Navigating through complex regulatory frameworks while ensuring adherence to industry standards can be a daunting task for organizations of all sizes. As the stakes continue to rise, the role of compliance automation software becomes indispensable in empowering businesses to maintain integrity and operational excellence.
To assist businesses in their compliance journey, we have curated a comprehensive list of the 9 best compliance automation software solutions that stand out in the market. These tools are designed to automate, streamline, and enhance various aspects of compliance management, allowing organizations to stay ahead of the curve and mitigate risks effectively.
How does a compliance automation platform help you?
As the number of cloud and people resources grows in your company, your cloud complexity grows as well—making it harder to stay compliant. A compliance automation software will not only help you find security issues but will also help you with auto-remediation.
Continuous compliance (not at a point in time)
Many tasks related to getting compliant can be automated with the help of a compliance automation software. Additionally, the right platform continuously monitors your controls to help you stay compliant.
Get compliant faster with less effort
Compliance automation software can help you get compliant in a much shorter time frame. For example, they can help you get ready for the SOC 2 compliance audit in 2-3 weeks as opposed to 1-2 months when done traditionally. Similarly, the manual effort required to get ready for the SOC 2 audit from your end can be reduced to 10-12 hours (based on the gap assessment) compared to 150 hours via the traditional solution.
All these benefits translate into peace of mind for you and high trust among your employees, partners, customers, vendors, and auditors. This makes you not just a supporting role in the company but a business enabler. You can focus on more strategic work and help the organization grow.
Top 9 compliance automation software
1. Scrut Automation
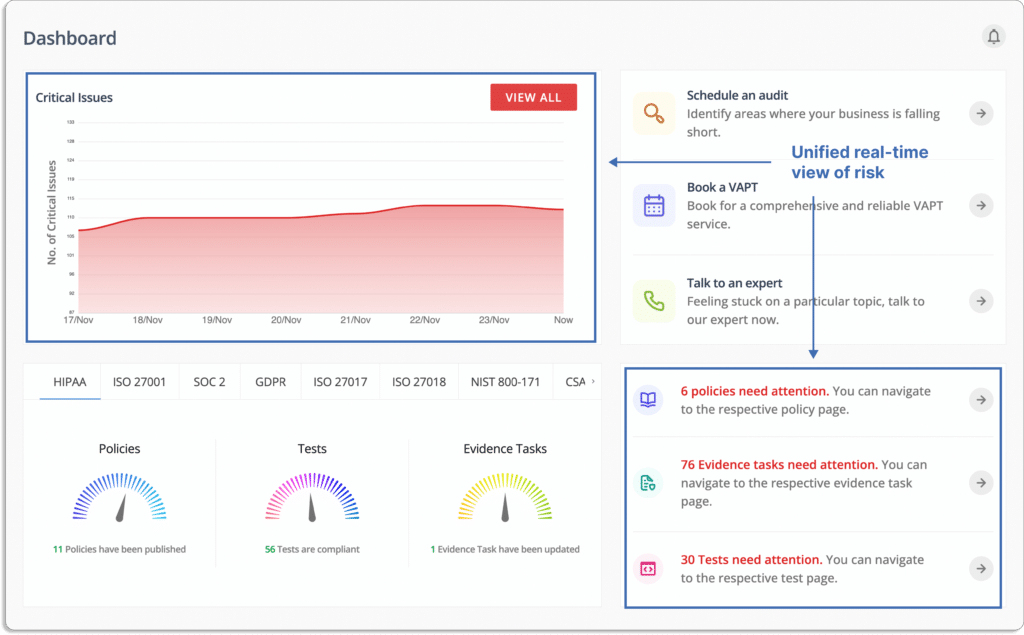
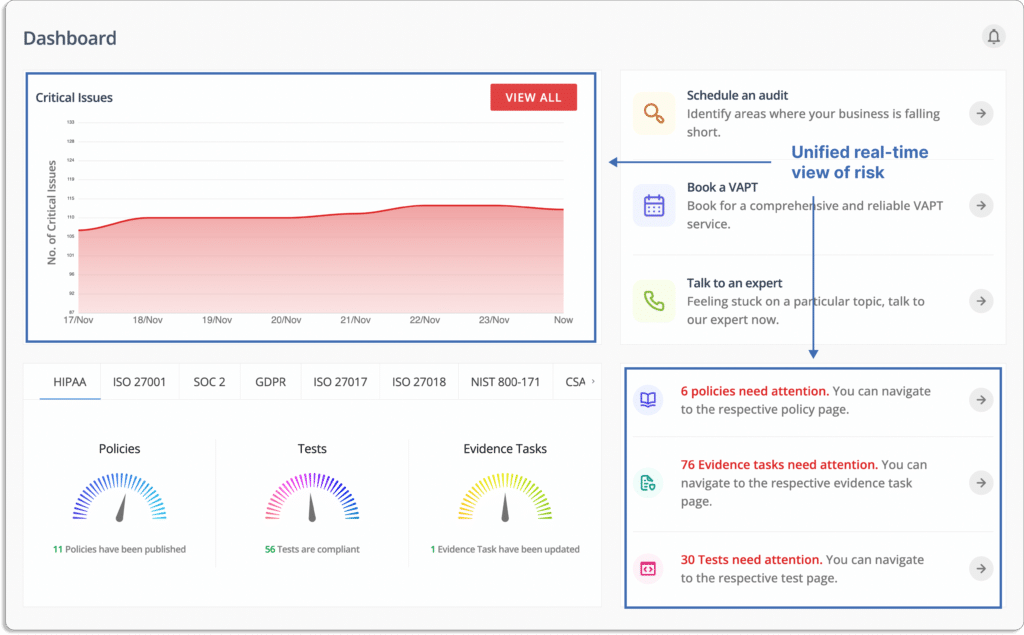
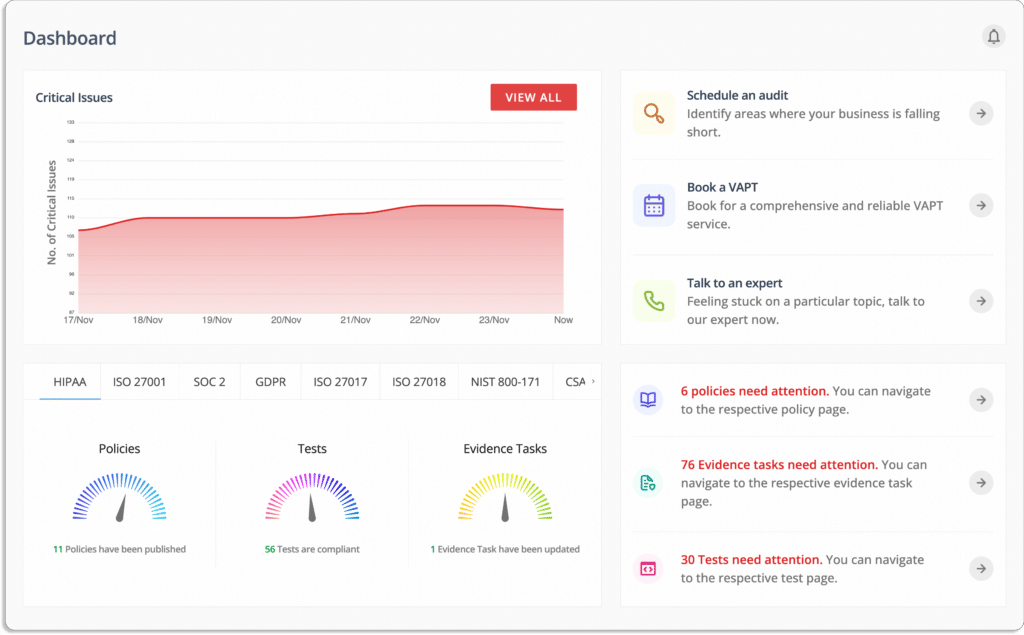
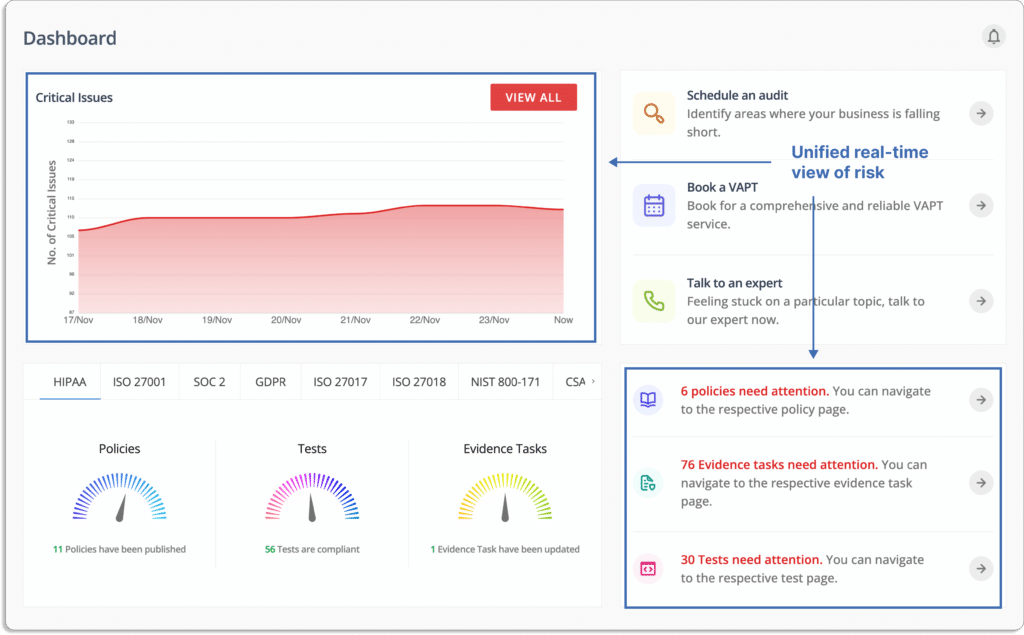
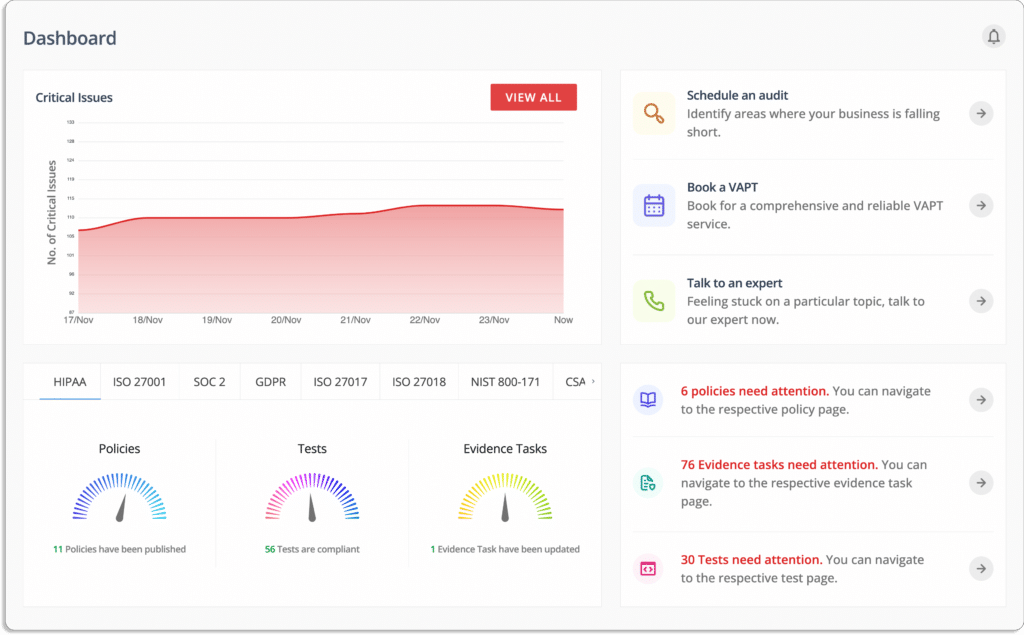
Scrut Automation is a risk-first smart governance, risk, and compliance (GRC) platform. With Scrut, you can say goodbye to the tedious process of getting compliant manually.
Scrut simplifies the compliance landscape, cutting down approximately 70% of the effort typically needed to meet the standards of over 20 frameworks. Whether it’s SOC 2, HIPAA, PCI DSS, ISO 27001, GDPR, CCPA, HITRUST, or others, Scrut streamlines compliance across a range of industry-leading standards.
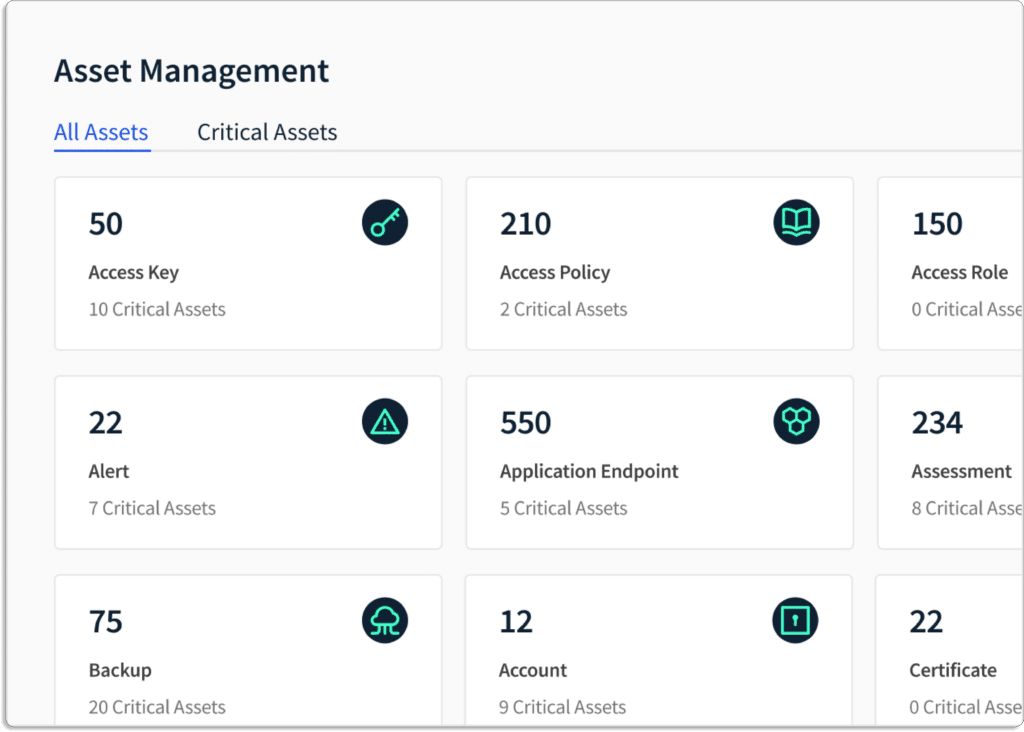
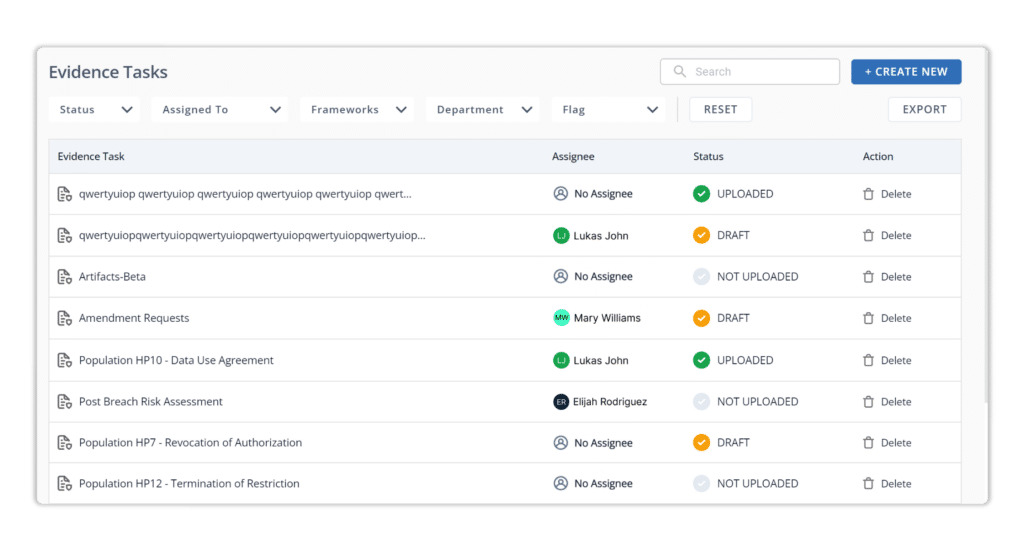
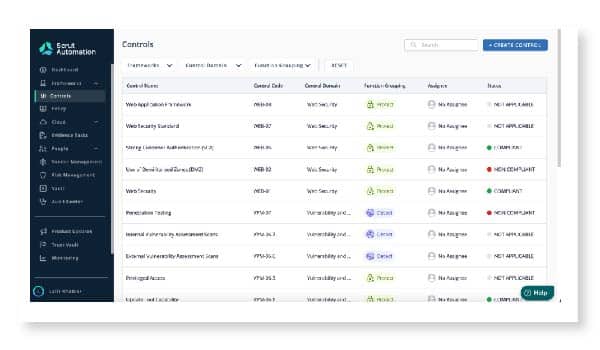
With Scrut Automation, put your InfoSec compliance on auto-pilot. The platform automates tedious compliance tasks, like cloud evidence collection, automatically checking against 150+ controls on a daily basis. Enjoy a more hands-free approach to risk management, as Scrut handles the heavy lifting, freeing up your time for strategic security considerations.
