In the thrilling arena of business, trust isn’t just the key to success – it’s the rocket fuel that propels companies to greatness. Governance, risk management, and compliance (GRC) play an important role in building trust.
GRC encompasses a set of practices, policies, and systems that organizations adopt to ensure ethical operations, transparency, and compliance with legal and regulatory requirements. It goes beyond risk management and rule adherence—GRC represents a strategic approach to cultivating trust.
By establishing robust governance structures, implementing effective risk management strategies, and adhering to applicable laws and standards, businesses can showcase their dedication to integrity and responsible conduct. This, in turn, cultivates trust among stakeholders, positioning the company for enduring success and sustainability.
In this blog, we will delve into the intricate relationship between trust and business, with a primary focus on the pivotal role played by GRC.
Understanding customer trust in business
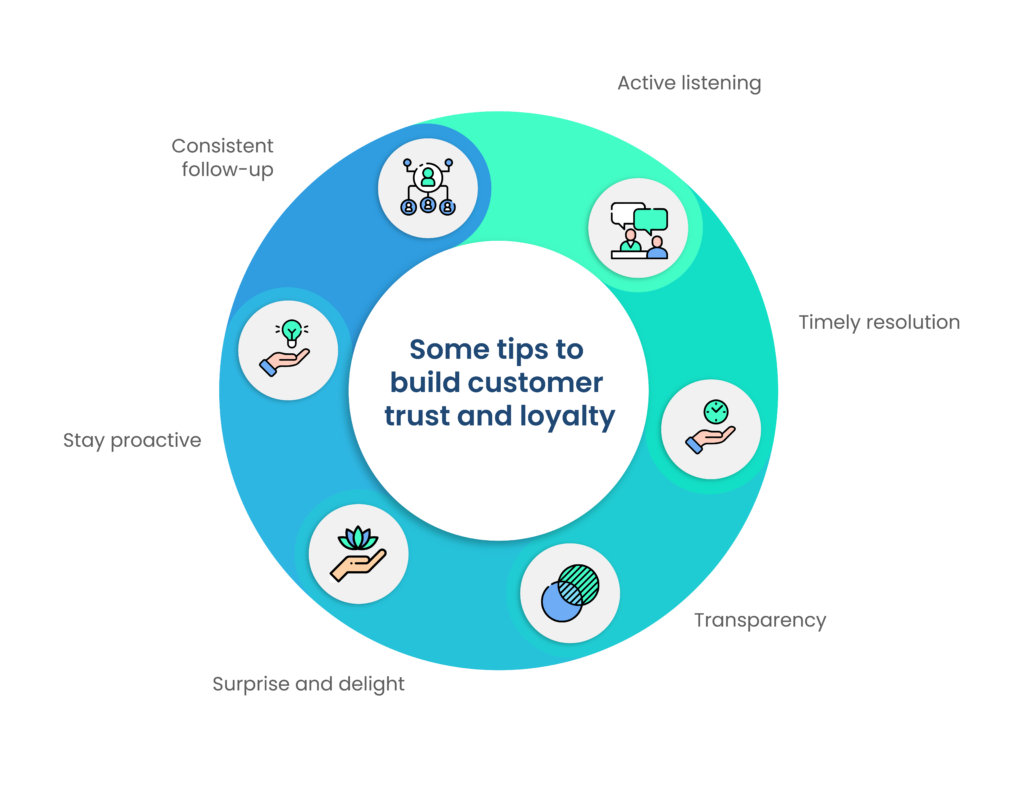
Customer trust, in the context of business, is the unwavering confidence that consumers place in a company. It signifies their belief that the company will consistently deliver on promises, provide value, and prioritize their best interests. Customer trust is not merely a virtue; it’s a strategic imperative that forms the foundation of successful customer relationships.
Customer trust wields incredible influence over behavior and loyalty. When customers trust a business, they are more likely to engage, make repeat purchases, and remain loyal in the long run. It serves as the catalyst for forging lasting connections, encouraging customers to choose a brand over competitors and become advocates. We’ll uncover the profound ways in which customer trust shapes buying decisions and loyalty.
In the fiercely competitive business landscape, brand reputation and credibility are priceless assets. Customer trust serves as the guardian of these assets. It’s the force that can elevate a brand’s reputation to new heights, making it synonymous with reliability and authenticity. We’ll explore how customer trust is the linchpin that bolsters brand reputation and enhances overall credibility, paving the way for sustained success in the marketplace.
What are the components of GRC?
GRC, or governance, risk management, and compliance, is the holistic framework that organizations employ to ensure ethical conduct, regulatory adherence, and sustainable operations.
- Governance: Governance entails the establishment of effective leadership structures, decision-making processes, and ethical guidelines. It’s about defining roles, responsibilities, and accountabilities within an organization.
- Risk management: Risk management involves identifying, assessing, and mitigating potential risks that could impact the organization’s objectives. It’s the proactive effort to protect the organization from adverse events.
- Compliance: Compliance is the commitment to adhere to applicable laws, regulations, and industry standards. It ensures that the organization operates within legal boundaries and aligns with ethical norms.
The three GRC components – governance, risk management, and compliance – are intertwined in a delicate dance that fosters trust. Effective governance sets the ethical tone for the organization, ensuring that decisions and actions align with its values. Risk management identifies and mitigates potential threats to trust, safeguarding against reputational damage.
Compliance ensures that the organization upholds its promises and adheres to the rules, reinforcing its trustworthiness. Together, these components form a formidable alliance, creating a culture of trust that permeates every facet of the organization.
The role of GRC leaders in driving trust within the organization
The GRC leader, often in the form of a Chief Governance Officer or Chief Compliance Officer, plays a pivotal role in nurturing trust within the organization. They are responsible for:
- Establishing and promoting ethical governance practices.
- Identifying and managing risks that could erode trust.
- Ensuring the organization complies with all relevant regulations.
- Communicating the importance of trust and GRC throughout the organization.
- Building a robust trust GRC framework that reinforces trust as a strategic imperative.
In essence, the GRC leader is the guardian of trust, spearheading efforts to embed trustworthiness into the organization’s DNA and facilitating its long-term success.
Let’s discuss each component of GRC and its relationship to customer trust.
How do we establish strong governance?
A. The crucial role of governance in building customer trust
Governance serves as the North Star guiding organizations toward ethical and responsible conduct, which is paramount in building and maintaining customer trust. Customers want to engage with businesses that demonstrate integrity, accountability, and transparency in their operations. In this section, we’ll explore how robust governance is the cornerstone of customer trust.
B. Key principles and best practices for effective governance

Effective governance is built on a foundation of key principles and best practices that are indispensable in earning and preserving customer trust. Let’s delve into these guiding principles.
- Transparency: Transparency in decision-making and operations builds trust by allowing customers to see how an organization operates. Sharing information openly, especially about key policies and practices, is vital.
- Accountability: Effective governance includes clear lines of accountability. When individuals within an organization are held responsible for their actions, customers have confidence that the company is committed to rectifying any missteps.
- Ethical leadership: Ethical leadership sets the tone for the entire organization. Leaders who prioritize ethical behavior inspire trust and establish a culture of integrity.
- Compliance: Ensuring adherence to laws, regulations, and industry standards is essential. Customers trust organizations that consistently comply with the rules, as it signals reliability.
- Customer-centric approach: Governance should prioritize the best interests of customers. This means actively seeking customer feedback, addressing concerns promptly, and making decisions that enhance the customer experience.
