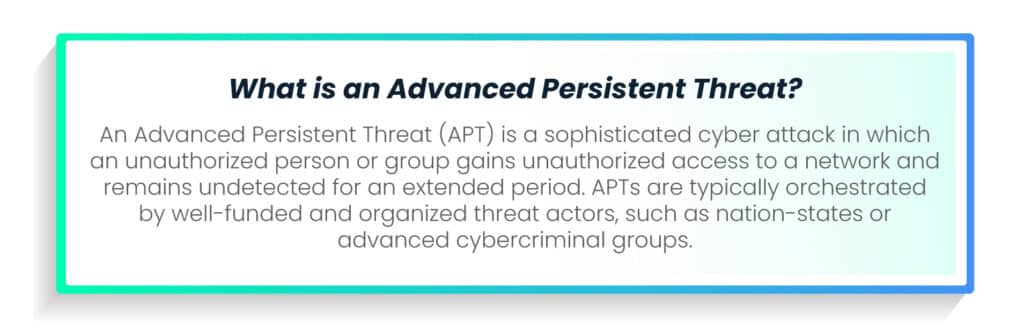
In today’s interconnected digital landscape, organizations across industries face an ever-growing array of cyber threats and operational disruptions.
The financial sector, in particular, stands as a prime target for cybercriminals seeking to exploit vulnerabilities and wreak havoc on critical infrastructure. Financial institutions grapple with the imperative to fortify their defenses and ensure robust operational resilience.
Amidst this landscape of evolving risks and regulatory challenges, the European Union has introduced a groundbreaking solution: the Digital Operational Resilience Act (DORA).
DORA emerges as a pivotal solution to address these pressing challenges.
It represents a transformative regulatory framework designed to equip financial entities with the tools and mechanisms necessary to withstand, respond to, and recover from cyber threats and ICT-related disruptions.
Through its comprehensive approach to managing operational resilience, DORA heralds a new era of cybersecurity regulation, empowering financial institutions to navigate the complexities of the digital landscape with confidence and resilience.
Definition and scope of DORA
The Digital Operational Resilience Act (DORA) is a significant EU financial regulation aimed at bolstering the operational resilience of organizations operating within the financial sector.
Indeed, DORA holds profound significance for financial institutions, including banks, investment firms, insurance companies, and crypto-asset service providers. It represents a paradigm shift in regulatory focus from solely managing financial risks to addressing operational resilience comprehensively. Compliance with DORA ensures that financial entities can effectively manage and mitigate cyber threats, safeguarding the stability and integrity of the financial system.
DORA mandates organizations to fortify their information and communication technology (ICT) capabilities to withstand, respond to, and recover from cyber threats and ICT-related disruptions. Its scope extends beyond traditional financial regulations, requiring comprehensive management of operational resilience across the entire ICT infrastructure.
This encompasses a wide range of organizations, including financial institutions such as banks, credit unions, insurance companies, investment firms, and stock exchanges. Additionally, critical infrastructure operators like energy providers, telecommunications companies, transportation systems, healthcare organizations, and government agencies fall under the purview of DORA.
Service providers such as cloud service providers, managed security service providers (MSSPs), data centers, and payment processors are also covered. Regulatory bodies and supervisory authorities responsible for financial regulation, ICT oversight, and cybersecurity governance are included. Moreover, other entities, such as corporations with significant ICT infrastructure, organizations handling sensitive data, and those involved in e-commerce and digital transactions, must adhere to DORA’s requirements for operational resilience across their ICT infrastructure.
Understanding DORA
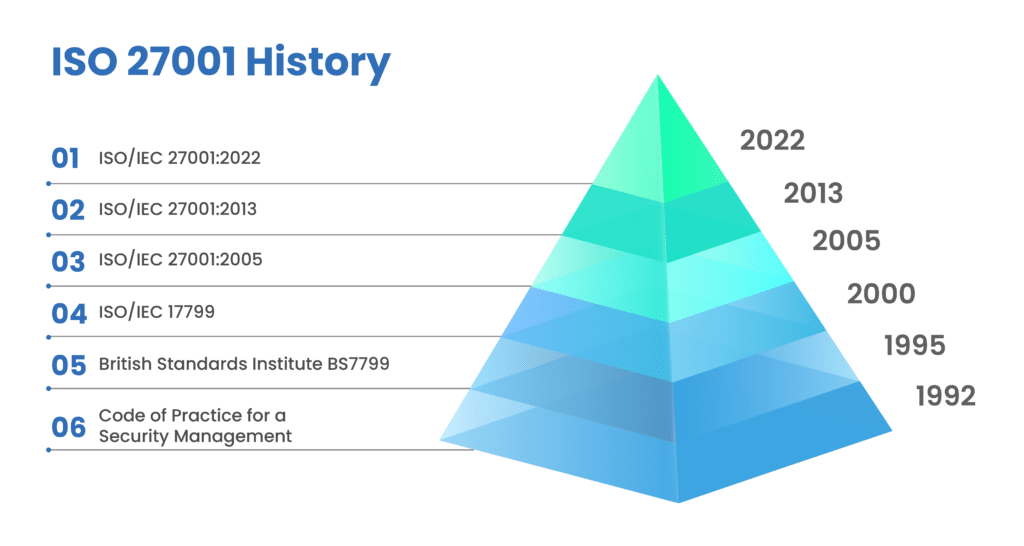
The Digital Operational Resilience Act (DORA) emerged as a response to the growing threats posed by cyberattacks and ICT-related disruptions in the financial sector.
With the increasing reliance on digital technologies, regulators recognized the need for comprehensive legislation to safeguard financial institutions and their customers from potential harm.
DORA represents a significant evolution from previous financial regulations, which primarily focused on managing operational risks through capital allocation. Unlike its predecessors, DORA addresses the entire spectrum of operational resilience, emphasizing proactive measures to prevent, detect, contain, and recover from cyber threats and disruptions.
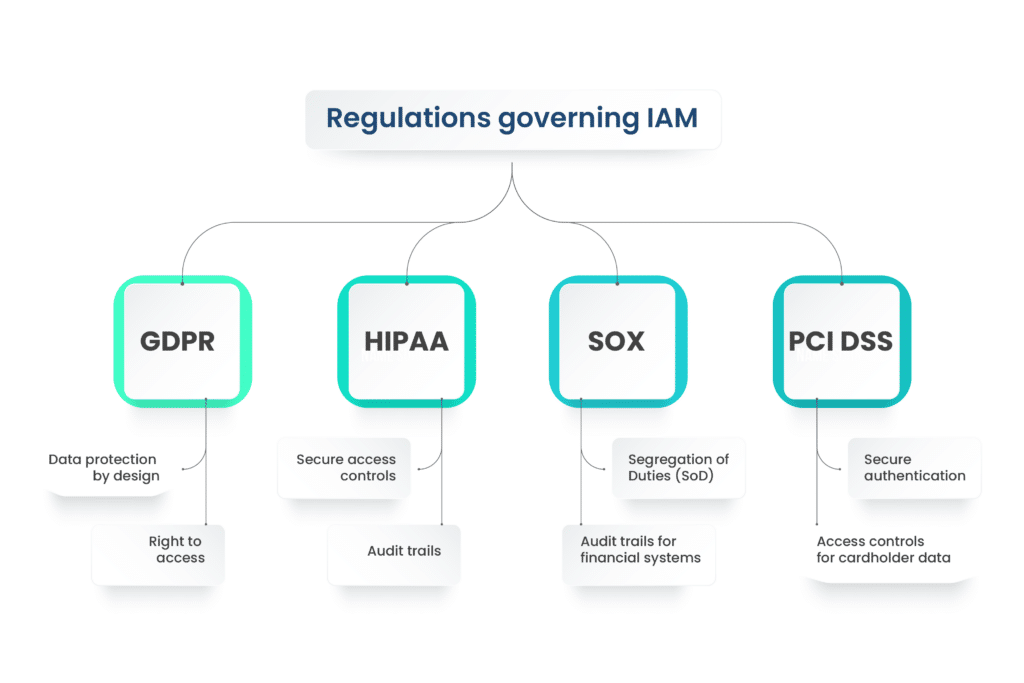
DORA establishes standardized security requirements for the network and information systems of companies and organizations within the financial sector, as well as critical third-party providers offering ICT services like cloud platforms or data analytics.
| How do DORA and GDPR differ? DORA emphasizes reporting ICT-related incidents, while GDPR focuses on reporting personal data breaches. While both entail reporting requirements, their application varies, reflecting their distinct regulatory scopes. |
DORA timeline and implementation
The DORA compliance journey begins with a clear understanding of the regulatory timeline. The official start date for DORA compliance initiatives commenced on January 17, 2023. This marked the initiation of a two-year implementation period for affected entities to align their operations with the regulatory requirements outlined in DORA.
Implementation period details
During the implementation period, organizations subject to DORA regulations must undertake comprehensive efforts to ensure compliance. This involves assessing existing operational frameworks, identifying gaps in resilience capabilities, and developing strategies to address these deficiencies. Additionally, it provides an opportunity for organizations to establish robust compliance mechanisms and integrate them seamlessly into their operations.
Preparing for compliance milestones
As the compliance deadline approaches, organizations must prioritize key milestones to ensure timely and effective adherence to DORA regulations. This includes finalizing compliance strategies, conducting thorough risk assessments, implementing necessary infrastructure enhancements, and providing comprehensive training to employees. By proactively preparing for compliance milestones, organizations can minimize disruptions and position themselves for successful DORA compliance.
DORA compliance deadlines
Organizations subject to DORA compliance face critical deadlines for implementation and adherence to its regulatory framework. With a two-year implementation period starting in January 2023, organizations must diligently prepare to meet compliance requirements by the deadline of January 17, 2025.
Understanding and adhering to these compliance deadlines is imperative for financial institutions to avoid penalties and ensure operational resilience in the face of evolving cyber threats.
DORA – Key components and objectives
At its core, DORA aims to enhance the operational resilience of financial institutions and other impacted organizations. By setting clear objectives and standards, DORA seeks to ensure the stability and security of the financial sector in the face of evolving cyber threats.
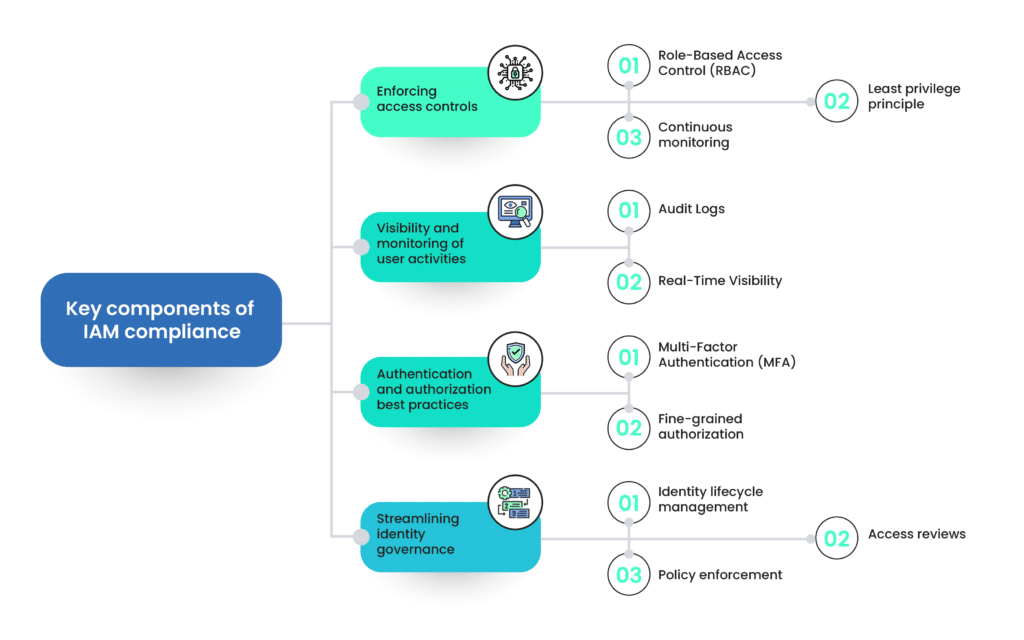
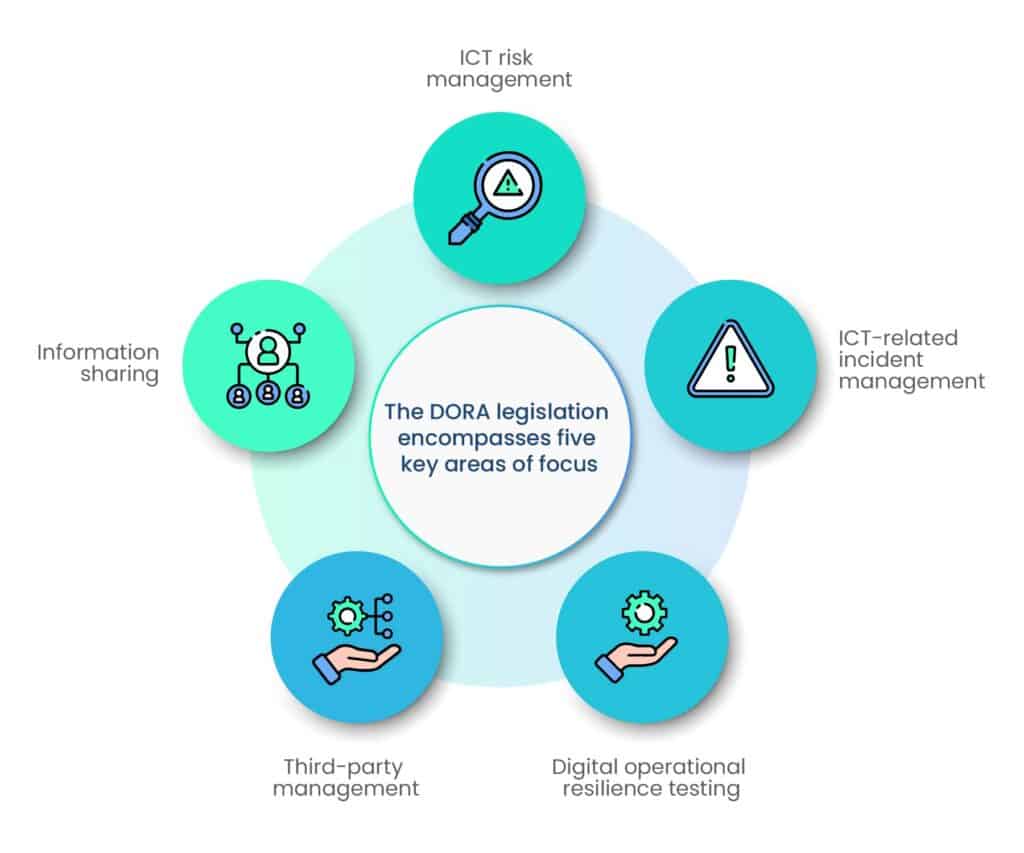
Its key components include:
- Provisions for third-party risk monitoring
- Rules for ICT risk management,
- Incident reporting requirements,
- Operational resilience testing.