How Scrut helps:
A. Gap Analysis
Identifying gaps in your security program is crucial, and Scrut steps in as your trusted partner to streamline the gap analysis process.
a. Extensive handholding
We understand that navigating the intricacies of compliance frameworks can be daunting. That’s why Scrut offers extensive handholding to guide you through the identification of missing elements in your security program concerning specific frameworks. Our experts bring over 50 years of cumulative experience, having conducted over 3000 assessments. This wealth of knowledge ensures a meticulous examination of your security landscape.
b. Cost & requirements estimation
Scrut’s seasoned experts don’t just identify gaps; they help you estimate the costs and requirements associated with achieving compliance. This strategic insight is invaluable in planning your compliance journey effectively, ensuring that you are well-prepared for the road ahead.
c. Centralized data view
The Scrut platform provides a centralized view of all your data, offering a comprehensive snapshot of your current security posture. This centralized view acts as a foundation for our experts to plan the next steps in your compliance roadmap.

d. Expertly guided process management
With Scrut, it’s not just about identifying gaps – our experts plan the next steps based on the centralized data view, providing you with a clear roadmap for compliance. The platform empowers you to manage the entire process seamlessly, ensuring that every action aligns with your organization’s compliance objectives.
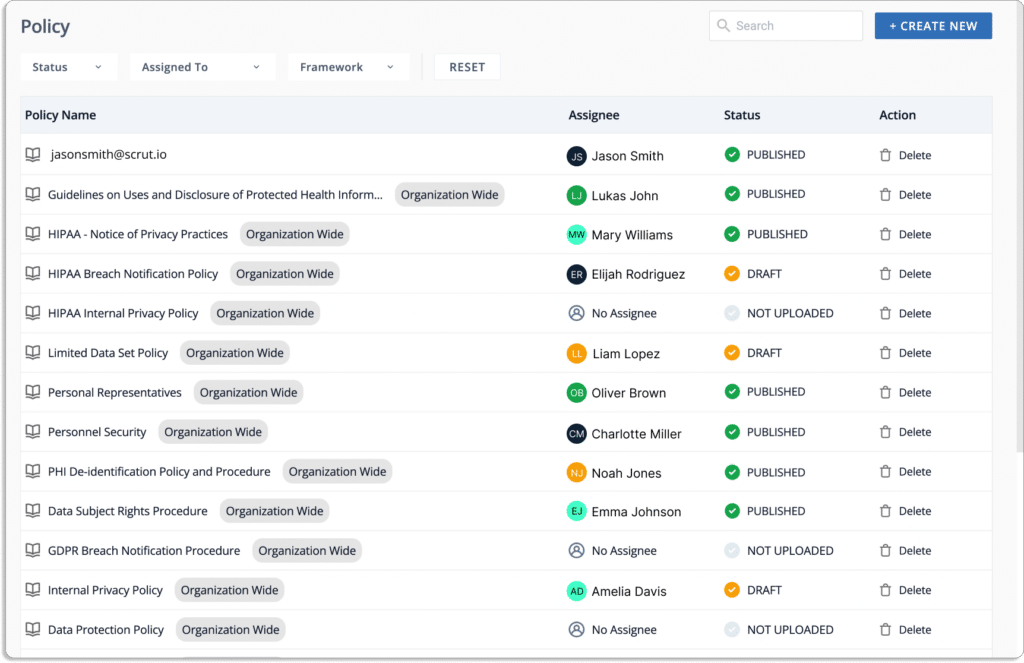
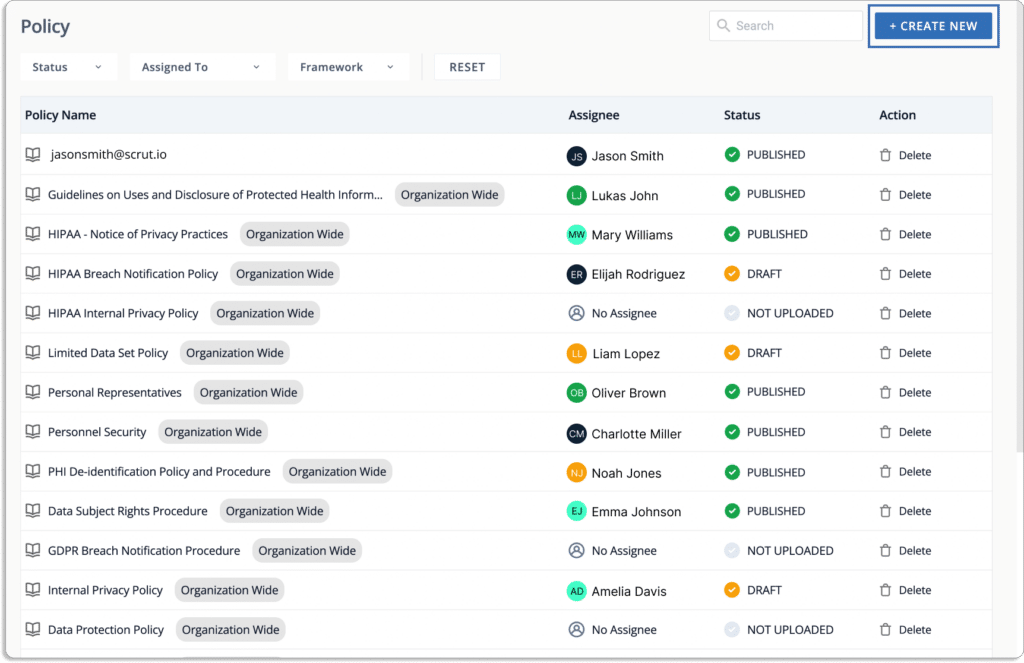
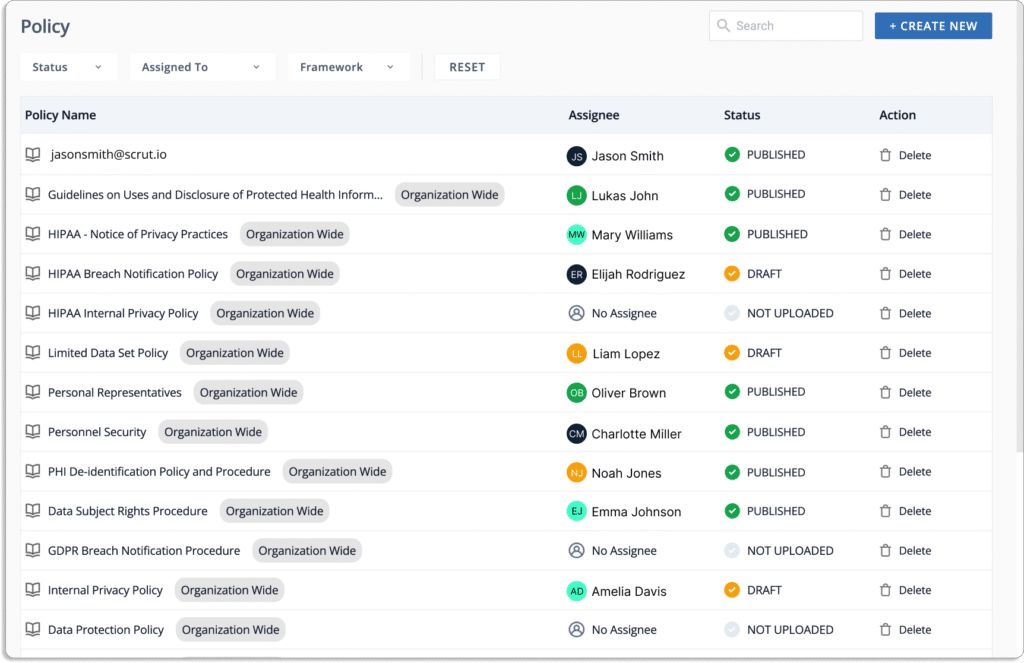
B. Policy creation
When it comes to policy creation, Scrut goes the extra mile to ensure that your organization’s security policies are not just compliant but perfectly aligned with your unique business needs.
a. Pre-built templates
Access a treasure trove of 45+ pre-built policy templates that serve as a solid foundation for your security policies. These templates cover a spectrum of compliance requirements, allowing you to kickstart your policy creation process with confidence.
b. Customizable to your needs
Recognizing that one size does not fit all, Scrut’s policy templates are fully customizable to cater to your specific business needs. Tailor the pre-built templates to align seamlessly with the nuances and intricacies of your organization, ensuring that your policies are not just compliant but also reflective of your unique operational environment.
c. Complete InfoSec team support
Crafting effective security policies requires expertise, and with Scrut, you’re not alone in this endeavor. Our complete InfoSec team stands ready to support you in reviewing and customizing policies. Benefit from the collective knowledge and experience of seasoned information security professionals who ensure that your policies are not only robust but also strategically tailored to address your organization’s specific challenges.
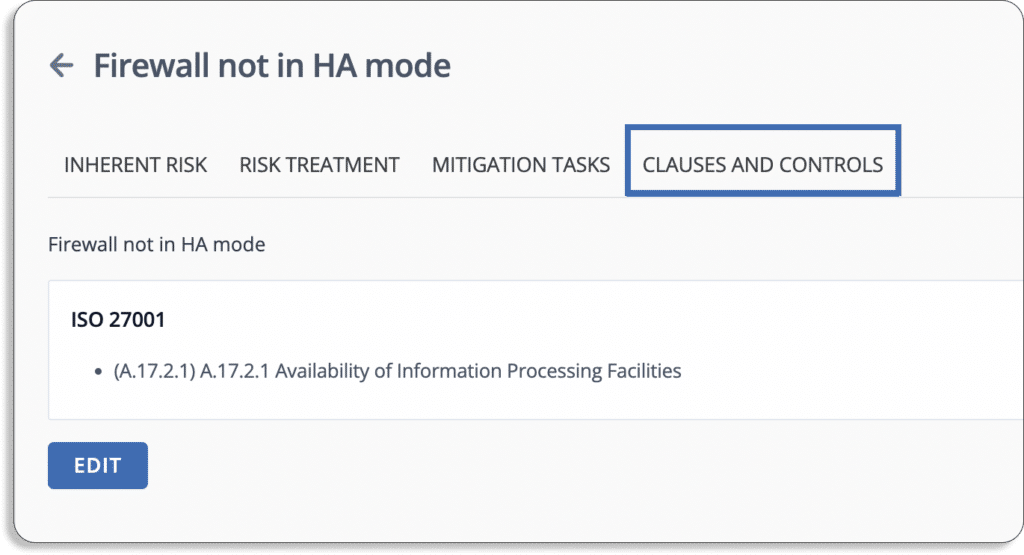
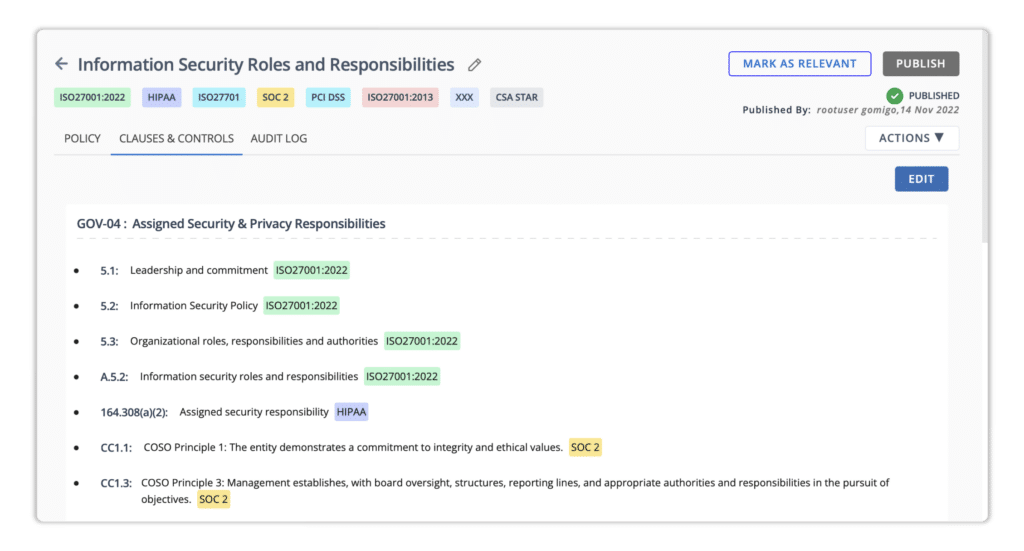
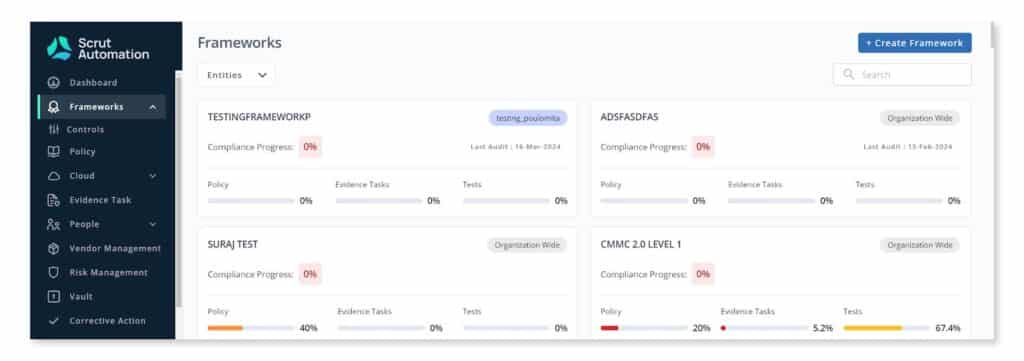
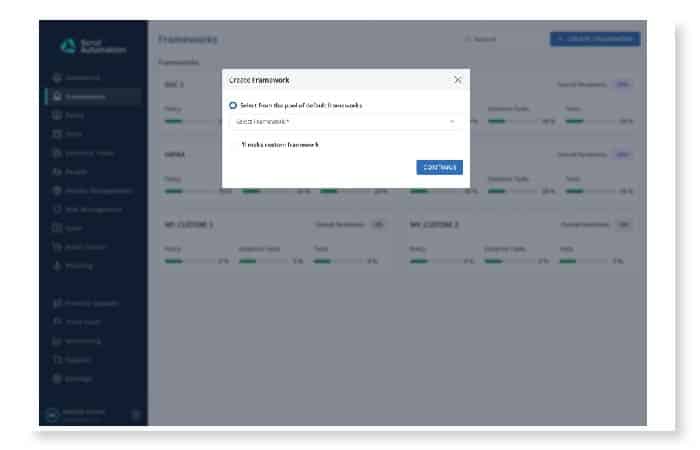
C. Framework mapping
Scrut simplifies the complex landscape of compliance frameworks, offering a seamless framework mapping experience tailored to your organizational needs.
a. Inbuilt frameworks
Explore and leverage 28 inbuilt frameworks directly within Scrut. These frameworks cover a diverse range of compliance standards, providing you with a comprehensive toolkit to align your security practices with industry requirements effortlessly.
b. Custom frameworks with expert support
Should your organization require a more tailored approach, Scrut offers the flexibility of creating custom frameworks. What sets us apart is the dedicated support of our InfoSec experts, ready to assist you in developing new frameworks – all without the hassle of starting from scratch. This service comes at no additional cost, ensuring that your compliance journey remains both efficient and cost-effective.
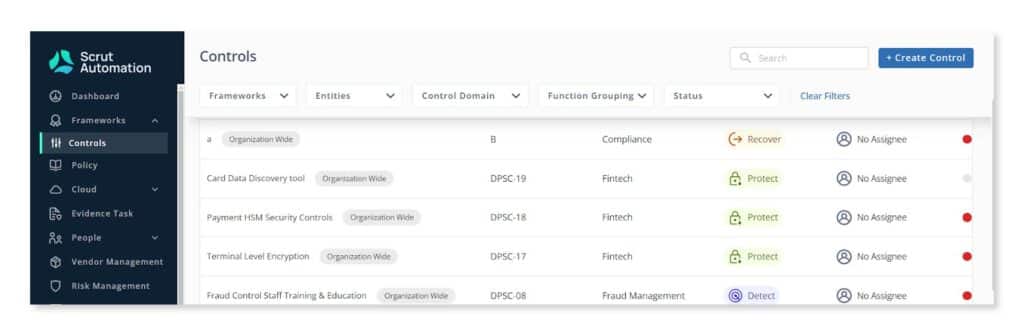
D. Custom controls
Scrut empowers you with the ability to craft custom controls that align precisely with your organization’s unique security requirements.
a. Expert guidance for custom controls
Tap into the expertise of our seasoned professionals as they guide you through the process of creating custom controls tailored to your specific needs. Whether it’s addressing industry-specific challenges or aligning controls with your unique operational landscape, our experts ensure that your security measures are not just compliant but strategically aligned.
b. Utilize existing controls via UCF
Alternatively, leverage the Unified Compliance Framework (UCF) within Scrut to access a repository of existing controls across frameworks. This functionality allows you to streamline and unify your approach to compliance, reducing duplicacy in controls and ensuring a more cohesive and scalable compliance strategy.
c. Mapping risks and artifacts
Scrut’s comprehensive platform allows for the meticulous mapping of all risks and artifacts to the controls. This holistic approach ensures that every aspect of your security landscape is accounted for, providing a clear and detailed picture of your compliance posture.
d. Reduced duplicacy and simplified scalability
The integration of custom controls and the use of UCF significantly reduce duplicacy in controls. This not only streamlines your compliance efforts but also simplifies scalability. Easily extend your compliance initiatives to embrace new and even less-known standards with ease, ensuring that your organization stays ahead of evolving industry requirements.