C. Examples of organizations with successful governance structures
To gain insight into the real-world impact of strong governance, let’s explore a few noteworthy examples of organizations that have successfully implemented robust governance structures, earning the trust and admiration of their customers.
- Microsoft: Microsoft’s governance structure is renowned for its transparency and commitment to compliance. The company publishes detailed reports on its ethical practices and compliance efforts, demonstrating a dedication to accountability and customer trust.
- The Walt Disney Company: Disney’s governance practices prioritize both shareholders and customers. The company’s ethical guidelines and commitment to quality entertainment have fostered a loyal customer base that trusts Disney for family-friendly content and memorable experiences.
- Procter & Gamble: P&G is recognized for its strong governance and ethical leadership. The company’s focus on sustainability and social responsibility aligns with customer values, enhancing trust in its products and practices.
These organizations exemplify how effective governance not only builds trust but also contributes to long-term success and customer loyalty. Their commitment to ethical principles and transparency has set them apart as leaders in their respective industries.
How to incorporate effective risk management?
A. The role of risk management in building trustworthiness
Risk management is the guardian of trust, as it ensures a company’s commitment to safeguarding its stakeholders from potential harm. In this section, we’ll explore how an effective risk management strategy is central to enhancing trustworthiness.
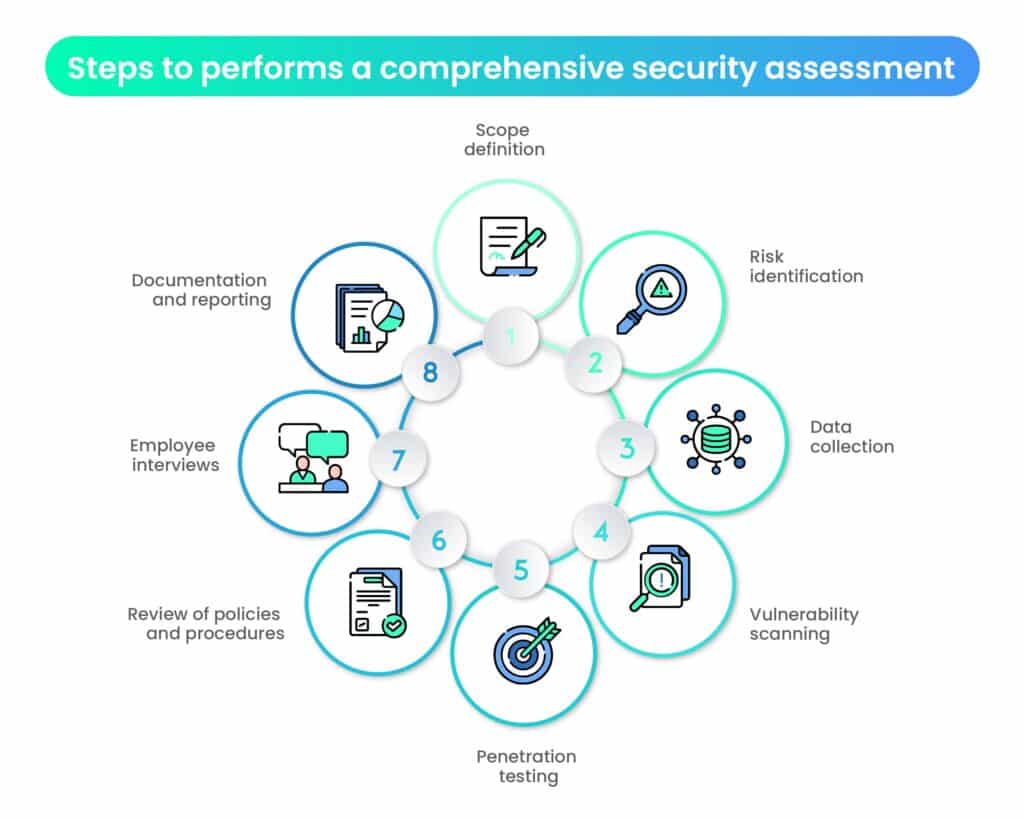
B. Steps involved in a robust risk management process

A robust risk management process involves a series of strategic steps that not only protect an organization from potential pitfalls but also play a vital role in bolstering trust by demonstrating foresight and responsibility.
- Risk identification: The first step is identifying potential risks that could affect the organization, ranging from operational and financial risks to reputational and compliance risks.
- Risk assessment: Assess the likelihood and impact of each identified risk. This step helps prioritize risks based on their significance.
- Risk mitigation: Develop and implement strategies to mitigate identified risks. This might include process improvements, insurance, or contingency plans.
- Monitoring and review: Continuously monitor the risk landscape, evaluating the effectiveness of risk mitigation measures. Adjust strategies as needed to adapt to changing circumstances.
- Communication: Maintain transparent communication with stakeholders about the organization’s risk management efforts. This fosters trust by demonstrating a proactive approach to risk mitigation.
C. Showcase of real-world cases of effective risk management
To appreciate the tangible impact of effective risk management on trust, let’s examine real-world instances where companies have successfully navigated challenges, earning admiration and confidence from their stakeholders through proactive risk management practices.
- JPMorgan Chase: After the 2008 financial crisis, JPMorgan Chase implemented a robust risk management framework. By focusing on risk identification and mitigation, the bank restored trust in its financial stability, which was critical in regaining customer and investor confidence.
- Toyota: Toyota’s proactive approach to product recalls and quality control is a testament to effective risk management. By addressing potential safety concerns swiftly and transparently, Toyota has maintained trust in its commitment to customer safety and quality.
- Johnson & Johnson: When faced with the Tylenol poisoning crisis in the 1980s, Johnson & Johnson’s swift response and product recall demonstrated their commitment to customer safety. This crisis management approach not only saved lives but also strengthened trust in the brand’s integrity.
These real-world examples showcase how effective risk management not only safeguards an organization but also reinforces trust among customers and stakeholders. A well-executed risk management strategy demonstrates an organization’s dedication to its responsibilities and its ability to navigate challenges with integrity.