The DORA legislation encompasses five key areas of focus:
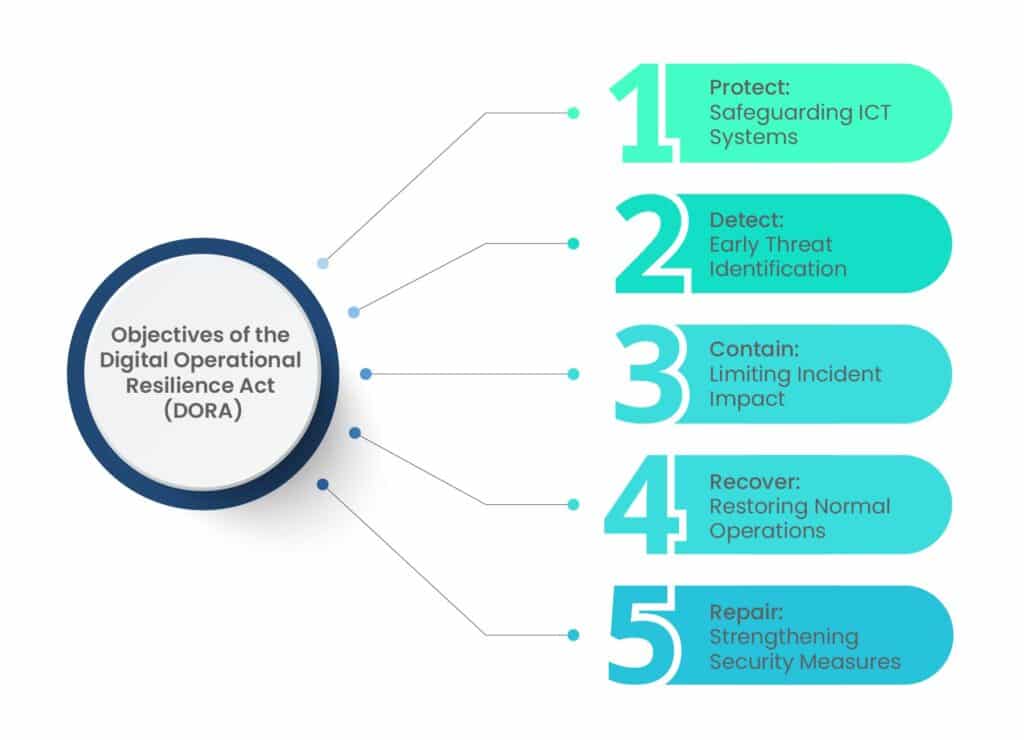
The objectives of DORA are to enhance the cyber resilience of financial entities, ensure the continuity of essential services, mitigate systemic risks, and promote collaboration among stakeholders to create a more secure and resilient financial ecosystem.
Here’s an elaboration on each of the objectives:
Exploring DORA’s regulatory framework
DORA’s regulatory framework is designed to establish comprehensive guidelines for operational resilience within the financial sector and other relevant industries. It outlines the necessary measures and procedures to protect against cyber threats and ICT-related disruptions, emphasizing proactive risk management and compliance.
DORA principles and requirements
At the heart of DORA are core principles and requirements aimed at strengthening operational resilience. These include mandates for robust risk assessment and management practices, incident reporting protocols, and stringent compliance monitoring.
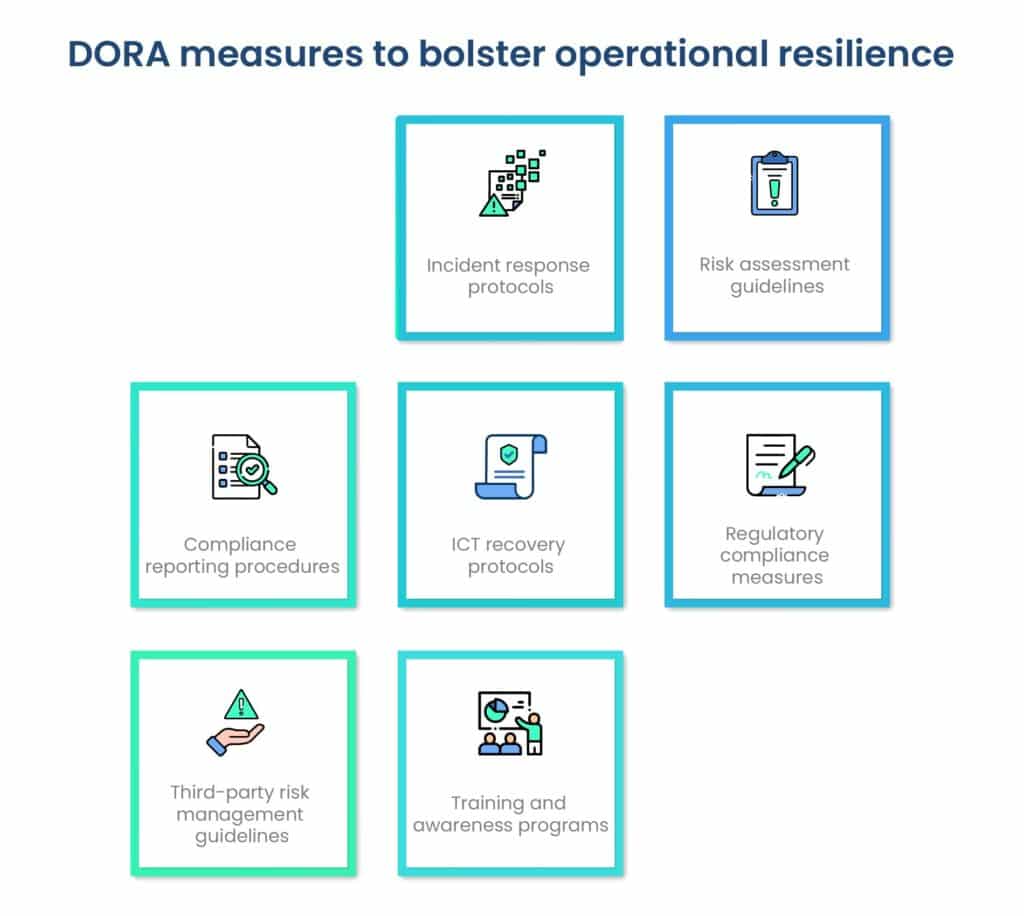
By adhering to these principles, organizations can better safeguard their operations and mitigate potential risks. The protocols, guidelines, and procedures within DORA’s regulatory framework encompass a range of specific measures aimed at bolstering operational resilience:
- Incident response protocols: Detailed procedures for promptly identifying, reporting, and responding to cybersecurity incidents, including protocols for containment, eradication, and recovery.
- Risk assessment guidelines: Comprehensive guidelines for conducting thorough risk assessments to identify potential vulnerabilities and threats to ICT systems, ensuring organizations can proactively address emerging risks.
- Compliance reporting procedures: Clear procedures for compiling and submitting compliance reports to regulatory authorities, outlining the required documentation and reporting timelines to ensure transparency and accountability.
- ICT recovery protocols: Protocols for recovering and restoring ICT systems following a cyber incident or disruption, including steps for data recovery, system restoration, and post-incident analysis.
- Regulatory compliance measures: Specific measures for ensuring ongoing compliance with DORA requirements, including regular audits, internal controls, and governance structures to maintain adherence to regulatory standards.
- Third-party risk management guidelines: Guidelines for assessing and managing risks associated with third-party service providers, including due diligence procedures, contractual obligations, and monitoring mechanisms to mitigate potential risks.
- Training and awareness programs: Procedures for implementing training and awareness programs to educate employees on cybersecurity best practices, raise awareness of potential threats, and promote a culture of cybersecurity awareness within the organization.
Key Requirements for Financial Institutions under EU Regulation
- Mapping and Testing: Financial institutions identify and manage operational risks through comprehensive mapping and testing of critical business services.
- Outsourcing Measures: Financial institutions implement risk management measures to address risks associated with outsourcing critical functions or services.
- Incident Reporting: Financial institutions report incidents impacting service continuity or posing threats to the financial system.
- Cybersecurity Measures: Financial institutions adopt effective cybersecurity measures to prevent cyber threats and data breaches.
- Risk Management Framework: Financial institutions establish integrated risk management frameworks aligned with business strategy.
- Governance and Oversight: Clear lines of responsibility and oversight ensure operational resilience, with the board overseeing strategy.
- Business Continuity Planning: Comprehensive plans ensure the continuity of critical services during disruptions.
- Testing and Training: Regular testing and staff training enhance preparedness for operational disruptions.
DORA’s implications on operational resilience
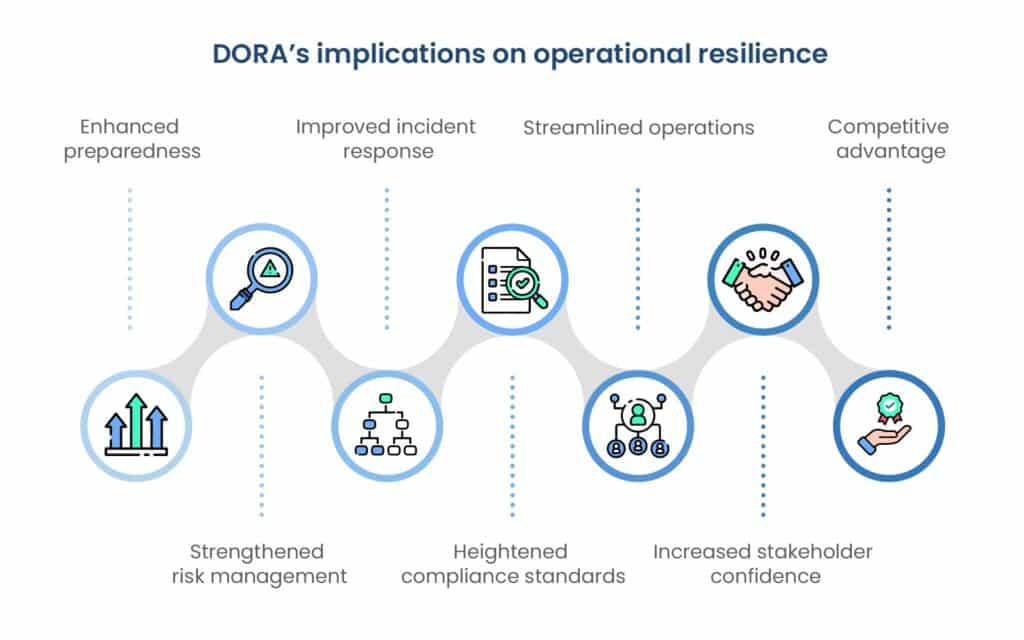
DORA’s implications for operational resilience are far-reaching, as they demand that organizations adopt a proactive and comprehensive approach to risk management.
- Enhanced preparedness: DORA mandates organizations to develop robust strategies and mechanisms to withstand, respond to, and recover from cyber threats and ICT-related disruptions effectively.
- Strengthened risk management: By emphasizing proactive risk identification and mitigation, DORA encourages organizations to adopt comprehensive risk management practices, reducing vulnerabilities and enhancing operational resilience.
