the confidentiality, integrity, and availability of information, as well as maintaining the trust of stakeholders and clients.
Who needs to be informed about your security posture?
The communication of security posture is a multifaceted process that requires tailoring the message to different stakeholders within and outside the organization. The primary target audience includes:
Internal stakeholders
- Employees: Educating and informing employees about the organization’s security posture is essential for fostering a culture of compliance and cybersecurity awareness. This ensures that individuals understand their roles in safeguarding sensitive information and following security protocols.
- Management and leadership: Executives and decision-makers need a comprehensive understanding of the security posture to make informed strategic decisions. Clear communication with leadership helps align security initiatives with overall business objectives.
External stakeholders
- Customers: Building trust with clients is critical for maintaining business relationships. Communicating the security measures in place assures clients that their data is handled with the utmost care and security.
- Partners and suppliers: Collaborative efforts often involve sharing sensitive information. Communicating security posture to partners and suppliers establishes a baseline of expectations and fosters a secure collaborative environment.
- Regulatory bodies: Compliance with industry regulations is imperative. Clearly articulating the security posture aids in demonstrating adherence to regulatory requirements and standards.
Why is it important to communicate your company’s security posture?
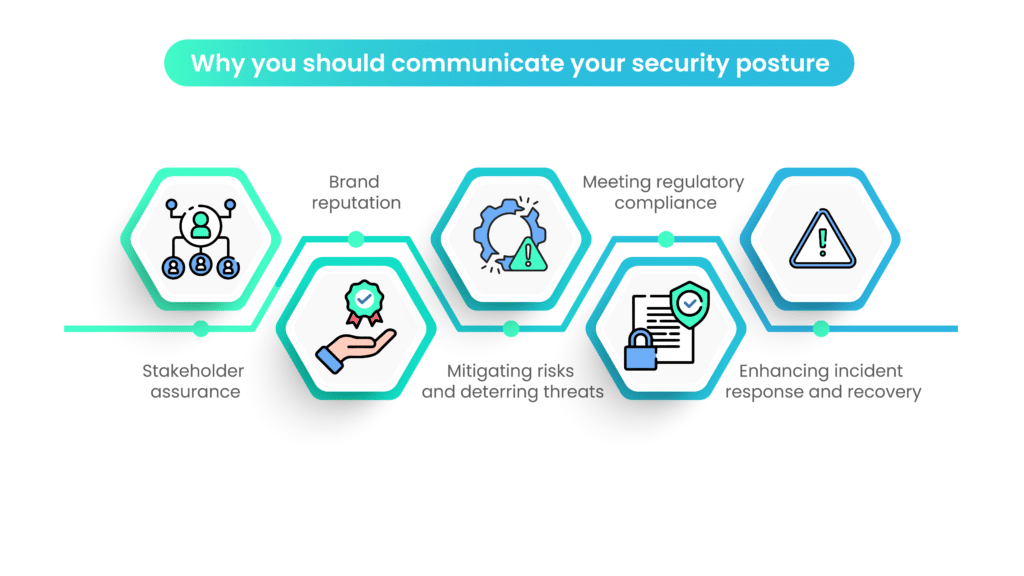
In an era dominated by digital connectivity and an ever-evolving threat landscape, the importance of transparently communicating your company’s security posture cannot be overstated. This section explores the critical reasons why organizations should actively articulate and share details about their security stance.
Stakeholder assurance
Communicating your company’s security posture is a proactive measure to assure stakeholders—both internal and external—that the organization takes cybersecurity seriously. This assurance is important for building and maintaining trust with employees, clients, partners, and investors.
Brand reputation
In an age where data breaches and cyber incidents are headline news, a strong security posture contributes significantly to a positive brand image. Openly communicating security measures signals a commitment to safeguarding sensitive information, enhancing the organization’s credibility in the eyes of customers and the public.
Mitigating risk and deterring threats
Publicizing your security measures acts as a deterrent to potential cyber threats. When attackers perceive a robust security posture, they are less likely to target the organization, opting for easier and less fortified targets. This proactive deterrence can be a crucial element in the overall cybersecurity strategy.
By clearly communicating security protocols and practices, your company also equips stakeholders with the knowledge to identify and mitigate potential risks. This empowers employees to make informed decisions that contribute to the overall security resilience of the organization.
Meeting regulatory compliance
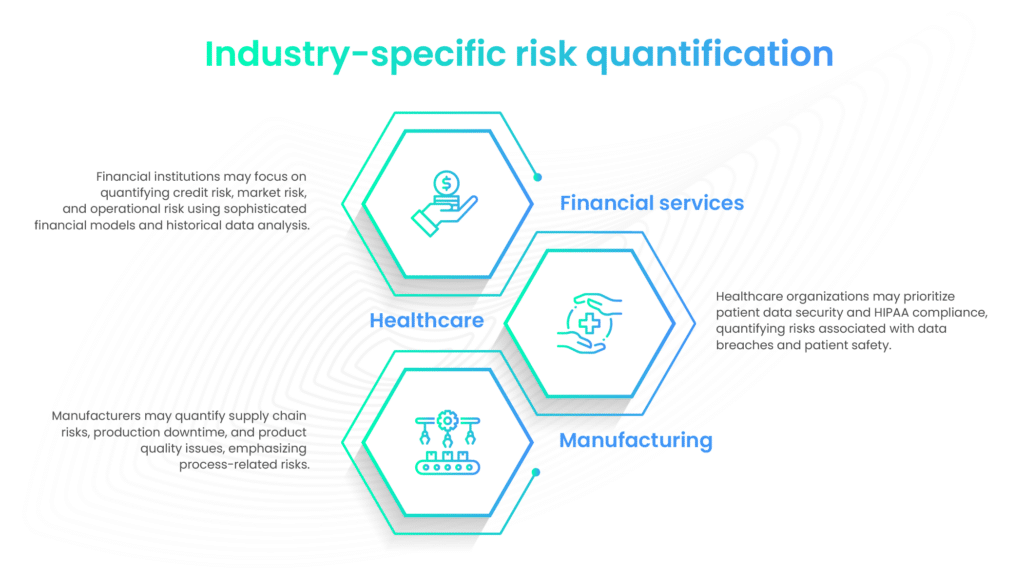
Numerous industries are subject to stringent data protection regulations. For instance, the healthcare industry has to adhere to HIPAA (Health Insurance Portability and Accountability Act) guidelines.