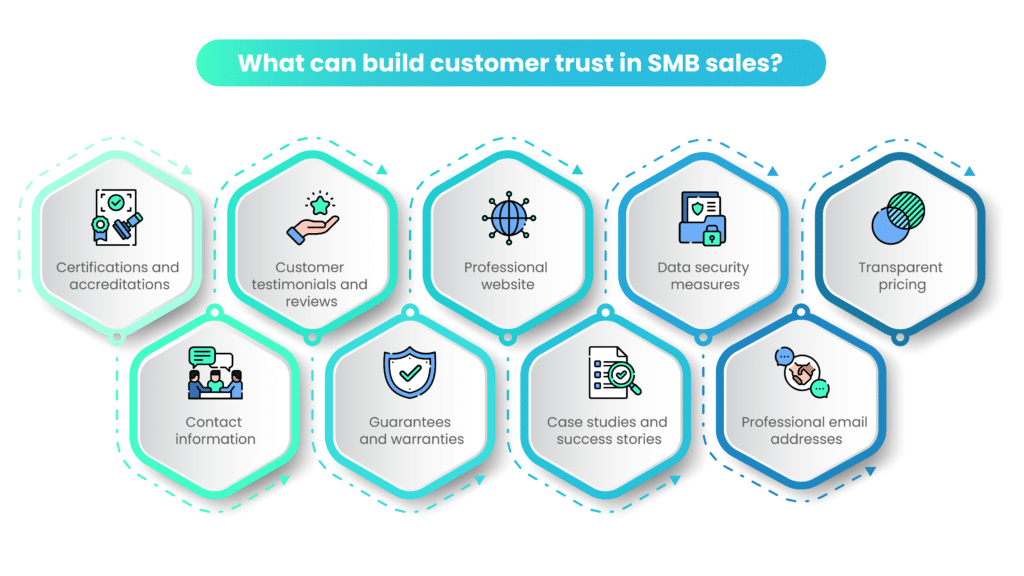
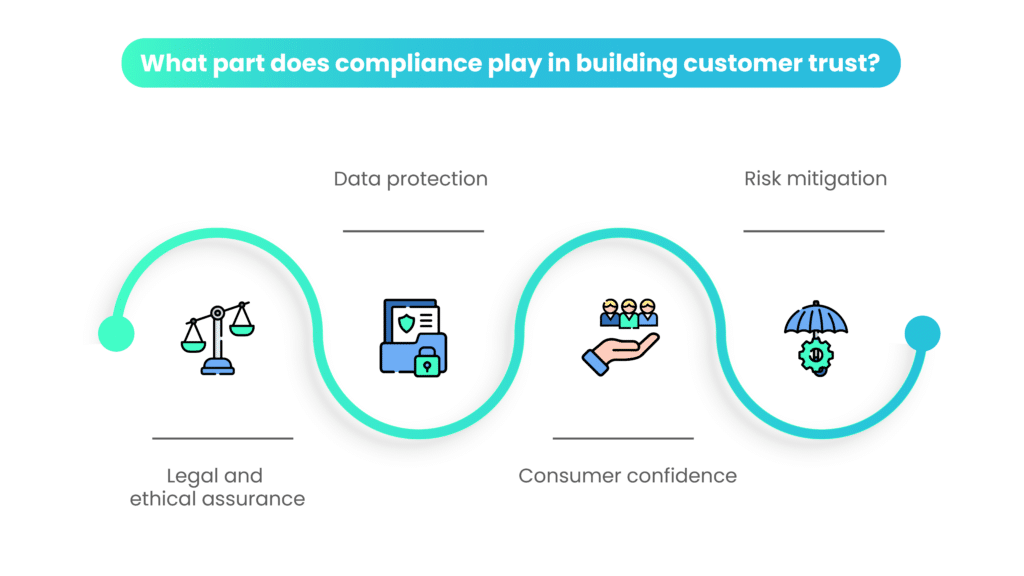
How do we build customer trust with compliance?
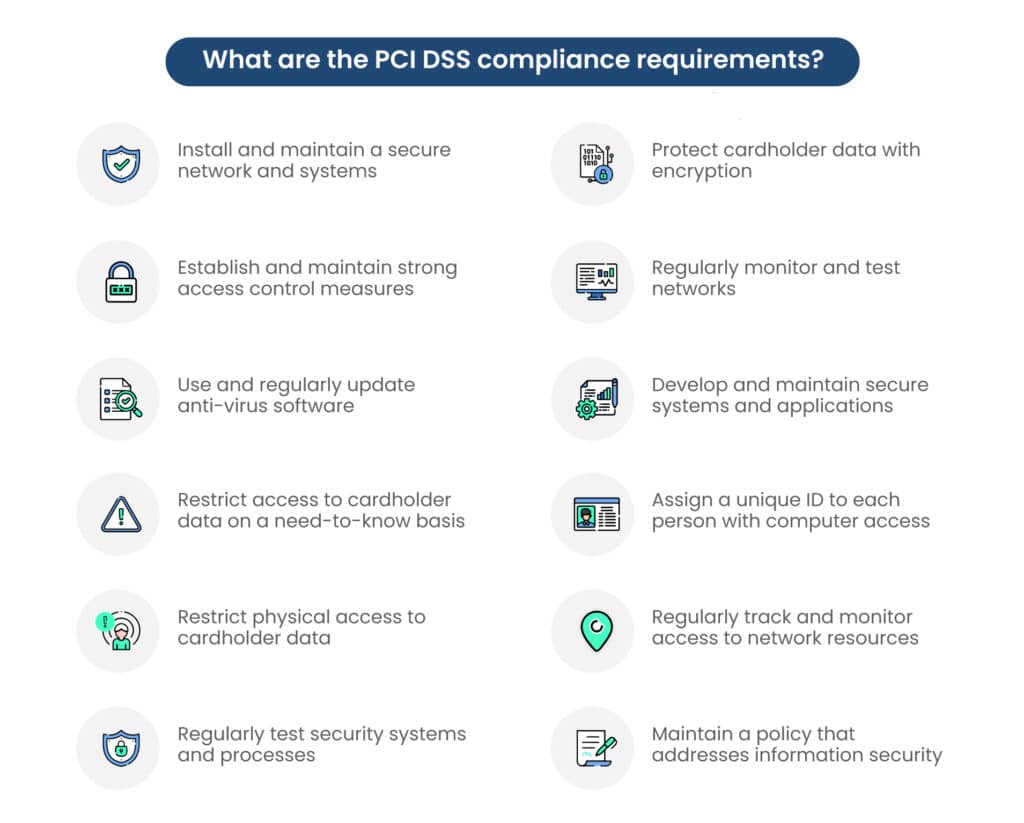
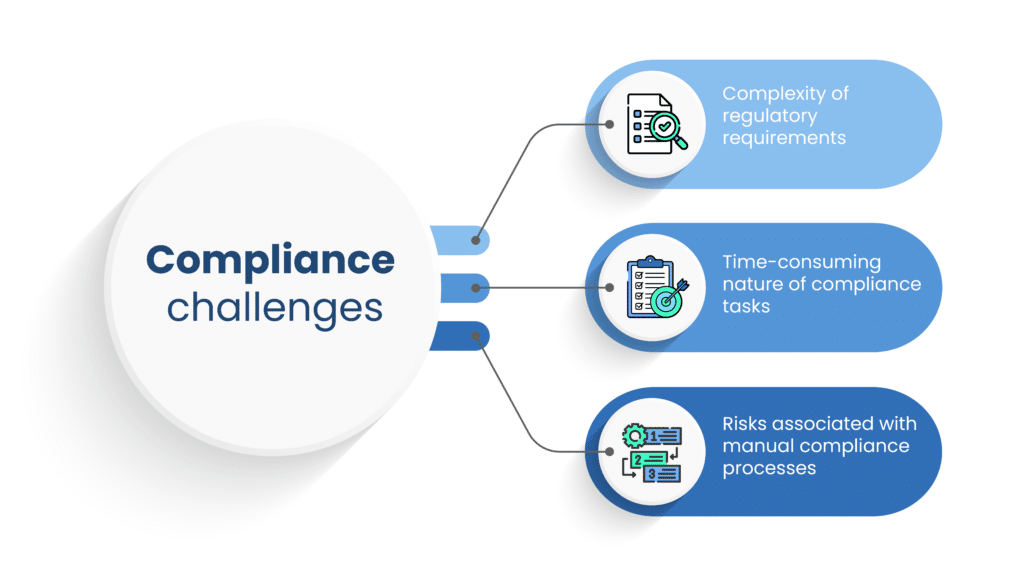
Compliance is not just a legal necessity; it’s the linchpin of customer trust in the business world. In this section, we’ll delve into the symbiotic relationship between compliance and the trust customers place in an organization.