- Improved incident response: DORA requires organizations to establish clear protocols and procedures for incident response, ensuring swift and effective actions to minimize the impact of cybersecurity incidents on operations.
- Heightened compliance standards: Compliance with DORA necessitates adherence to stringent regulatory standards, fostering a culture of compliance and accountability within organizations.
- Streamlined operations: Implementing DORA-compliant practices can lead to more efficient and streamlined operations, as organizations prioritize resilience and risk management in their day-to-day activities.
- Increased stakeholder confidence: Demonstrating compliance with DORA signals to stakeholders, including customers, partners, and regulators, that an organization is committed to maintaining operational resilience and safeguarding sensitive information.
- Competitive advantage: Organizations that successfully adhere to DORA’s requirements may gain a competitive edge by positioning themselves as reliable and resilient partners in the marketplace.
DORA and financial entities
DORA’s scope extends across various sectors within the financial industry, impacting a wide array of entities. From traditional banks and investment firms to insurance companies and crypto-asset service providers, DORA’s regulatory framework applies to a diverse range of financial institutions. Regardless of size or specialization, all entities operating within the financial sector are subject to the compliance requirements set forth by DORA.
The following is expressly mentioned in the standard:
“…The regulation covers a range of financial entities regulated at Union level namely credit institutions, payment institutions, electronic money institutions, investment firms, crypto-asset service providers, central securities depositories, central counterparties, trading venues, trade repositories, managers of alternative investment funds and management companies, data reporting service providers, insurance and reinsurance undertakings, insurance intermediaries, reinsurance intermediaries and ancillary insurance intermediaries, institutions for occupational retirement pensions, credit rating agencies, statutory auditors and audit firms, administrators of critical benchmarks and crowdfunding service providers”.
For banks, investment firms, insurance companies, and other financial entities, DORA represents a significant shift in regulatory focus. The Act imposes stringent requirements aimed at enhancing operational resilience and mitigating cyber threats across the financial sector. Institutions must adapt their existing practices to comply with DORA’s mandates, which encompass areas such as risk management, incident reporting, and third-party oversight.
DORA’s implications on financial institutions
- Increased compliance costs: Financial institutions will need to allocate additional resources to meet the new regulatory requirements, potentially resulting in higher compliance costs.
- Enhanced regulatory oversight: Supervisory authorities will have expanded powers to monitor and evaluate financial institutions’ operational resilience, leading to increased regulatory scrutiny and more thorough examinations.
- Changes in business practices: Financial institutions may need to adapt their business practices to align with the regulation, such as revising outsourcing agreements, strengthening cybersecurity measures, and enhancing business continuity plans.
- Emphasis on risk management: The regulation places a greater emphasis on risk management, prompting financial institutions to establish more robust frameworks and procedures for identifying, assessing, and mitigating risks.
- Improved operational resilience: Ultimately, the goal of the regulation is to enhance the operational resilience of financial institutions, enabling them to better withstand and respond to various threats and disruptions, including cyberattacks and IT failures.
DORA’s reach extending to third-party service providers
DORA’s impact extends beyond traditional financial institutions to encompass third-party service providers offering IT and cybersecurity services. These entities play a critical role in supporting the digital infrastructure of financial organizations, making them integral to the overall operational resilience of the sector.
As such, DORA’s regulatory framework extends its reach to ensure that third-party service providers adhere to the same standards of cybersecurity and operational resilience as their financial counterparts.
Regulations for third-party IT and cybersecurity services:
Under DORA, third-party IT and cybersecurity service providers are subject to specific regulations aimed at enhancing the security and resilience of financial systems. These regulations mandate:

By holding third-party providers accountable for maintaining high standards of cybersecurity, DORA aims to mitigate the risks associated with outsourcing critical IT functions.
| Which entities are excluded from DORA? Article 2(3) outlines exemptions, including Managers of Alternative Investment Funds under Article 3(2) of Directive 2011/61/EU (AIFMD), and Insurance and Reinsurance Undertakings as detailed in Article 4 of Directive 2009/138/EC (Solvency II). |
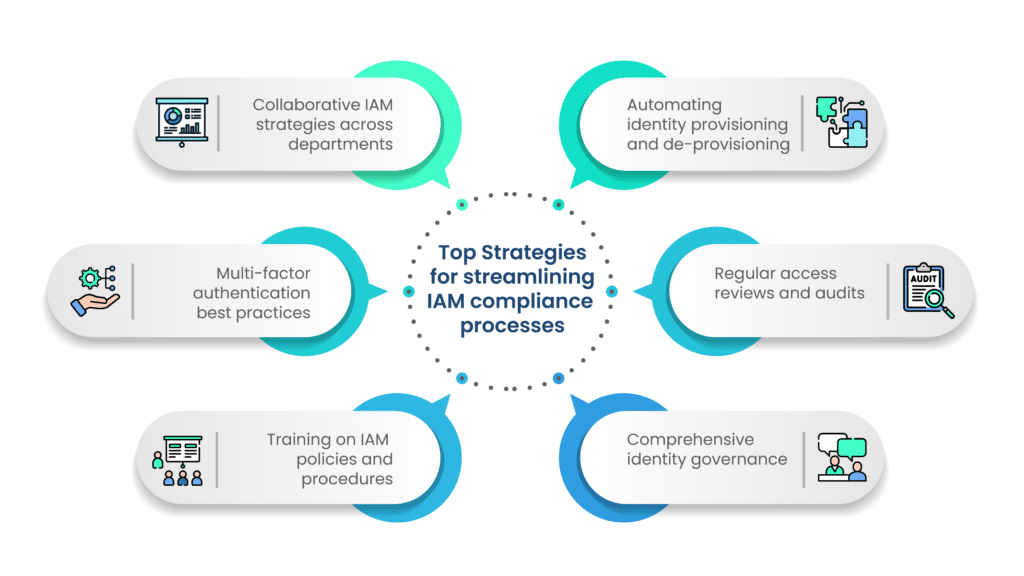
Collaborative approaches for comprehensive compliance
To achieve comprehensive compliance with DORA, financial institutions and third-party service providers must adopt collaborative approaches to cybersecurity and operational resilience.
This involves establishing clear communication channels, sharing relevant information, and aligning strategies to address common cybersecurity challenges.
By fostering collaboration between financial institutions and their third-party partners, DORA promotes a unified approach to cybersecurity that strengthens the resilience of the entire financial ecosystem.
Consequences of non-compliance with DORA
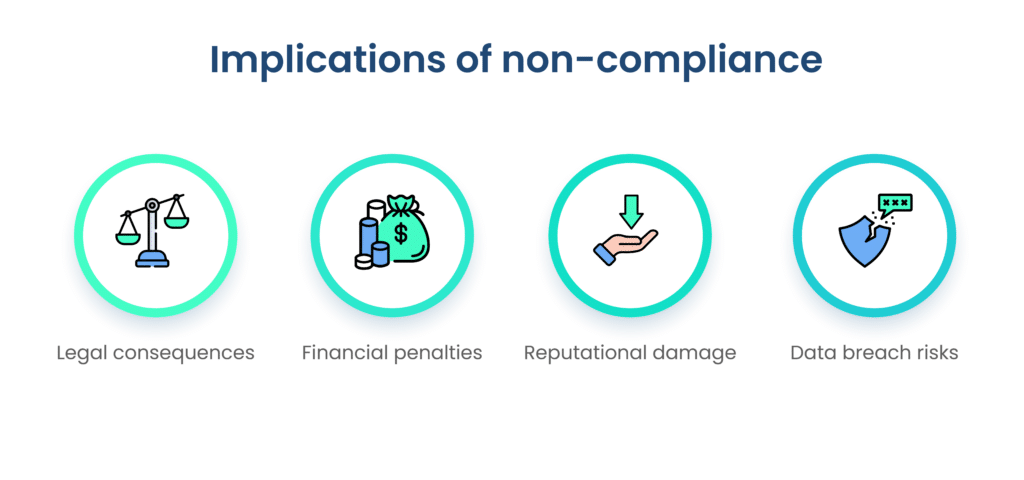
Penalties: Non-compliance with DORA regulations can result in a range of penalties, varying in severity depending on the nature and extent of the violation. These penalties may include fines, sanctions, or legal action imposed by regulatory authorities.
Financial entities found in breach of DORA requirements may face financial penalties proportional to the severity of the violation, with fines potentially reaching significant amounts. Additionally, regulatory authorities may impose remedial measures or require compensation for damages incurred as a result of non-compliance.
Legal consequences: Financial entities failing to comply with DORA regulations may face legal consequences that extend beyond financial penalties. Depending on the severity of the violation and its impact on stakeholders, regulatory authorities may resort to legal action, including public reprimands, withdrawal of authorization, or criminal charges against responsible individuals or entities.
Moreover, non-compliance with DORA requirements can damage the reputation of financial institutions, erode customer trust, and adversely affect business operations.
Costs associated with data breaches: The costs associated with data breaches have been steadily rising, posing significant financial risks to organizations that fail to comply with DORA regulations. Data breaches not only result in direct financial losses due to theft or misuse of sensitive information but also incur expenses related to incident response, remediation, and regulatory fines. Moreover, the long-term impact of reputational damage and loss of customer trust can further escalate the costs of data breaches for non-compliant organizations.
Financial implications for non-compliant organizations: Non-compliance with DORA regulations can have severe financial implications for organizations, including financial institutions and third-party service providers. Regulatory fines imposed for non-compliance can amount to substantial sums, potentially jeopardizing the financial stability and profitability of affected entities. Additionally, the costs associated with legal proceedings, remediation efforts, and operational disruptions further exacerbate the financial burden on non-compliant organizations, highlighting the importance of proactive compliance measures to mitigate financial risks.
Long-term reputational damage: One of the most significant costs of non-compliance with DORA regulations is the long-term reputational damage suffered by organizations. Incidents of non-compliance, data breaches, or cybersecurity incidents can tarnish the reputation of financial institutions and third-party service providers, eroding customer trust and loyalty. The negative publicity resulting from such incidents can have lasting effects on brand perception and market competitiveness, leading to reduced customer acquisition, retention, and revenue generation. Therefore, mitigating the risk of reputational damage through compliance with DORA regulations is essential for preserving the long-term viability and success of organizations operating in the financial sector.

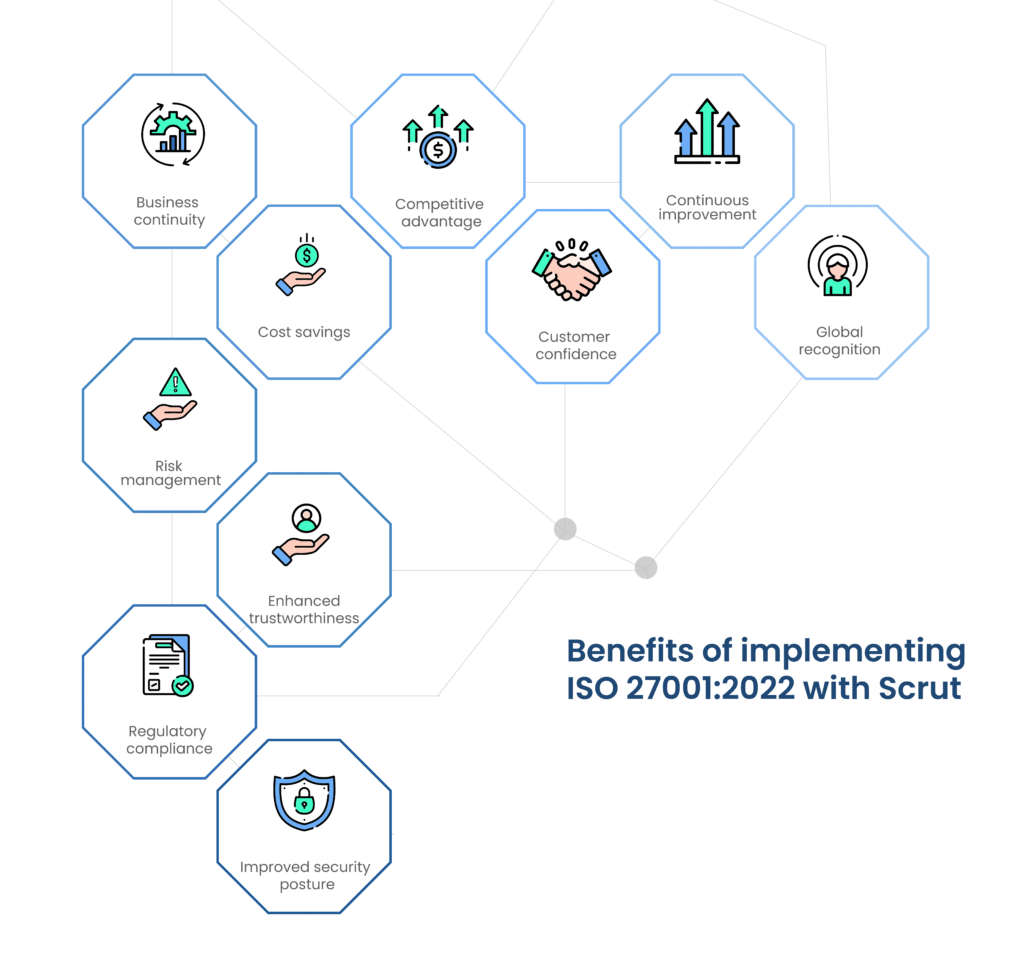
Benefits of DORA compliance
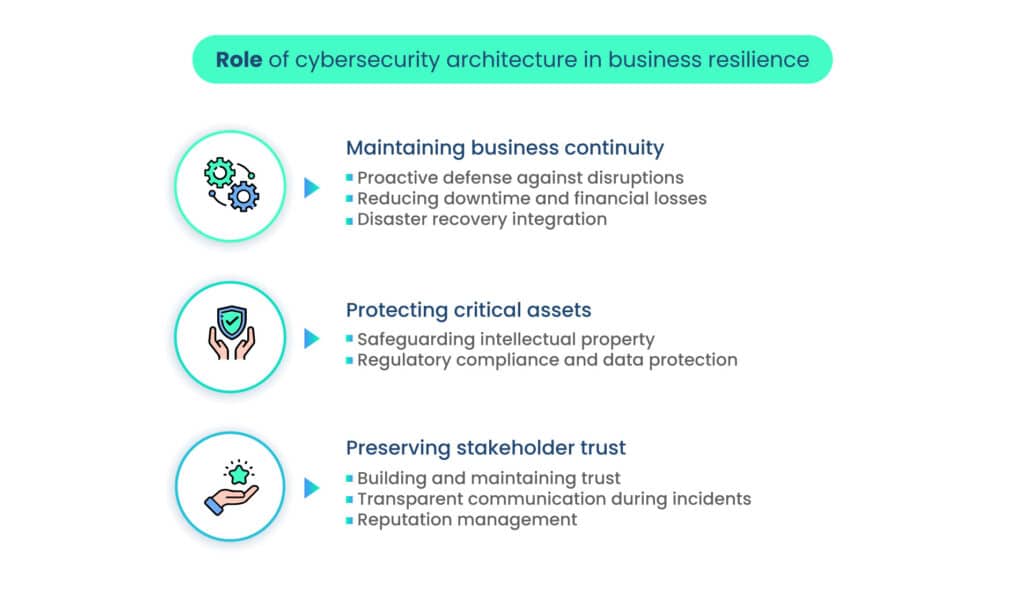
Compliance with DORA regulations not only enhances operational resilience and customer trust but also contributes to long-term market stability and security in the financial sector.