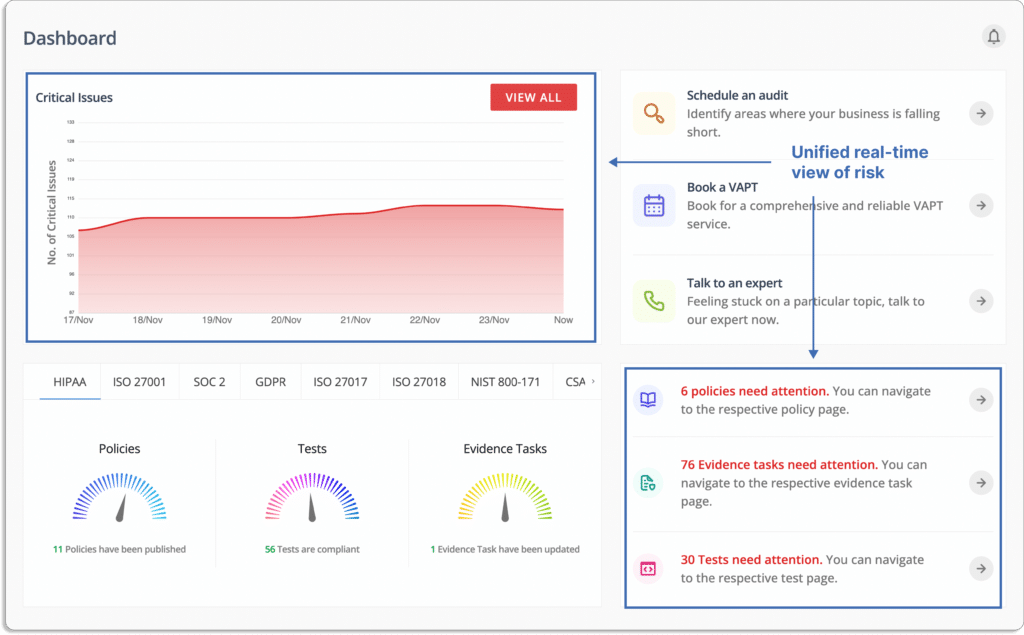
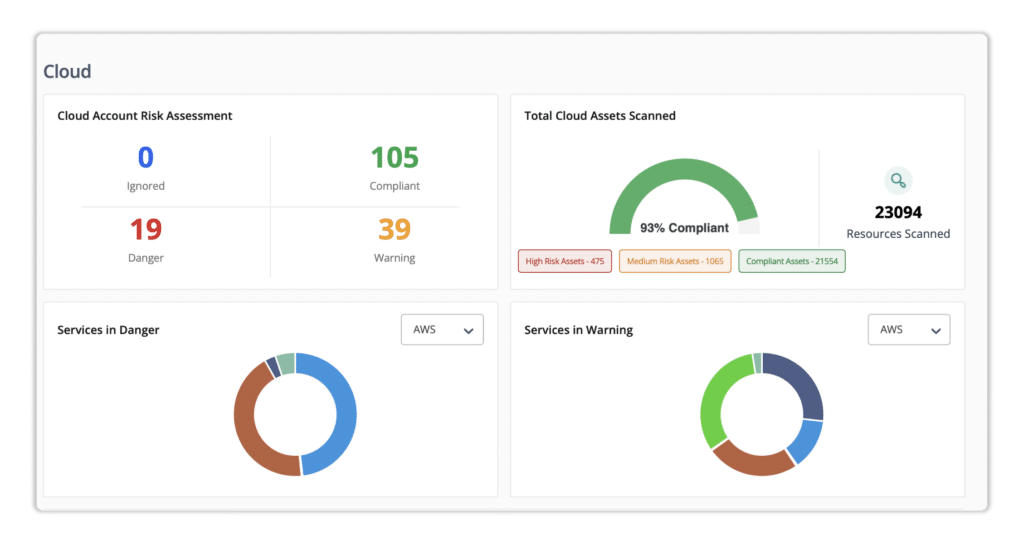
E. Cloud monitoring
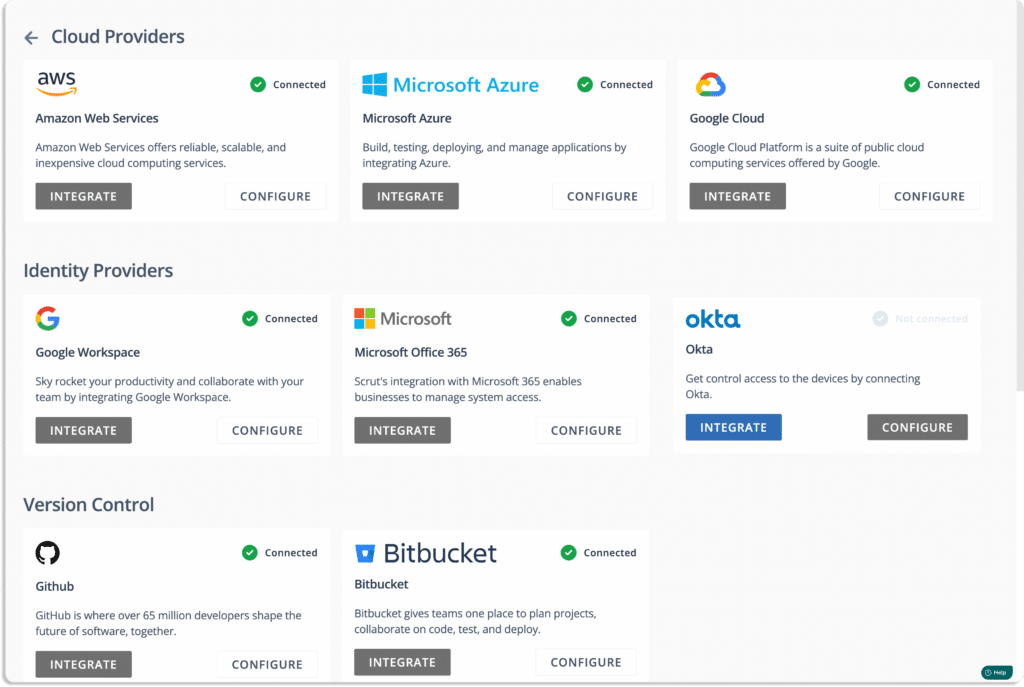
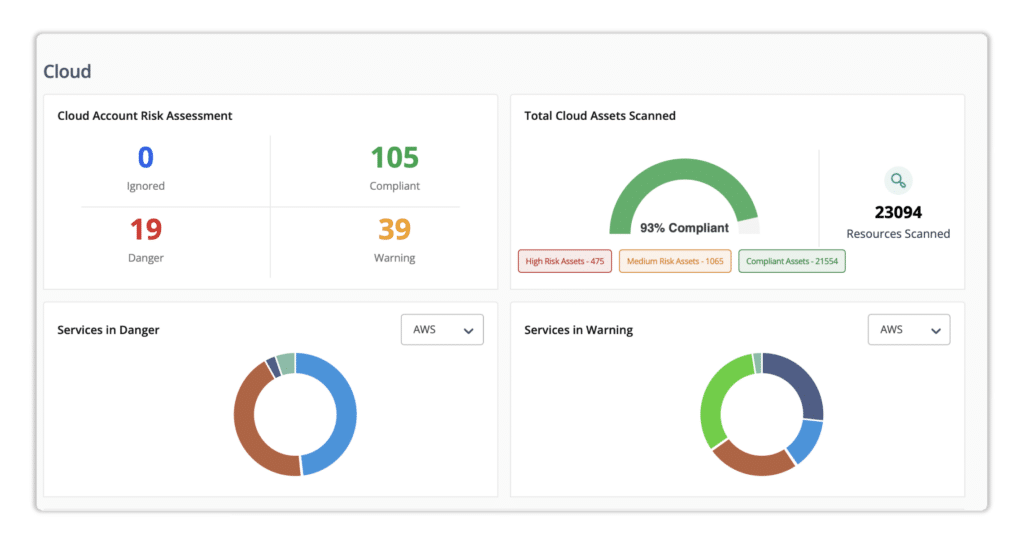
When it comes to cloud security, Scrut brings a robust solution to the table with automated cloud monitoring that goes beyond the ordinary.
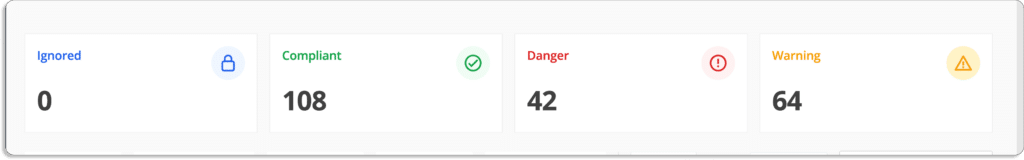
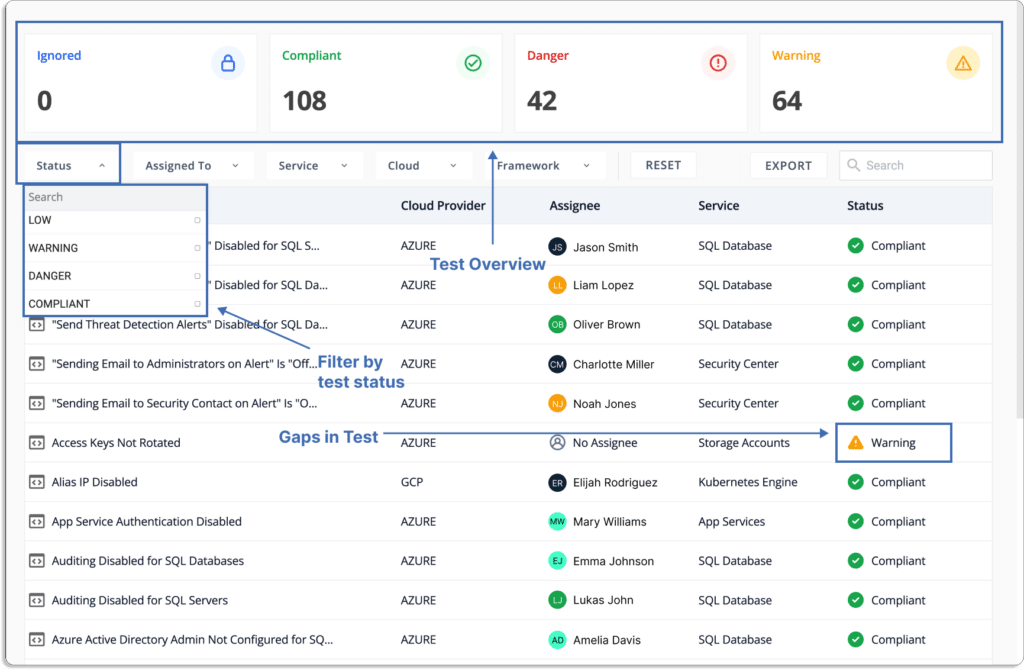
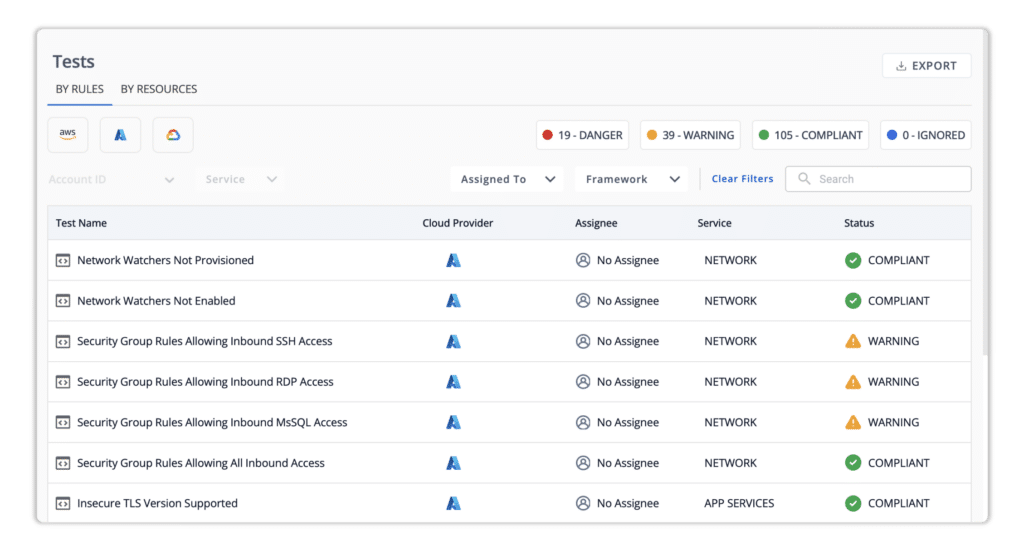
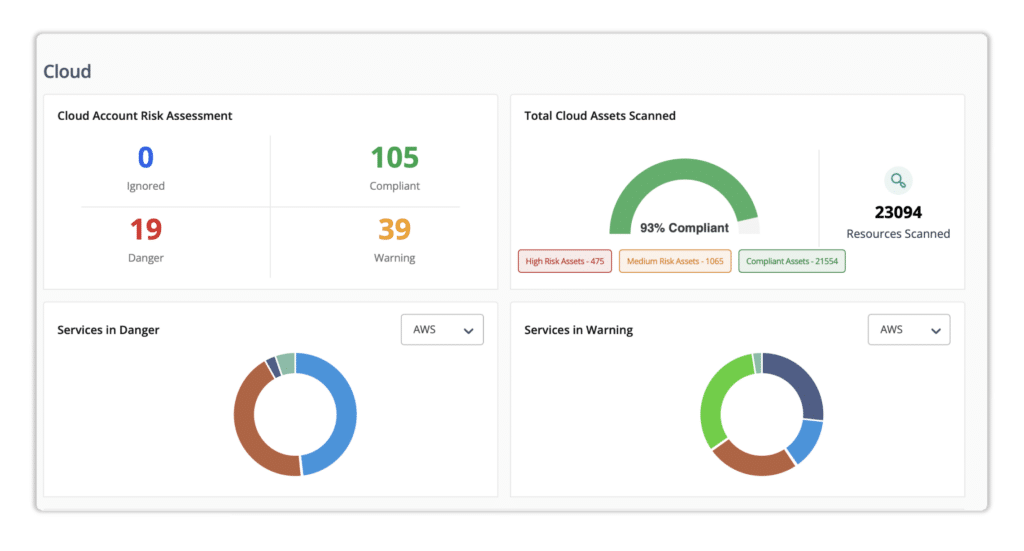
a. Automated checks across 200+ cloud controls
Scrut’s cloud monitoring feature conducts automated checks across a comprehensive array of 200+ cloud controls. This meticulous scrutiny ensures that your cloud infrastructure aligns with the highest standards of security, covering a spectrum of critical aspects to fortify your digital assets.
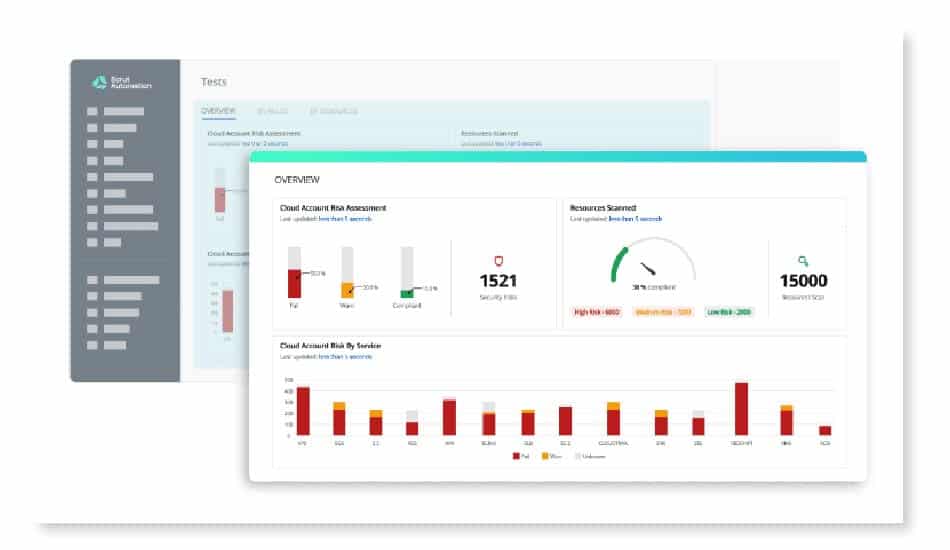
b. Testing against CIS benchmarks
Scrut sets the gold standard for cloud security by rigorously testing your cloud infrastructure against the CIS benchmarks. These benchmarks, recognized as the industry’s gold standard, provide a thorough evaluation of your cloud environment, ensuring that it meets the most stringent security requirements.
F. Automated remediation
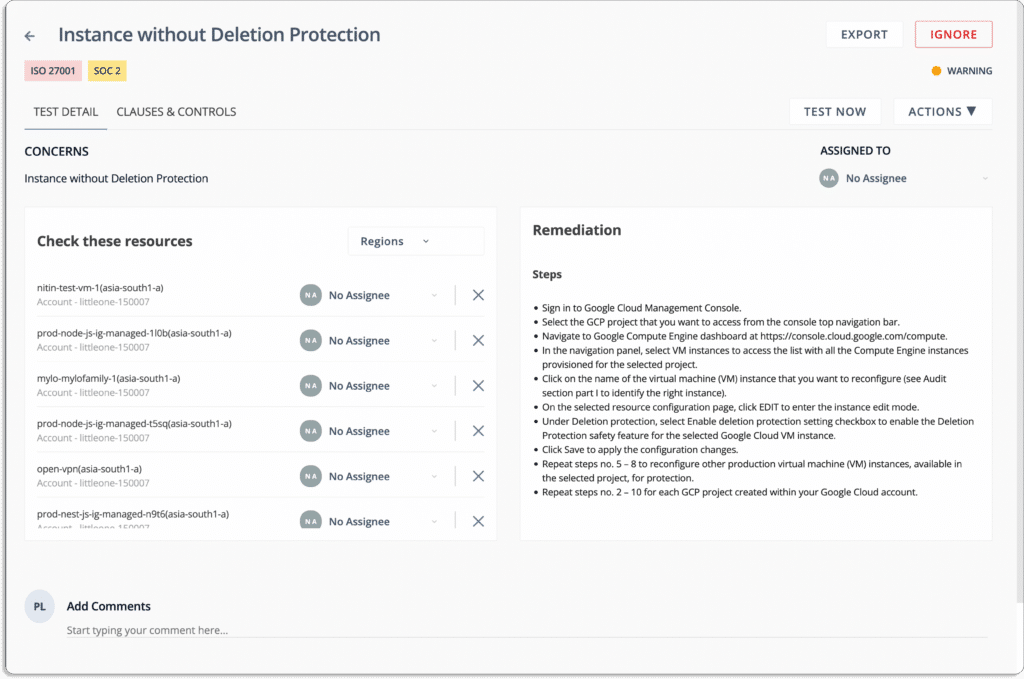
Scrut introduces a game-changing feature—automated remediation designed to keep your cloud infrastructure in optimal condition.
a. Daily automated tests
Scrut conducts thorough tests across your cloud environment every 24 hours, providing a proactive approach to identifying potential issues. These tests cover a broad spectrum, ensuring a comprehensive examination of your cloud resources.
