In this article, we will explore the most popular GDPR compliance tools available in the market and how to select the one that fits your need.
GDPR compliance software speeds up the compliance process by eliminating the efforts required to prepare for and complete an audit.
Here are some key benefits of GDPR compliance software compared to doing it via consultants or in-house.
GDPR compliance automation tools:
- Come with pre-built policy templates to quickly get started
- Helps you collaborate with team members
- Automate evidence collection to eliminate manual work
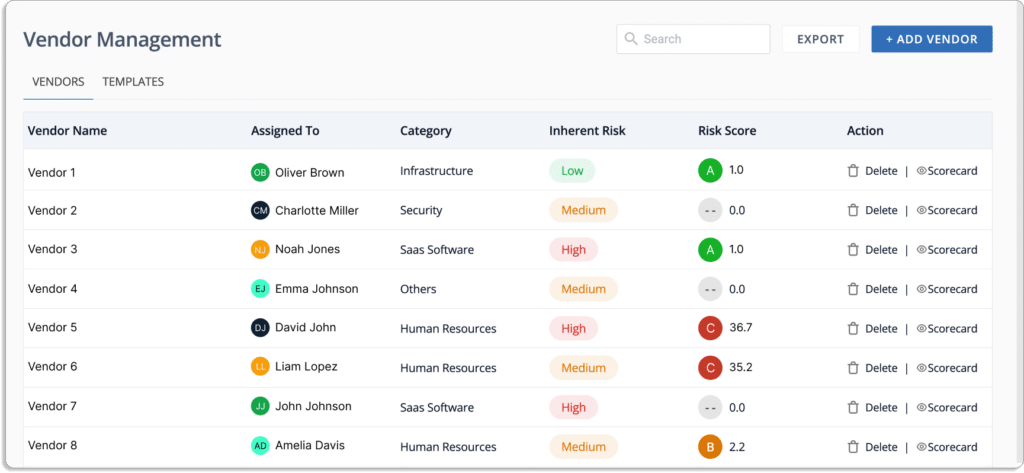
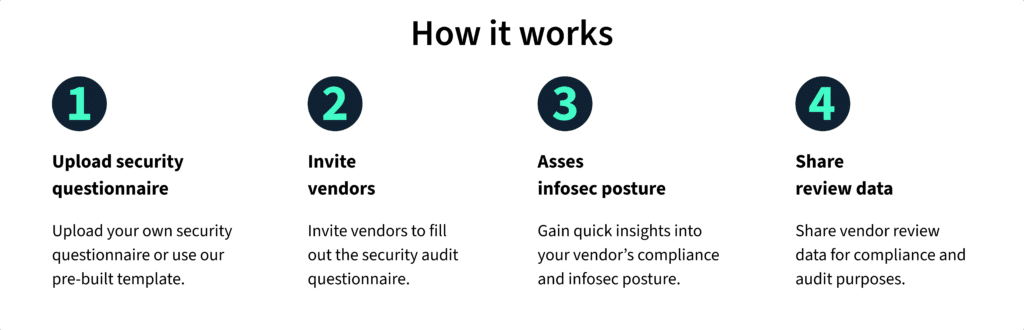
- Helps you with vendor risk management
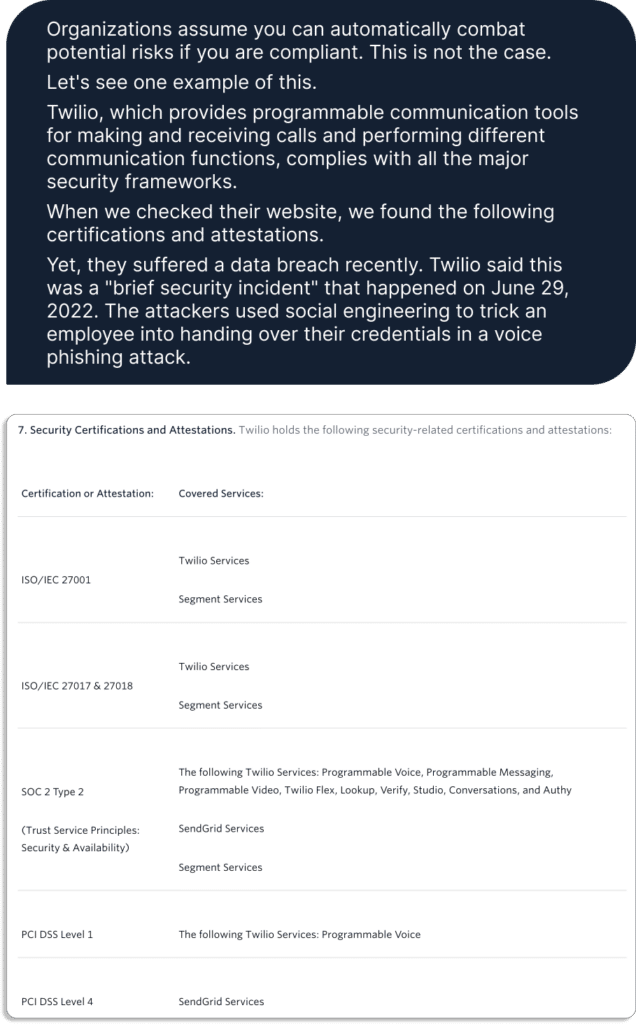
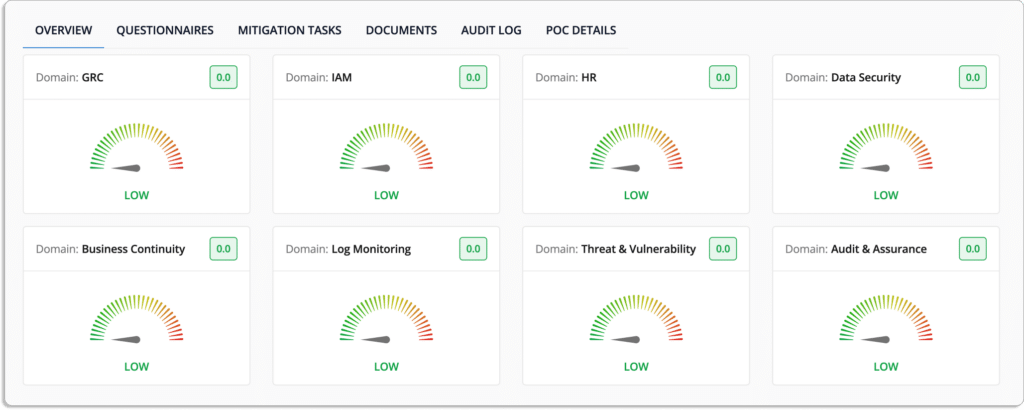
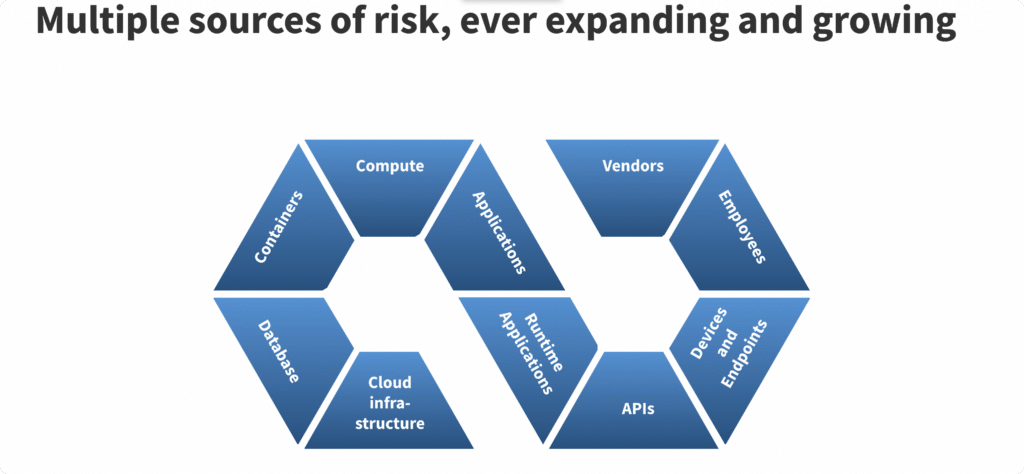
- Gives you visibility into all your InfoSec risks
- Monitor cloud environment for security and compliance misconfigurations
- Some tools like Scrut can help you train your employees for security awareness
- Allows you to collaborate with auditors on the platform
How to select a GDPR Automation Software?
There are many GDPR compliance software available in the market. Before you choose one, here are some important things you need to keep in mind to determine which tool is best for you:
- It should be one stop solution for getting compliant
There are many jobs involved when preparing for GDPR audit, like doing gap assessment, vulnerability assessment and penetration testing (VAPT), finding CPAs, etc.