Effectively communicating your company’s security posture is essential for demonstrating compliance with these regulations. This not only helps avoid legal ramifications but also showcases a commitment to ethical business practices.
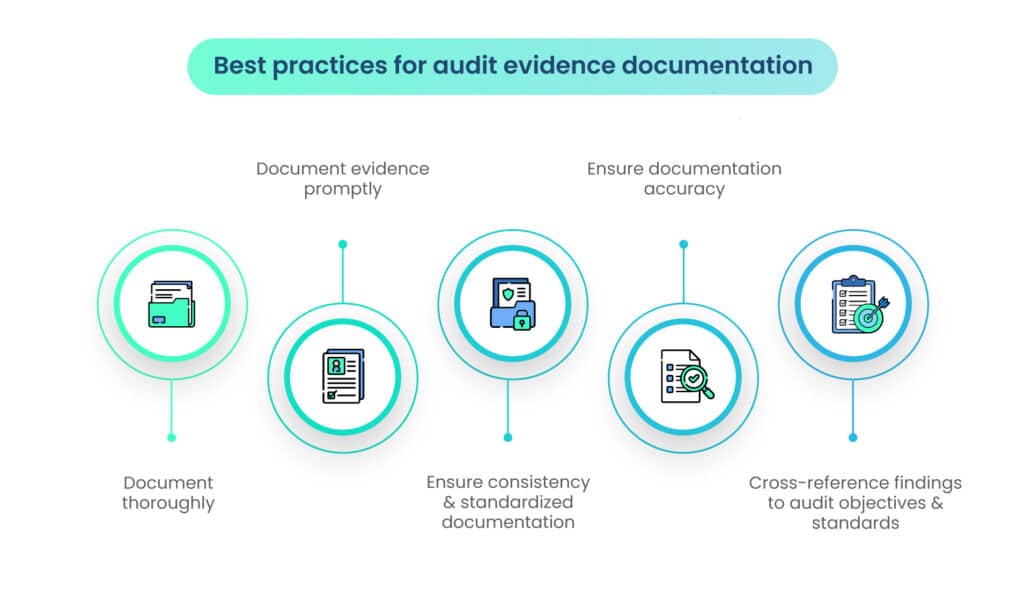
Regular communication of security practices also aids in creating a compliance culture of continuous improvement and readiness for audits. When regulatory bodies or external auditors assess your company’s adherence to standards, transparent communication facilitates a smoother and more favorable audit process.
Enhancing incident response and recovery
In the event of a security incident, clear communication channels established beforehand enable a more rapid and coordinated response. Employees, clients, and other stakeholders can be promptly informed of the situation, mitigating potential damage and demonstrating the organization’s commitment to transparency.
Should a security incident occur, a history of transparent communication about security posture can contribute to a quicker recovery of reputation. Stakeholders are more likely to trust an organization that openly acknowledges and addresses security challenges.
This was not the case in Equifax’s 2017 data breach. The company faced criticism for its delayed public disclosure of the breach, which was discovered in July 2017 but only announced in September 2017.
Aligning security with business objectives
Transparent communication of security posture ensures that cybersecurity is integrated into the broader business strategy. This alignment helps leaders make informed decisions that balance security requirements with organizational goals, promoting a holistic approach to risk management.
Shareholders and investors increasingly consider cybersecurity a critical aspect of due diligence. Communicating a strong security posture enhances investor confidence, contributing to a positive perception of the organization’s long-term viability.
The growing need for a defensible security program
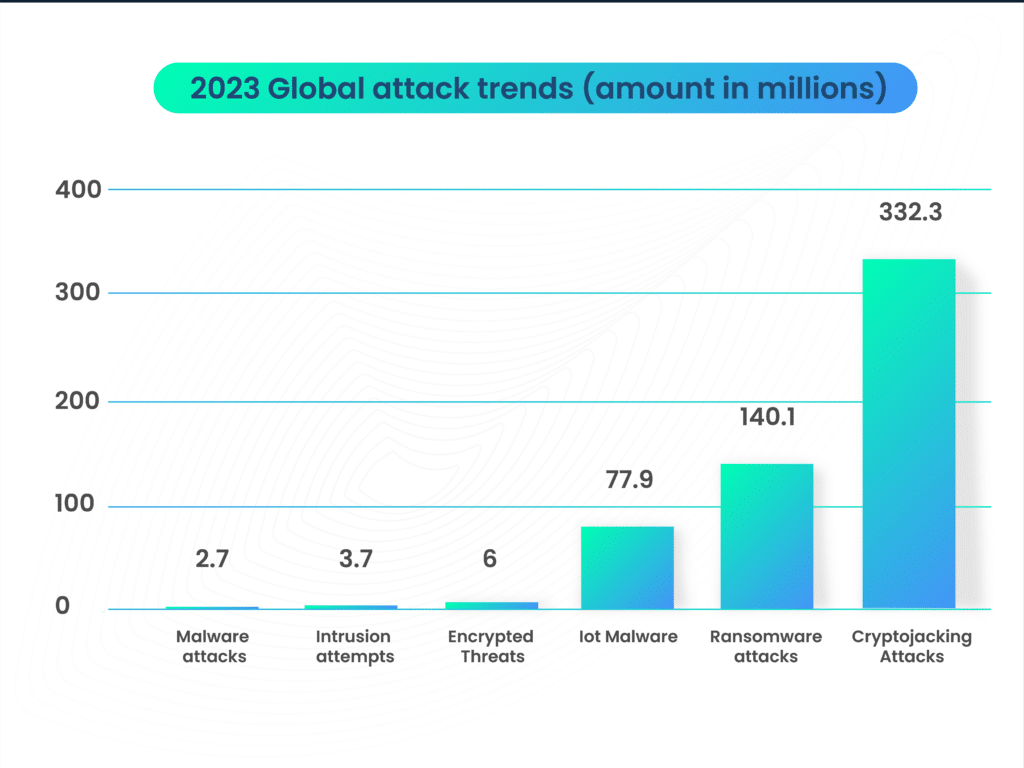
According to IBM’s Cost of a Data Breach 2023 Report, the worldwide average cost of a data breach in 2023 reached USD 4.45 million, marking a 15% escalation over the preceding three years.