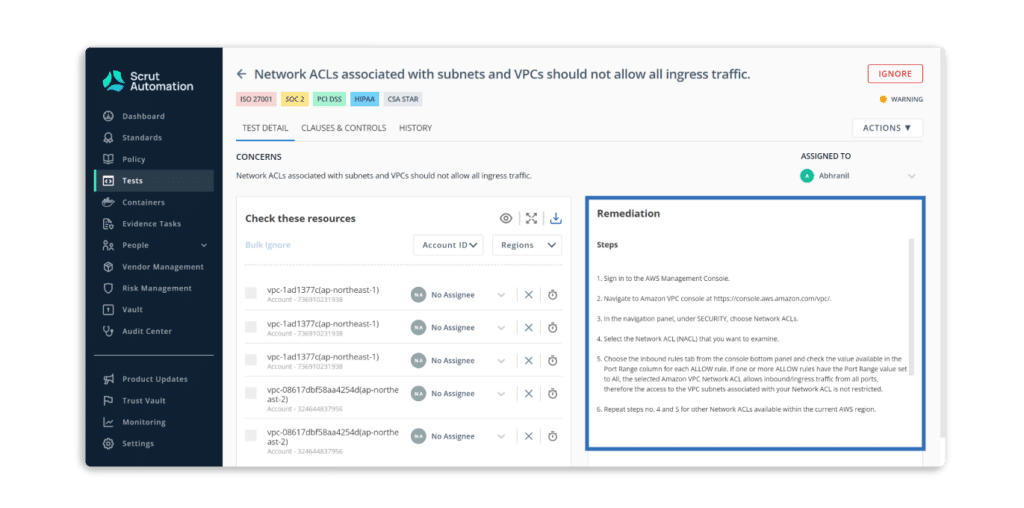
b. Comprehensive issue reports
Receive detailed reports highlighting resources that have issues within your cloud infrastructure. Scrut goes beyond mere identification, offering an insightful breakdown of the problems detected.
c. Step-by-step remediation guidance
For every identified issue, Scrut provides clear and concise steps for remediation. This guidance is not just about flagging problems; it’s about empowering you with actionable insights to address and resolve issues promptly.
d. Integrated project management workflows
Seamlessly integrate remediation into your project management workflows. Scrut ensures that the remediation process aligns with your overall project strategy, facilitating a cohesive and efficient approach to cloud security.
e. Automated code generation
In cases where specific code is required to address issues, Scrut takes the hassle out of coding. The system generates the necessary code for you, streamlining the implementation of remediation steps and saving you valuable time and resources.
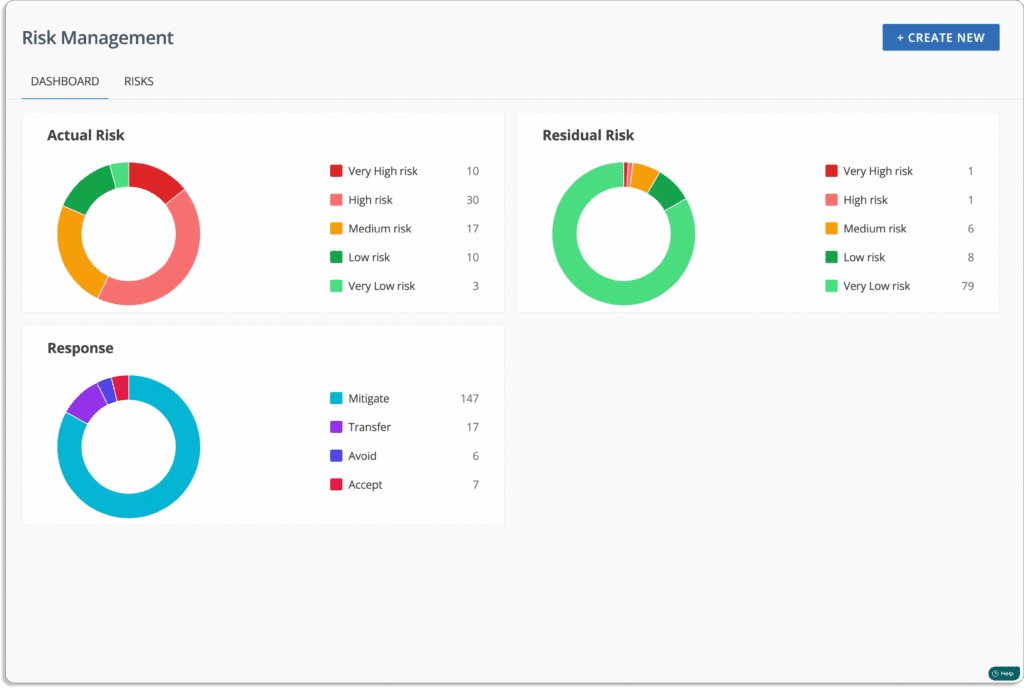
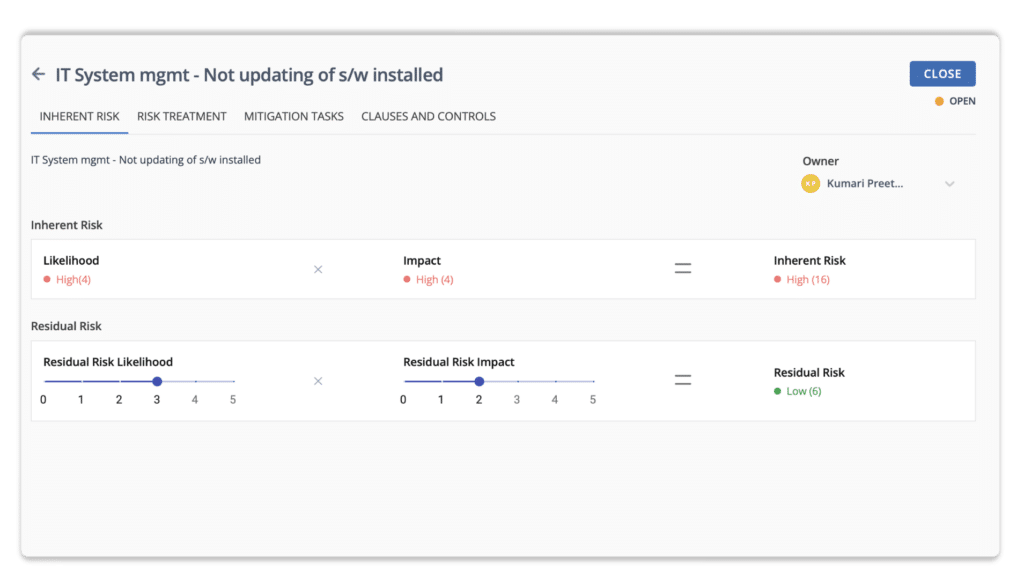
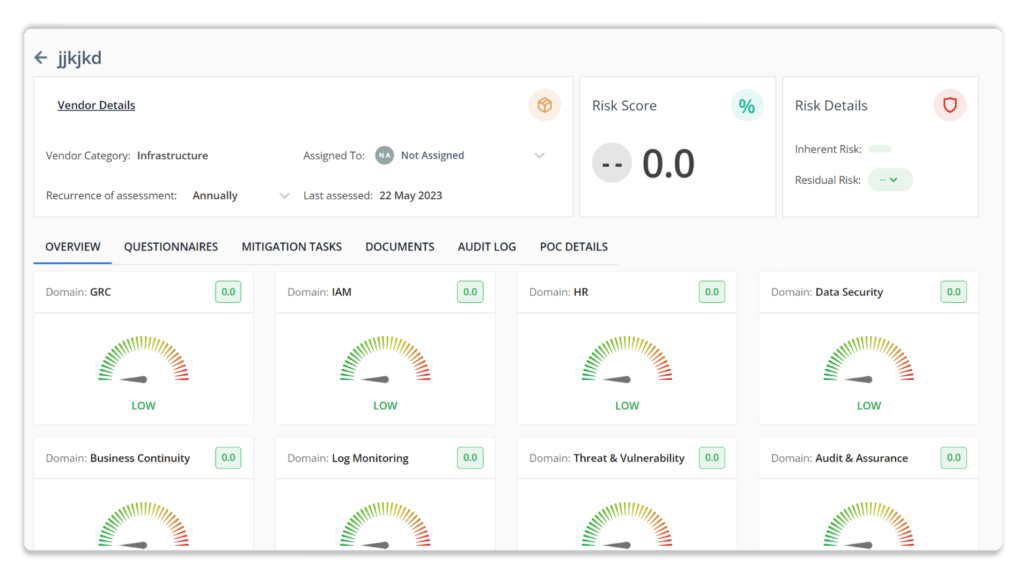
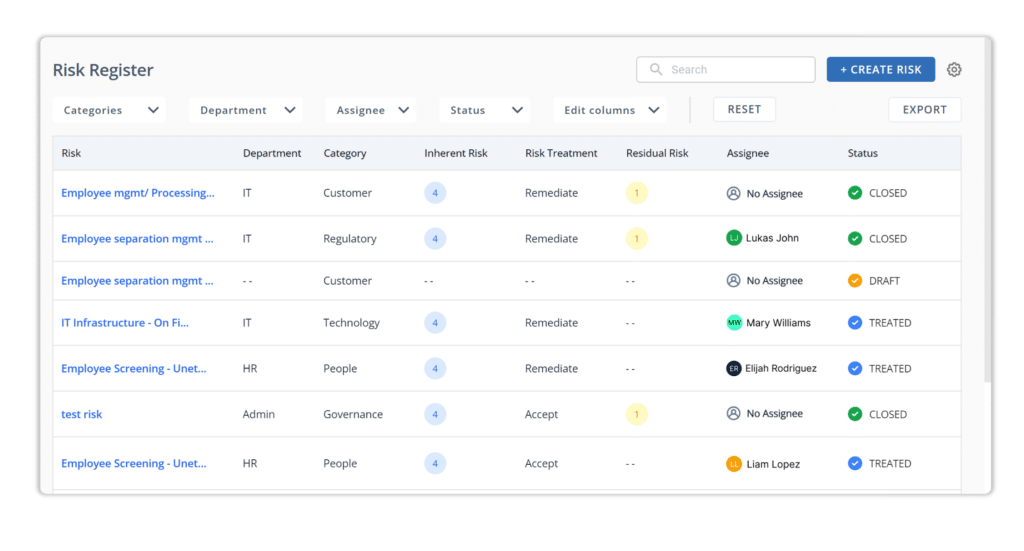
G. Risk management
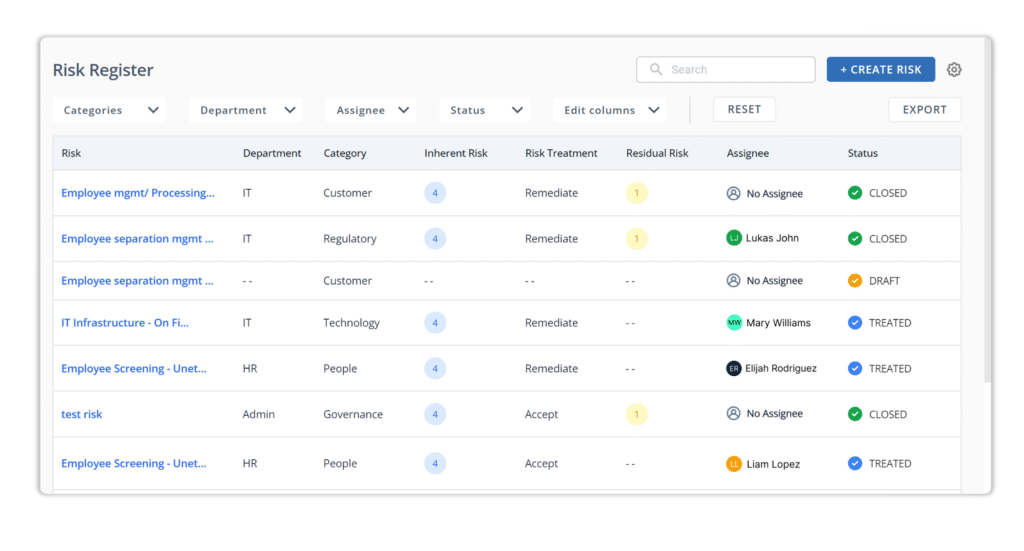