Some providers, like Scrut, have a partnership with these vendors for a seamless experience. A single-window solution prevents the hassle of searching for multiple partners for various jobs.
- It should come with pre-built templates
A GDPR compliance software that has pre-built templates helps you to get started quickly, as creating policies from the ground up for GDPR requires a lot of effort and time.
Some vendors, like Scrut, come with in-built policy editors to help you build custom policies per your organization’s requirements.
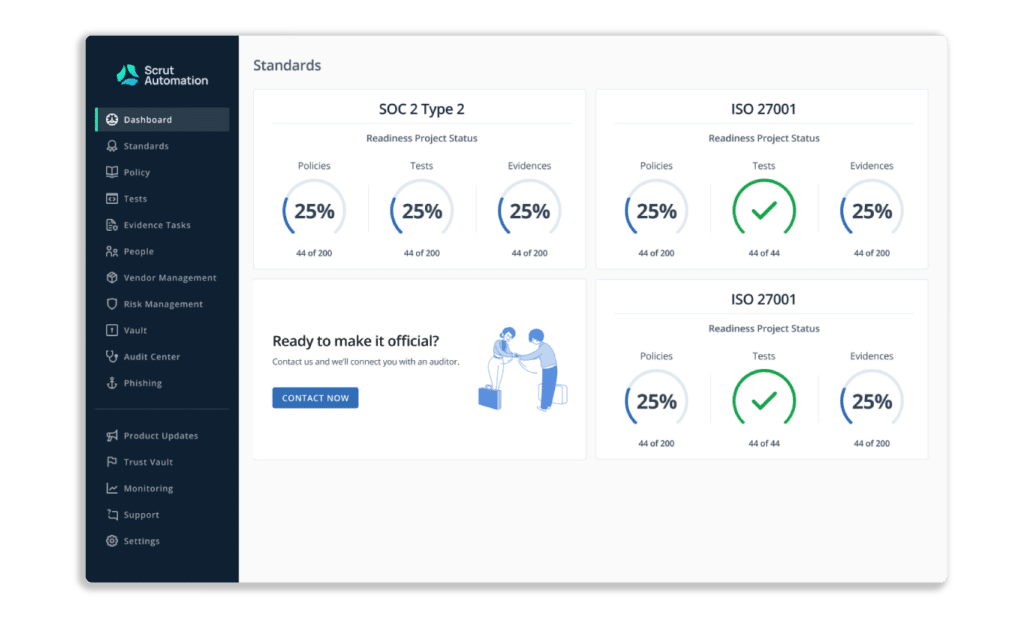
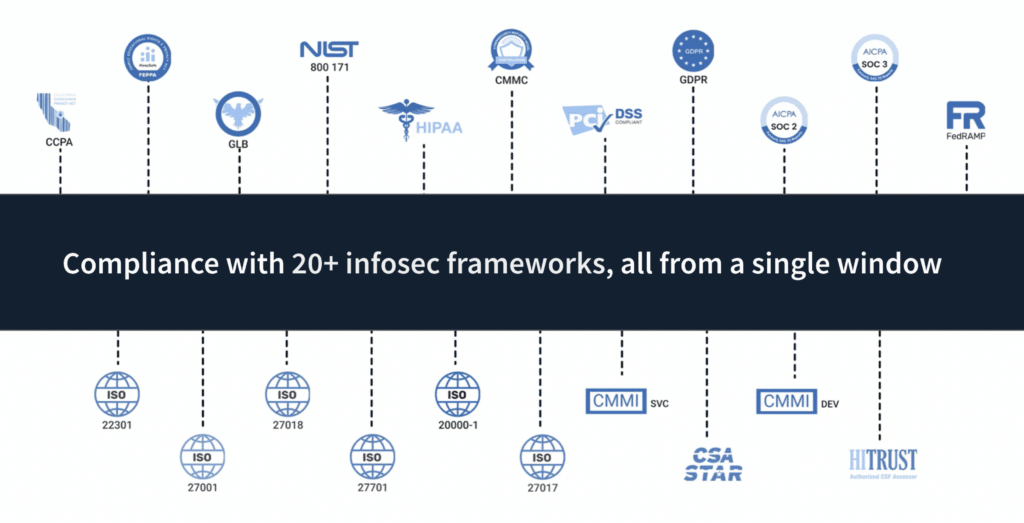
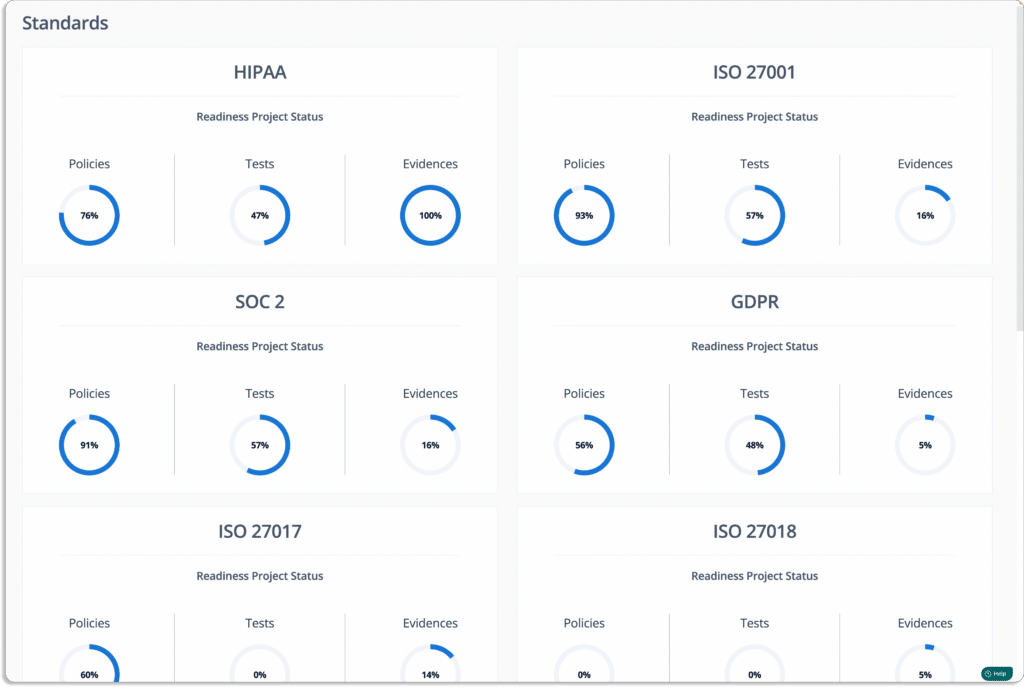
- It should support multiple compliance frameworks
Many times, GDPR is not the only compliance framework you would be required to be compliant with. In future, you may go for other security or privacy frameworks, such as ISO 27001, SOC 2, HIPPA, PCI DSS etc. based on your organizational requirements.
Hence, the tool must not be just limited to GDPR solution, but should help you with all the frameworks that you will need in future. For example, Scrut comes with over 20+ privacy and security frameworks out-of-box.
- All the changes on the platform must be traceable
The tool must keep track of all the changes taking place in the cloud environment that may affect your compliance posture. It must also log all actions taken by users, changes made to policy documents, and API calls made through any integration, and monitor it in the form of audit logs.