Simultaneously, the global regulatory landscape is tightening, mandating the appointment of a singular individual accountable for an organization’s security program.
The Digital Operational Resilience Act (DORA) in the EU goes a step further, introducing provisions for potential criminal prosecution of the person in charge.
The Chief Resilience Officer must heed the insights derived from compliance peers and cultivate a culture of compliance to these requirements within their organizational framework.
The responsibilities regarding reporting and information sharing are expanding, with evolving guidance and legislation incorporating additional clauses for incident management and breach notification.
Professionals in risk and compliance can no longer afford to keep such information confidential. Responding to incidents that disrupt business operations or compromise consumer safety has become more critical than ever, and regulators are emphasizing the heightened importance of organizational trust.
The United States Securities & Exchange Commission (SEC) has adopted measures to hold executives accountable for misconduct during their tenure.
By utilizing existing provisions in the Sarbanes-Oxley Act, the SEC has indicated its intent to reclaim specific compensation bonuses and stock sale profits from Chief Executive Officers and Chief Financial Officers when companies need to reissue an accounting statement due to misconduct.
Notably, the Act is not applicable if the executives were directly involved in the misconduct leading to the restatement; rather, it applies when they presided over a company where the misconduct occurred.
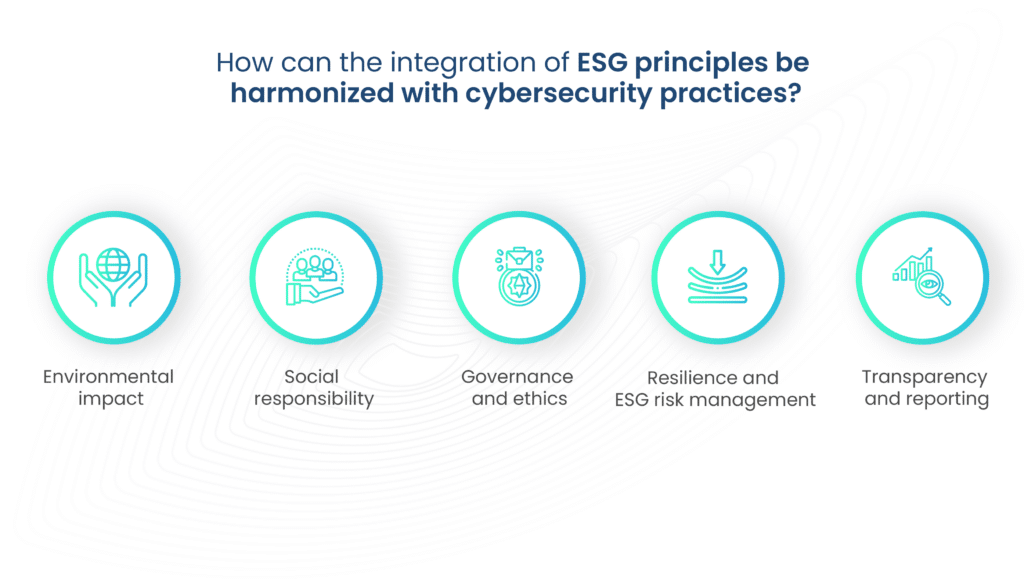
As reporting obligations to the SEC expand to encompass cybersecurity and ESG (environmental, social, and governance), executives must acknowledge that it is now more crucial than ever for their organization’s success to have effective risk mitigation and preventive monitoring controls across these domains.
This is vital to ensure that third parties provide accurate information substantiating statements made in SEC reports.
Defense costs associated with an SEC investigation can surpass $1 million, necessary for defending individuals, directors, and officers – and indemnification insurance may not invariably cover these costs.
All these factors contribute to the growing need for organizations to enforce a strong security program. Cultivating a culture of compliance, proactive risk mitigation and vigilant monitoring across various domains is not just a mandate for resilience but a strategic imperative for sustained success in an ever-changing digital environment.