In the realm of risk management, Scrut presents a dynamic and flexible solution that not only identifies risks but empowers organizations to respond proactively, ensuring resilience across departments and applications.
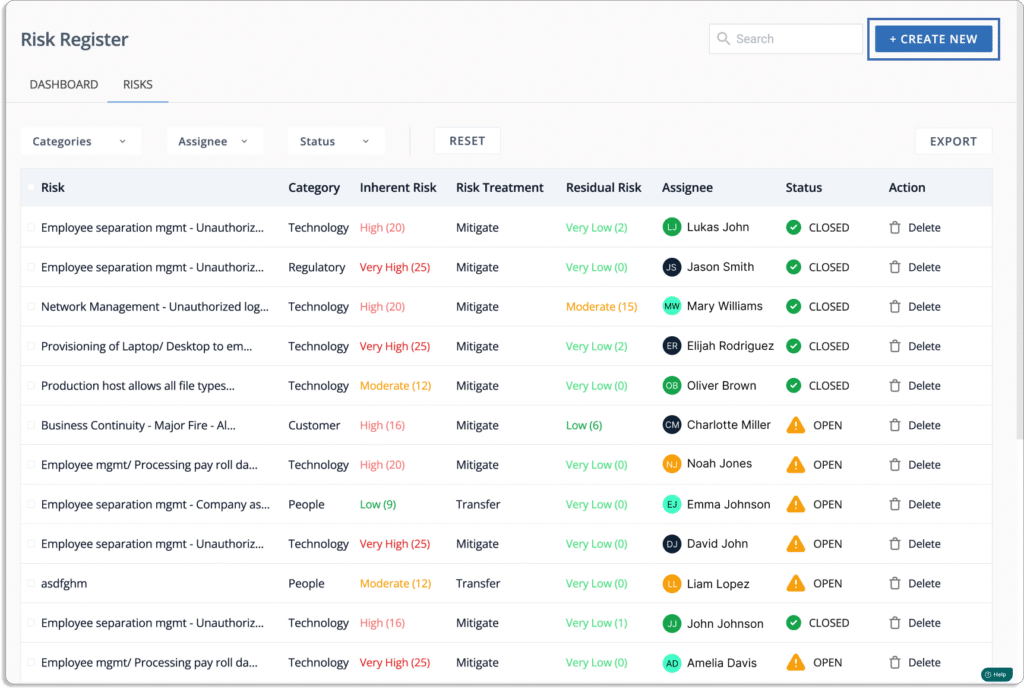
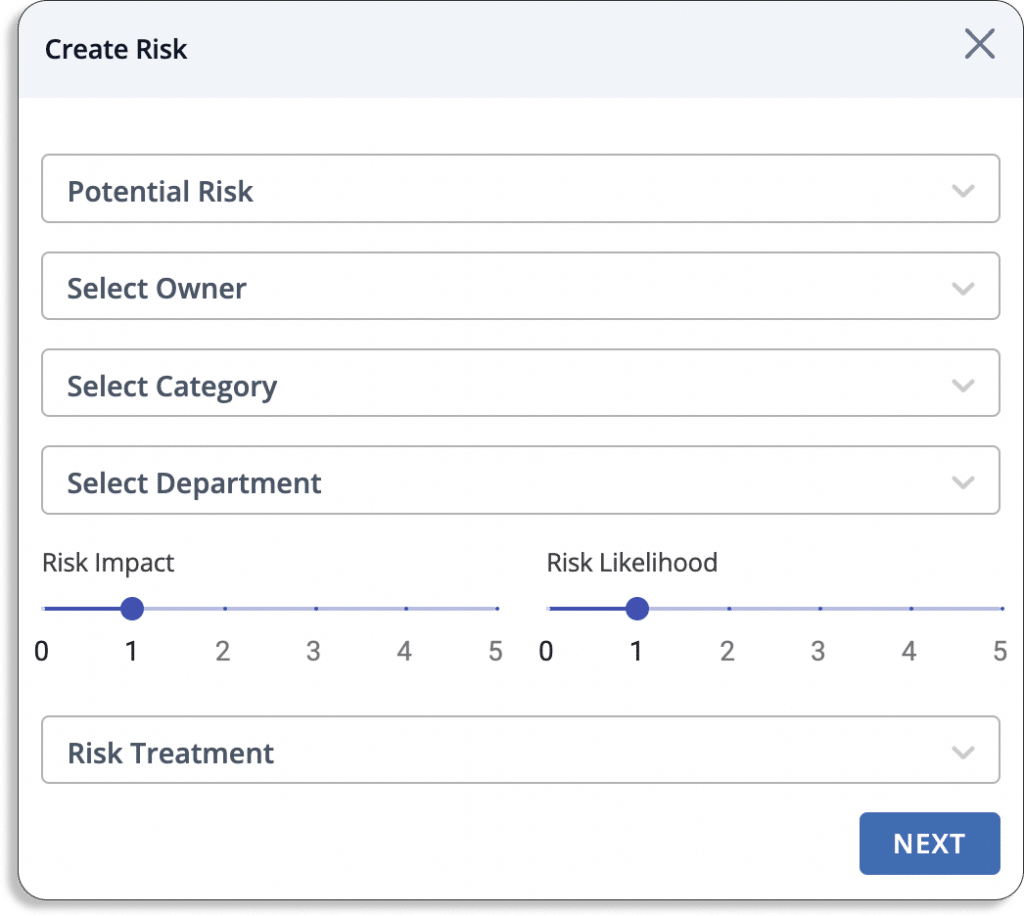
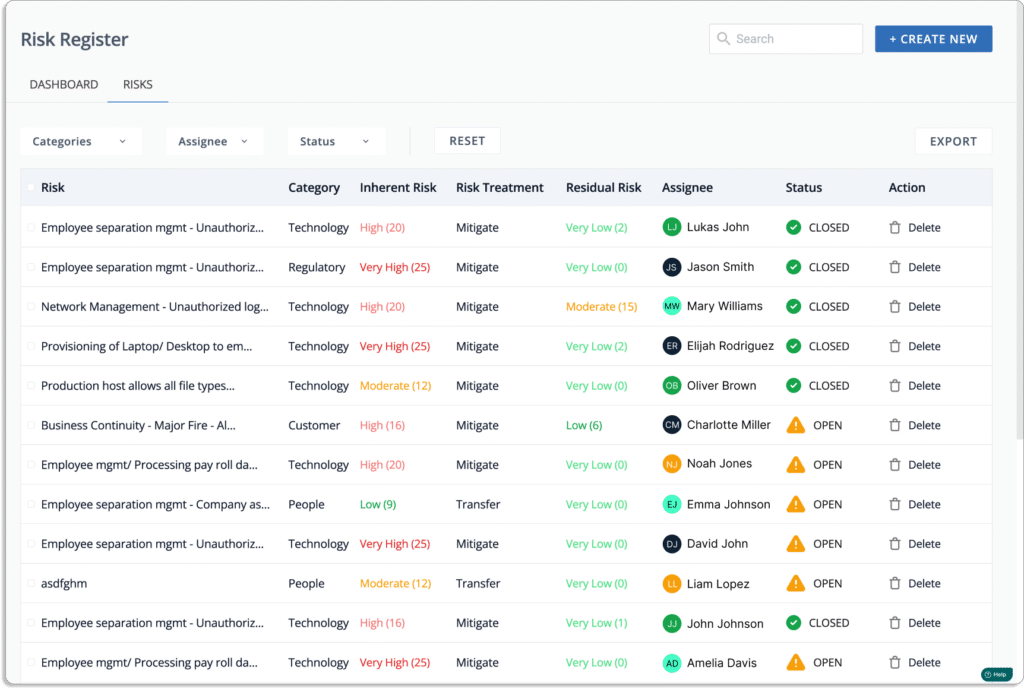
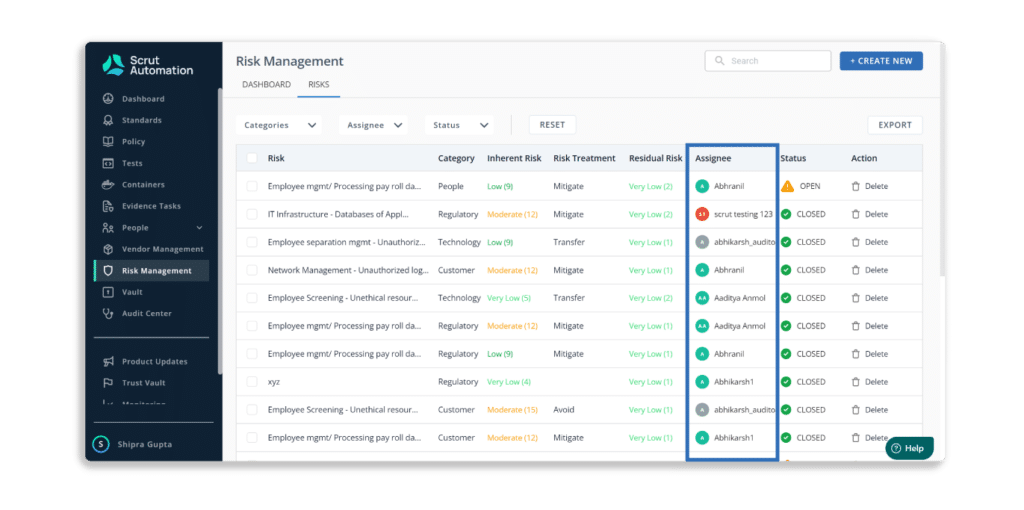
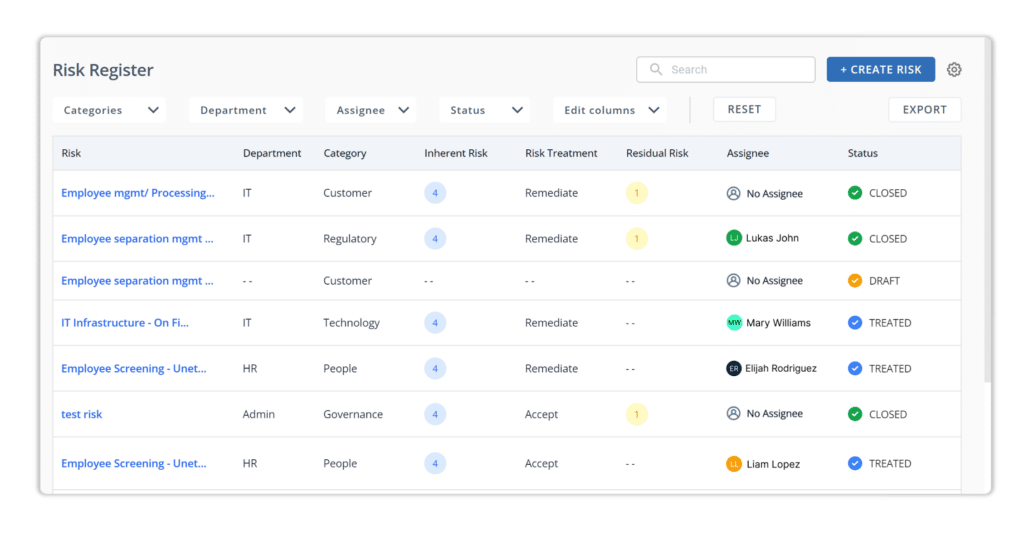
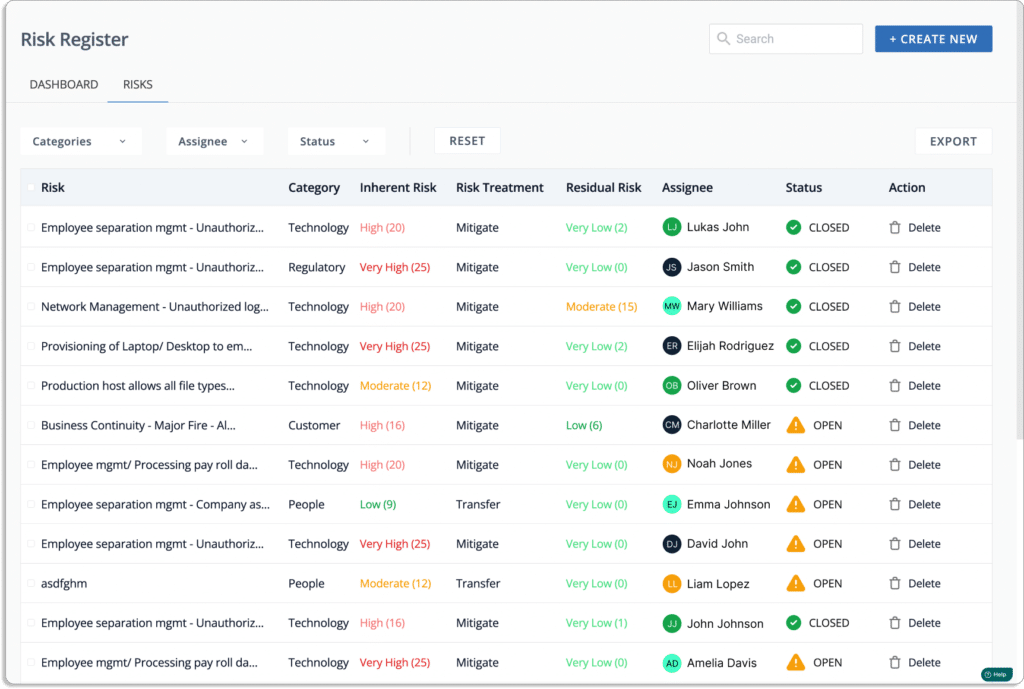
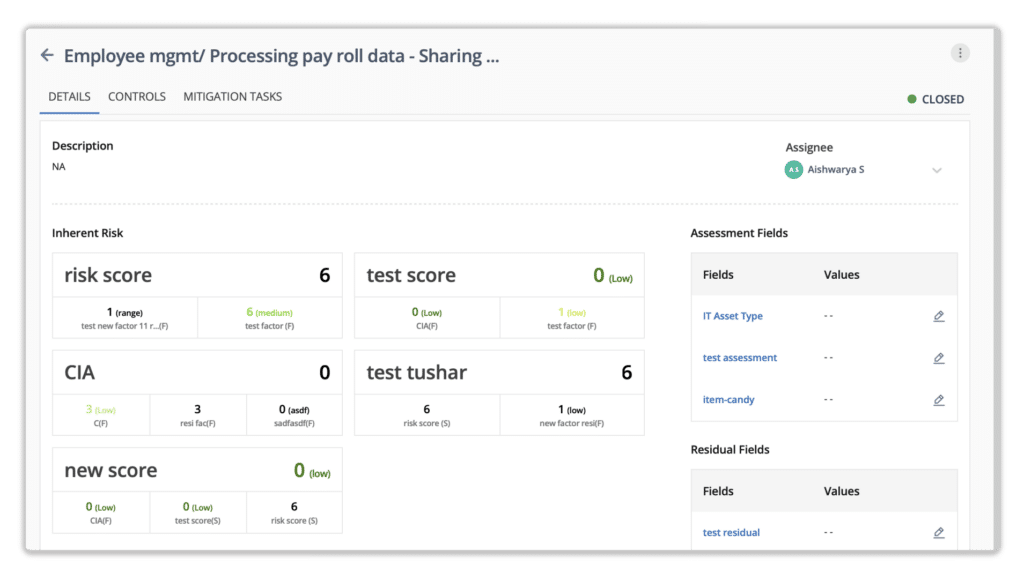
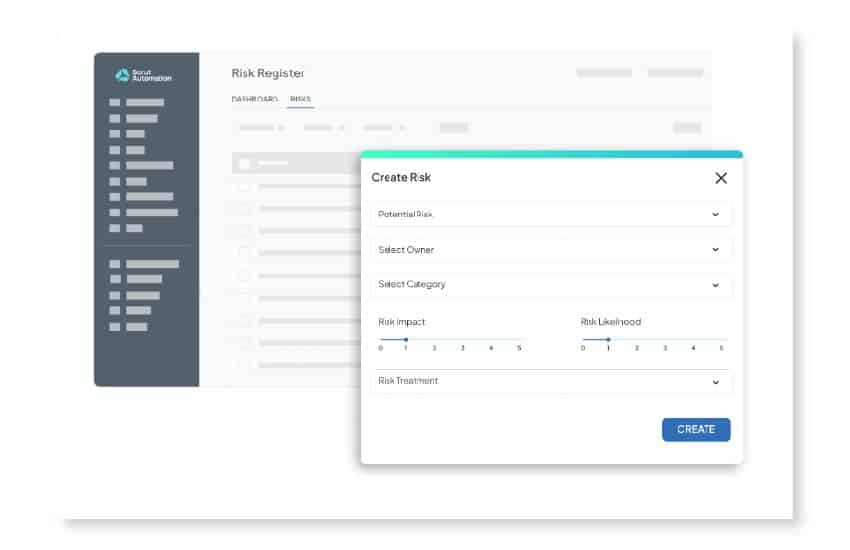
a. Flexible risk register
Scrut’s risk management begins with a flexible risk register, enabling you to log and monitor risks across various dimensions, including departments, applications, and impact. This comprehensive view ensures that no aspect of your organizational landscape is left unmonitored.
b. Configurable scoring criteria
Tailor risk identification and response with configurable scoring criteria. Scrut allows you to set up configurations and add scoring criteria, providing a robust framework to identify, assess, and respond to risks with precision.
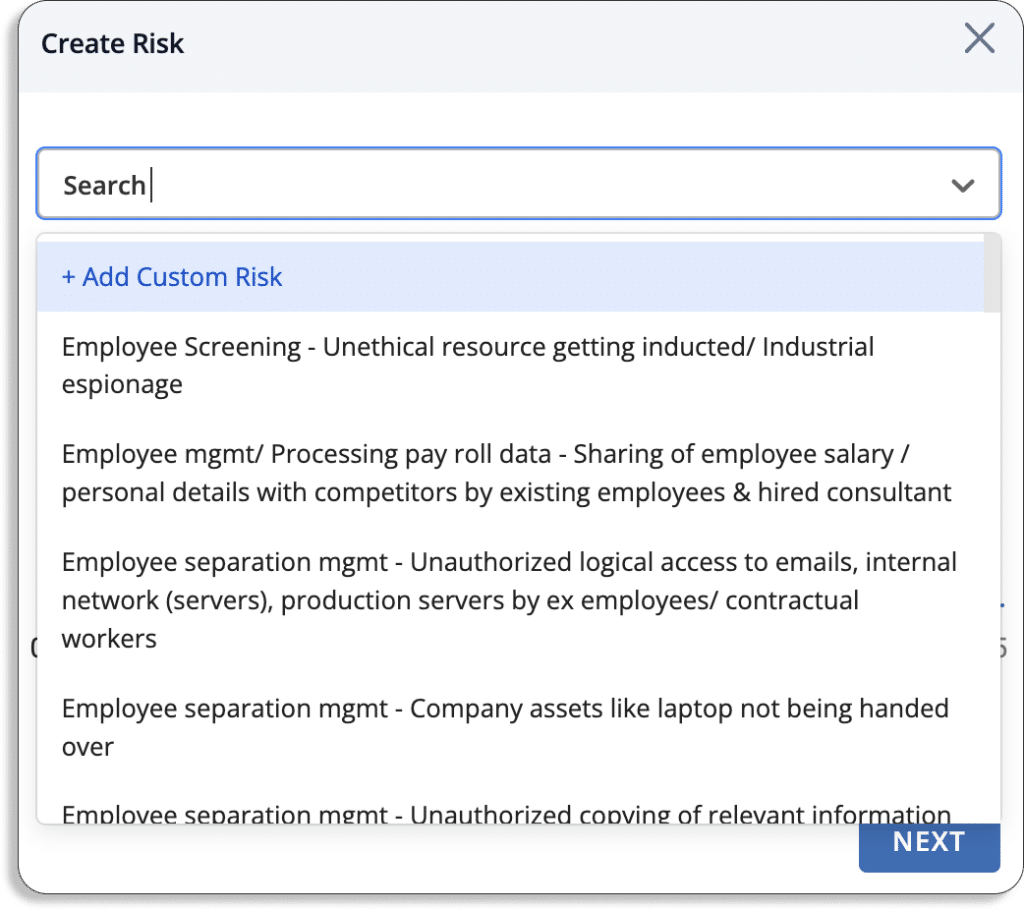
c. Templates & customization
Access Scrut’s extensive risk library or create your own risks manually, either individually or by importing spreadsheets. Custom field availability allows you to map additional values, ensuring that risk management aligns seamlessly with regulatory requirements and the unique needs of your organization.