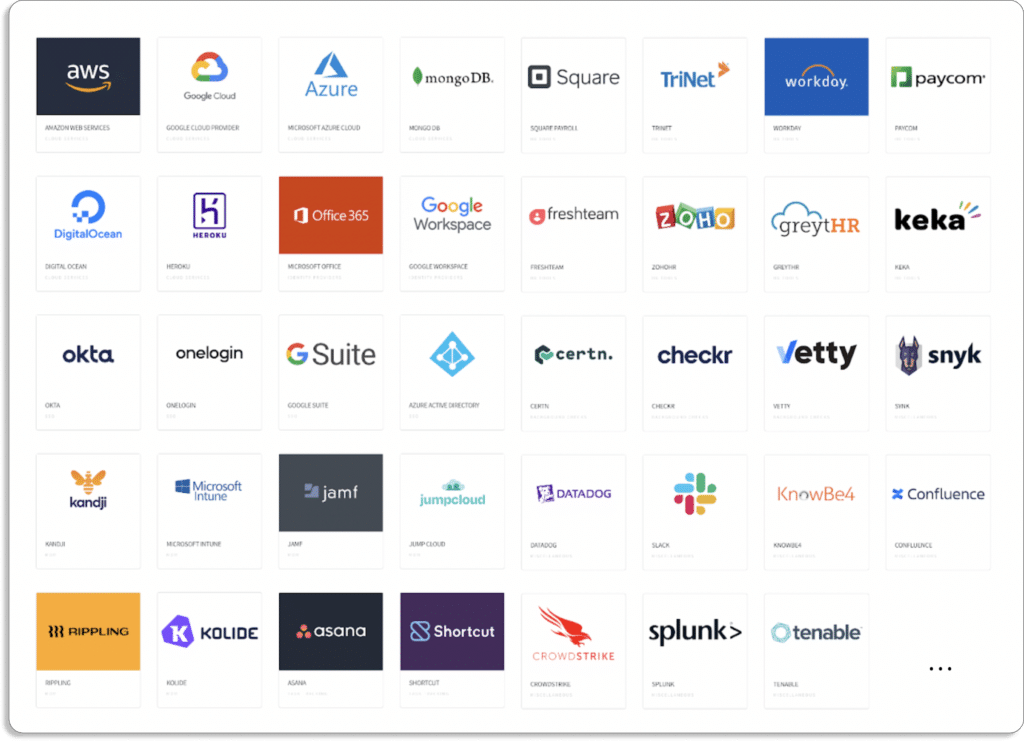
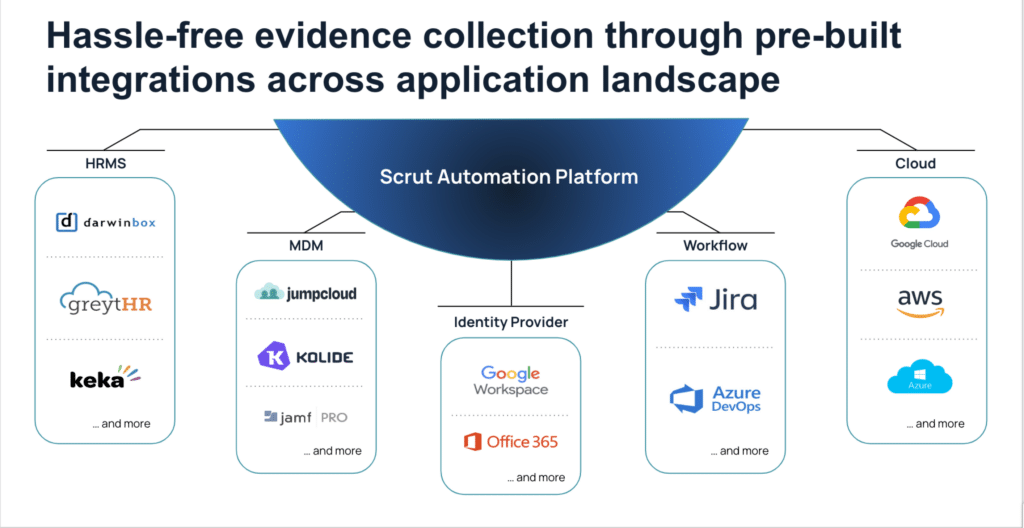
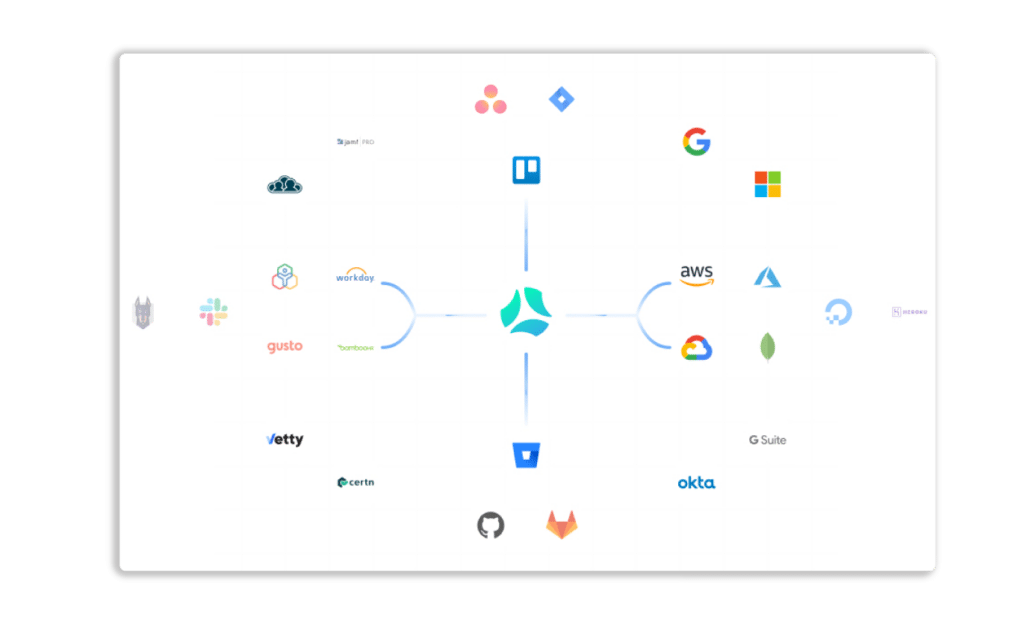
- It should integrate with your existing tech stack
The GDPR compliance software should eliminate most of the manual tasks required to get compliant and reduce the time required in the same with its automation capabilities.
The automation capability depends on the number of tools in your tech