Conducting a security posture assessment
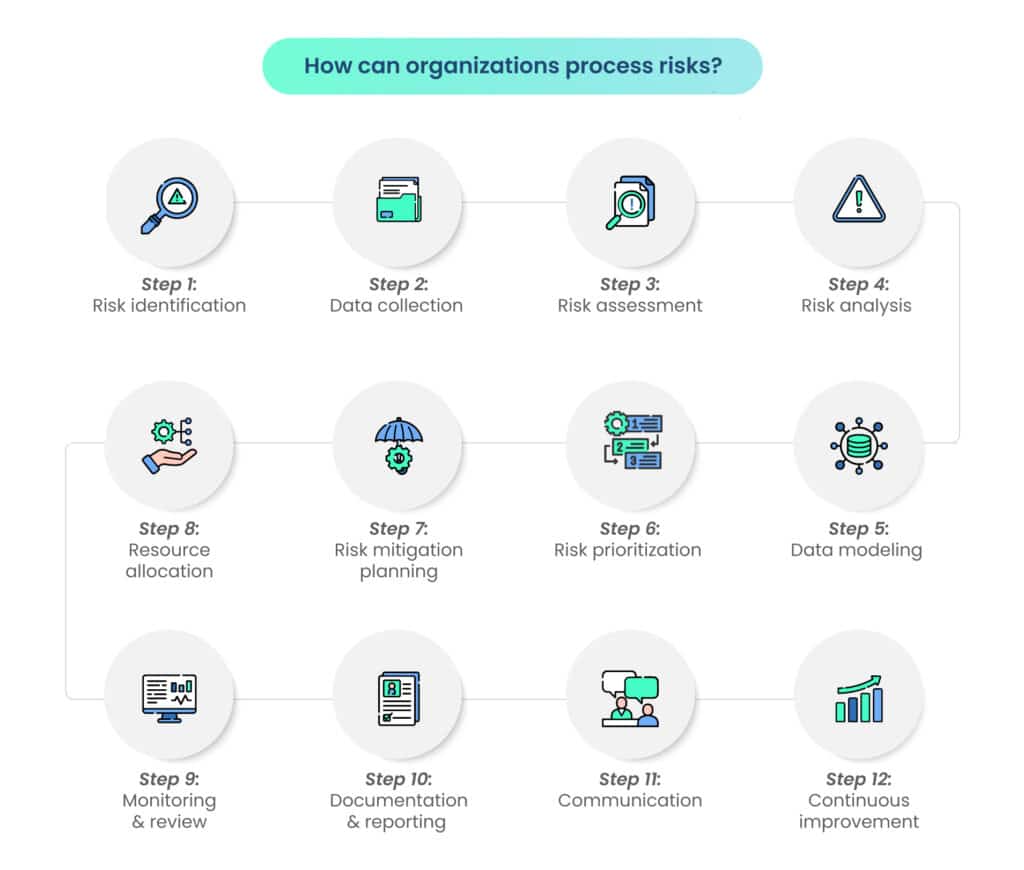
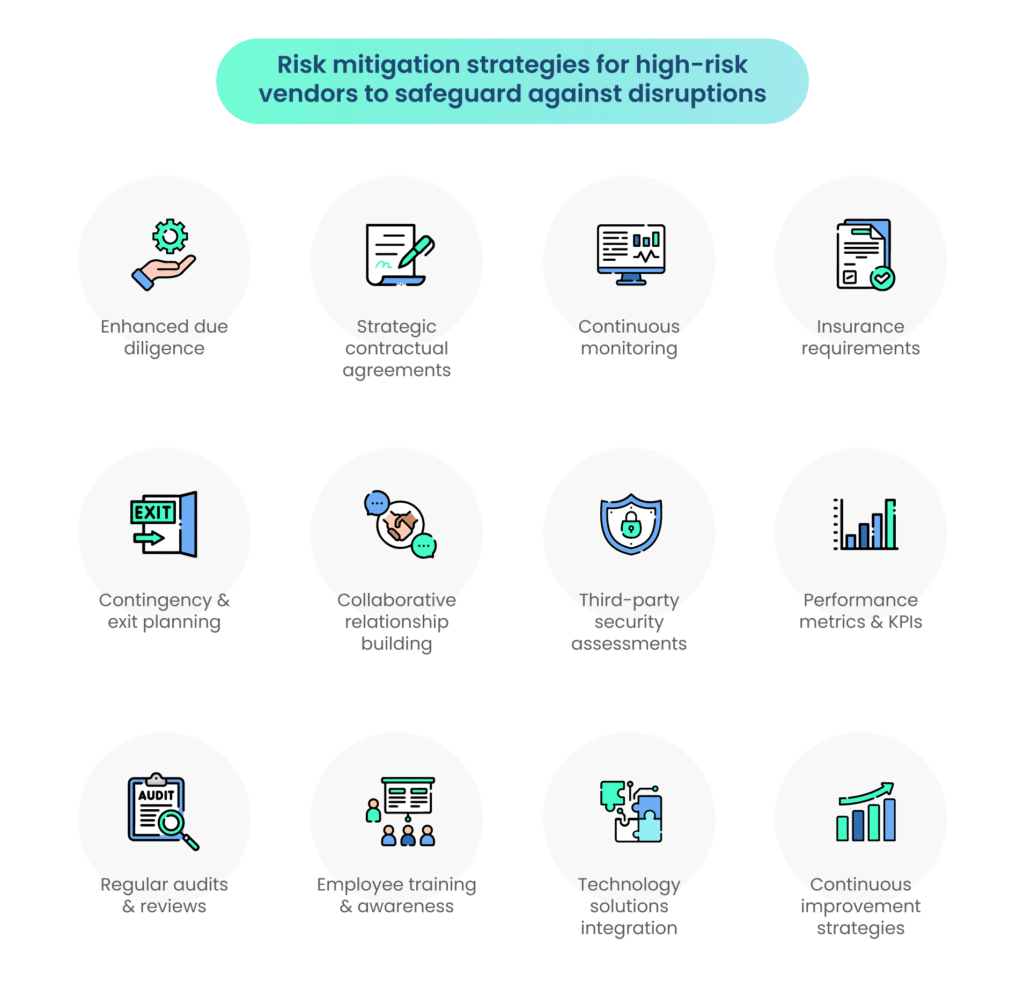
Conducting a security posture assessment is the cornerstone of a resilient cybersecurity strategy. It involves a meticulous exploration of an organization’s digital landscape to identify critical elements. Here are important steps to take while assessing your security posture.