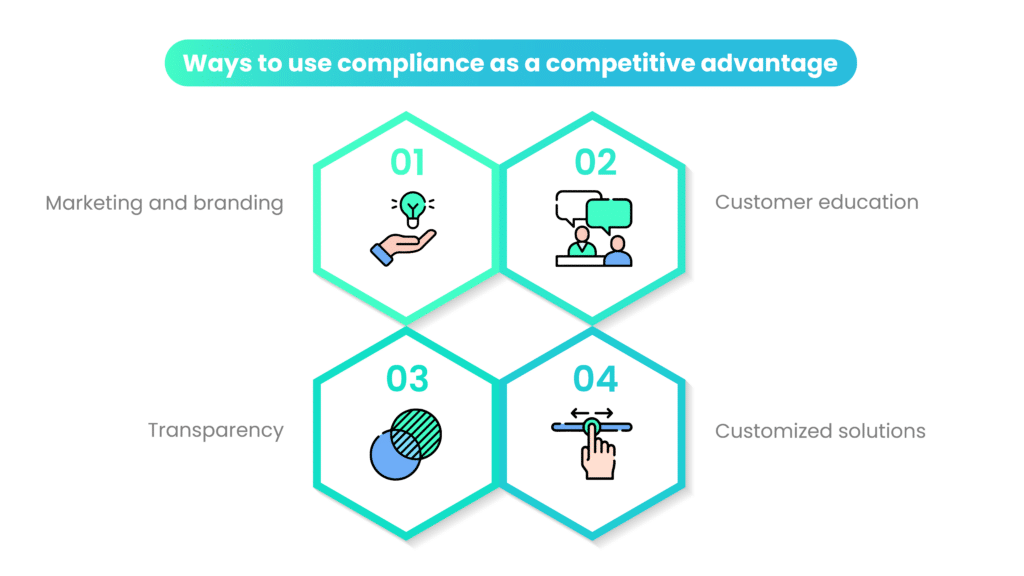
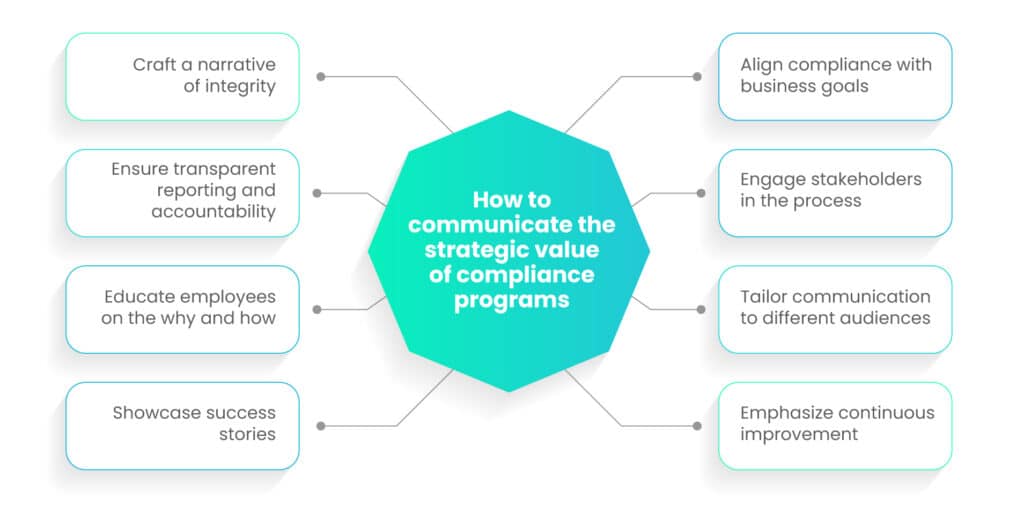
Strategies to fostering customer trust while maintaining compliance
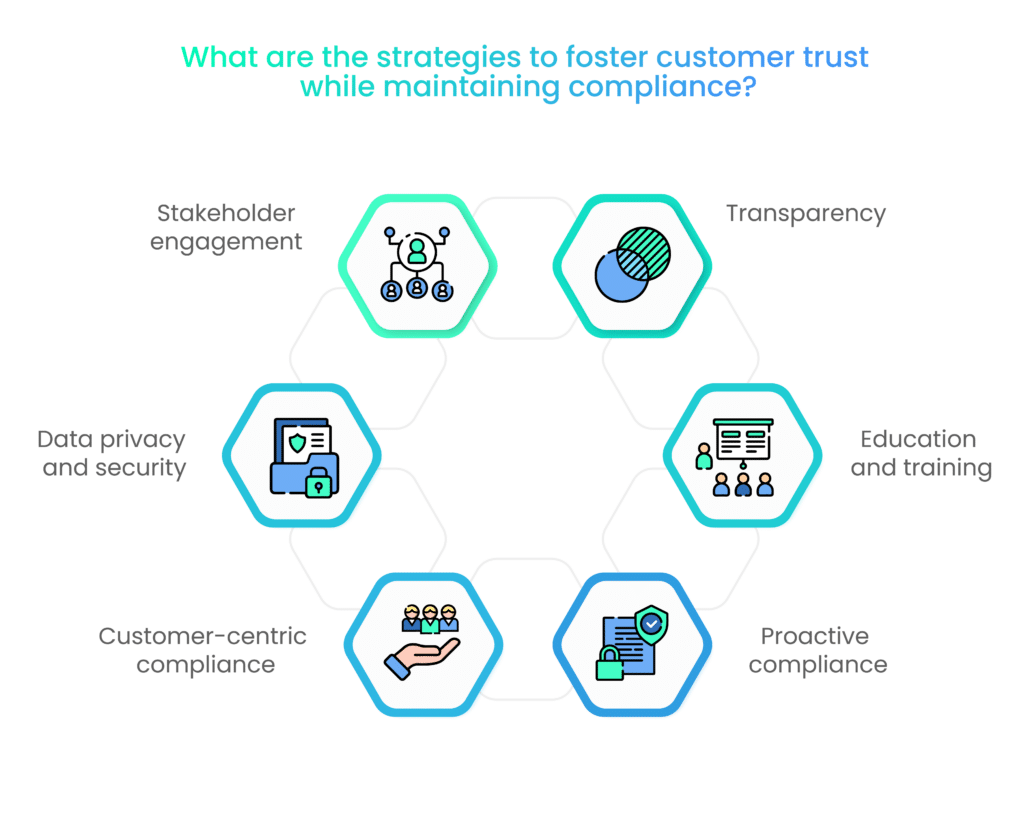
Balancing the demands of compliance with the imperative of fostering trust requires a thoughtful approach. Here, we’ll explore key strategies that organizations can employ to navigate this delicate equilibrium, ensuring both ethical integrity and customer confidence.
1. Transparency
Openly communicate your commitment to compliance and ethical conduct to customers. Transparency builds trust by assuring customers that your organization is accountable.