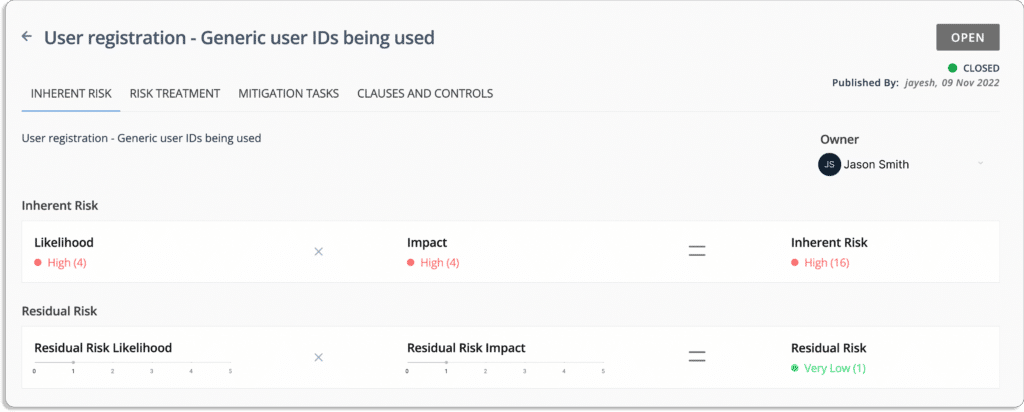
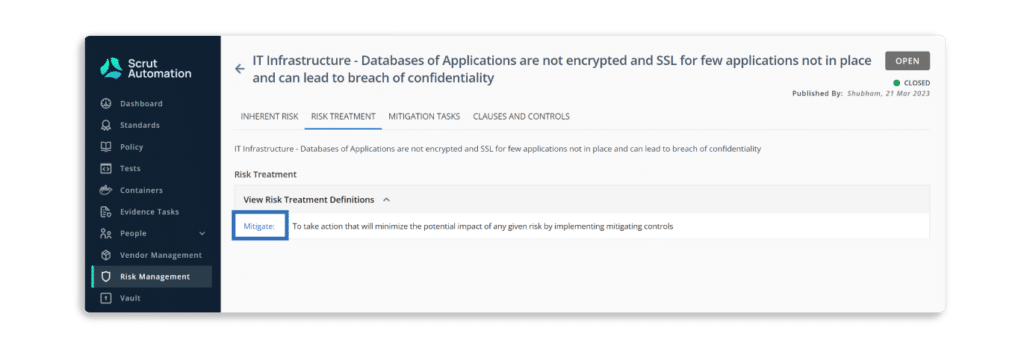
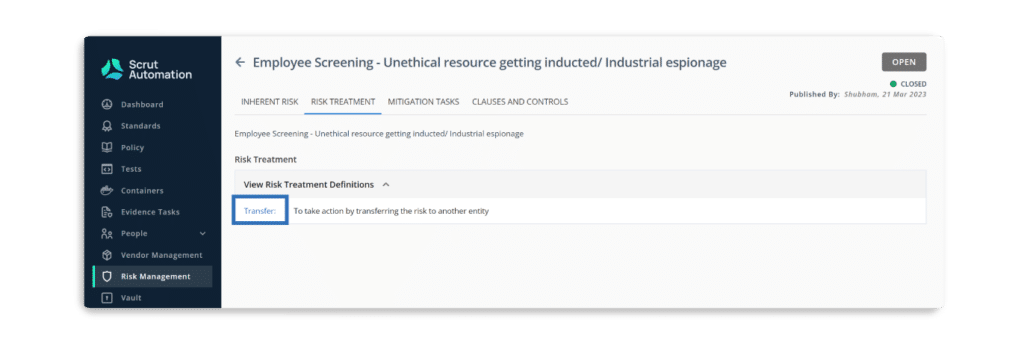
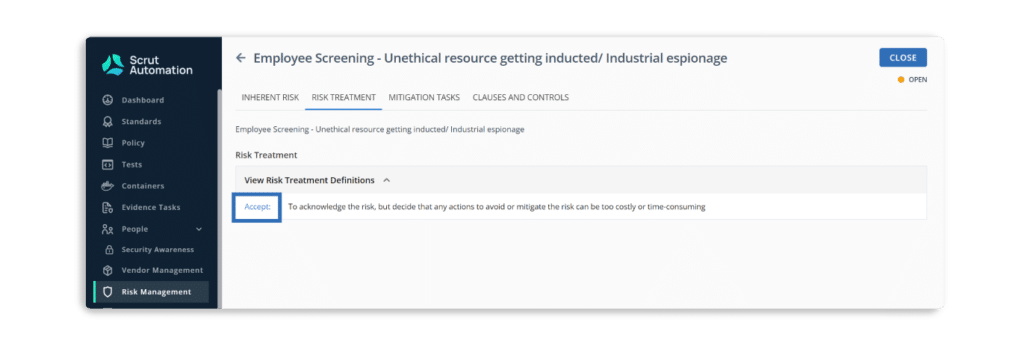
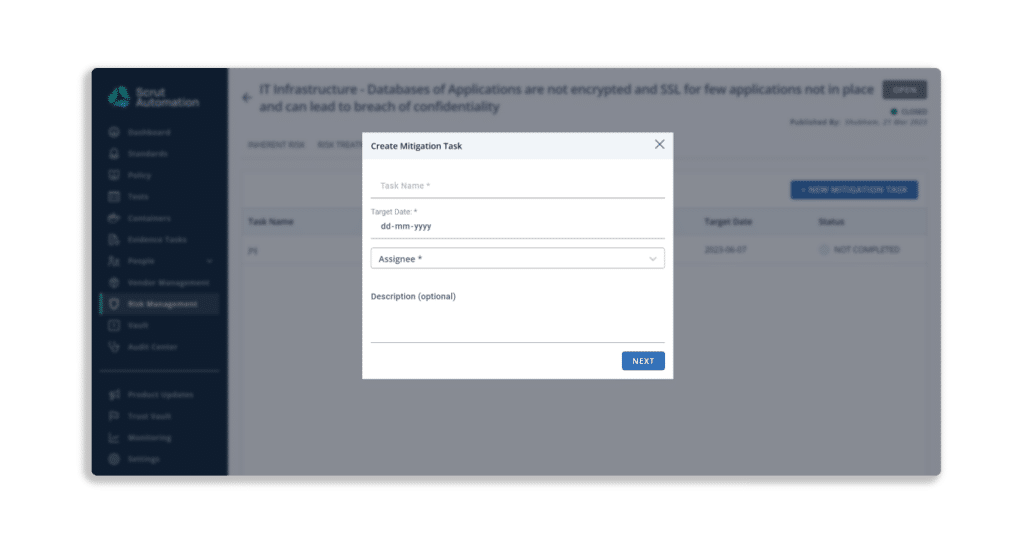
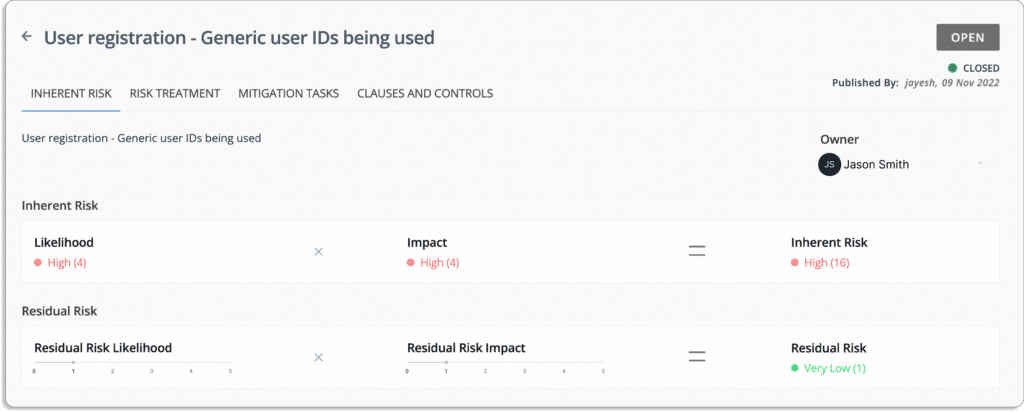
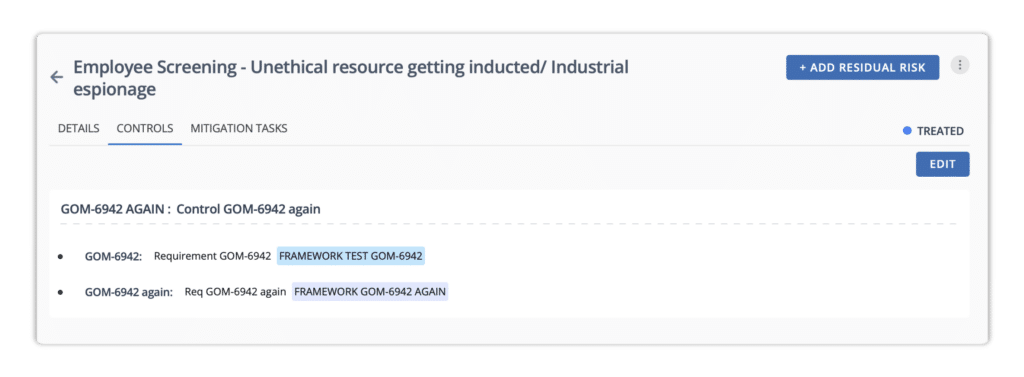
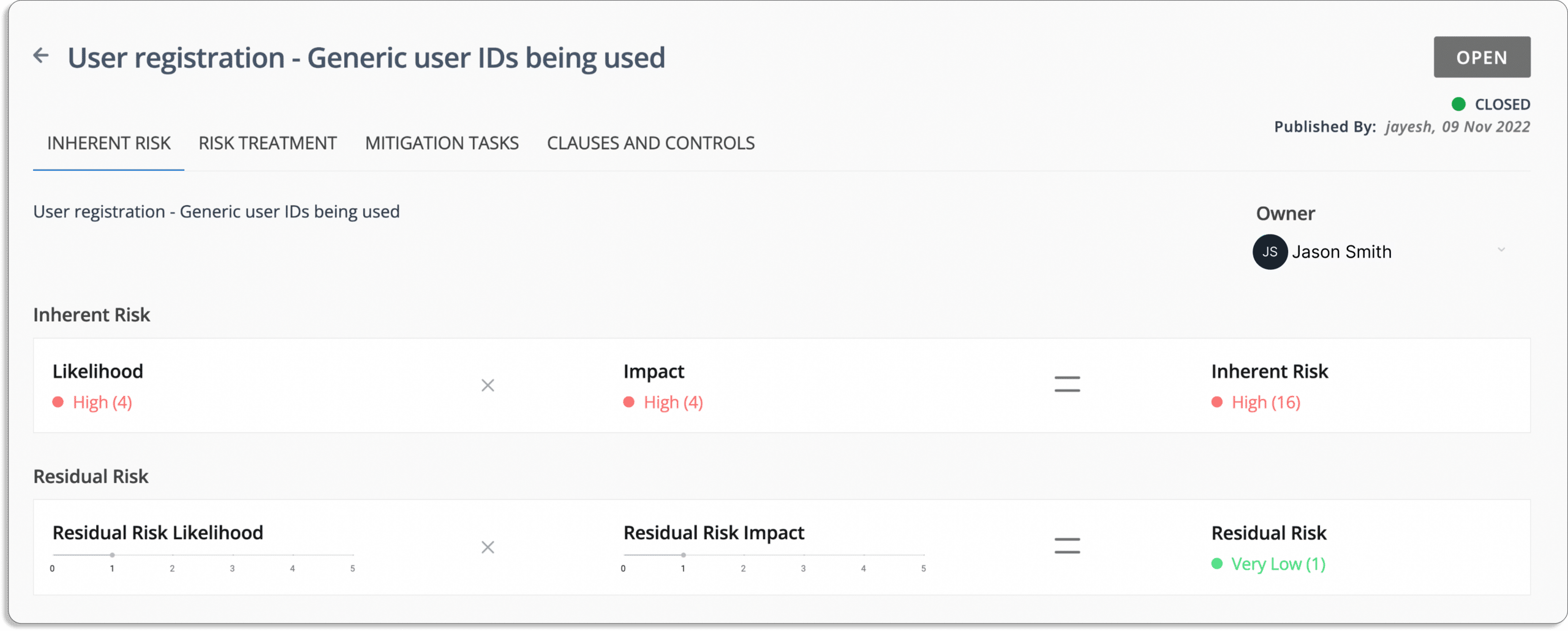
d. Assessments & treatment strategies
For each identified risk, Scrut facilitates the setting of scores and the subsequent definition of treatment strategies. Efficient workflows allow you to select relevant controls or requirements to mitigate risks, ensuring a systematic and strategic approach to risk management.
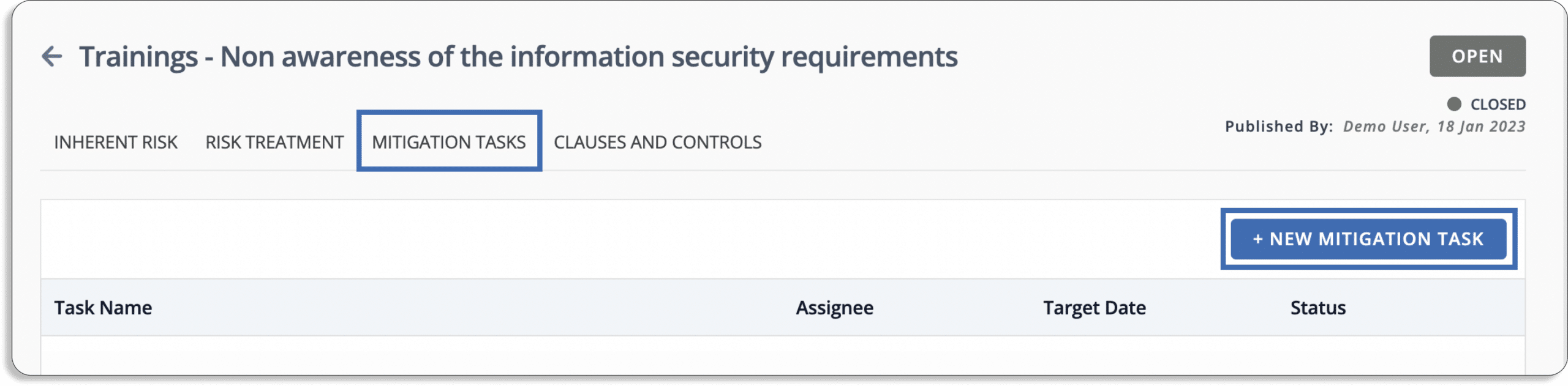
e. Mitigation beyond the basics
Scrut goes beyond one-size-fits-all mitigation tasks, providing a structured approach for addressing risks comprehensively. The platform allows you to add residual risks after mitigation, officially closing risks while acknowledging any remaining concerns. In response to new information, you can also reset risks for a fresh evaluation, ensuring a dynamic and adaptive risk management process.
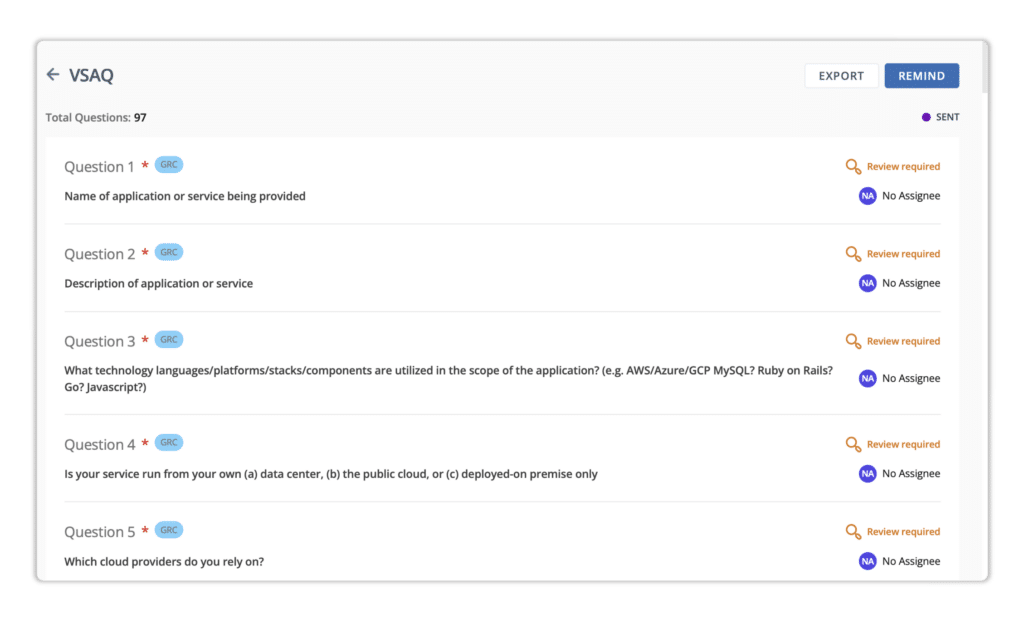
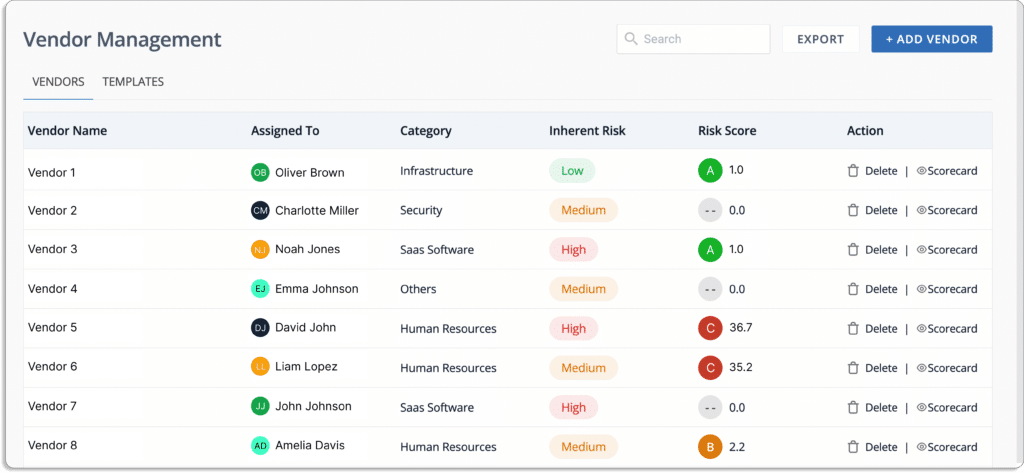
H. Vendor risk management
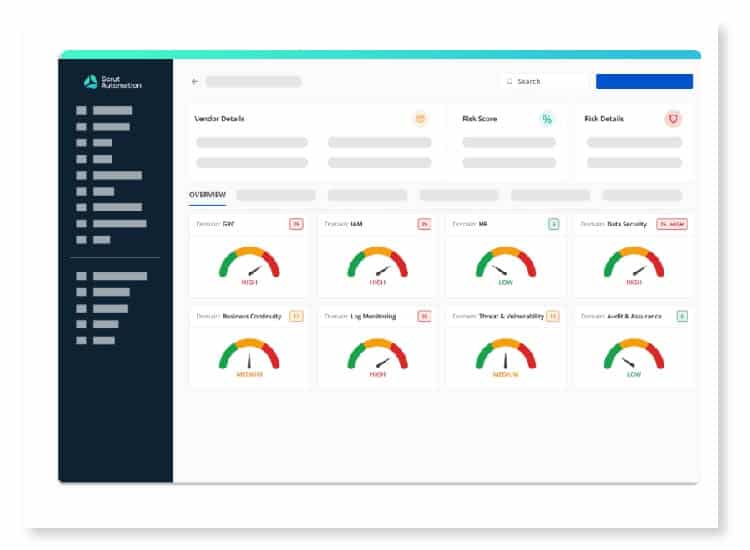
Scrut extends its capabilities to vendor risk management, offering a seamless and comprehensive approach from onboarding to actionable reporting.
a. Onboarding – Vendor discovery
Scrut simplifies the onboarding process with efficient vendor discovery. Seamlessly integrate vendors into your risk management landscape, ensuring a comprehensive view of potential risks associated with third-party relationships.