Improving operational resilience
- Compliance with DORA regulations establishes robust frameworks for managing and mitigating cyber risks and ICT-related disruptions.
- Proactive measures to protect, detect, respond to, and recover from threats strengthen the organization’s ability to maintain critical business functions and services.
- Enhanced operational resilience minimizes the impact of disruptions, improves organizational agility, competitiveness, and sustainability.
Enhancing customer trust and stakeholder confidence
- DORA compliance demonstrates a commitment to cybersecurity, data protection, and operational excellence, enhancing customer trust and stakeholder confidence.
- Safeguarding sensitive information, protecting customer assets, and ensuring the integrity of financial services fosters stronger relationships with customers, partners, investors, and regulatory authorities.
- Building trust strengthens brand reputation, enhances market credibility, and facilitates business growth in competitive and regulated environments.
Long-term market stability and security
- Compliance with DORA regulations promotes a culture of risk awareness, resilience, and accountability across the financial ecosystem.
- Establishing consistent standards and practices for managing cyber risks reduces systemic vulnerabilities, mitigates systemic risks, and enhances overall market integrity and stability.
- A more secure and resilient financial sector fosters investor confidence, promotes economic growth, and safeguards the interests of consumers, businesses, and society, ensuring sustainable financial development and prosperity.
Preparing for DORA compliance
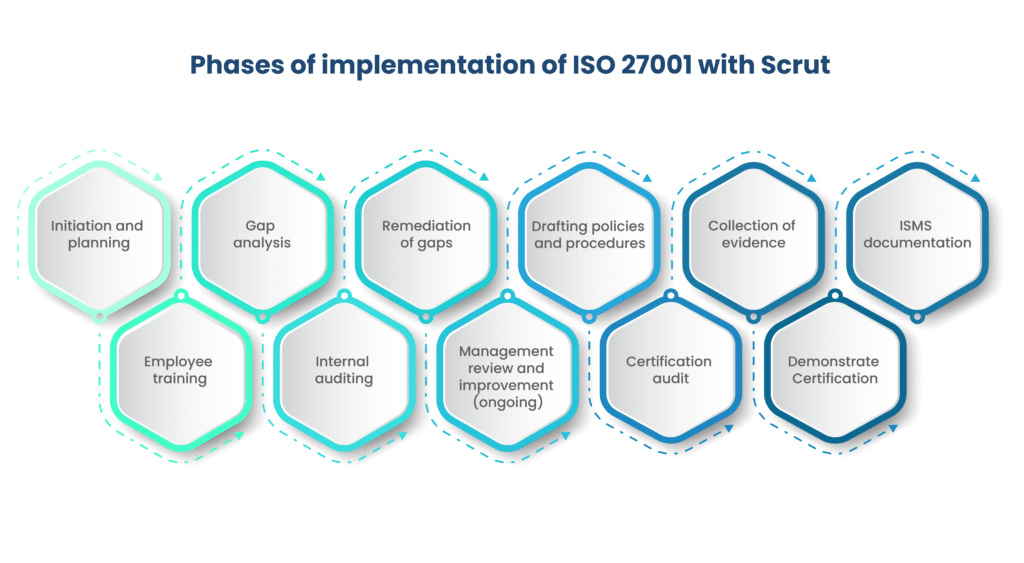
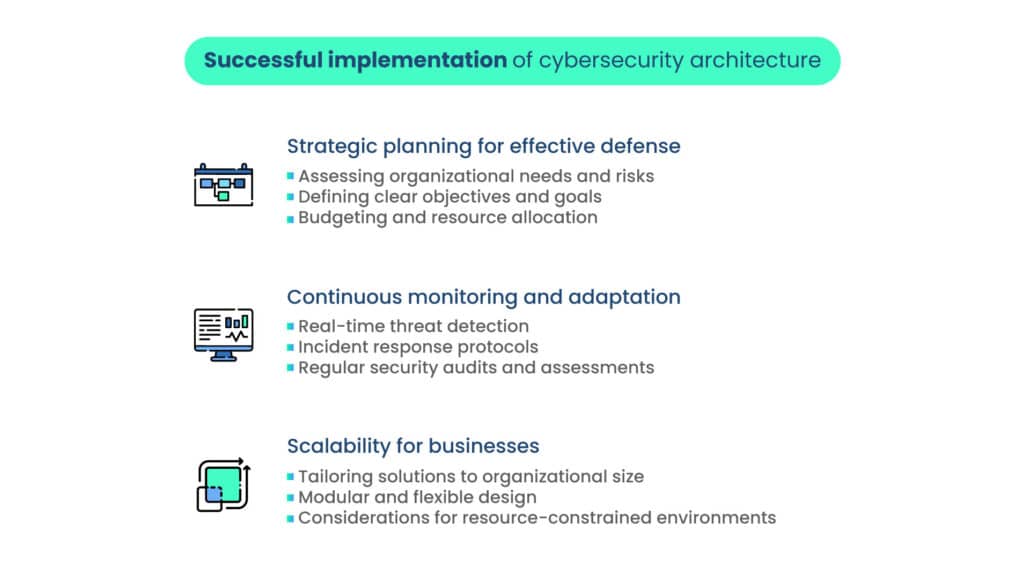
Preparing for DORA compliance requires organizations to undertake several essential steps to ensure readiness and effectiveness in meeting regulatory requirements.
Steps to prepare for DORA compliance:
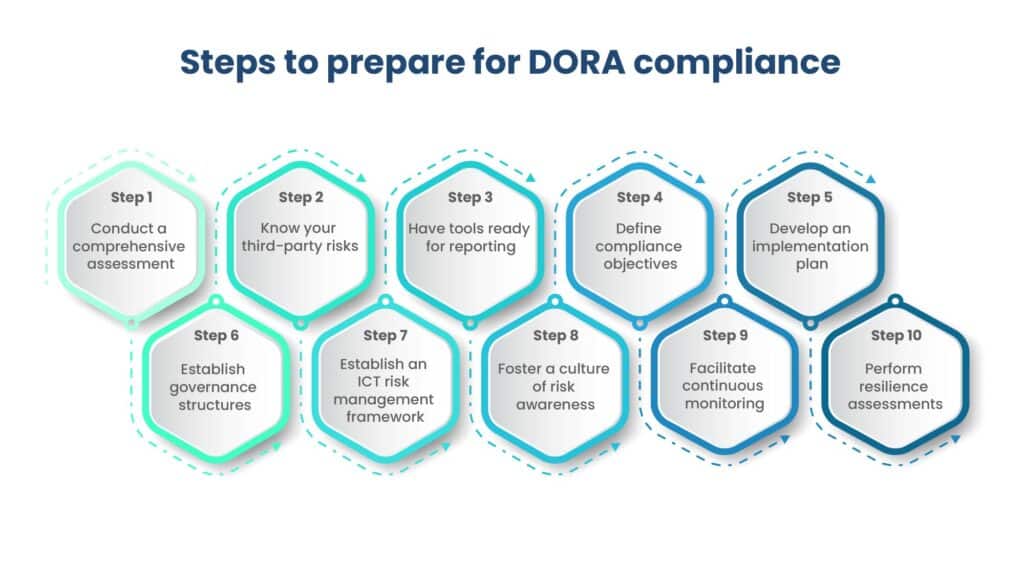
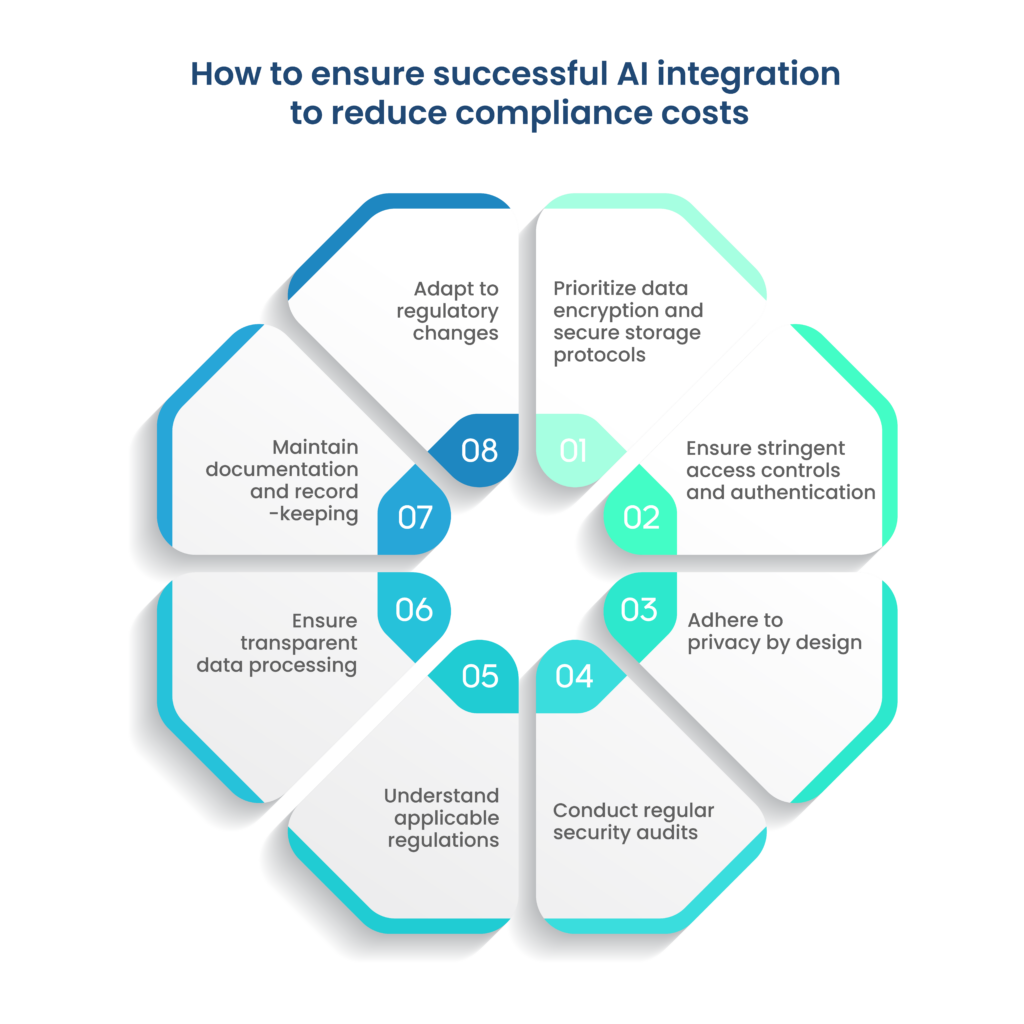
- Conduct a comprehensive assessment: Begin by assessing existing ICT capabilities, identifying vulnerabilities, and gaps in operational resilience.