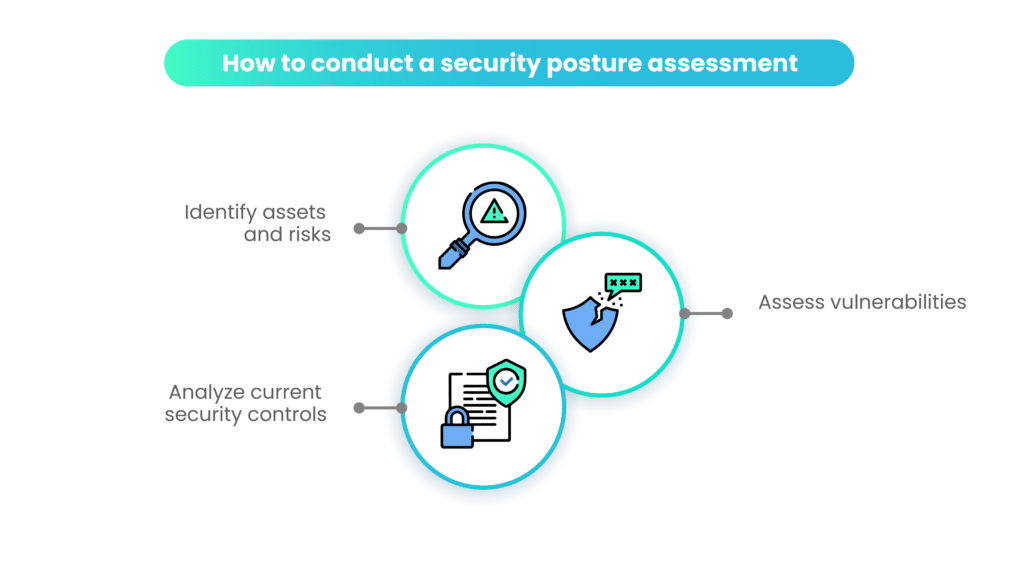
Identifying assets and risks
To comprehensively evaluate your security posture, begin by conducting a thorough assessment to identify all assets within your organizational framework. This encompasses not only tangible assets but also intangible ones such as sensitive data and intellectual property.
Simultaneously, recognize potential risks associated with these assets, considering both internal and external threats. A meticulous identification process forms the foundation for building a resilient security strategy.
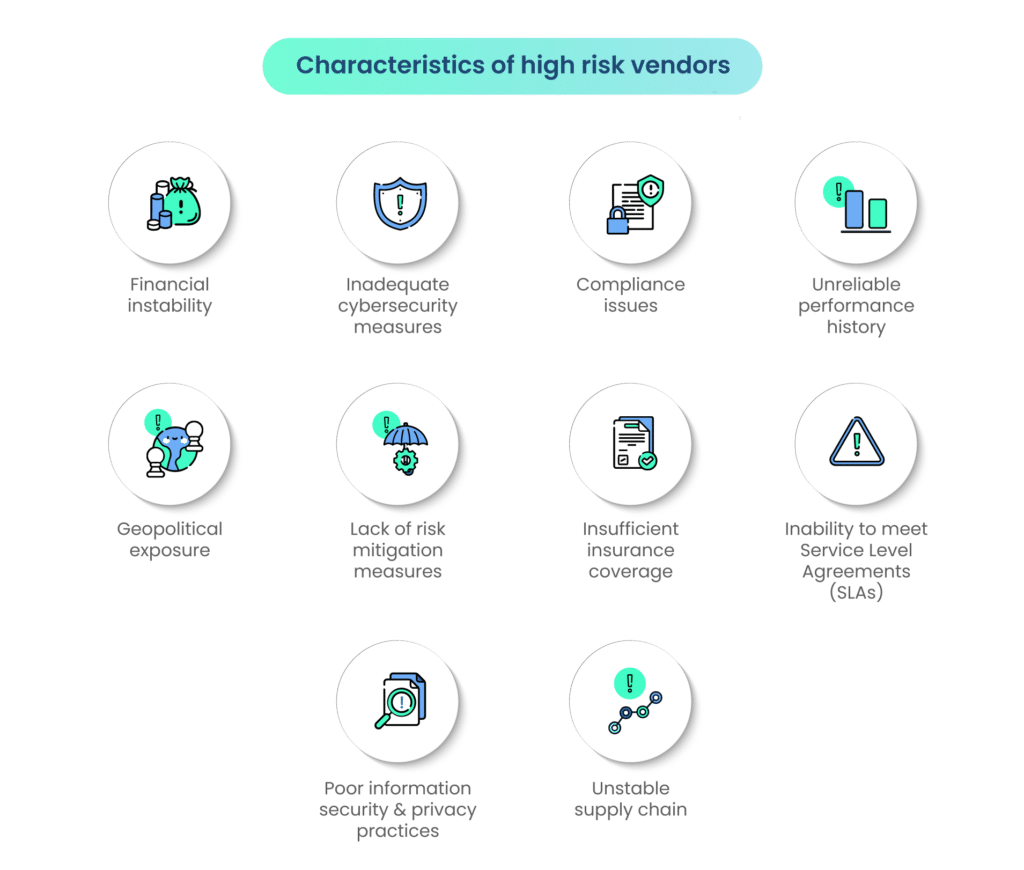
Assessing vulnerabilities
Once assets and risks are identified, proceed to assess vulnerabilities within your system. Pinpoint potential weaknesses, whether they lie in hardware, software, personnel, or processes.
This step involves a systematic examination to uncover points of susceptibility that could be exploited by malicious actors. A granular understanding of vulnerabilities is essential for crafting targeted security measures to fortify your overall defense.
Analyzing current security controls
Evaluate the effectiveness of your existing security controls. This involves a critical analysis of the tools, policies, and procedures in place to safeguard your assets and mitigate vulnerabilities.
Identify strengths and weaknesses in your current security framework, considering aspects such as access controls, encryption protocols, and incident response mechanisms. This analysis serves as a benchmark for refining and enhancing your security controls to align with the evolving threat landscape.
Tailoring communication for different stakeholders
Effectively communicating security information requires a tailored approach to cater to the diverse needs and perspectives of different stakeholders.
This ensures that each stakeholder group receives information relevant to their roles and responsibilities, fostering a shared understanding of the importance of security measures. Here’s how to customize your communication strategies based on the type of stakeholder:
Executives and leadership
For executives and leadership, a high-level overview is paramount. Communicate the security landscape in a strategic context, highlighting key threats and vulnerabilities without delving into technical minutiae.
Emphasize the relevance of security measures in achieving business objectives and maintaining organizational resilience.
Tailor the message to address business impact and risk mitigation strategies. Outline how security initiatives align with broader business goals, emphasizing the potential financial and reputational consequences of security lapses.