stack with which the software integrates. Therefore, you should look for the number of tools with which the software integrates.
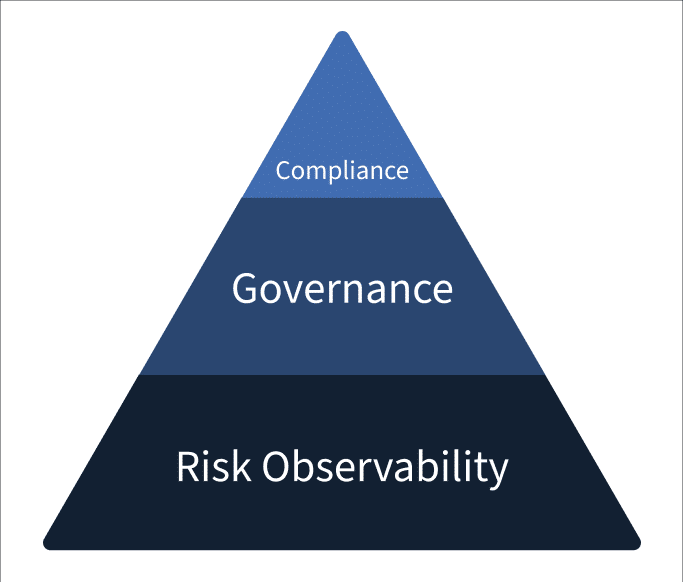
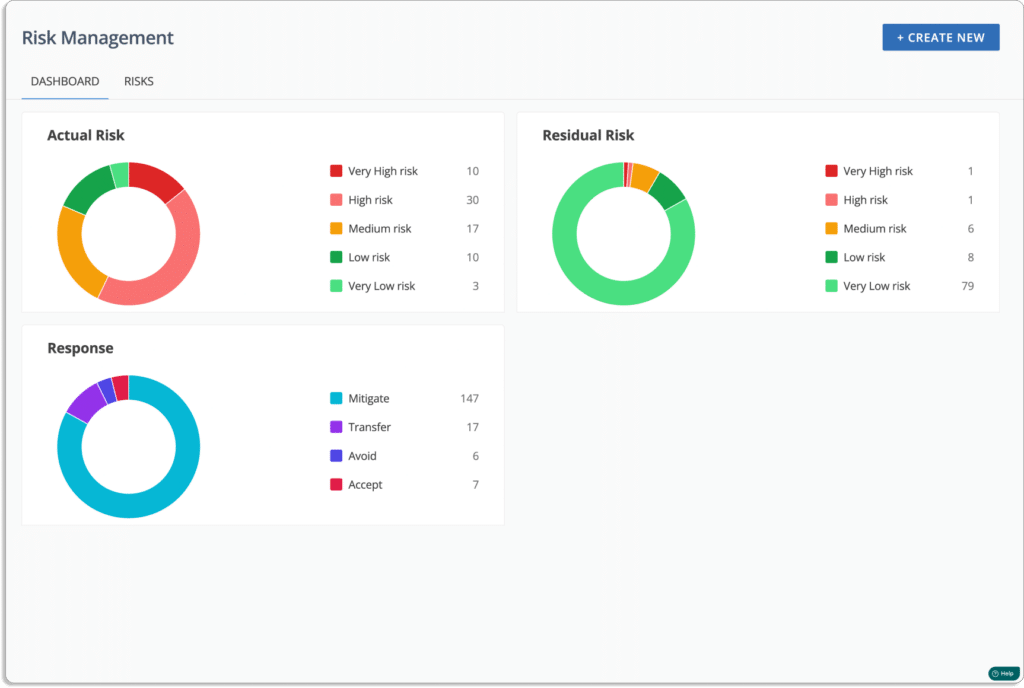
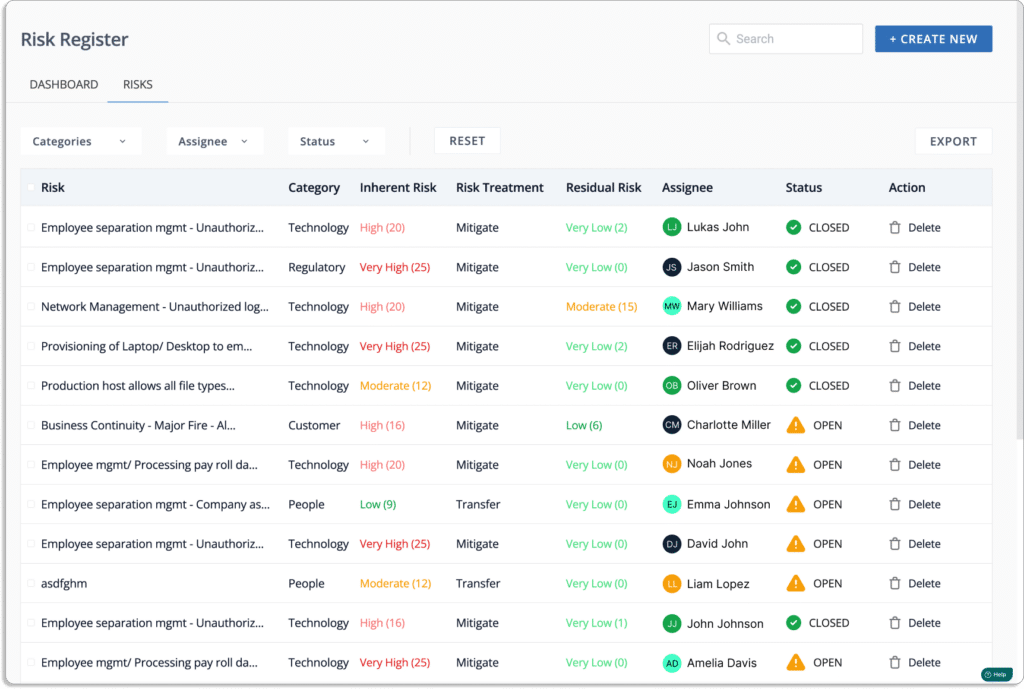
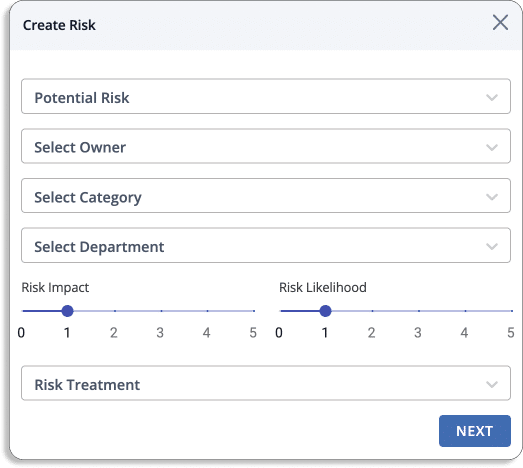
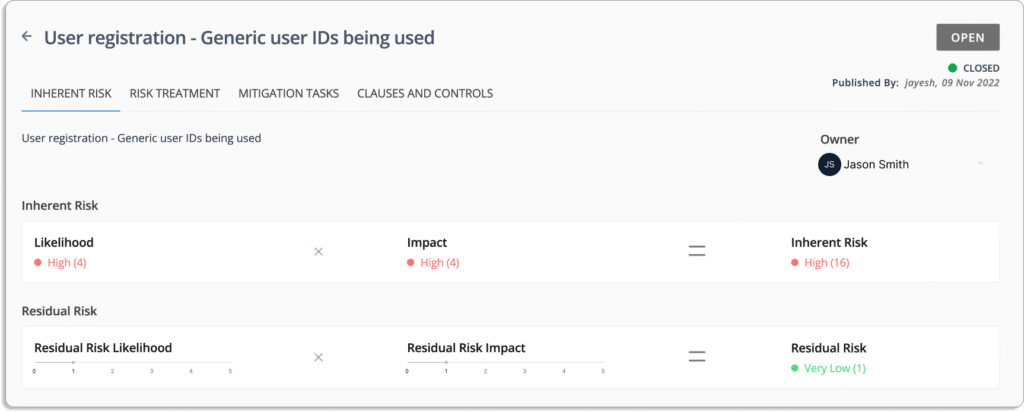
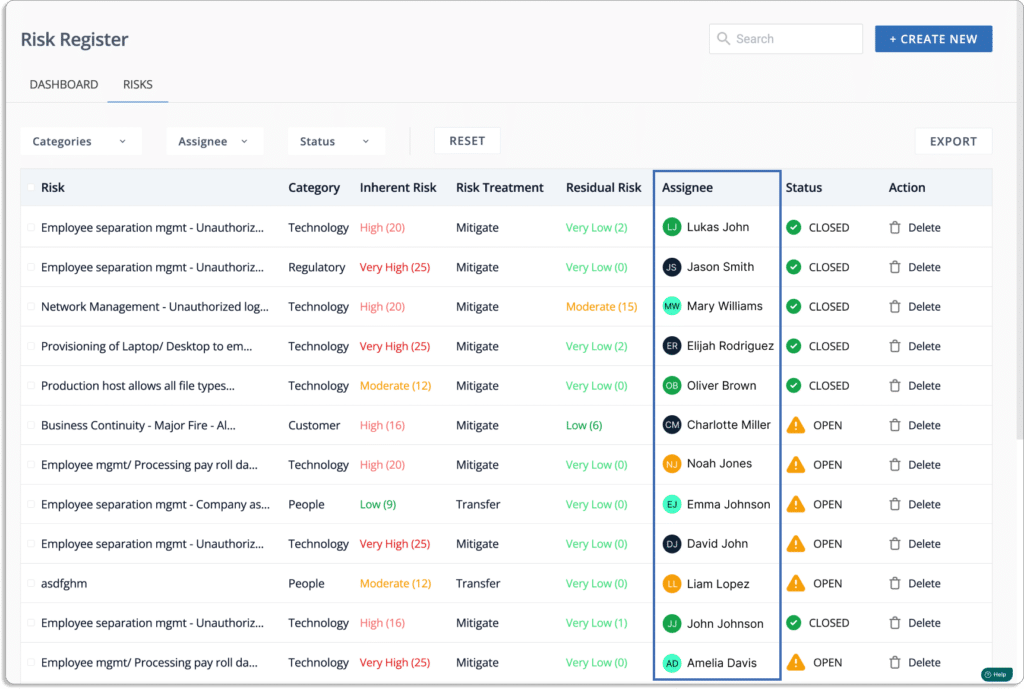
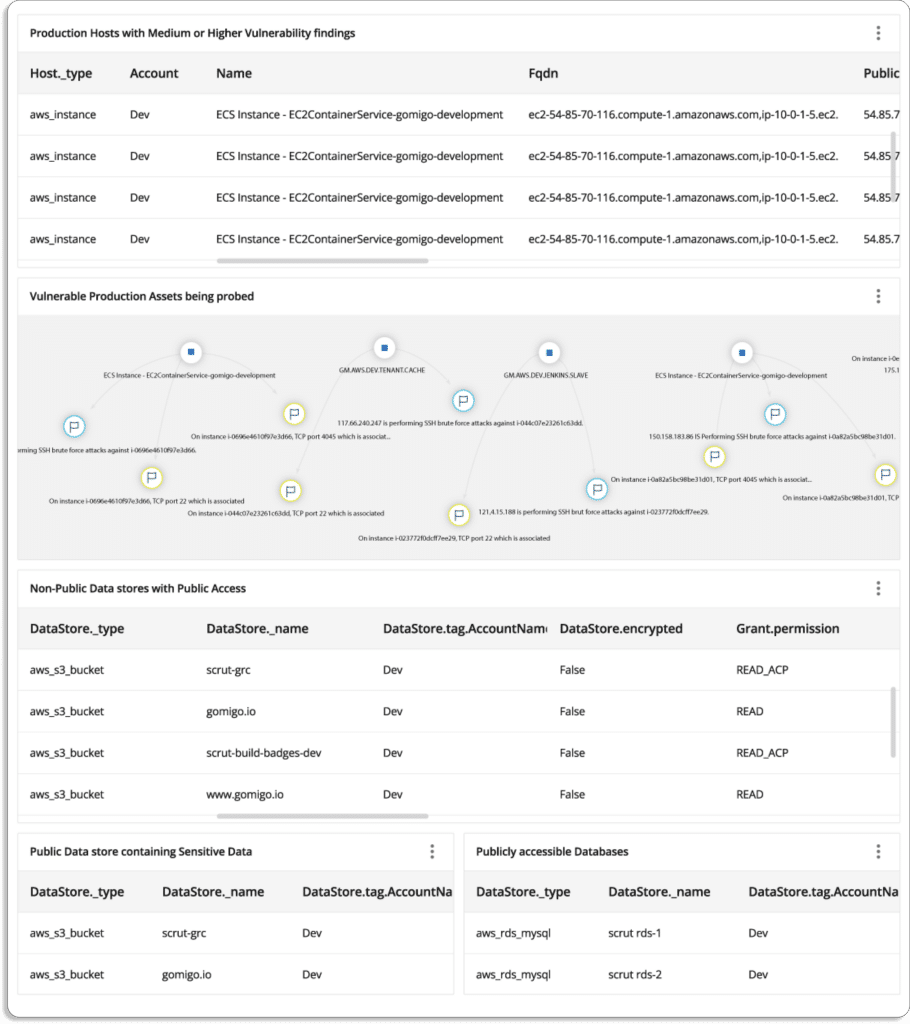