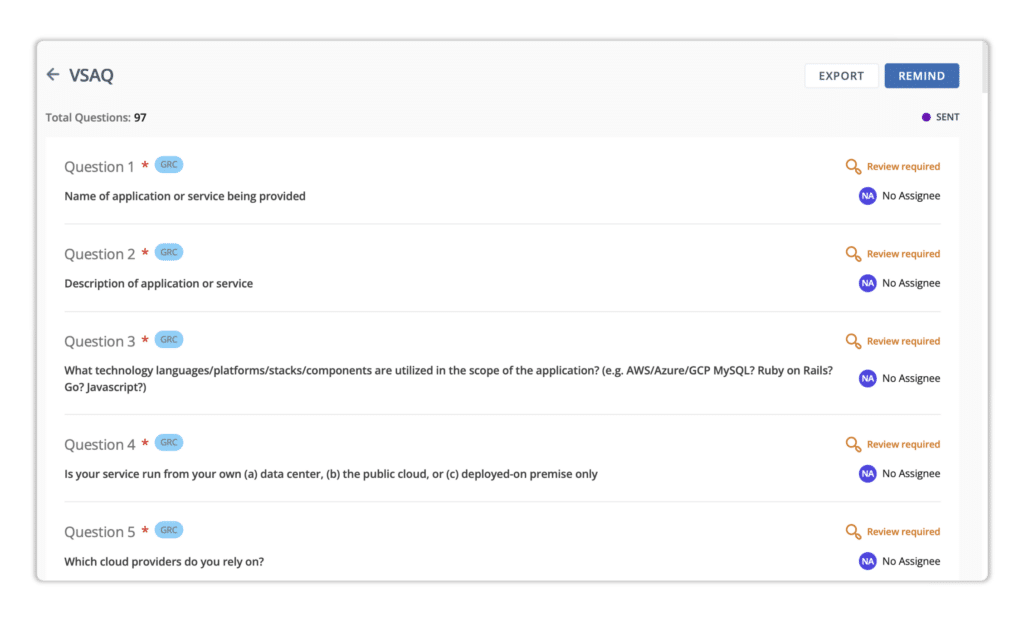
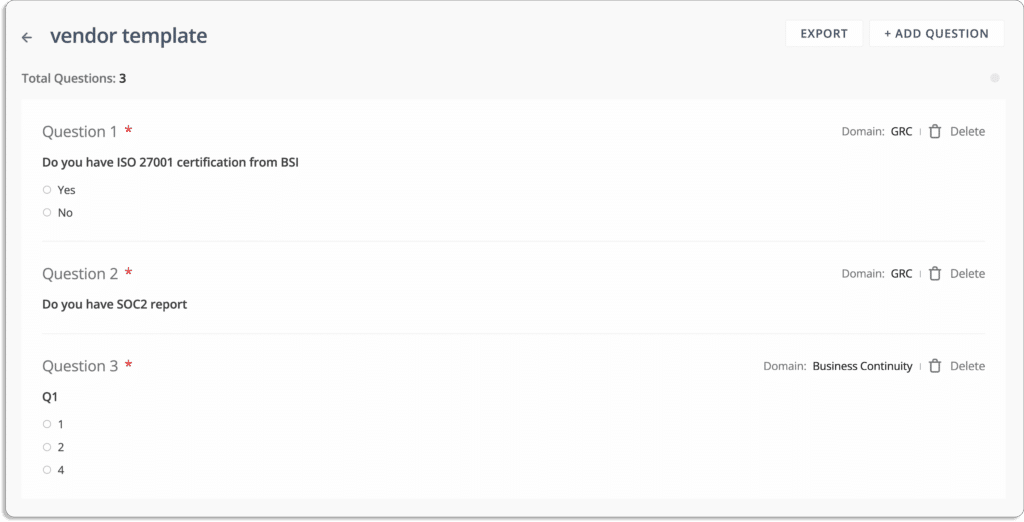
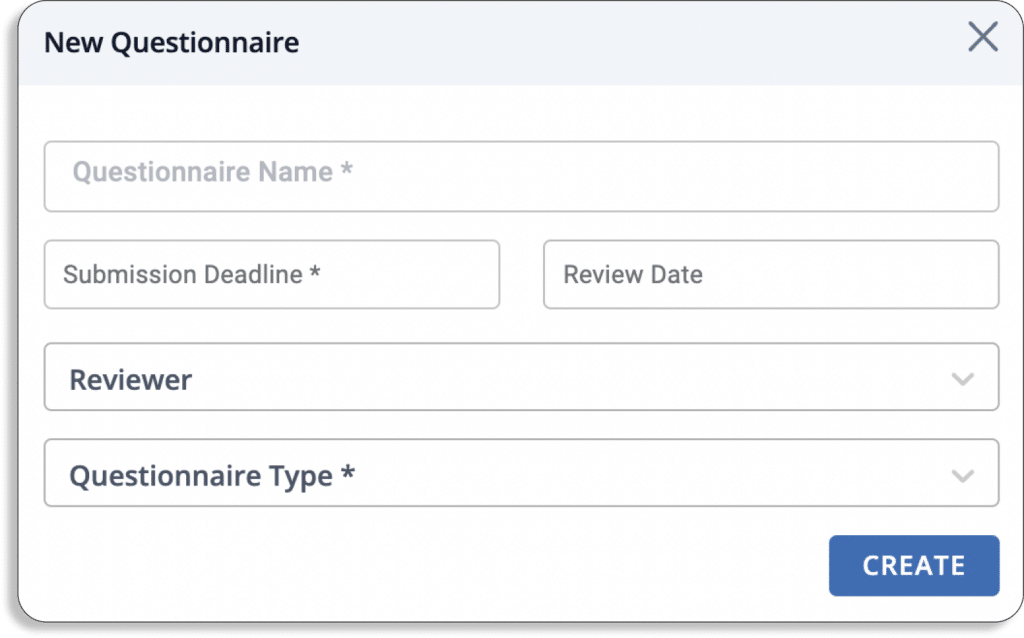
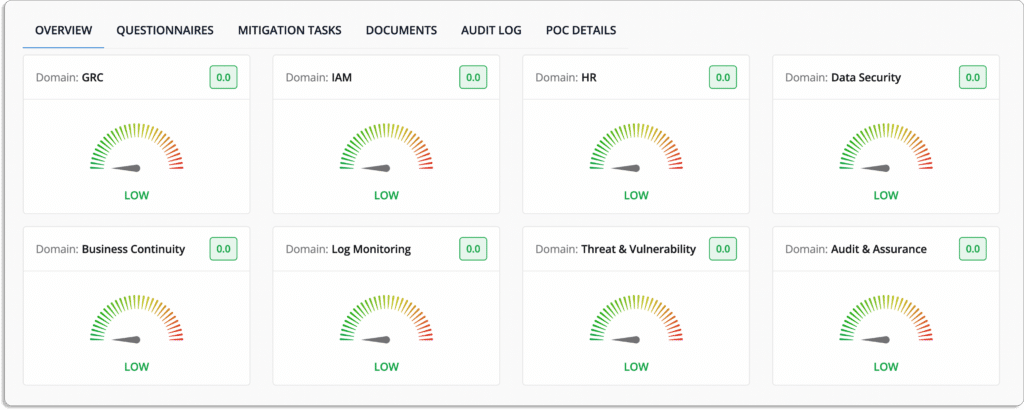
b. Assessment – Comprehensive questionnaires
The assessment phase is enhanced through Scrut’s robust questionnaire creation tools. Craft comprehensive questionnaires tailored to your specific needs, utilizing a response portal for vendors to provide detailed information. Custom fields offer flexibility in capturing additional information critical for a thorough evaluation.
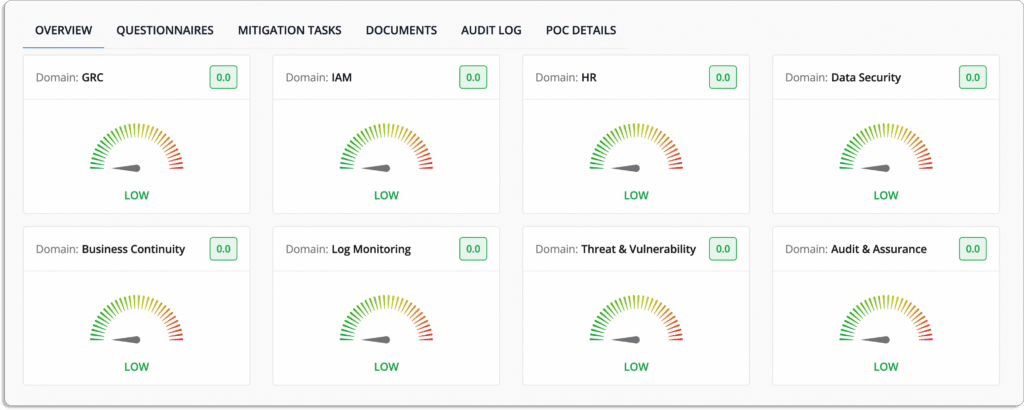
c. Evaluation & scoring
Scrut facilitates a structured evaluation and scoring process. Assess vendor responses against predefined criteria, ensuring a standardized approach to evaluating and scoring potential risks associated with vendor relationships.
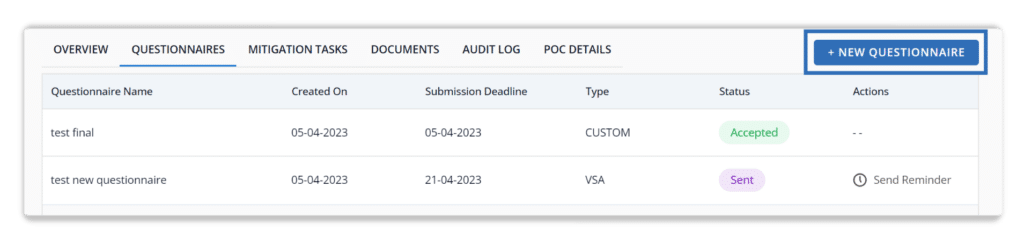
d. Questionnaire reminders + mitigation tasks
Keep the process on track with Scrut’s automated questionnaire reminders. Timely notifications ensure that vendors provide necessary information promptly. Additionally, the platform enables the assignment and tracking of mitigation tasks, ensuring a proactive stance in addressing identified risks.
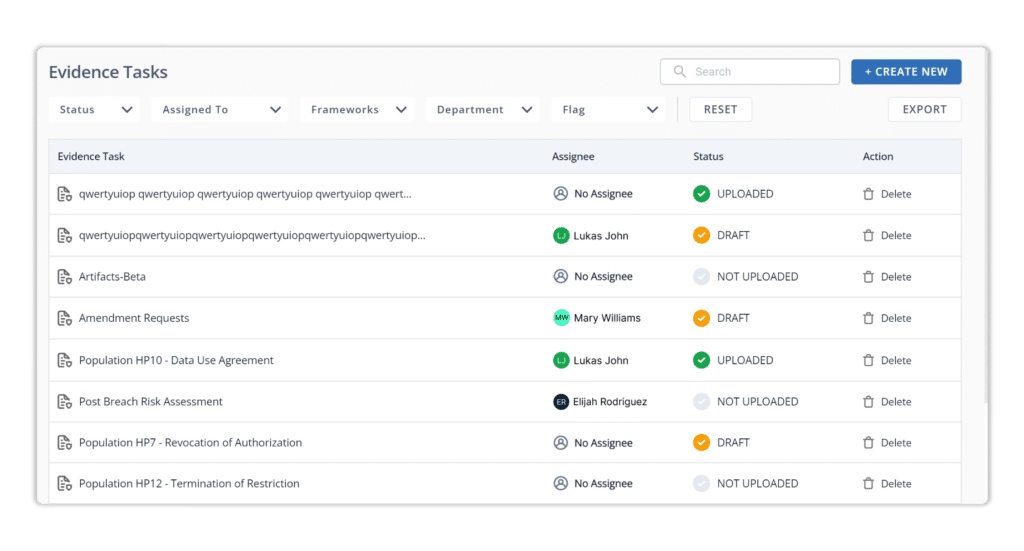
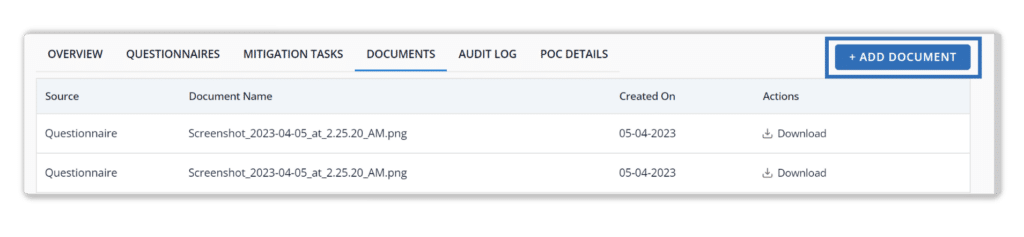
e. Document repository
Centralize all vendor-related documentation with Scrut’s document repository. This feature ensures that all relevant information, agreements, and communication are easily accessible, providing a centralized hub for efficient vendor risk management.
f. Actionable reporting
Scrut doesn’t just provide data; it translates information into actionable insights. Leverage Scrut’s reporting capabilities to gain a comprehensive understanding of vendor risk landscapes. These actionable reports empower informed decision-making and strategic risk mitigation.
I. Trust module
Scrut’s Trust Module is your strategic ally, empowering you to proactively showcase your information security posture, fostering trust, and expediting deal closures with prospective partners.
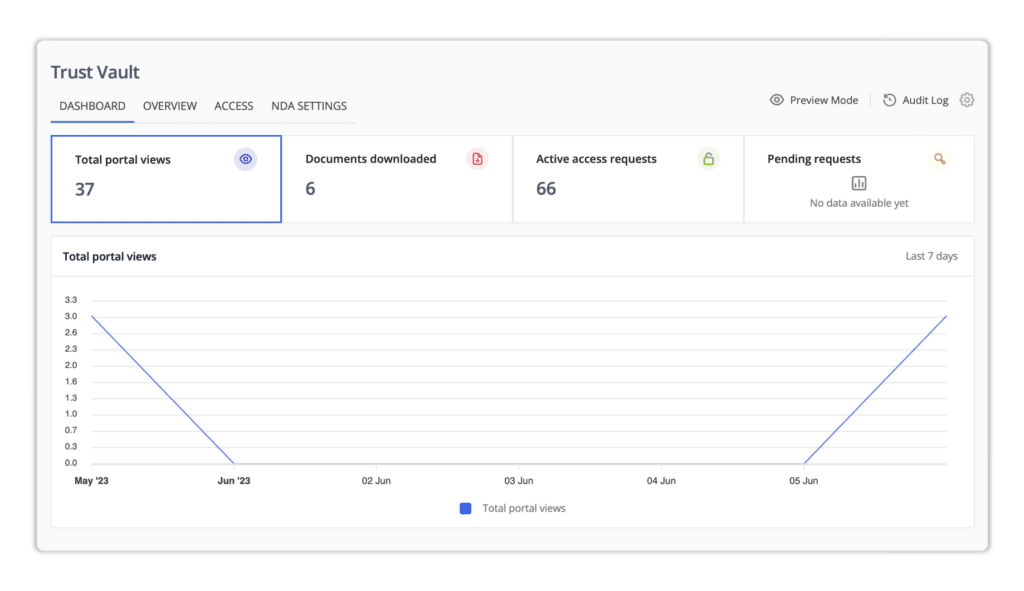
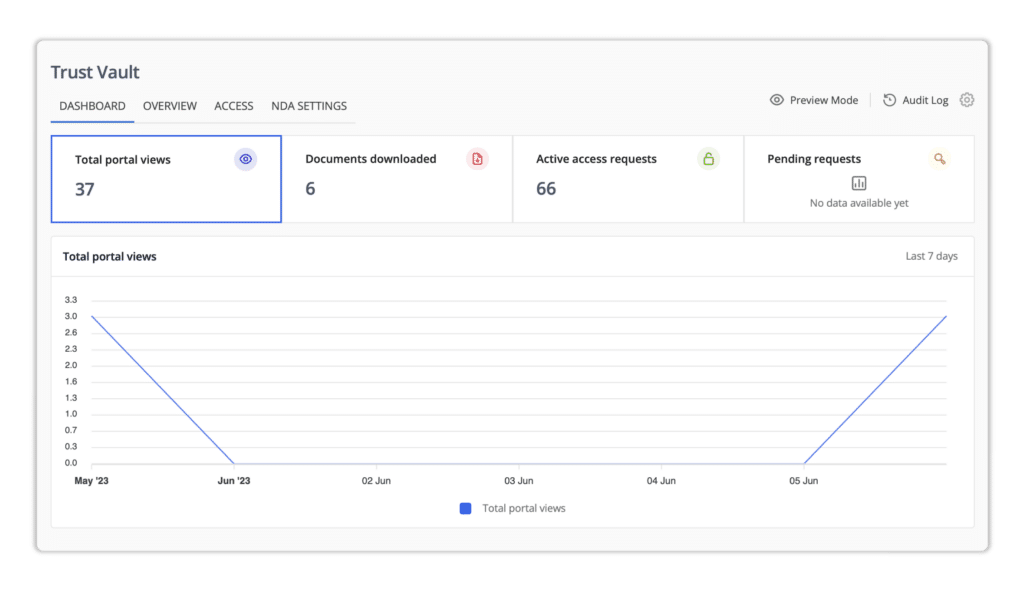
a. Trust Vault
The Trust Vault within Scrut brings transparency to your compliances and control-level documentation, ensuring your commitment to information security standards is readily apparent.
It safeguards sensitive information, allowing access based on Non-Disclosure Agreements (NDAs) and implementing time-gated access. This dual-layer protection ensures confidentiality and secure information sharing.
Trust Vault streamlines security reviews with effective monitoring of requests through the dashboard, expediting the entire process and contributing to swift decision-making.
b. KAI
Scrut’s KAI, armed with artificial intelligence, transforms the security questionnaire response process. By scanning controls and documentation, KAI generates responses that are not just generic but uniquely tailored to your organization’s specifics.
Bid farewell to unnecessary communication loops between teams. KAI minimizes back-and-forth by providing accurate and comprehensive responses, saving valuable time and optimizing resource utilization.