- Know your third-party risks: DORA will require third-party risk to be managed as a crucial part of overall ICT risk management, ensuring that providers assist your firm during cybersecurity incidents and adhere to stricter security standards. Consequently, organizations must consistently assess and monitor these relationships to promptly detect any issues and oversee providers critical to the supply chain.
- Have tools ready for reporting: Ensure readiness for reporting under DORA guidelines. Financial institutions must promptly report ICT-related incidents to regulators, including details such as the number of affected users, data loss, geographic impact, economic implications, and additional relevant information. A comprehensive plan should outline employee response procedures during a cyberattack and strategies for restoring operations post-breach.
- Define compliance objectives: Clearly define compliance objectives and priorities based on the assessment findings to guide the implementation process.
- Develop an implementation plan: Create a structured implementation plan with defined timelines, milestones, and responsibilities to ensure organized and effective execution.
- Establish governance structures: Set up robust governance structures, policies, and procedures for managing cyber risks, incident response, and business continuity.
- Establish an ICT risk management framework: Organizations should establish a robust ICT risk management framework within their broader risk management system. Utilizing a platform to develop, implement, and monitor this framework ensures compliance with regulations. Additionally, cybersecurity ratings offer a quantitative evaluation of your organization’s cybersecurity stance, enhancing regulatory adherence.
- Foster a culture of risk awareness: Promote a culture of risk awareness, accountability, and continuous improvement across the organization to enhance compliance efforts.
- Facilitate continuous monitoring: Facilitate ongoing monitoring to stay vigilant about cybersecurity threats. Regular assessment of your security posture enables swift action against emerging risks. This involves consistent scrutiny of third-party vendors to detect changes or vulnerabilities that could affect your organization’s risk landscape.
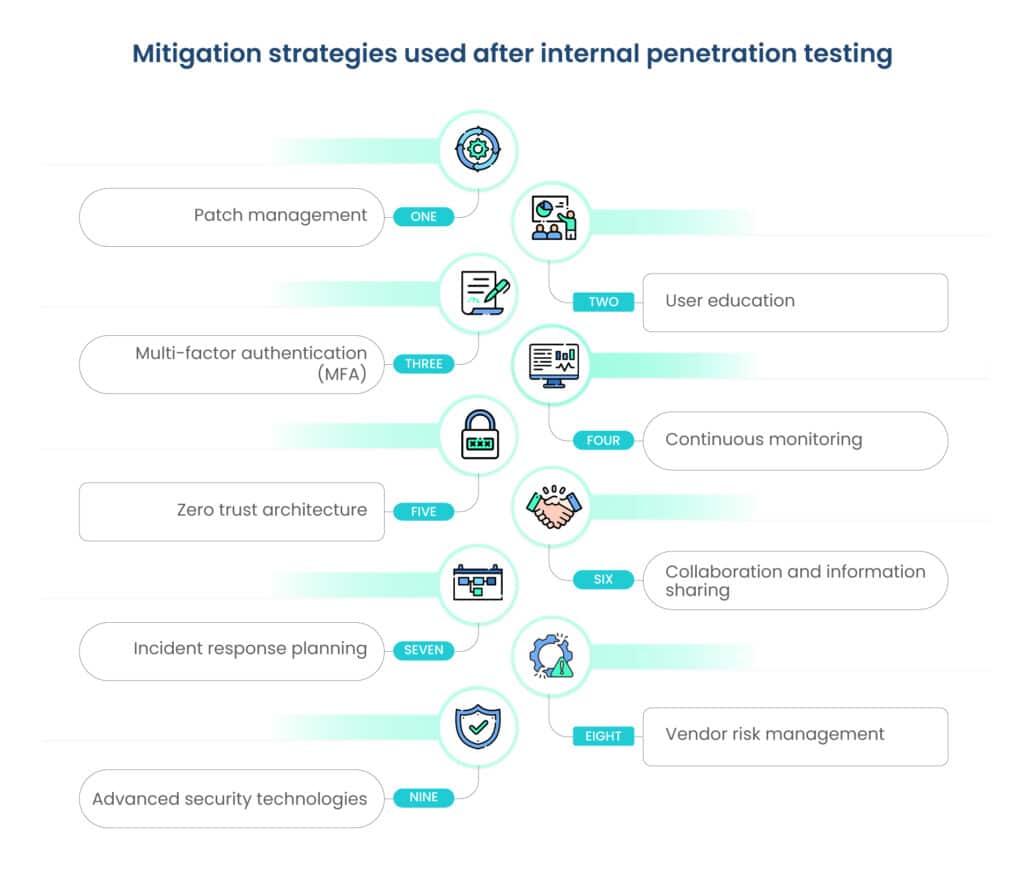
- Perform resilience assessments: Perform routine resilience assessments as mandated by DORA, involving vulnerability assessments, penetration testing, red team exercises, and tabletop drills. This proactive approach aids in identifying and mitigating risks, ensuring seamless business operations during cyber incidents.
| Here are some additional tips for navigating DORA compliance: 1. Ensure board involvement: DORA places cybersecurity responsibility on the board, necessitating enforcement of protocols, policies, and tools. Board alignment is crucial to avoid fines or reputational harm, so ensure management is fully briefed and committed to DORA’s significance. 2. Engage multiple teams: Cybersecurity is now a multifaceted issue, so compliance with DORA should involve more than just the CISO. Involving legal, compliance, and risk management teams from the outset ensures a faster, more efficient DORA compliance process. 3. Start preparation early: Begin planning now to align with DORA regulations. While many firms may have existing policies, this is an opportunity to enhance cybersecurity and bolster resilience in preparation for DORA compliance. |
Employee training programs and their importance
Employee training programs play a crucial role in preparing organizations for DORA compliance by raising awareness, building knowledge, and enhancing skills related to cybersecurity, data protection, and operational resilience.