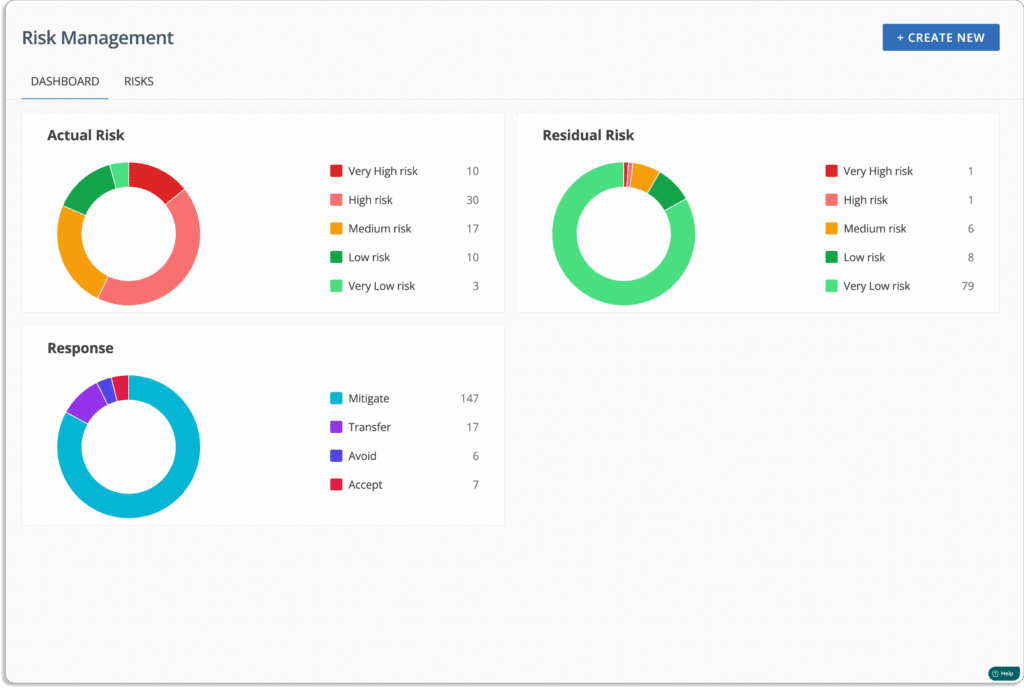
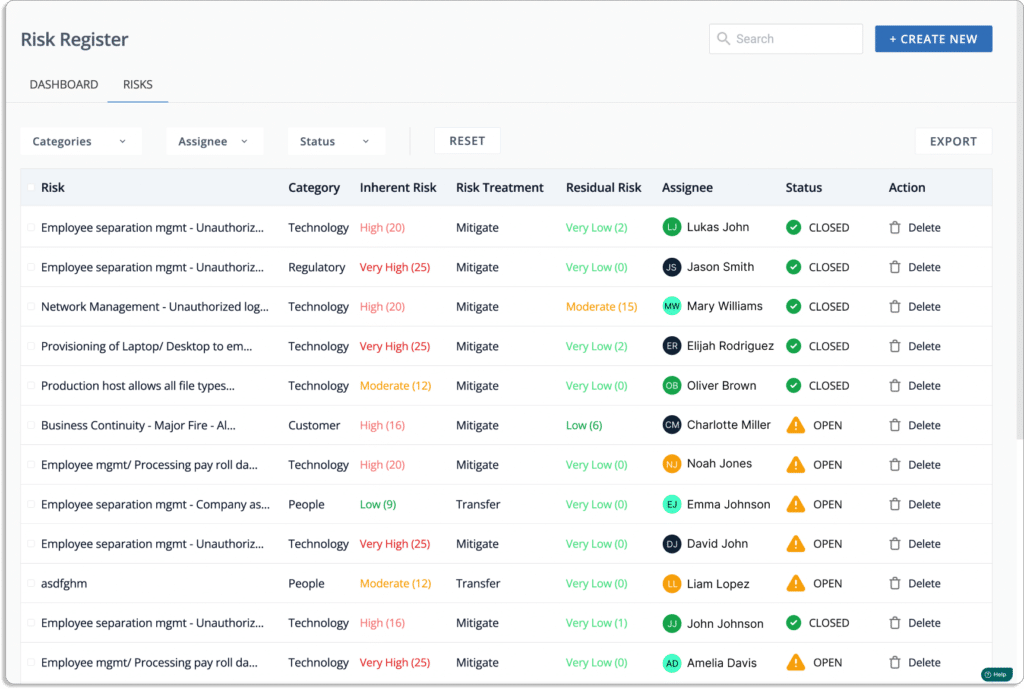
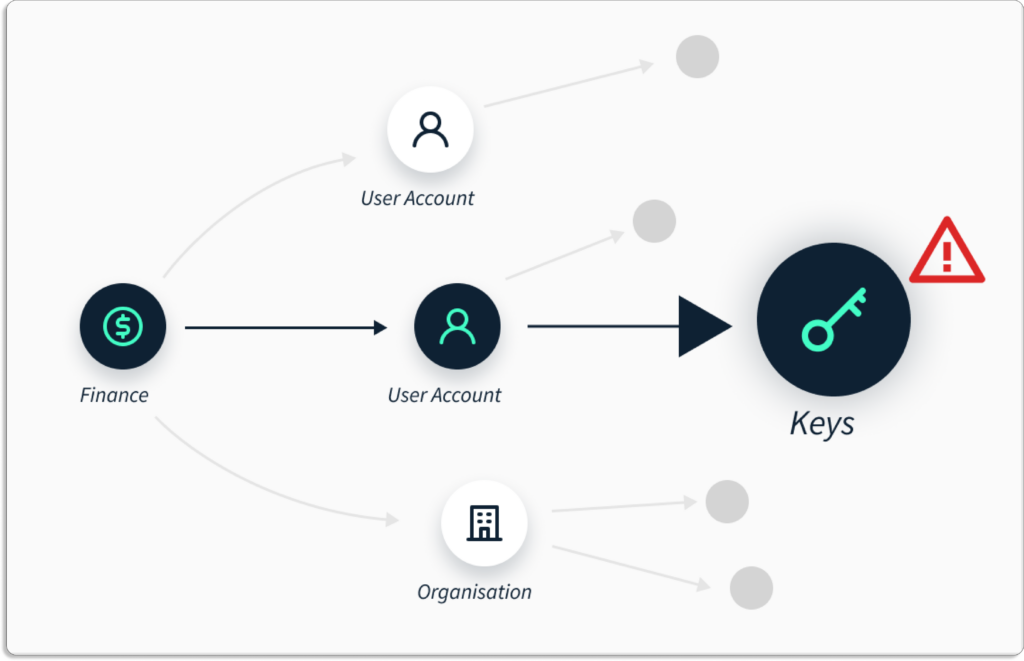
- It should have risk management capabilities
An efficient GDPR tool should have risk management capability. GDPR compliance software vendors can help with risk management by helping you with risk identification, performing risk assessments, risk remediation, and vendor risk management.