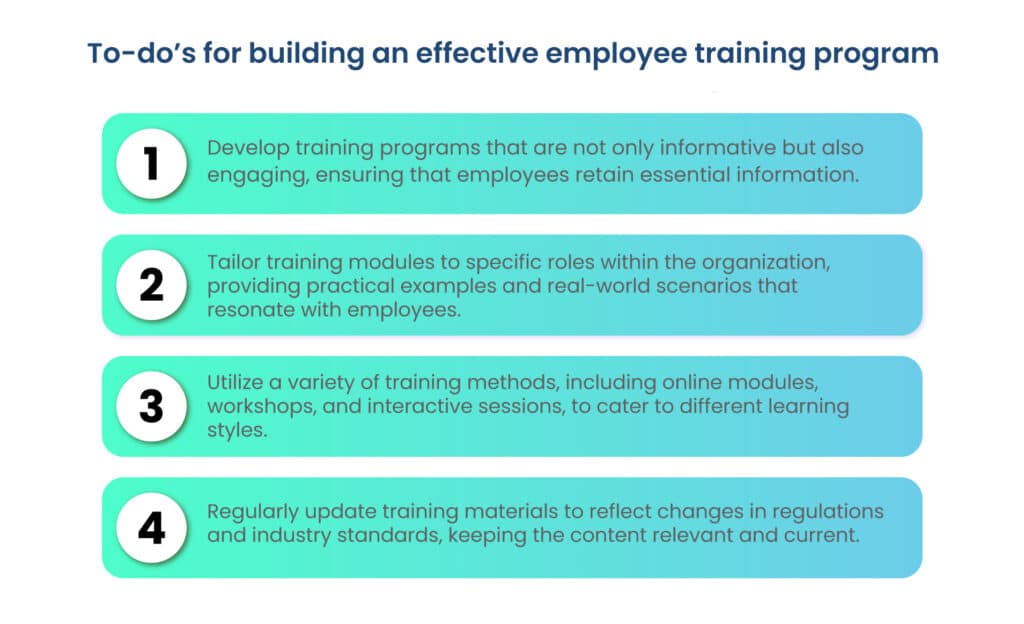
2. Education and training
Invest in ongoing education and training for employees to ensure they understand the importance of compliance and are equipped to meet ethical and regulatory standards.
3. Proactive compliance
Be proactive in identifying and addressing compliance issues before they escalate. Promptly rectifying any violations demonstrates a commitment to rectifying errors and upholding trust.
4. Customer-centric compliance
Align compliance efforts with customer interests. Ensure that compliance measures are designed to protect customers, fostering the perception that their well-being is a top priority.
5. Data privacy and security
With the rise in data breaches, robust data privacy and security compliance are essential. Customers trust organizations that safeguard their personal information.
6. Stakeholder engagement
Engage with stakeholders, including customers, in discussions about compliance and ethical practices. Their input can provide valuable insights and build trust in your commitment to transparency.
Incorporating these strategies into your compliance framework not only ensures regulatory adherence but also fosters a culture of trust. Customers are more likely to engage with and remain loyal to organizations that prioritize compliance and ethical conduct, ultimately leading to sustainable business success.
What is the role of technology in enhancing trust?
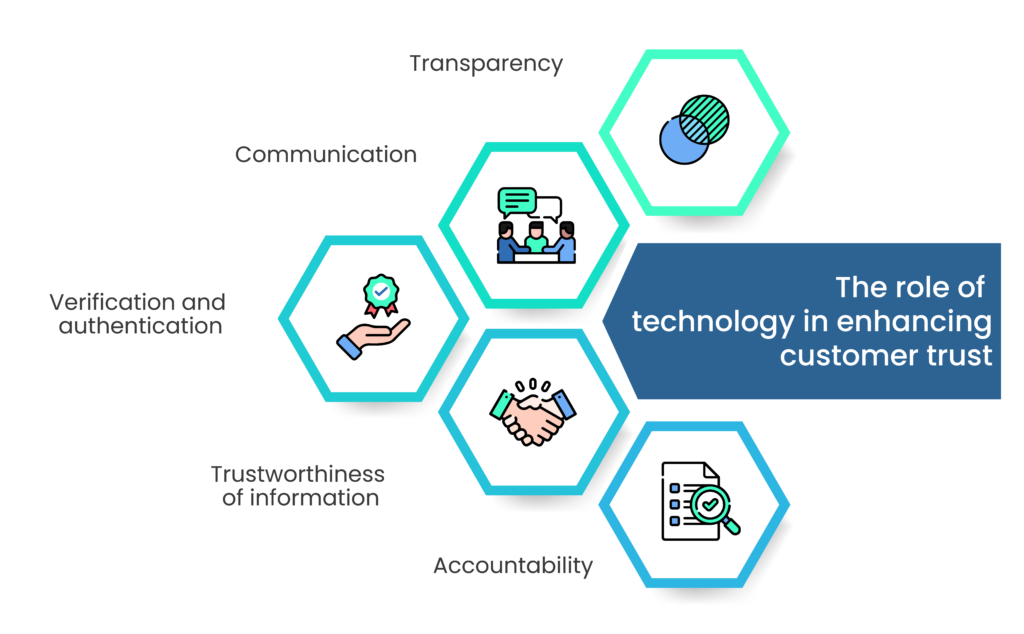
Technology plays a crucial role in enhancing trust in various aspects of our personal and professional lives. Here are some ways in which technology contributes to building and enhancing trust:
1. Transparency
Technology enables organizations to be more transparent in their operations. Through tools like blockchain, companies can provide transparent records of transactions and supply chains, which can help build trust with customers and partners.
2. Communication
Technology, particularly digital communication tools, allows for more efficient and instant communication. Timely and clear communication fosters trust between individuals and organizations.
3. Verification and authentication
Technologies such as biometrics (fingerprint, facial recognition) and multi-factor authentication (MFA) help verify the identity of users, reducing the risk of fraud and enhancing trust in online interactions.
4. Trustworthiness of information
With the advent of AI and machine learning, technology can help filter and verify information sources, reducing the spread of misinformation and enhancing trust in the information ecosystem.
5. Accountability
Through the use of data analytics and monitoring tools, technology can help organizations hold themselves accountable for their actions, leading to increased trust from stakeholders.
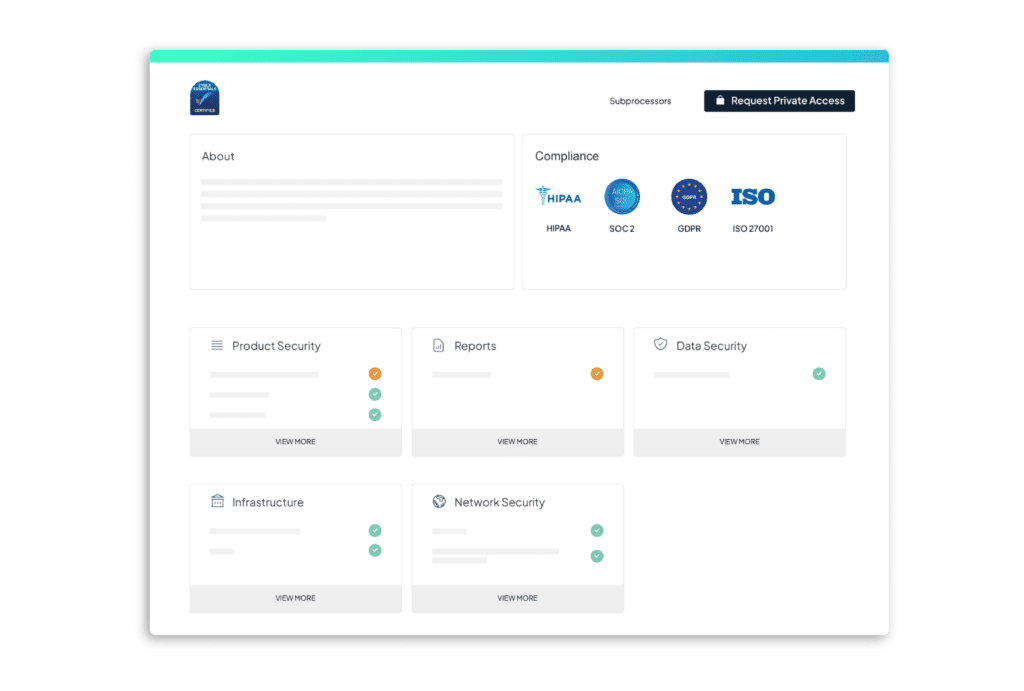
Cybersecurity and data privacy as trust-building factors
Cybersecurity and data privacy are foundational elements for building trust in the digital age. Strong cybersecurity practices protect against threats, while respect for data privacy assures individuals that their information is handled responsibly.