Training programs should cover a wide range of topics, including identifying cyber threats, adhering to security protocols, responding to incidents, and complying with regulatory requirements.
By investing in comprehensive and ongoing training initiatives, organizations can empower employees to recognize and mitigate cyber risks, foster a security-conscious culture, and contribute to the overall resilience and effectiveness of the organization’s ICT capabilities.
Strategic collaboration across internal teams

Achieving DORA compliance requires strategic collaboration and coordination across internal teams, departments, and functions within the organization. Cross-functional collaboration enables organizations to leverage diverse expertise, perspectives, and resources to address complex compliance challenges, identify innovative solutions, and drive meaningful change.
By fostering communication, alignment, and synergy among compliance, IT, risk management, legal, finance, and other relevant teams, organizations can develop integrated strategies, implement coordinated initiatives, and overcome barriers to compliance more effectively. Strategic collaboration also promotes shared ownership, accountability, and success in achieving organizational goals and objectives related to DORA compliance.
DORA compliance checklist
Ensure compliance with DORA by considering the following essential areas:
- Risk management: Conduct regular risk assessments and establish a comprehensive risk management framework to mitigate operational risks effectively.
- Business continuity planning: Develop and maintain a detailed business continuity plan to address operational disruptions, including cyber threats and data breaches.
- IT and security testing: Regularly test IT systems and security controls to enhance resilience against cyber threats through activities like penetration testing and vulnerability assessments.
- Incident management: Establish an incident management plan to guide your organization’s response to operational incidents, with regular testing and updates.
- Data protection: Protect customer data and comply with data protection regulations like GDPR by implementing appropriate measures and conducting regular audits.
- Outsourcing: Ensure proper oversight of third-party service providers, incorporating contractual provisions for compliance with DORA requirements.
- Reporting: Establish suitable reporting mechanisms to notify management and supervisory authorities of significant operational incidents and risks.
- Compliance monitoring: Monitor compliance with DORA regularly through self-assessments, internal audits, and risk assessments.
Navigating challenges and solutions
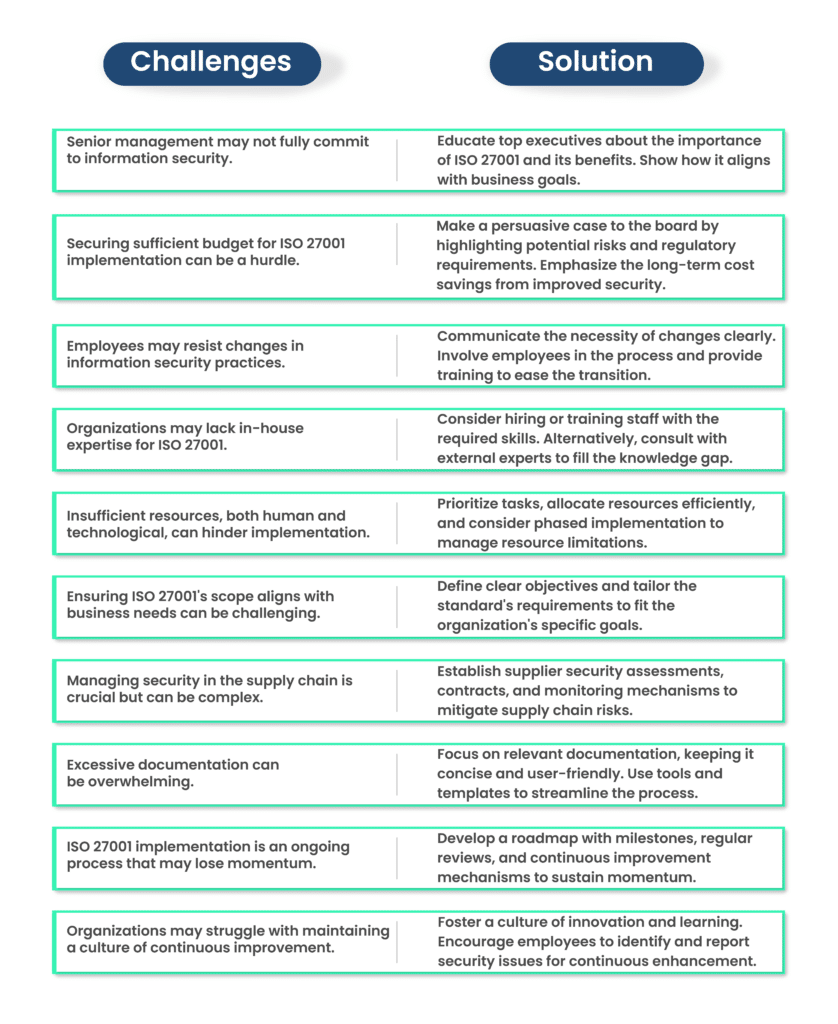
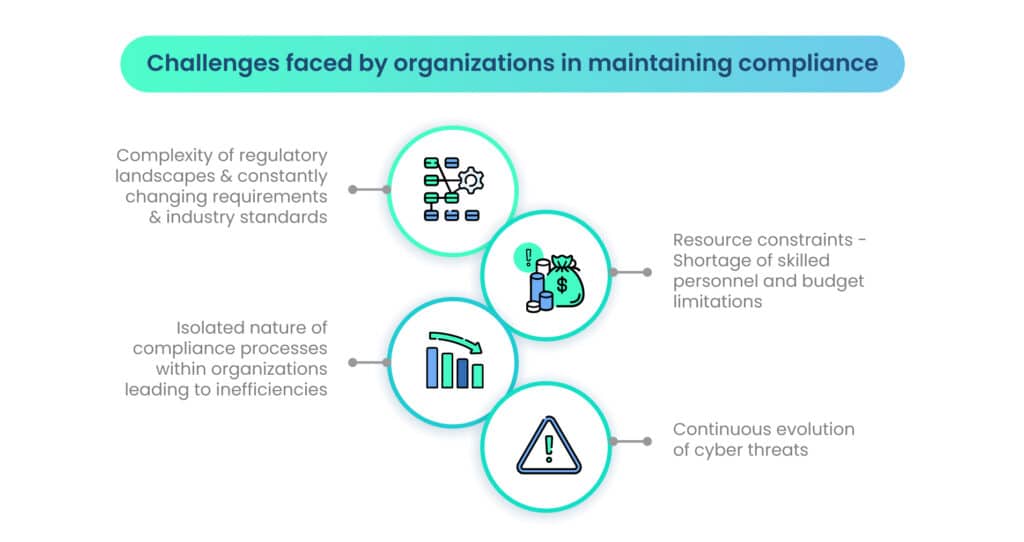
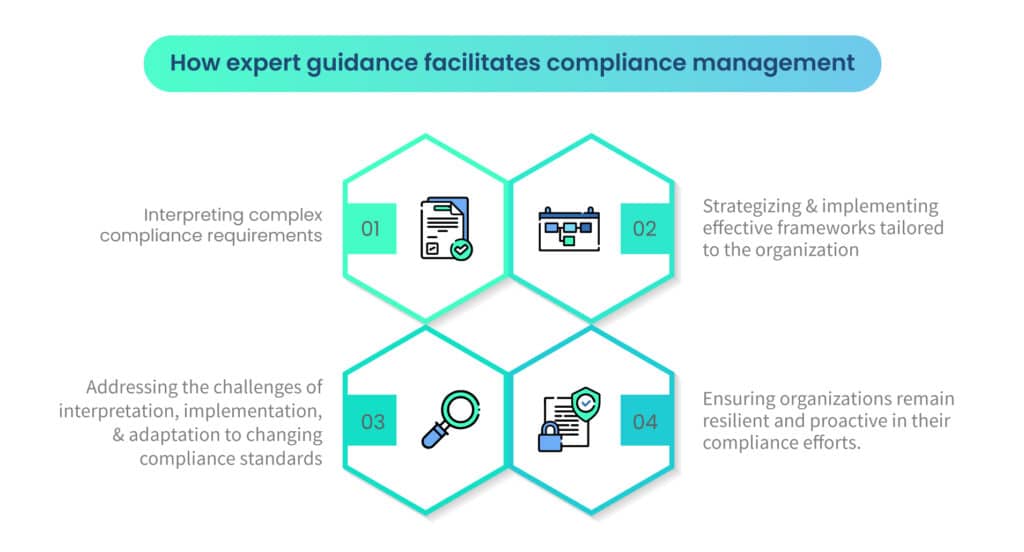
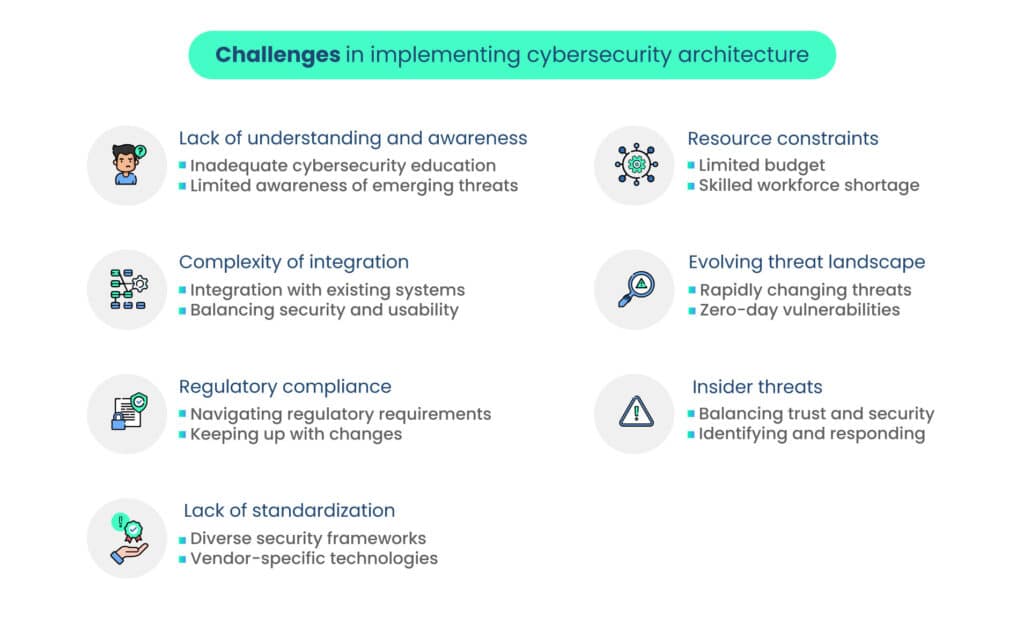
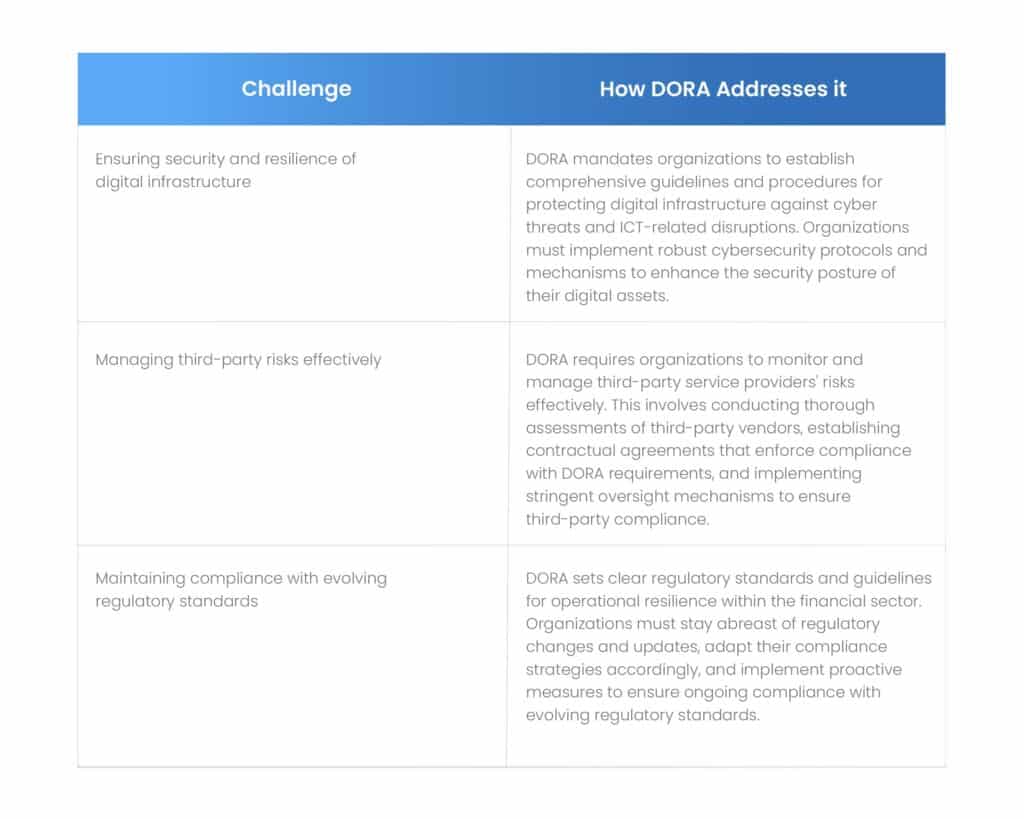
Navigating the landscape of DORA compliance presents organizations with several common challenges that may be addressed with suitable solutions.
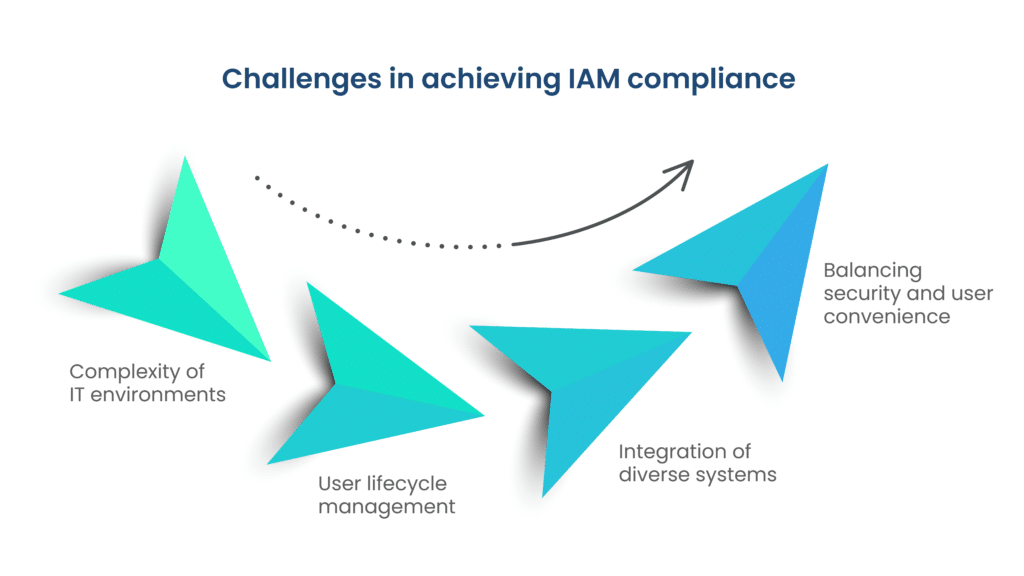
Common challenges in achieving DORA compliance
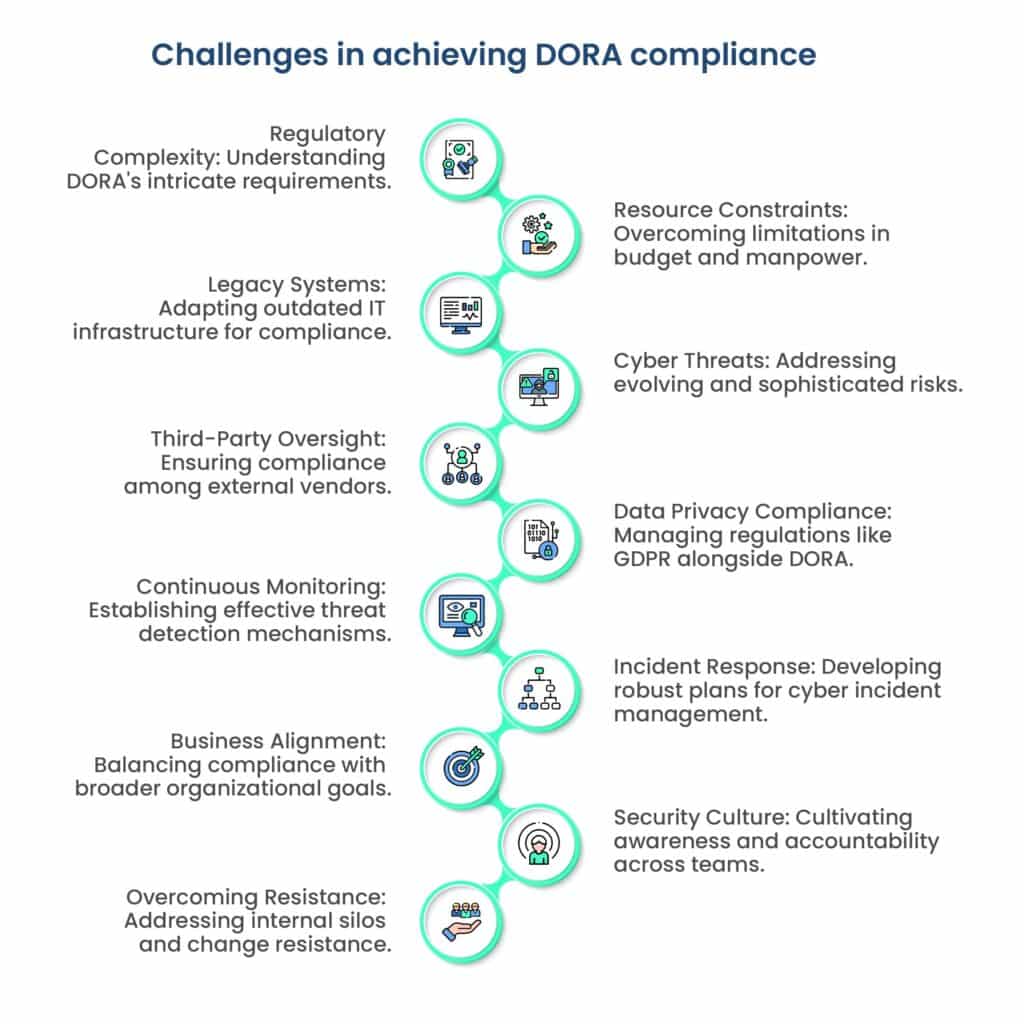
Navigating the landscape of DORA compliance presents organizations with several common challenges.
- Complexity of regulatory requirements: Understanding and interpreting the multifaceted DORA regulations can be challenging due to their intricate nature and evolving landscape, requiring organizations to invest time and resources in comprehensive compliance efforts.
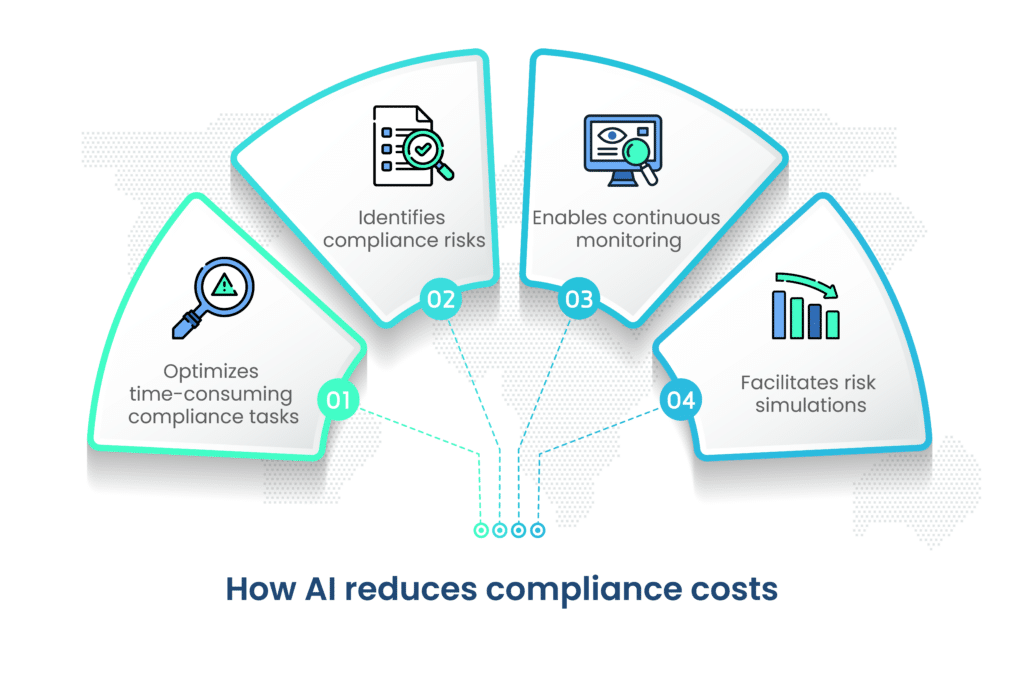
- Resource constraints: Limited budget, manpower, and expertise may hinder organizations’ ability to implement robust compliance measures, conduct thorough risk assessments, and invest in advanced cybersecurity solutions necessary for DORA compliance.