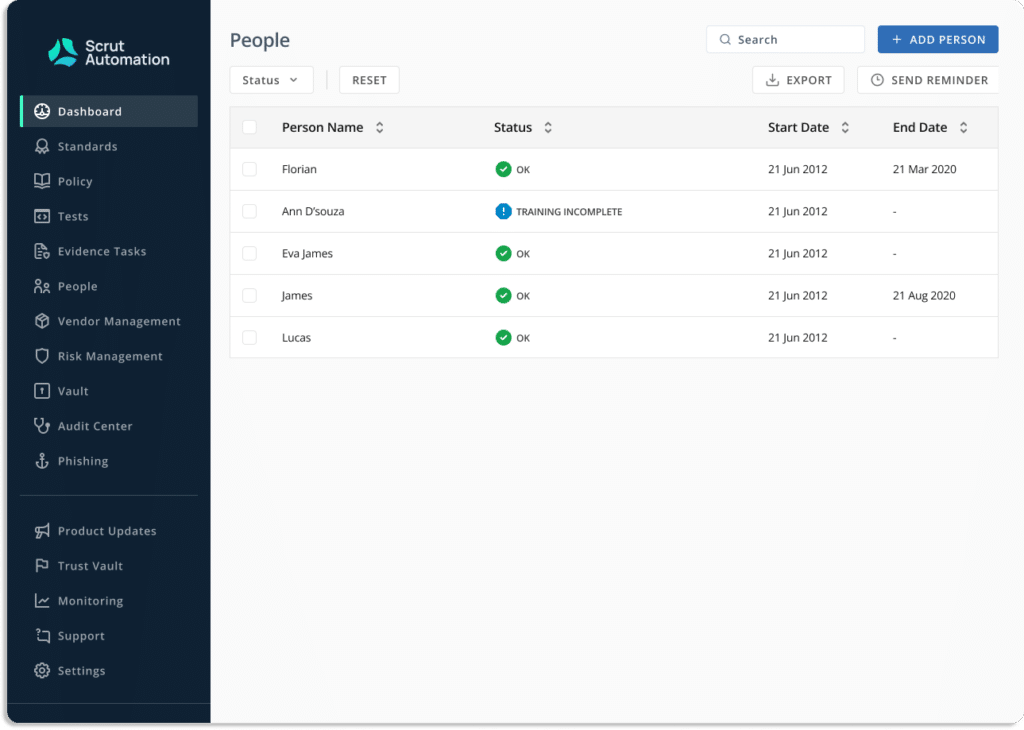
- It should help you in privacy and security awareness training for employees
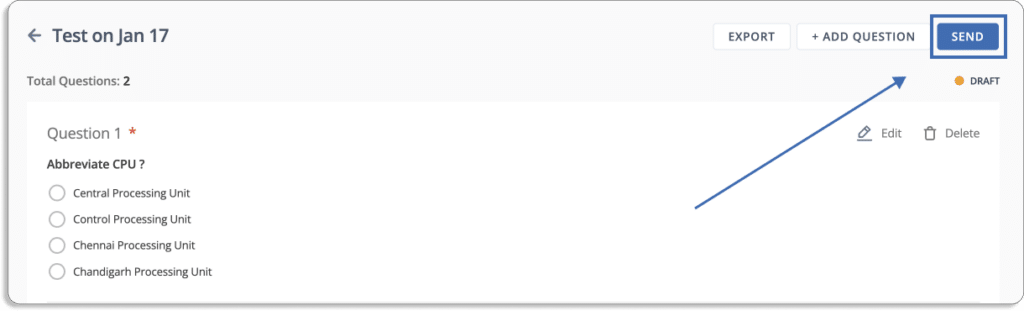
The platform should offer pre-built courses for employee information security training. It should keep track of the training completion status and employee acknowledgment through an easy-to-use dashboard.
The tool should be able to quickly grade and monitor your employees’ awareness performance through quizzes and tests.
Top 15 GDPR Compliance Automation Tools
If you go to the market looking for GDPR automation tools, it is easy to become overwhelmed by the hundreds of GDPR compliance automation solutions.
But, the question remains the same: Which GDPR compliance tool would fit your business needs?