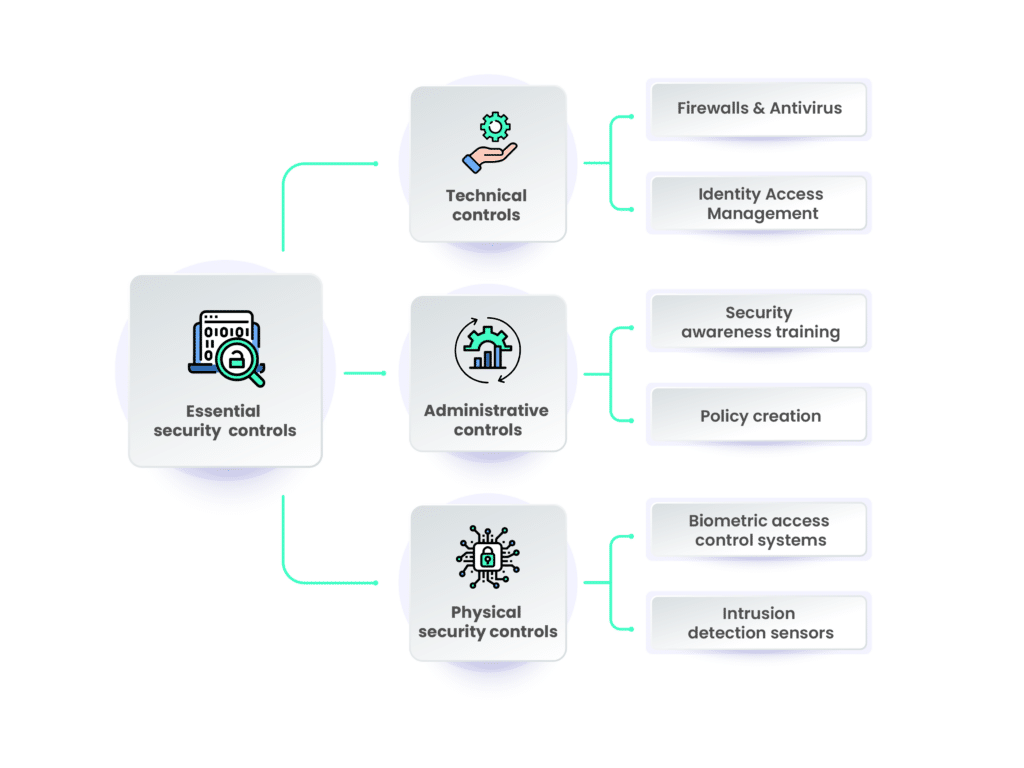
Cybersecurity
Robust cybersecurity practices are essential for building trust in the digital age. Organizations must protect their systems and data from cyberattacks to ensure the trust of their customers and partners. Measures include:
- Regular security audits and penetration testing.
- Encryption of sensitive data.
- Employee training on security best practices.
- Incident response plans to address breaches promptly.
Data privacy
Respecting data privacy is a key factor in building trust, as individuals want assurance that their personal information is handled responsibly. Steps to promote data privacy and trust include:
- Complying with data protection regulations (e.g., GDPR, CCPA).
- Clearly communicating privacy policies to users.
- Obtaining explicit consent for data collection and processing.
- Providing users with control over their data.
Tips on selecting and implementing trust-enabling technologies
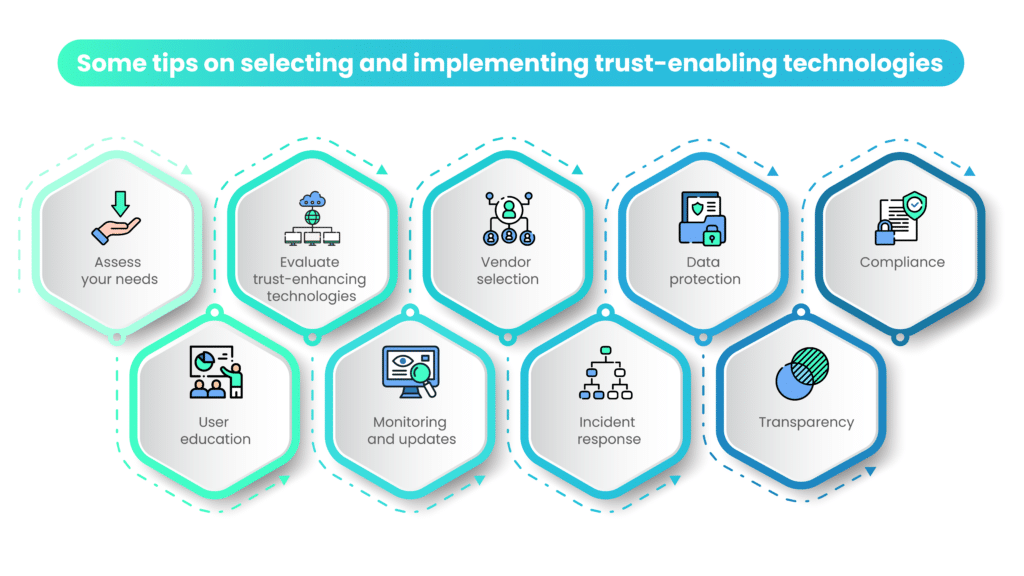
Selecting and implementing trust-enabling technologies involves a strategic approach that considers specific needs, evaluates technology options, and ensures compliance with security and privacy standards. Here are some key tips for success:
1. Assess your needs
Start by identifying the specific trust-related challenges or goals your organization faces. Understand what technologies are relevant to your industry and objectives.
2. Evaluate trust-enhancing technologies
Research and evaluate technologies that address your trust-related needs. Consider factors such as security, reliability, scalability, and cost-effectiveness.
3. Vendor selection
Choose reputable vendors with a track record of delivering trustworthy solutions. Look for customer reviews, case studies, and certifications to gauge their trustworthiness.
4. Data protection
Ensure that the technologies you select have robust data protection features. This includes encryption, access controls, and data backup strategies.
5. Compliance
Ensure that the technologies align with relevant regulatory requirements and industry standards related to trust and security.
6. User education
Train your employees and users on the proper use of trust-enabling technologies to minimize vulnerabilities and risks.
7. Monitoring and updates
Continuously monitor and update your trust-enabling technologies to stay ahead of emerging threats and vulnerabilities.
8. Incident response
Develop a clear incident response plan to address any breaches or trust-related issues promptly and effectively.
9. Transparency
Be transparent with your stakeholders about the technologies you use and the measures you take to enhance trust. Communication is key to building and maintaining trust.
In conclusion, technology is a powerful tool for enhancing trust in various aspects of our lives. Whether it’s through transparent operations, robust cybersecurity, or responsible data privacy practices, organizations can leverage technology to build and maintain trust with their stakeholders. However, this requires careful consideration of the technologies chosen and a commitment to ethical and responsible use.