Provide a clear roadmap for risk mitigation to instill confidence in decision-makers.
IT and security teams
Catering to IT and security teams involves delving into technical specifics. Provide in-depth information on security protocols, tools, and technologies.
Clearly articulate the implementation plan, detailing how these measures contribute to overall security. Addressing technical nuances is crucial for the effective execution of security strategies.
Ensure clarity on incident response procedures for IT and security teams. Outline specific protocols, roles, and responsibilities during security incidents.
Foster a compliance-based culture of preparedness by detailing the step-by-step procedures to follow in the event of a security breach, empowering the teams to respond effectively.
Non-technical employees
Tailor communication for non-technical employees by emphasizing the importance of security awareness.
Provide accessible and engaging security awareness training to educate employees on potential risks, common threats, and best practices.
Promote a culture of vigilance and responsibility to enhance the organization’s overall security posture.
Clearly define user responsibilities, focusing on everyday actions that contribute to a secure environment. Communicate simple yet effective security practices, such as password hygiene, data handling procedures, and recognizing phishing attempts.
Empower non-technical employees to be active contributors to the organization’s security culture.
Customers
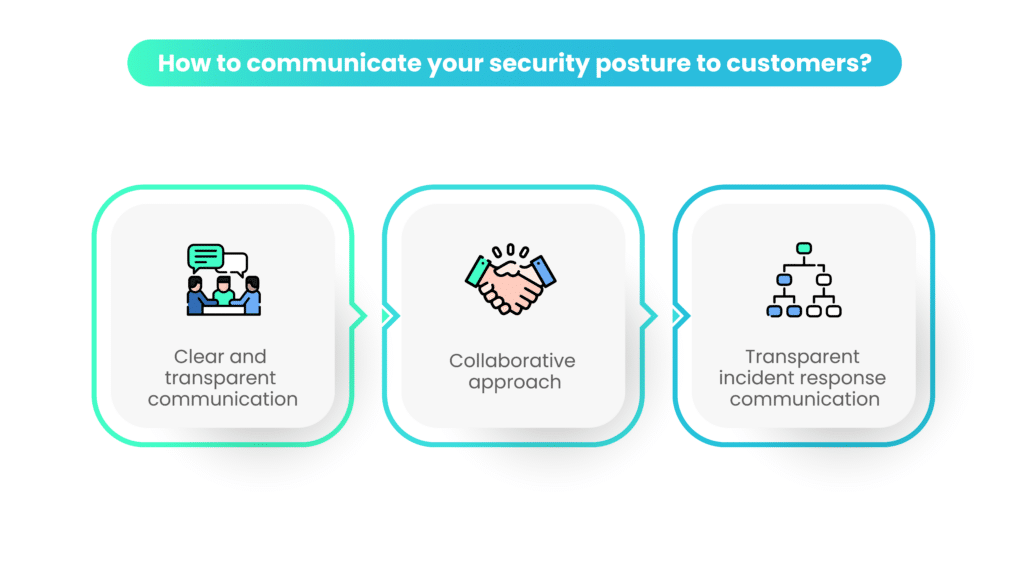
Tailor communication for customers by providing a clear and transparent overview of your security measures. Develop user-friendly documentation that emphasizes the importance of data protection. Communicate how their information is safeguarded, using language that is easily understandable and avoiding technical jargon.
Foster a collaborative approach with customers by regularly updating them on security enhancements and new features. Establish a dedicated customer support channel for security inquiries and concerns, ensuring that customers feel confident in the security measures in place. Provide educational content to empower customers to contribute actively to the organization’s security culture.
When communicating with customers, incorporate information about security certifications and compliance. Highlight your organization’s commitment to maintaining a strong security posture, aligning with industry standards, and ensuring that their data is handled with the utmost care.
In the event of a security incident, communicate promptly and transparently with customers. Provide clear and concise information about the nature of the incident, the steps being taken to address it, and any actions customers may need to take. This transparency contributes to a quicker recovery of customer trust.