We made it easier for you to choose by compiling a list of GDPR compliance tools based on their features, benefits, and drawbacks.
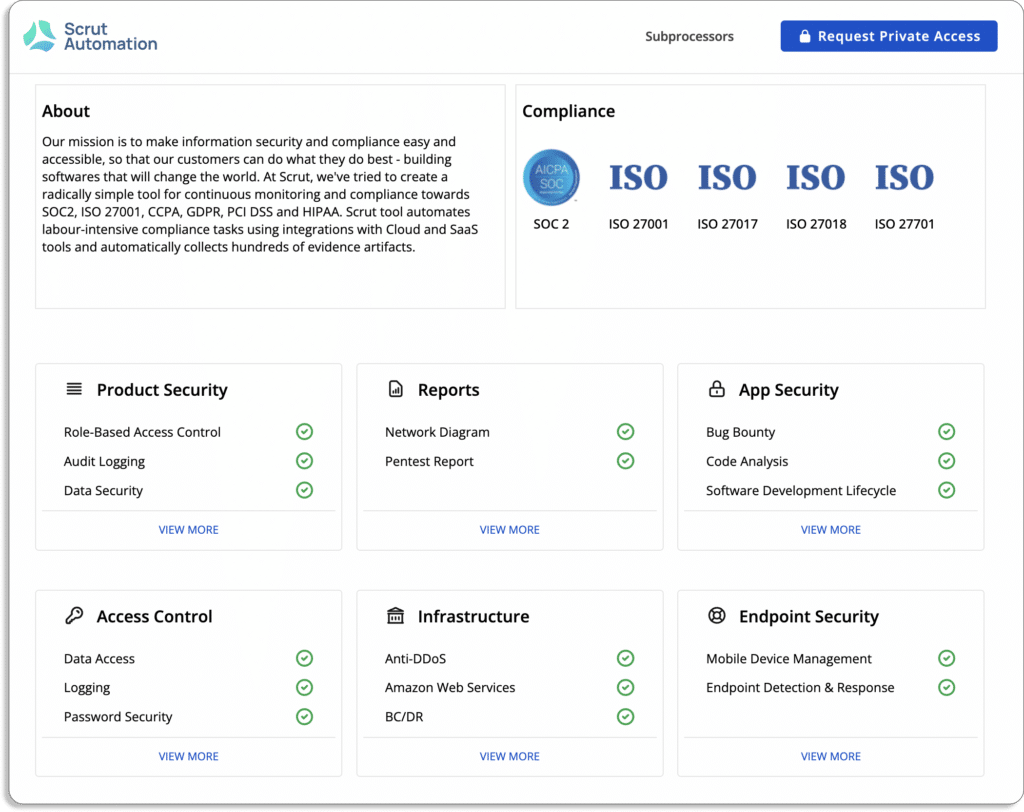
1. Scrut Automation
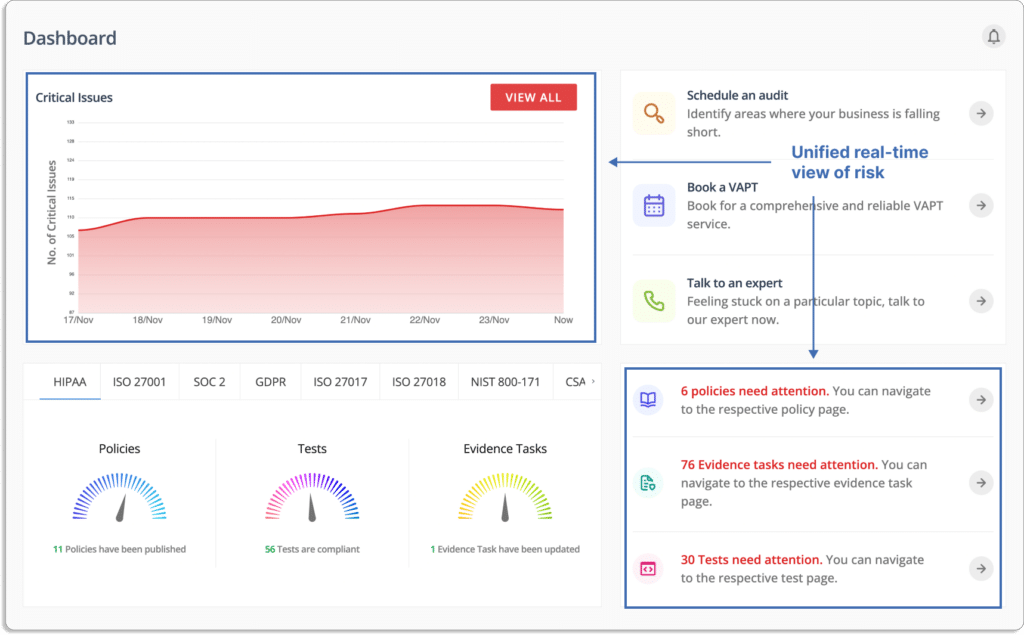
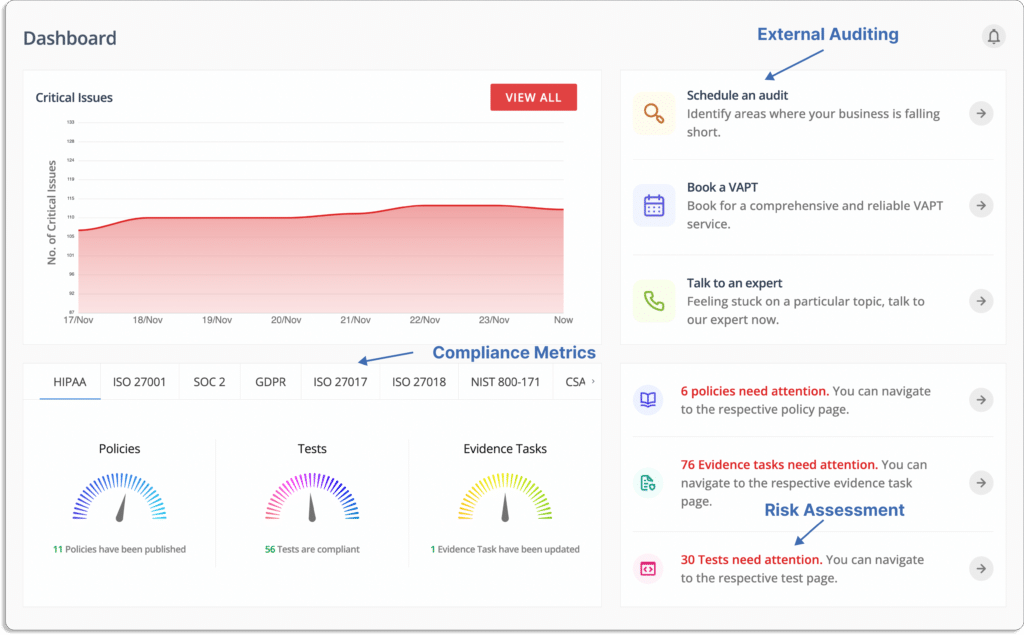
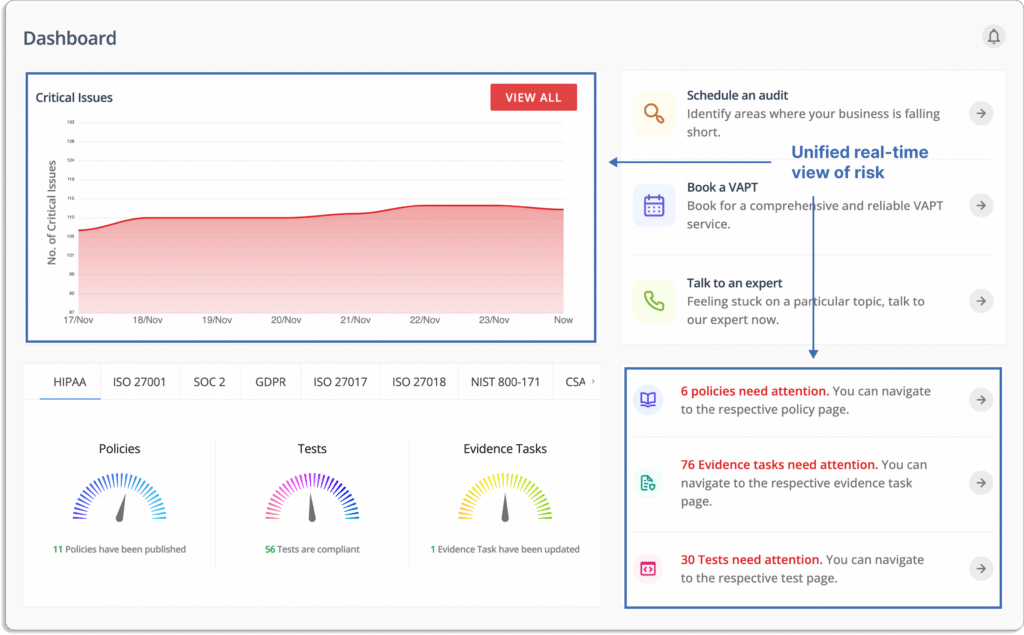
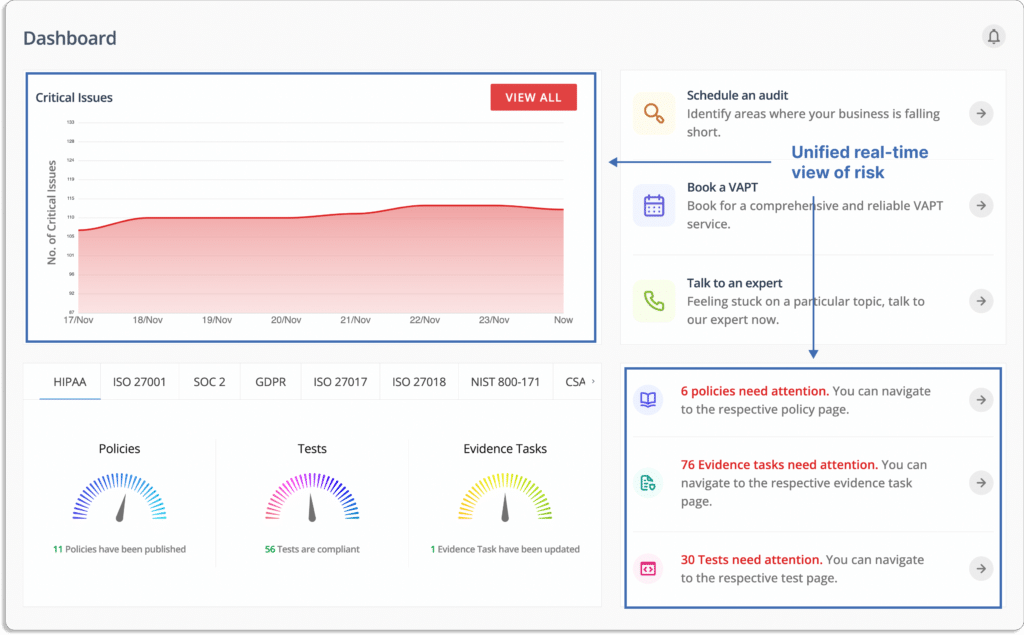
Scrut Automation improves your GDPR compliance posture with pre-built controls and ongoing compliance monitoring. Let’s see how.
- Simplifies end-to-end GDPR compliance
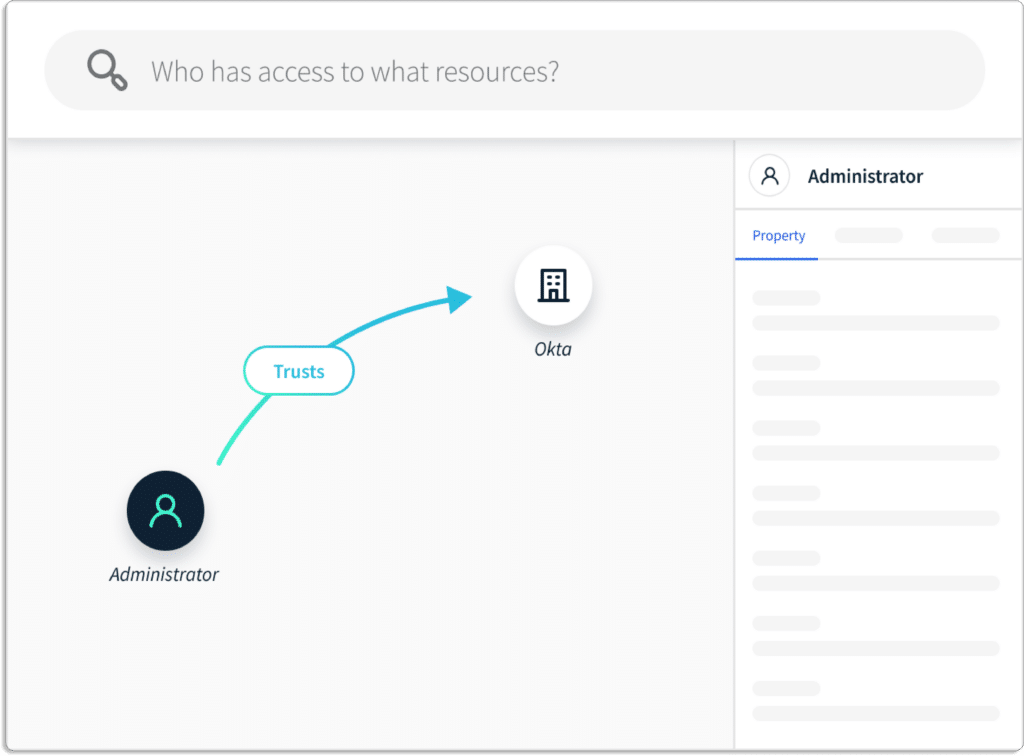
Scrut simplifies the GDPR compliance process by managing everything from cloud risk assessments to vendor risks, control reviews, and employee policy attestations. The platform identifies compliance gaps so you can concentrate on what needs to be fixed.