- Legacy IT systems: Outdated infrastructure and legacy systems may lack the necessary capabilities and security measures to meet DORA compliance standards, necessitating costly upgrades or replacements to align with regulatory requirements.
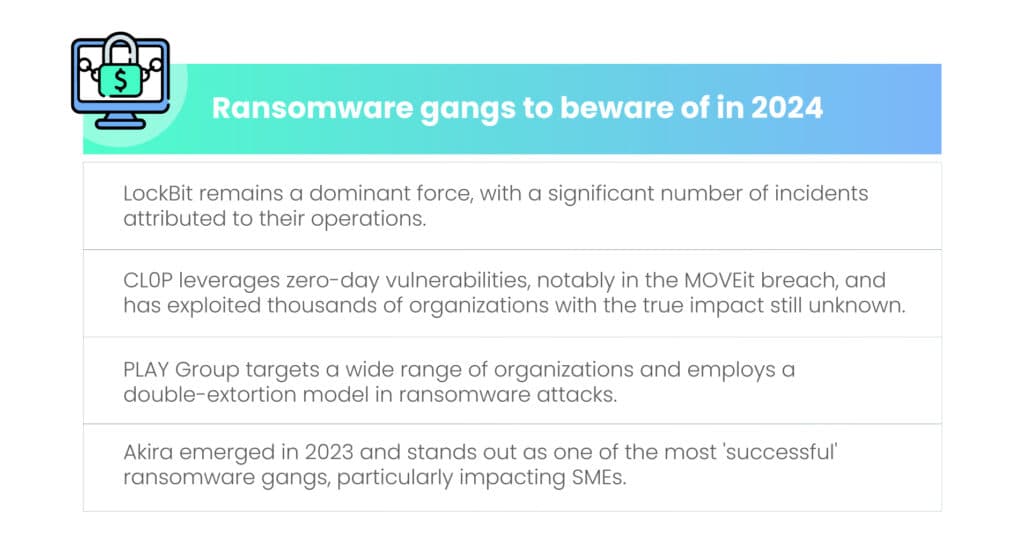
- Evolving cyber threats: The dynamic and sophisticated nature of cyber threats presents a constant challenge for organizations striving to maintain resilience against cyberattacks, requiring continuous monitoring, adaptation, and investment in cybersecurity measures.
- Third-party dependencies: Organizations relying on third-party service providers for critical IT and cybersecurity functions face challenges in ensuring the compliance of these vendors with DORA regulations, necessitating robust oversight, contractual agreements, and risk management practices.
- Data privacy and protection: Compliance with data privacy regulations such as GDPR adds complexity to DORA compliance efforts, requiring organizations to implement stringent data protection measures and ensure compliance with privacy requirements.
- Continuous monitoring and detection: Establishing effective mechanisms for continuous monitoring, detection, and response to cyber risks is crucial for DORA compliance but can be challenging due to the volume and sophistication of cyber threats and the need for real-time threat intelligence.
- Incident response and recovery: Developing and testing robust incident response and recovery plans is essential for DORA compliance but can be challenging due to the complexity of cyber incidents, coordination across departments, and the need for timely and effective response actions.
- Alignment with business objectives: Maintaining alignment between compliance efforts and broader business objectives can be challenging, requiring organizations to balance regulatory requirements with operational efficiency, innovation, and growth initiatives.
- Culture of security awareness: Fostering a culture of security awareness, accountability, and proactive risk management throughout the organization is crucial for DORA compliance but may face resistance or lack of buy-in from employees, requiring ongoing education and awareness initiatives.
- Organizational silos and resistance to change: Overcoming organizational silos, resistance to change, and internal politics can pose significant challenges in achieving DORA compliance, requiring strong leadership, communication, and collaboration across departments and stakeholders.
Innovative solutions and best practices to address challenges
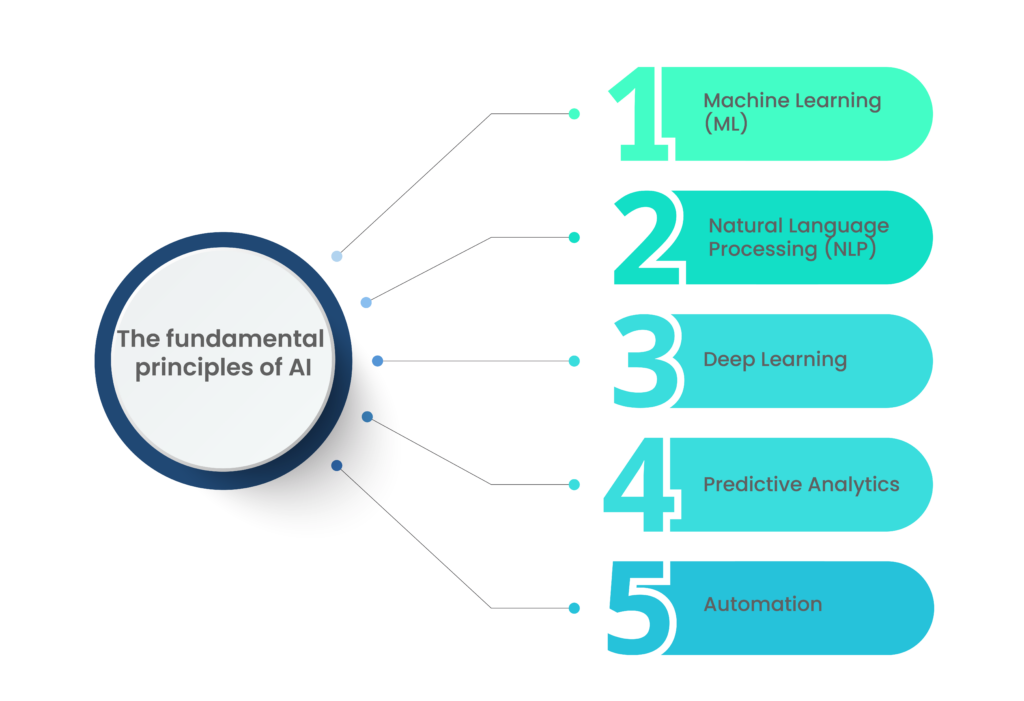
To address the challenges associated with DORA compliance, organizations can adopt innovative solutions and best practices tailored to their specific needs and circumstances.
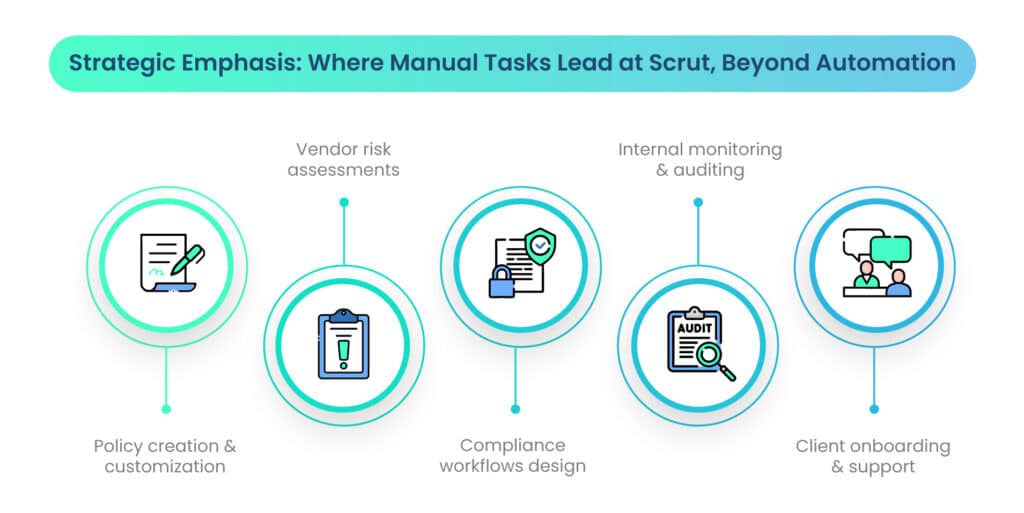
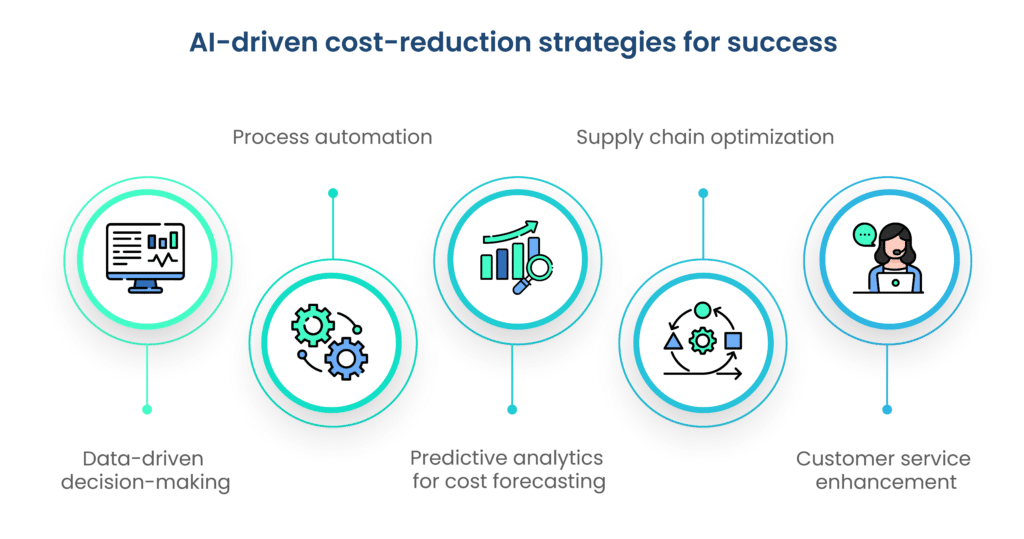
These solutions may include leveraging advanced technologies such as artificial intelligence, machine learning, and automation to enhance risk assessment, threat detection, and compliance monitoring capabilities.
Organizations can also implement robust cybersecurity frameworks, policies, and controls aligned with industry standards and best practices to mitigate cyber risks effectively. Furthermore, investing in employee training and awareness programs, establishing strategic partnerships with cybersecurity experts and industry associations, and leveraging regulatory compliance tools and platforms can help organizations streamline compliance efforts and achieve DORA compliance more efficiently and effectively.