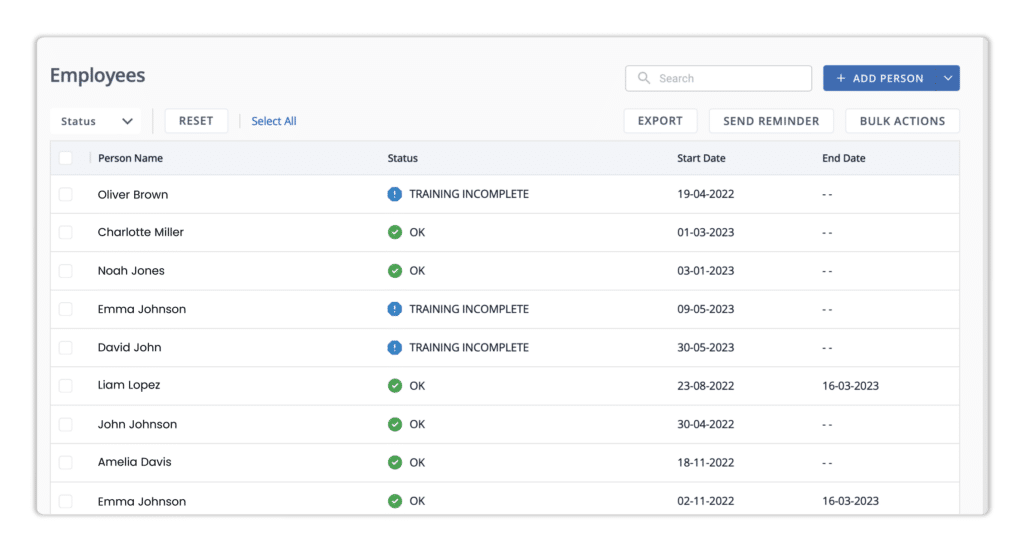
J. People Module
Scrut’s People Module is your comprehensive solution for monitoring and managing compliance among employees, enhancing your internal security posture, and fostering a culture of security awareness.
a. Comprehensive compliance oversight
Scrut allows you to govern each employee’s system and device compliance with a detailed technical overview. Gain insights into the compliance status of individual devices, ensuring a proactive approach to internal security.
b. Policy acceptance monitoring
Scrut provides a thorough organizational view to monitor and increase policy acceptance rates. Utilize interactive dashboards to assess the policy compliance landscape across your entire organization.
Facilitate policy adherence with ease using 1-click reminders, ensuring that employees stay informed and compliant with organizational policies.
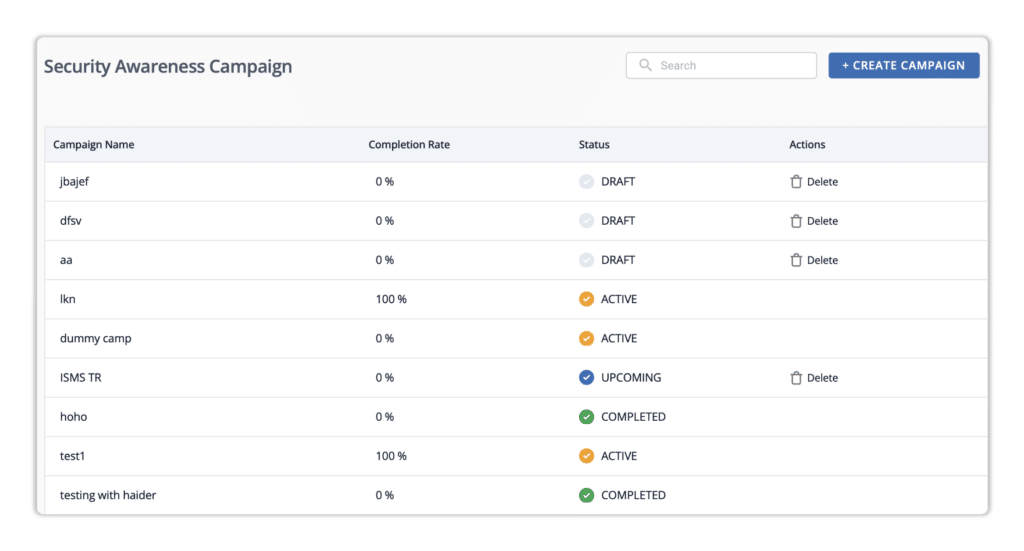
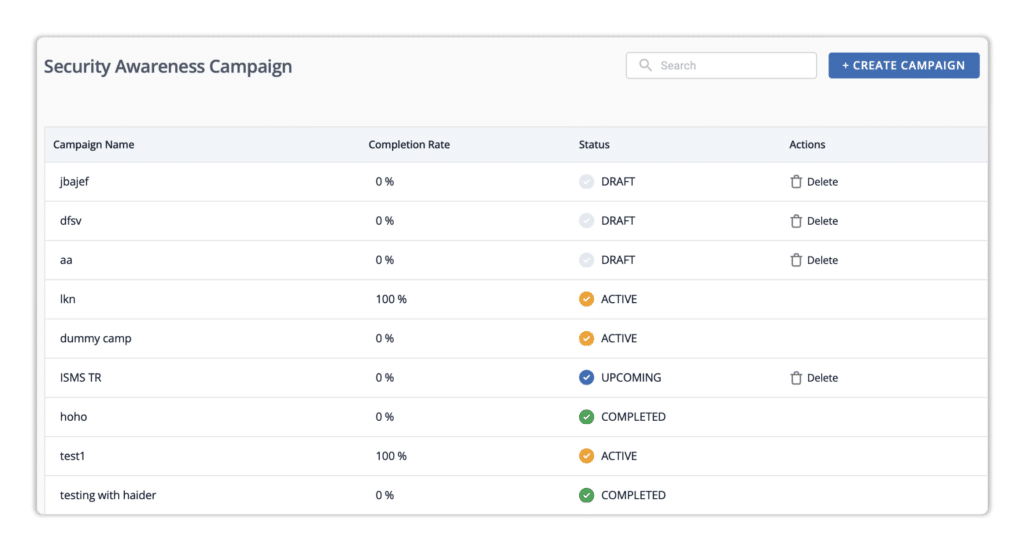
c. Security awareness campaigns
Create and deploy security awareness campaigns tailored to your organizational needs. These campaigns may include multiple quizzes to engage and educate employees on crucial security practices.
Scrut’s interactive dashboards offer a real-time view of completion rates, statuses, and other pertinent information. Track the effectiveness of campaigns and identify areas for improvement.
d. Employee lifecycle management
Seamlessly manage the employee lifecycle by integrating with your Human Resource Information System (HRIS). Scrut allows you to connect with your HRIS to streamline onboarding and offboarding processes.
Offboard employees directly from the platform, ensuring a smooth transition and minimizing security risks associated with employee departures.
K. Custom Requirements
Scrut understands that one size doesn’t fit all in the realm of compliance. That’s why we empower you with a suite of tools under Custom Requirements, allowing you to mold your compliance initiatives according to your organization’s distinct needs.
a. UCF integration
Scrut features UCF, a centralized repository of controls. This integration enables you to map various compliance requirements effortlessly across different standards. Experience a holistic understanding of controls, reducing the complexity associated with diverse compliance landscapes.
b. Custom frameworks
Craft bespoke compliance frameworks with Scrut’s custom framework capabilities. Draw from existing policies and evidences to create frameworks that align precisely with your internal requirements. This flexibility ensures that your compliance efforts are not just efficient but also tailored to your business objectives.
c. Policy creation
Rely on Scrut for expert guidance in policy creation. Access Infosec experts who can assist you in crafting policies that align with the latest industry standards, tailoring them to your organization’s unique needs. Scrut simplifies the policy creation process, ensuring alignment with regulatory requirements.
d. Controls creation
With Scrut, you have the ability to define your controls based on your specific security and compliance needs. This granular control creation ensures that your organization’s unique requirements are met, providing a tailored approach to safeguarding your digital assets.
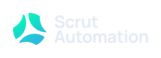
e. Integrations
Recognizing the importance of collaboration, Scrut seamlessly integrates with various tools and applications. Ensure that compliance is seamlessly woven into your existing workflows by integrating Scrut with project management tools and other applications, creating a cohesive work environment.
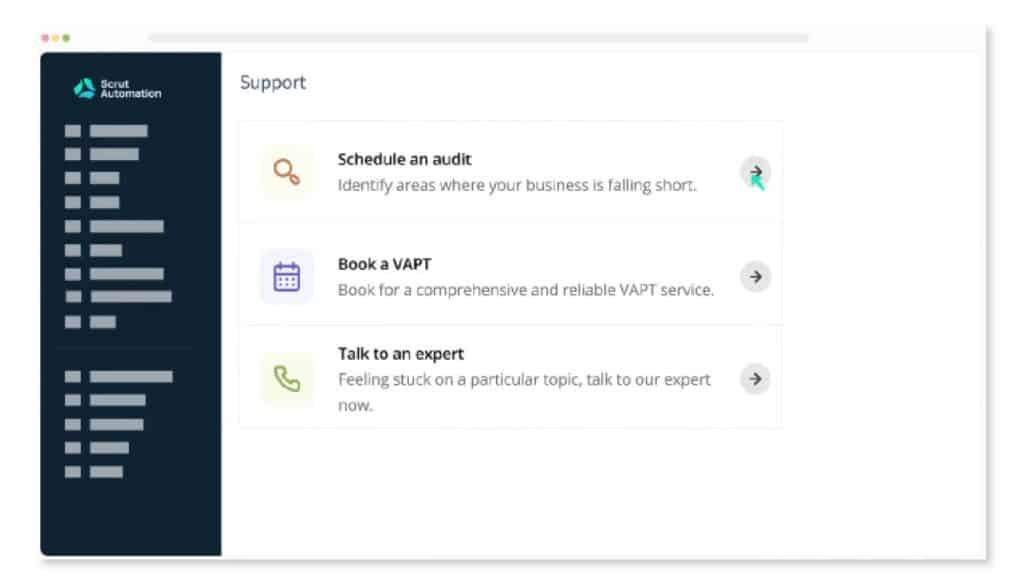
L. Additional support
Scrut goes beyond the standard offerings to provide additional support, ensuring a comprehensive and fortified compliance journey for your organization. This includes specialized assistance in Vulnerability Assessment and Penetration Testing (VAPT) and managed support throughout audits.
a. Vulnerability Assessment and Penetration Testing (VAPT)
Scrut offers a proactive approach to security with specialized VAPT services. Conduct thorough examinations of your systems to identify vulnerabilities and potential exploits. This ensures a robust defense against emerging threats and vulnerabilities, fortifying your overall security posture.
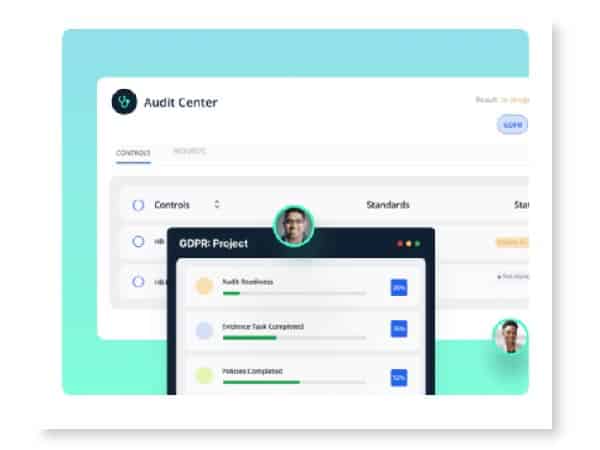
b. Managed support in audits
Navigating audits becomes a seamless experience with Scrut’s user-friendly interface and intuitive tools. The platform simplifies the audit process, ensuring that your organization not only meets but exceeds compliance standards effortlessly.
Scrut provides hands-on assistance throughout the audit process. Our dedicated support includes expert guidance, ensuring that your organization remains in full compliance with industry standards and regulations. Rely on our expertise to navigate the complexities of compliance requirements successfully.

2. Drata
Drata offers a comprehensive security and compliance automation software that efficiently monitors and gathers evidence of security controls. It simplifies compliance processes through automated monitoring, evidence collection, and asset tracking.
Supported frameworks by Drata encompass SOC 2, ISO 27001, HIPAA, GDPR, PCI DSS, CCPA, ISO 27701, NIST CSF, and more.
With Drata, you gain insight into your organization’s security posture, compliance status, and control. Additionally, it seamlessly integrates with your SaaS applications, consolidating compliance status into a single platform for ease of management.
Pros
- Almost effortless setup
- Comprehensive documentation that helps to get familiar with various topics
- Centralized visibility of all your personnel and assets
- Gives you insights into what compliance requirements need your attention
Cons
- Lacks some custom integrations with other systems
- Some integrations (Checkr, GCP) don’t work properly
- The inability to customize what to monitor poses challenges for the engineering team

3. Hyperproof
Hyperproof is a robust security assurance and compliance operations platform designed to assist organizations in meeting regulatory requirements effectively. It enhances compliance and risk management by streamlining processes and automating tasks.
This platform provides a comprehensive solution for comprehending compliance needs, overseeing internal controls, and establishing audit processes and workflows. With Hyperproof, you can seamlessly adapt to any compliance framework based on your business needs, reducing manual efforts associated with control mapping, testing, and evidence collection.
Hyperproof supports various compliance frameworks including SOC 2, ISO 27001, NIST 800-53, NIST CSF, NIST privacy, PCI, SOX, and more. Moreover, it enables users to upload custom frameworks and manage them within the platform for added flexibility and convenience.
Pros
- Role-based access management ensures users have access to only their tasks and are focused on what they should be
- Easily integrates with numerous tools, and automates evidence collection
- Easy tasks management: Tasks can be viewed on either a Kanban board or a simple grid
Cons
- Inability to configure and customize notifications
- Occasionally, the system stops functioning and has to be refreshed to work again

4. AuditBoard
AuditBoard is a cloud-based audit, risk, and compliance management platform that helps comply with SOC 2, ISO 2700x, NIST, CMMC, PCI DSS, and more.
The platform centralizes all your compliance frameworks in a single location and helps you manage efficiently. It reduces manual tasks, avoids duplicative assessments, and streamlines reporting with automation. The tool eliminates manual follow-ups with automated alerts and reminders to stakeholders.
AuditBoard identifies the compliance gaps between your organization and industry standards and ensures that your organization stays compliant with the changing requirements.
Pros
- Single hub for all risks and controls
- Easy implementation and customizable as per your needs
Cons
- Incapable of third-party risk management
- Confusing to set up new controls, processes, etc.

5. LogicGate
With LogicGate’s Risk Cloud platform, you can manage and improve your governance, risk, and compliance (GRC) program with ease. LogicGate proactively tracks and responds to issues and provides insights.
The platform helps you with the entire compliance lifecycle— from identifying the right rules to keeping tabs on the effectiveness of your compliance programs. LogicGate helps you communicate processes to remain compliant, assess and manage risks across the organization, and protect your business from threats.
Pros
- Highly customizable platform that doesn’t require technical knowledge to make changes
- In-depth training on using the platform and getting complaint for administrators
Cons
- Options for bulk changes are not available
- Steep learning curve; you have to spend good time training employees

5. Sprinto
Sprinto is a compliance automation software that helps companies automate information security compliances and privacy laws, including SOC 2, ISO 27001, HIPAA, GDPR, and PCI DSS. It automatically creates security documents and enables real-time centralized monitoring.
It automatically maps your work to audit requirements and collects evidence. Sprinto detects new joiners and triggers onboarding workflows. It generates downstream tasks around background checks, security training, policy acknowledgments, access control, etc., and tracks them to completion.
Pros
- Provides real-time evidence-tracking
- The interface is clean and easy to understand and navigate
Cons
- You need to reach out to their support team due to missing information in the knowledge base
- Sync delay: Consumes time in monitoring and fetching data

6. Vanta
Vanta is an automated security and compliance management platform. It helps your organization remain compliant by monitoring, improving your security posture, and meeting requirements for standards like SOC 2, HIPAA, ISO 27001, PCI DSS, etc.
Vanta trust reports allow you to avoid repetitive tasks and provide customized reports. It gives you insights on compliance violations and helps you avoid hefty audit fines.
It has integrations with cloud service providers, identity providers, task trackers, and many more to automatically collect evidence. Additionally, it helps you manage vendor risks.
Pros
- Provides a large library for pre-built policies and process templates
- Enables sharing audit access to auditors directly on the platform
Cons
- The built-in risk assessments are not too in-depth,
- Checkr International is not supported resulting in fail tests for international employees
- Setup is tedious and takes a lot of time

7. Secureframe
Secureframe helps companies comply with compliance frameworks like SOC 2, ISO 27001, PCI DSS, CCPA, GDPR, and HIPAA. As compliance is a continuous process, it helps you always remain compliant and sends alerts and reports on any deviation.
With a streamlined workflow, Secureframe automates most of the compliance process as per your business requirements. In addition, it integrates with several service providers to help you stay compliant and make you audit-ready.
Pros
- Policy builder saves a lot of time
- Good number of integrations
Cons
- Sends false notifications sometimes
- Many processes require a lot of manual work that could be automated
8. Carbide
Carbide identifies gaps, automates the compliance process, and accelerates your compliance programs. It provides a hassle-free way to compliance, starting from mapping your security and privacy policies to various frameworks and regulatory controls to managing audits.
This compliance automation software makes you aware of shortcomings in your audits and guides you to overcome them. It reduces manual time and effort by integrating with your systems and automatically collecting evidence for audits.
Pros
- User interface is simple
- Easy to add and edit content
Cons
- Takes time to load

9. Strike Graph
Strike Graph is a compliance automation software that simplifies security certifications for SOC 2, ISO 27001, HIPAA, and more. It assesses risk and assigns controls to create a cybersecurity program that matches your business requirements.
Moreover, it brings your auditor on the same platform and helps to pass your audit and get certified. Strike Graph maintains a state of compliance with automated tracking and evidence collection. The compliance automation platform tracks and manages all your evidence requirements from one location.
Pros
- Provides a straightforward evidence package
- Good customer support
Cons
- Lacks in automation and integrations
- There are a few UI errors

Wrapping up
Navigating the complexities of regulatory frameworks and industry standards is a significant challenge for organizations of all sizes. As these challenges continue to evolve, the importance of compliance software cannot be overstated.
Our list of the top 9 compliance automation software solutions available in 2024 offers streamlined approaches to compliance management, empowering organizations to stay ahead of the curve and mitigate risks effectively.
From automating tedious compliance tasks to providing comprehensive risk management and vendor oversight, these platforms offer a wide range of features tailored to meet the unique needs of modern businesses.
If you’re interested in exploring Scrut’s incredible compliance automation and risk monitoring capabilities, make sure you schedule a demo with us today!