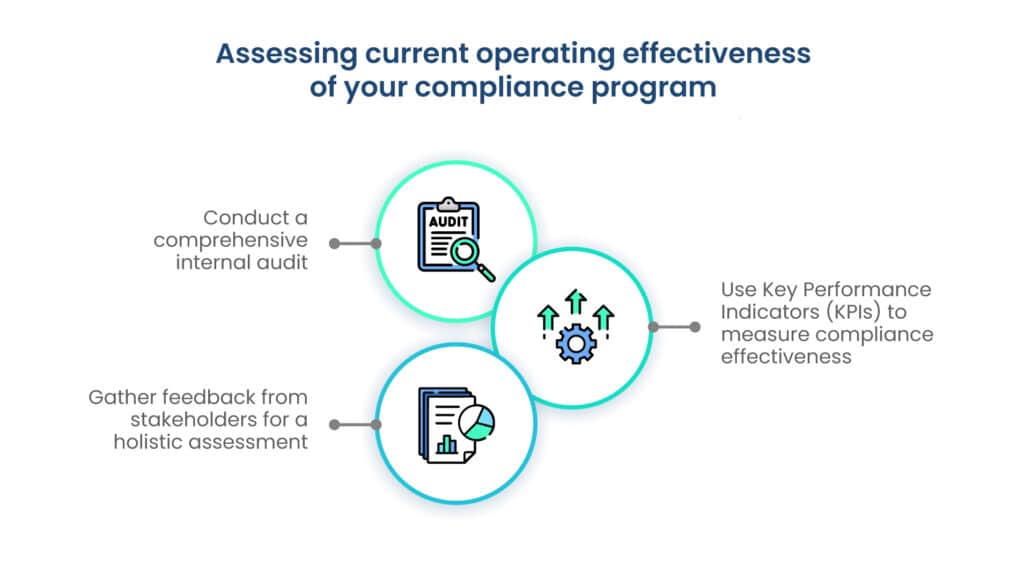
How do we assess and measure the trustworthiness of an organization?

Assessing and measuring the trustworthiness of an organization is critical for maintaining and enhancing trust with stakeholders. Here’s how you can do it:
1. Stakeholder feedback
Gather feedback from customers, employees, partners, and other stakeholders through surveys, interviews, and reviews. Their perceptions can provide valuable insights into your organization’s trustworthiness.
2. Transparency
Assess how transparent your organization is in its operations, communications, and decision-making processes. Transparency is a key indicator of trustworthiness.
3. Compliance and ethics
Evaluate your organization’s adherence to legal and ethical standards. Compliance with regulations and ethical principles is fundamental to trust.
4. Data privacy and security
Measure the effectiveness of your data privacy and cybersecurity measures. A breach of data can significantly erode trust.
5. Reliability and consistency
Assess your organization’s ability to consistently deliver on promises and commitments. Reliability is a cornerstone of trust.
6. Accountability
Gauge how well your organization takes responsibility for its actions and addresses issues or mistakes. Accountability builds trust when handled appropriately.
7. Competence
Evaluate the competence of your team and the quality of products or services provided. Incompetence can lead to a loss of trust.
8. Social responsibility
Consider your organization’s efforts toward social responsibility and sustainability. Ethical behavior and a commitment to social causes can enhance trustworthiness.
What are the key performance indicators (KPIs) for customer trust measurement?
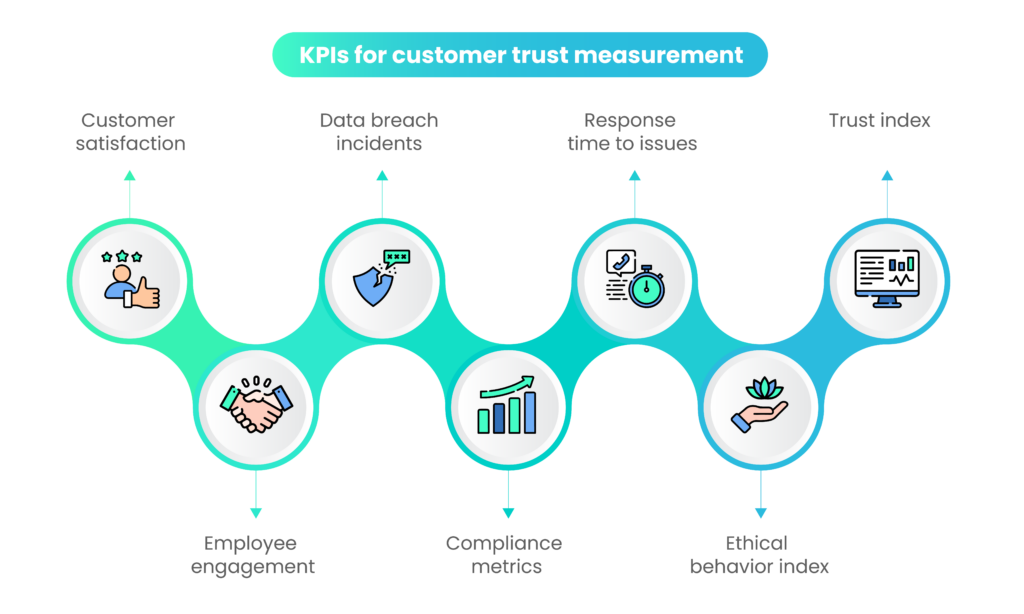
To quantitatively measure trust, you can establish KPIs tailored to your organization’s goals and context. Some KPIs for trust measurement include:
1. Customer satisfaction
Measure customer satisfaction through surveys, Net promoter score (NPS), or Customer satisfaction score (CSAT). Satisfied customers are more likely to trust your organization.
2. Employee engagement
Assess employee engagement levels using employee surveys and turnover rates. Engaged employees often contribute to a more trustworthy organization.
3. Data breach incidents
Track the number and severity of data breaches. Fewer incidents indicate a more trustworthy approach to data security.
4. Compliance metrics
Monitor compliance with relevant regulations and industry standards. Achieving and maintaining compliance can enhance trust.
5. Response time to issues
Measure the time it takes for your organization to respond to customer complaints or issues. Quick and effective responses demonstrate trustworthiness.
6. Ethical behavior index
Develop an index to measure ethical behavior within your organization, considering factors like ethical training completion rates and incident reports.
7. Trust index
Create a trust index based on stakeholder feedback, combining ratings related to transparency, reliability, accountability, and other trust-related factors.
How can you use trust metrics for ongoing development?
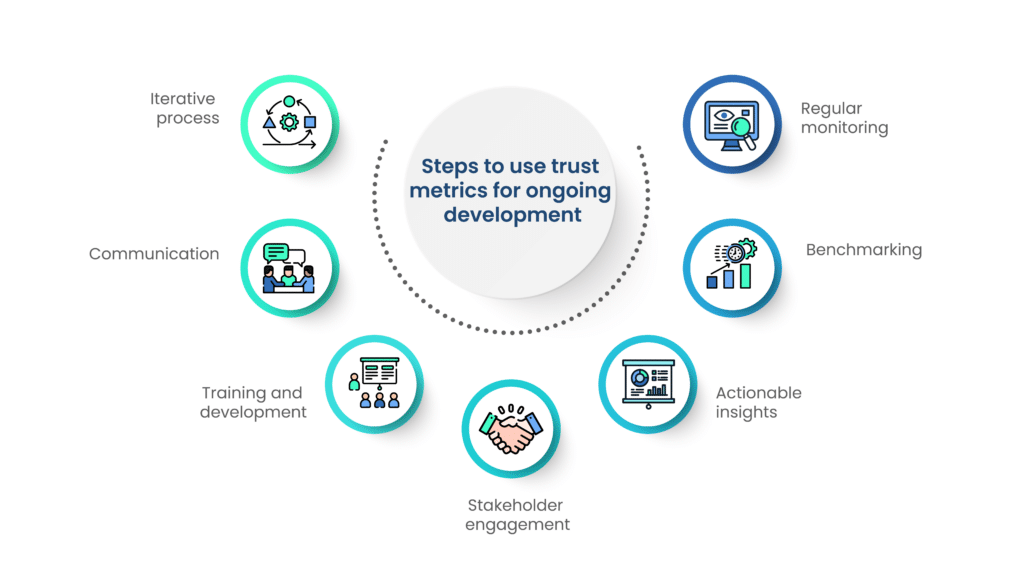
Continuous improvement is essential for maintaining and enhancing trust. Here’s how to use trust metrics to guide your organization’s ongoing development:
- Regular monitoring: Continuously monitor the KPIs related to trust to detect trends and areas needing improvement.