Suppliers and partners
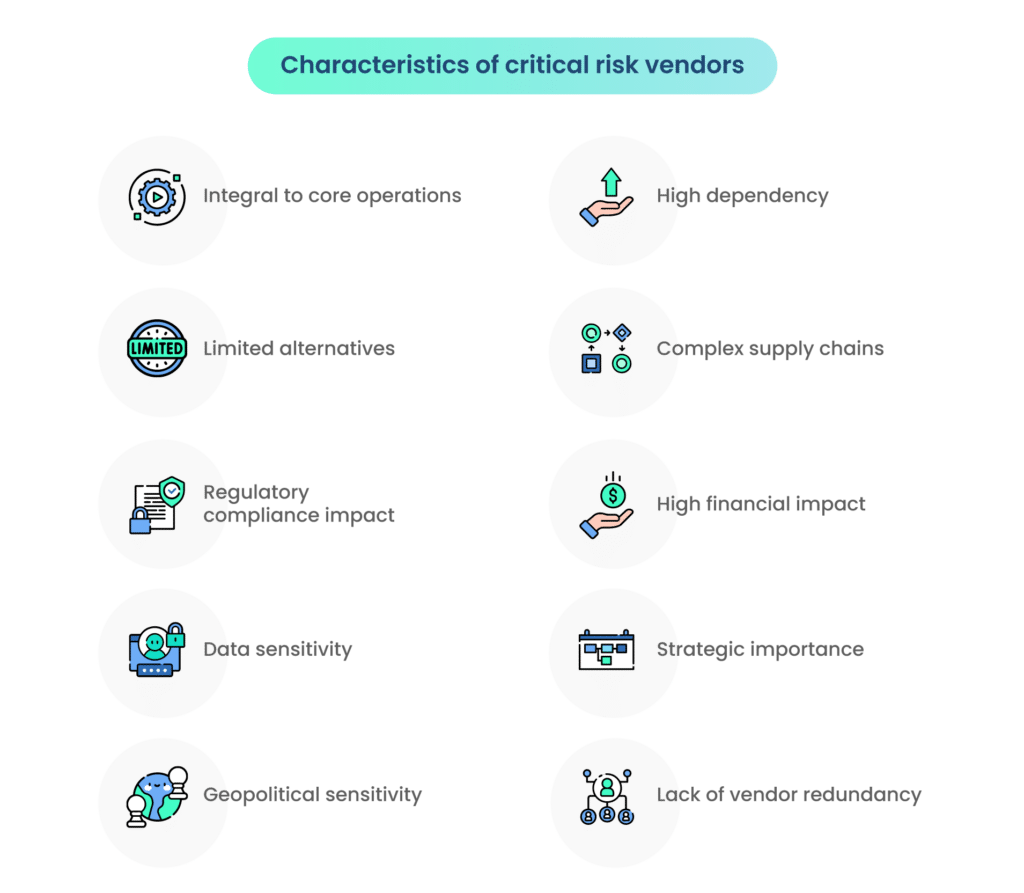
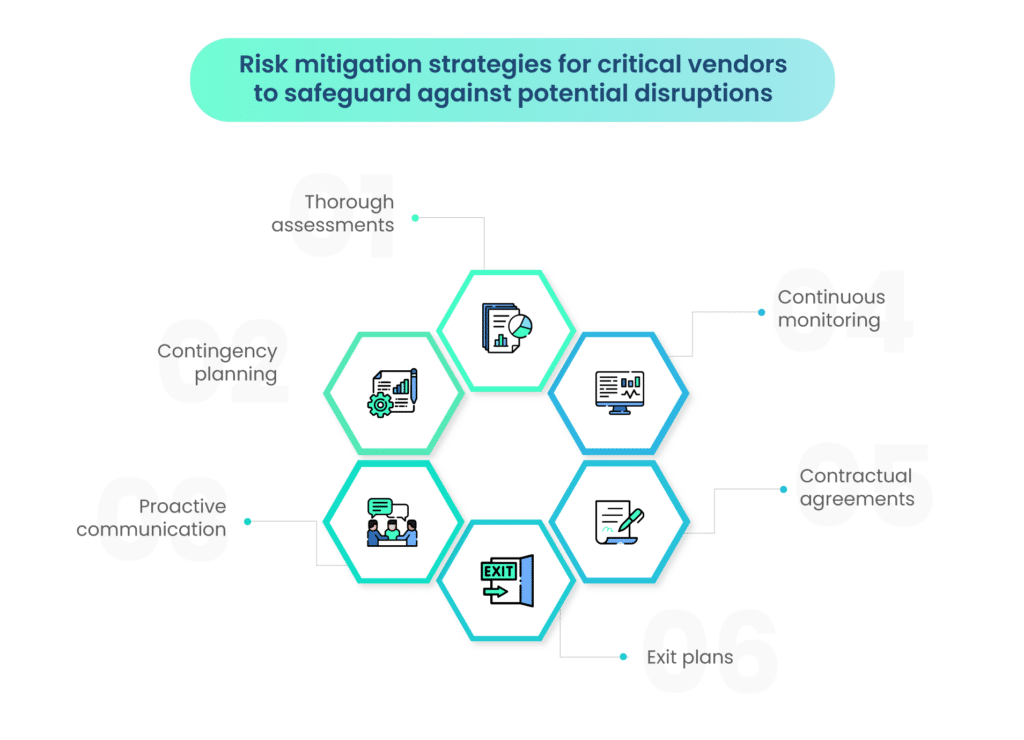
Foster a collaborative approach with suppliers and partners by sharing relevant security information. Establish secure channels for communication and collaboration, emphasizing the mutual commitment to maintaining a robust security posture. Encourage open dialogue to address concerns and ensure that security practices align seamlessly across the collaborative network.
Clearly outline security requirements and expectations in contractual agreements with suppliers and partners. Ensure that all parties involved understand and commit to maintaining strong security practices. Regularly review and update these clauses to adapt to evolving security needs within the collaborative ecosystem.
Share incident response plans with suppliers and partners to instill confidence in your organization’s ability to address security incidents effectively. Communicate the steps that will be taken in the event of a security breach, highlighting the collaborative measures in place to minimize the impact on all stakeholders.
Establish regular collaboration sessions with suppliers and partners to discuss and update security measures. This proactive approach ensures that all entities within the collaborative network are aligned with the latest security protocols and practices, contributing to a secure business environment for all parties involved.
Regulatory bodies
Tailor communication for regulatory bodies by clearly articulating your organization’s commitment to compliance with industry regulations and standards. Provide regular reports and updates to regulatory authorities, showcasing how your security posture aligns with specific guidelines and frameworks.
Establish transparent incident reporting protocols for regulatory bodies. In the unfortunate event of a security incident, communicate promptly and openly with relevant regulatory authorities. Provide detailed information about the nature of the incident, the steps being taken to address it, and the preventive measures in place to mitigate future risks.
Adopt a proactive and collaborative approach with regulatory bodies by actively participating in industry discussions and initiatives related to cybersecurity. This engagement demonstrates a commitment to shared objectives and contributes to the overall improvement of cybersecurity practices within the industry.
Ensure compliance with reporting obligations to regulatory bodies. Regularly update regulatory authorities on changes to your security measures, enhancements to your security posture, and any other pertinent information that aligns with industry standards and regulations.