| Solutions | Challenges Addressed |
| Leveraging advanced technologies | Enhancing risk assessment, threat detection, and compliance monitoring capabilities. |
| Implementing robust cybersecurity frameworks | Effectively mitigating cyber risks aligned with industry standards and best practices. |
| Investing in employee training and awareness | Strengthening organizational readiness and responsiveness to cyber threats. |
| Establishing strategic partnerships | Accessing specialized expertise and resources to navigate complex compliance requirements. |
| Leveraging regulatory compliance tools | Streamlining compliance processes and ensuring adherence to regulatory standards. |
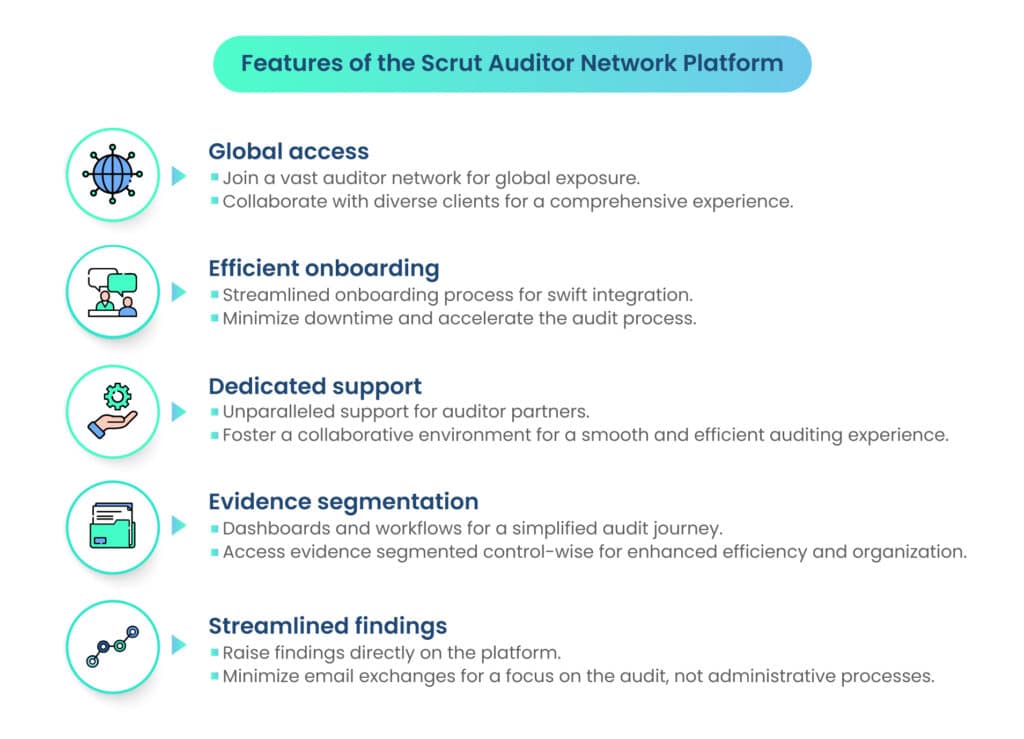
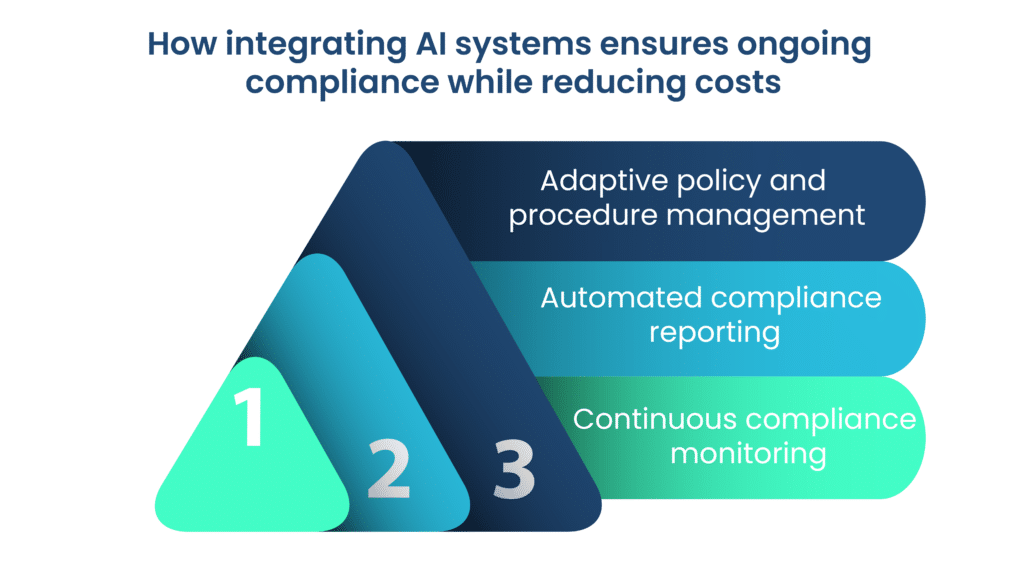
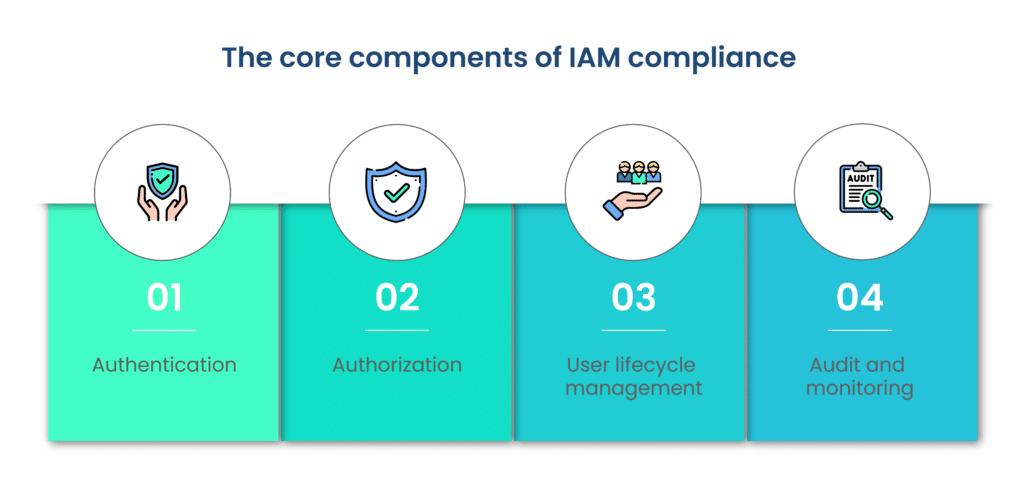
DORA compliance – Role of audit and reporting
Regular audits play a critical role in ensuring ongoing compliance with DORA requirements. By conducting periodic audits, organizations can assess their adherence to regulatory standards, identify areas of non-compliance or weakness, and implement corrective actions to address deficiencies.
These audits may cover various aspects of operational resilience, including cybersecurity practices, incident response procedures, risk management frameworks, and third-party vendor management processes.
By establishing a robust audit program, organizations can maintain a proactive approach to compliance and demonstrate their commitment to regulatory requirements.
Generating comprehensive compliance reports
Comprehensive compliance reports are essential for documenting adherence to DORA regulations and providing evidence of compliance to regulatory authorities and stakeholders.
These reports should capture key compliance metrics, audit findings, remediation activities, and other relevant information necessary to assess the organization’s compliance posture.
By generating comprehensive compliance reports, organizations can facilitate transparency, accountability, and effective communication with regulators, auditors, board members, and other stakeholders. These reports can also serve as valuable tools for internal decision-making, risk management, and strategic planning initiatives.
The role of scrutiny in audit preparedness
Scrutiny plays a crucial role in audit preparedness by enabling organizations to proactively assess their compliance readiness, identify potential gaps or deficiencies, and implement corrective measures as needed.
By subjecting their operations to rigorous scrutiny, organizations can uncover hidden risks, improve internal controls, and enhance overall operational resilience. Scrutiny can take various forms, including internal audits, third-party assessments, compliance reviews, and self-assessments.
By embracing scrutiny as a proactive tool for continuous improvement, organizations can strengthen their audit preparedness, mitigate compliance risks, and maintain confidence in their ability to meet regulatory obligations.
Role of supervisory authorities in enforcing DORA
Supervisory authorities play a crucial role in enforcing DORA regulations, including national competent authorities and the European Banking Authority (EBA). Their responsibilities include evaluating operational resilience by assessing plans, mapping critical services, and reviewing outsourcing. They conduct on-site inspections to confirm compliance, enforce penalties for non-compliance, provide guidance to institutions, and foster coordination among authorities to ensure consistent practices across the EU.
Future outlook
Anticipating and adapting to future changes in the regulatory landscape is essential for organizations striving to maintain compliance with evolving requirements like DORA.
By staying informed about emerging regulations, industry standards, and geopolitical developments, organizations can proactively adjust their compliance strategies and frameworks. This proactive approach enables organizations to navigate regulatory changes smoothly, minimize compliance risks, and ensure ongoing alignment with regulatory expectations.
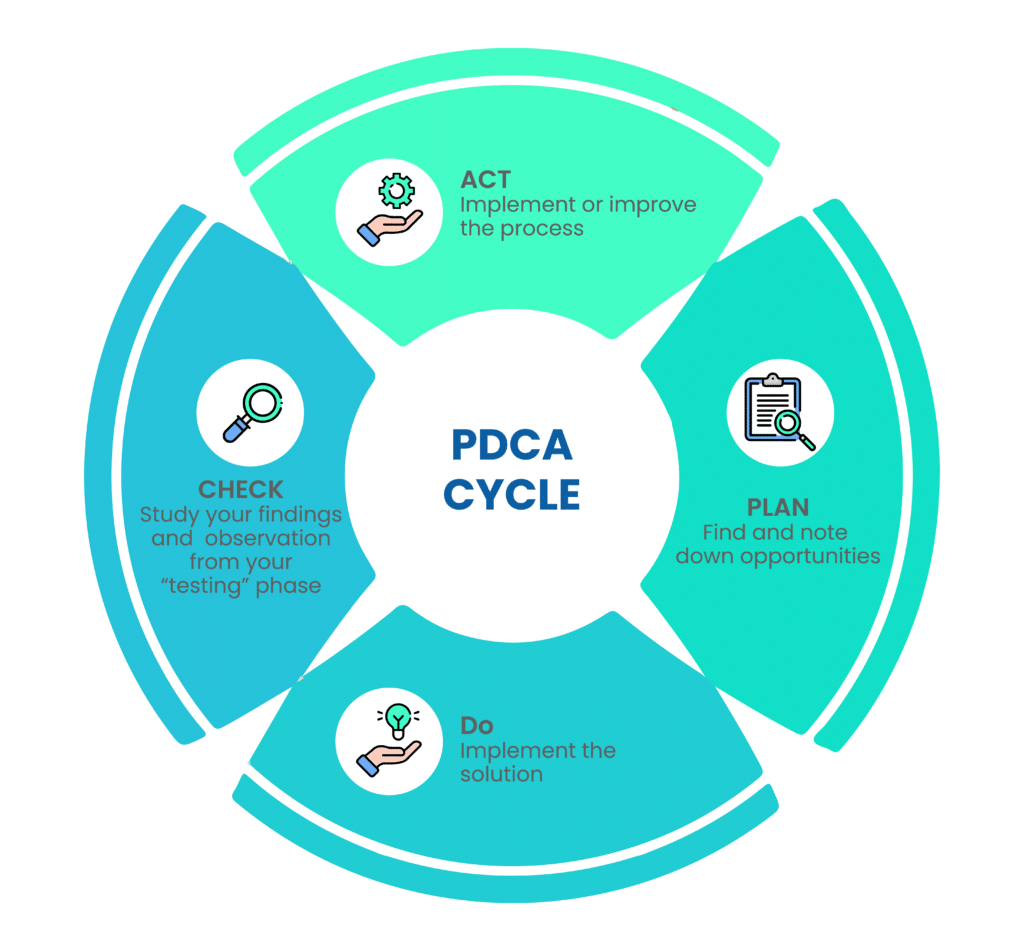
Implementing continuous improvement strategies is crucial for ensuring long-term compliance with DORA and other regulatory frameworks. Organizations must regularly assess their compliance programs, identify areas for enhancement, and implement targeted improvements to strengthen their resilience against emerging threats and regulatory changes.
Technology plays a pivotal role in shaping the future of DORA compliance, offering innovative solutions to streamline compliance processes, enhance risk management capabilities, and improve operational resilience.
Advancements in regulatory technology (RegTech), artificial intelligence, automation, and data analytics empower organizations to achieve greater efficiency, accuracy, and effectiveness in their compliance efforts. By leveraging cutting-edge technologies, organizations can stay ahead of regulatory challenges, mitigate compliance risks, and drive sustainable compliance outcomes in the digital age.
Conclusion
Throughout the DORA compliance journey, organizations have encountered various challenges, opportunities, and insights. From understanding the genesis of DORA to navigating its regulatory framework, organizations have gained valuable insights into enhancing operational resilience, mitigating risks, and ensuring compliance with evolving financial regulations.
As financial regulations continue to evolve, organizations must remain proactive in their compliance efforts. By taking proactive measures to understand and adapt to regulatory changes, organizations can strengthen their compliance programs, enhance risk management practices, and safeguard their operations against emerging threats and vulnerabilities.
Through proactive compliance measures and strategic investments in operational resilience, organizations can thrive in an increasingly complex and dynamic business environment.
For tailored guidance and support in meeting compliance needs, reach out to Scrut to ensure readiness and resilience in navigating the evolving regulatory landscape like DORA.
Frequently Asked Questions
DORA, or the Digital Operational Resilience Act, is an EU financial regulation aimed at ensuring organizations can withstand, respond to, and recover from cyber threats and ICT-related disruptions. It’s crucial for organizations as it enhances operational resilience, protects sensitive data, and helps prevent costly data breaches.
DORA encompasses requirements for risk management, incident reporting, ICT risk management, and operational resilience testing. These components impact businesses by necessitating robust cybersecurity measures, proactive risk management strategies, and thorough incident response protocols.
DORA compliance mandates that organizations implement measures to protect, detect, contain, recover, and repair their ICT capabilities. By adhering to these requirements, organizations enhance their cyber resilience, making them better equipped to withstand cyber threats and operational disruptions.
Organizations can ensure smooth DORA compliance implementation by conducting thorough risk assessments, establishing clear evaluation criteria for compliance solutions, conducting proof of concept tests, and providing comprehensive training for employees.
Non-compliant organizations may face penalties such as public reprimands, withdrawal of authorization, remedial measures, compensation for damages, criminal charges, and administrative fines, as determined by the laws of each EU member country. It’s essential for organizations to prioritize DORA compliance to avoid these repercussions.