- Benchmarking: Compare your organization’s trust metrics to industry standards and best practices to identify areas where you may lag or excel.
- Actionable insights: Use the data from trust metrics to identify specific actions that can be taken to improve trustworthiness. For example, if data breach incidents are high, invest in cybersecurity improvements.
- Stakeholder engagement: Engage with stakeholders to discuss the trust metrics and involve them in the improvement process. Their insights can be invaluable.
- Training and development: Invest in training and development programs to enhance competence and ethical behavior among employees.
- Communication: Communicate your organization’s commitment to trustworthiness and the steps being taken to improve. Transparency in improvement efforts can build trust.
- Iterative process: Understand that trust is built over time, and improvements should be an ongoing, iterative process. Regularly revisit your trust metrics to ensure progress.
In conclusion, assessing, measuring, and improving the trustworthiness of an organization requires a holistic approach that considers stakeholder feedback, transparent operations, ethical behavior, and data-driven KPIs. By continuously monitoring and acting on trust metrics, organizations can foster a culture of trust and strengthen their relationships with stakeholders.
Conclusion
In the dynamic world of business, trust is the ultimate game-changer, propelling companies to greatness. We explored the vital link between trust and GRC, recognizing that trust is not just a virtue but a strategic imperative.
Assessing trustworthiness is a continuous journey, relying on stakeholder feedback, transparency, compliance, and ethical conduct. Trust metrics guide ongoing development, ensuring trust remains paramount.
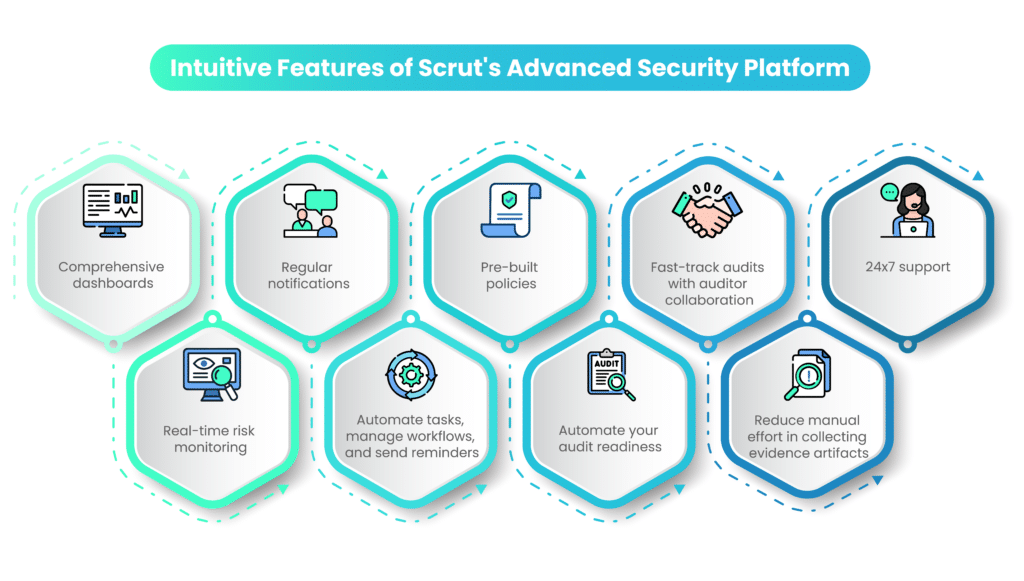
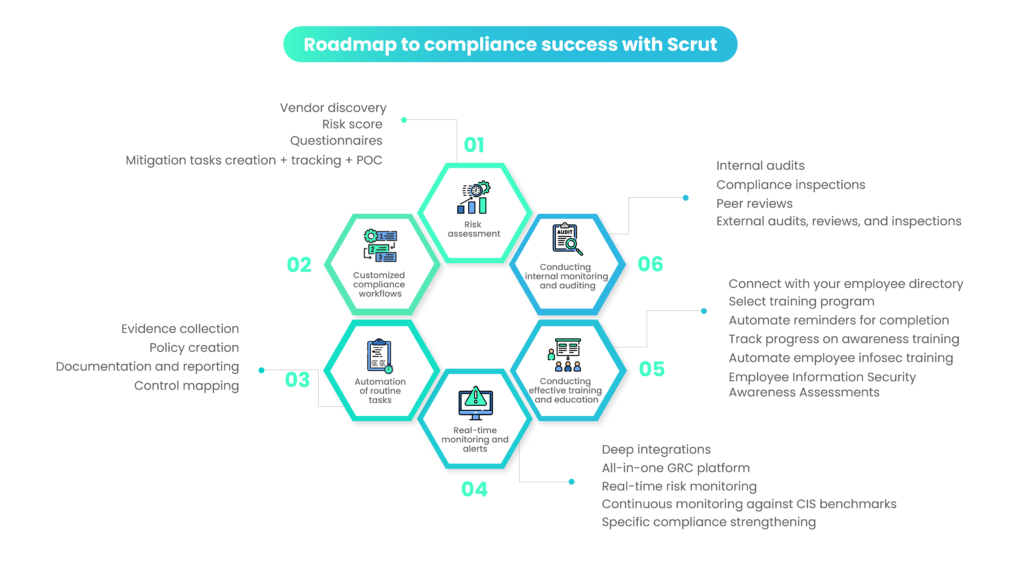
Are you eager to strengthen trust, enhance compliance, and bolster security within your organization? Scrut offers a range of comprehensive GRC solutions designed to empower your business.
Take the proactive step towards a more secure and trustworthy future – explore our GRC offerings with Scrut today!
FAQs
Governance, Risk Management, and Compliance (GRC) is a holistic framework that organizations use to ensure ethical conduct, regulatory adherence, and sustainable operations. GRC is crucial because it establishes a foundation of trust, ethical behavior, and responsible business practices. It helps companies maintain a good reputation, adhere to laws and regulations, and mitigate risks effectively.
GRC is a holistic framework that organizations use to ensure ethical conduct, regulatory adherence, and sustainable operations. GRC is crucial because it establishes a foundation of trust, ethical behavior, and responsible business practices. It helps companies maintain a good reputation, adhere to laws and regulations, and mitigate risks effectively.
GRC contributes to building customer trust by ensuring ethical conduct, transparent operations, and adherence to regulations. When customers see that a company is committed to responsible practices and protecting their interests, they are more likely to trust the brand. GRC helps in maintaining consistency, reliability, and accountability, which are essential for customer trust.
Technology plays a significant role in Scrut’s GRC solutions. It enables automation of compliance processes, real-time risk monitoring, data analytics, and reporting. This technology-driven approach enhances efficiency, reduces human error, and provides organizations with the tools needed to adapt to evolving regulatory landscapes.
Scrut’s GRC solutions include features that help organizations stay up-to-date with changing regulations. These solutions often include automated alerts, compliance monitoring, and access to resources that provide insights into evolving regulatory requirements, enabling organizations to adapt proactively.