Using technology to communicate your organization’s security posture
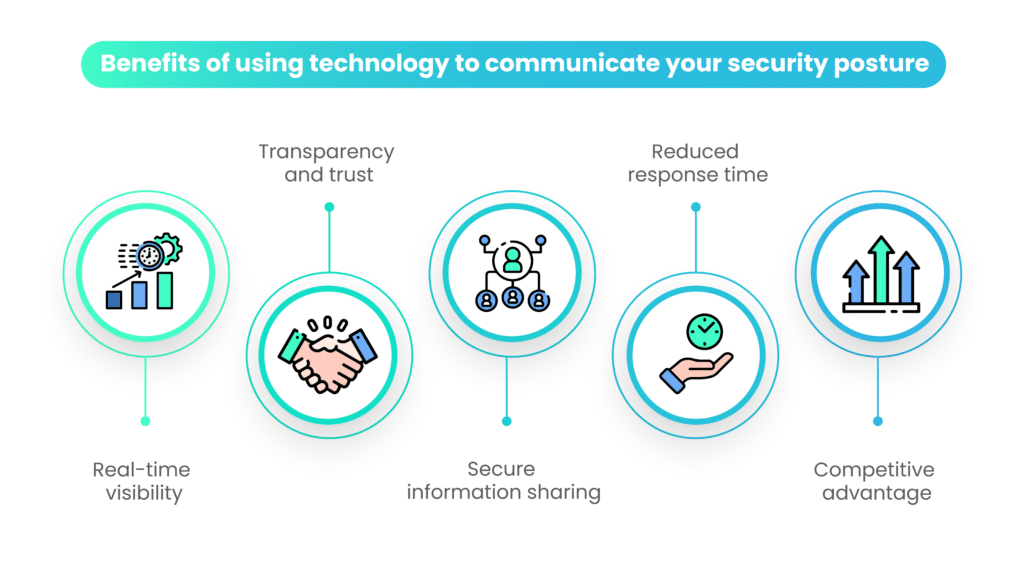
In this era of heightened cybersecurity concerns and evolving regulatory frameworks, how an organization conveys its commitment to data security significantly influences its credibility and trustworthiness. Leveraging advanced technological solutions emerges as a pivotal strategy in fortifying this communication process. Expanding on this, let’s delve into key facets that underscore the indispensable role of technology in the strategic communication of an organization’s security posture:
1. Real-time visibility
Technology allows for real-time visibility into your organization’s security posture. Tools like Scrut’s Trust Vault provide a dynamic and constantly updated view of certifications, compliance reports, and security controls. This real-time information instills confidence in customers and stakeholders, assuring them that your security measures are current and actively monitored.
2. Efficient information access
Technology streamlines the accessibility of crucial security information. Instead of traditional methods involving manual requests and document sharing, tools enable stakeholders to access the information they need quickly and conveniently. This efficiency is particularly valuable in fast-paced business environments where timely decision-making is essential.
3. Transparency and trust
Utilizing technology to communicate security posture promotes transparency. When customers and stakeholders can easily access detailed information about your security measures, it builds trust. Transparency is a key element in establishing and maintaining strong relationships, especially in industries where data security is a top priority.
4. Secure information sharing
Advanced technologies provide a secure means of sharing sensitive security information. Features like NDA-backed gated access, as seen in Trust Vault, add an extra layer of security to detailed reports. This secure sharing mechanism assures stakeholders that their access to sensitive data is carefully managed and controlled.
5. Reduced response time
Technology streamlines the communication process, reducing the time it takes to respond to security-related queries. Automated systems can update security controls in real-time, saving valuable resources and accelerating response times.
6. Adherence to compliance standards
Many tools are designed to adhere to and demonstrate compliance with industry standards. This is critical for organizations operating in regulated environments. Automated platforms can help ensure that the organization’s security posture aligns with established standards and frameworks.
7. Data-driven decision-making
Technology provides the means to collect and analyze data related to security posture. This data-driven approach allows organizations to identify trends, measure the effectiveness of security measures, and continuously improve their security protocols based on informed decision-making.
8. Ease of communication
Technology facilitates easy communication by consolidating security information into a single, accessible platform. This simplicity ensures that stakeholders, regardless of their role or department, can understand and engage with the organization’s security posture without unnecessary complexity.
9. Competitive advantage
Organizations that effectively use technology to communicate their security posture gain a competitive advantage. Demonstrating a robust security infrastructure can be a key differentiator in industries where customers prioritize data protection and compliance.
Wrapping up
Communicating your organization’s security posture effectively can make a substantial difference in the competitive landscape, especially in the realm of SaaS where trust and reliability are paramount.
While cutting-edge technology and innovation are essential for attracting customers, the often-underestimated factors of trustworthiness and reliability play a crucial role in customer retention.
The importance of communicating security posture is further underscored by its impact on stakeholder assurance, brand reputation, risk mitigation, regulatory compliance, incident response, and the alignment of security with broader business objectives.
In an era marked by escalating costs of data breaches and tightening regulatory landscapes, the need for a defensible security program has never been more apparent.
Using tools like Scrut’s Trust Vault can help you communicate your organization’s security posture effectively. Schedule a demo today to learn more.
FAQs
A security posture assessment involves a comprehensive evaluation of an organization’s approach to managing and safeguarding its information assets, technology infrastructure, and sensitive data. It is crucial for identifying vulnerabilities, assessing risks, and analyzing the effectiveness of existing security controls. This assessment lays the foundation for building a resilient cybersecurity strategy.
The primary stakeholders include internal audiences such as employees, management, and leadership, as well as external audiences like clients, customers, partners, and regulatory bodies. Tailoring the communication to different stakeholder groups ensures a shared understanding of the importance of security measures and builds trust.
In an era where data breaches and cyber incidents are headline news, openly communicating security measures signals a commitment to safeguarding sensitive information. This commitment enhances the organization’s credibility in the eyes of customers and the public, contributing significantly to a positive brand image.
Technology plays a pivotal role in enhancing the communication of security posture. It provides real-time visibility into security measures, streamlines information access, ensures secure sharing of sensitive data, reduces response times, and facilitates data-driven decision-making. Leveraging technology not only enhances security but also provides a competitive advantage in industries where data protection is a top priority.
Communicating security posture to customers is crucial for building trust and demonstrating a commitment to safeguarding their data. Clear and transparent communication, along with the highlighting of compliance and certifications, helps assure customers that their information is handled with the utmost care. Regular updates and educational content further engage customers and empower them to be active contributors to the organization’s security culture.