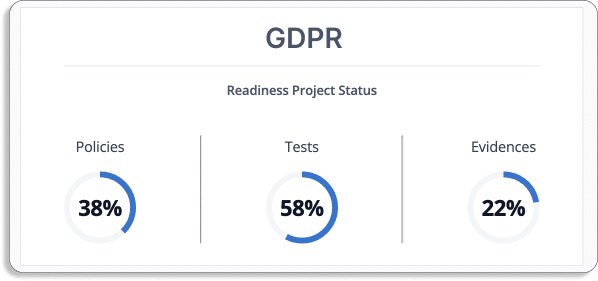
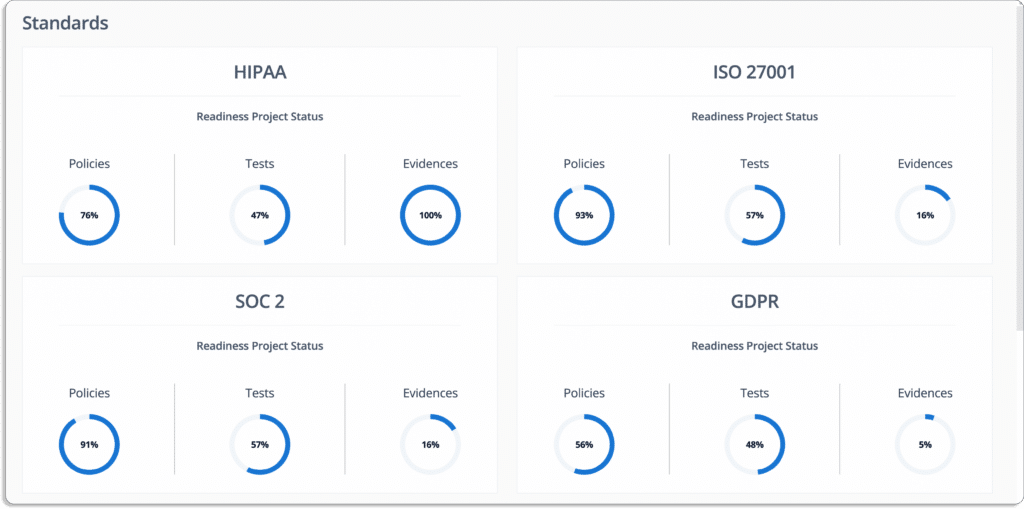
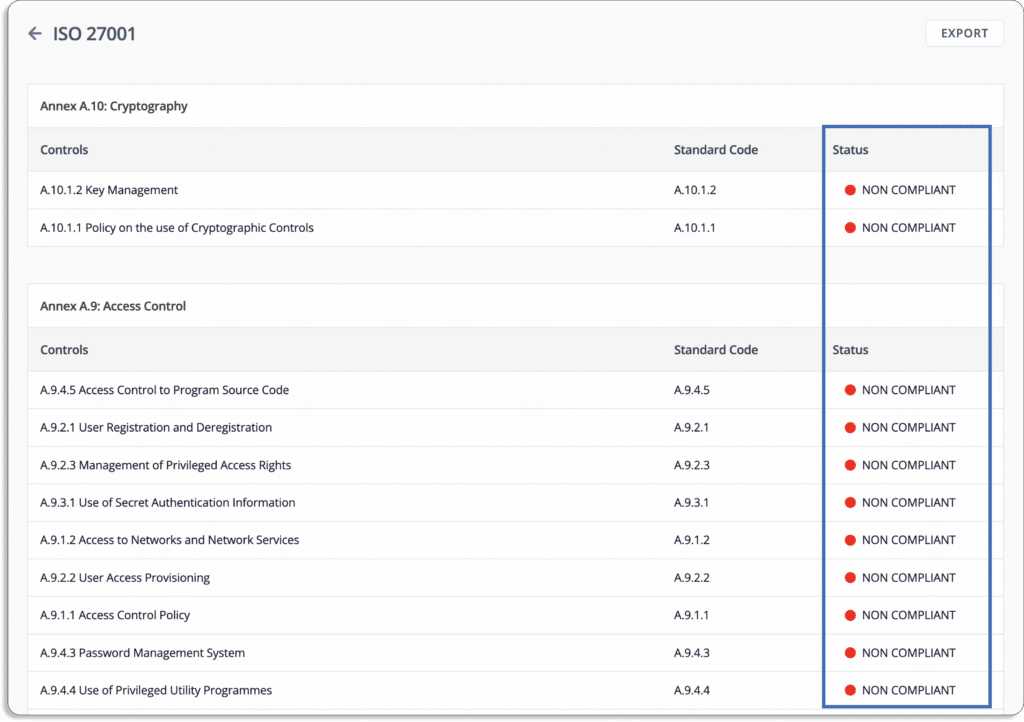
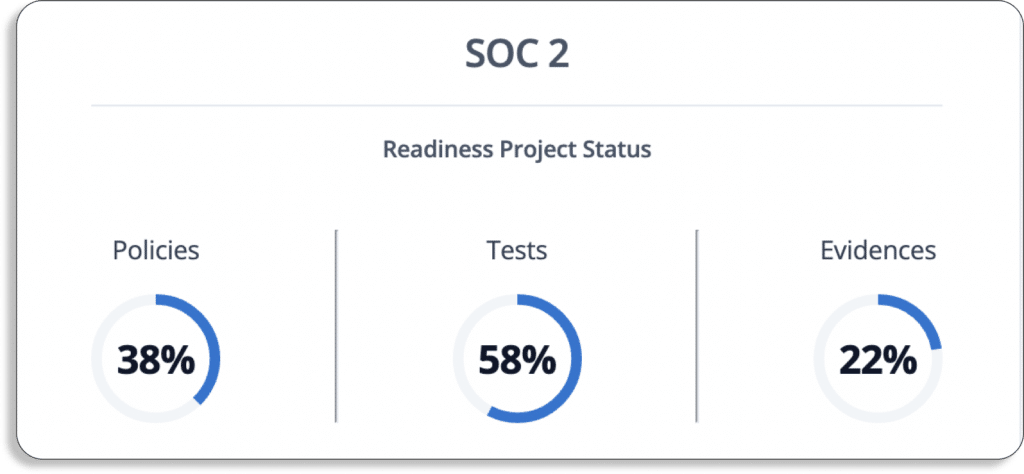
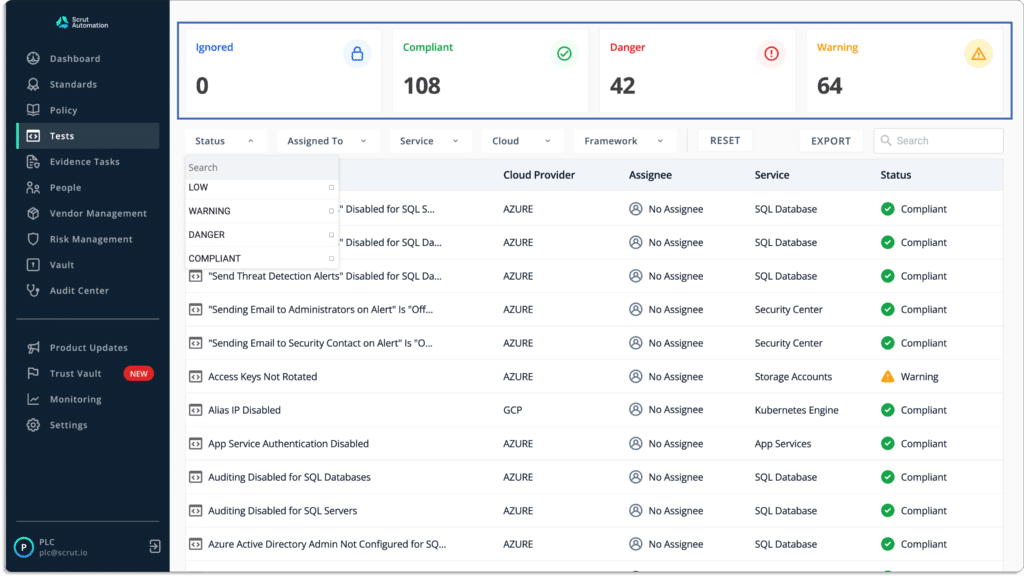
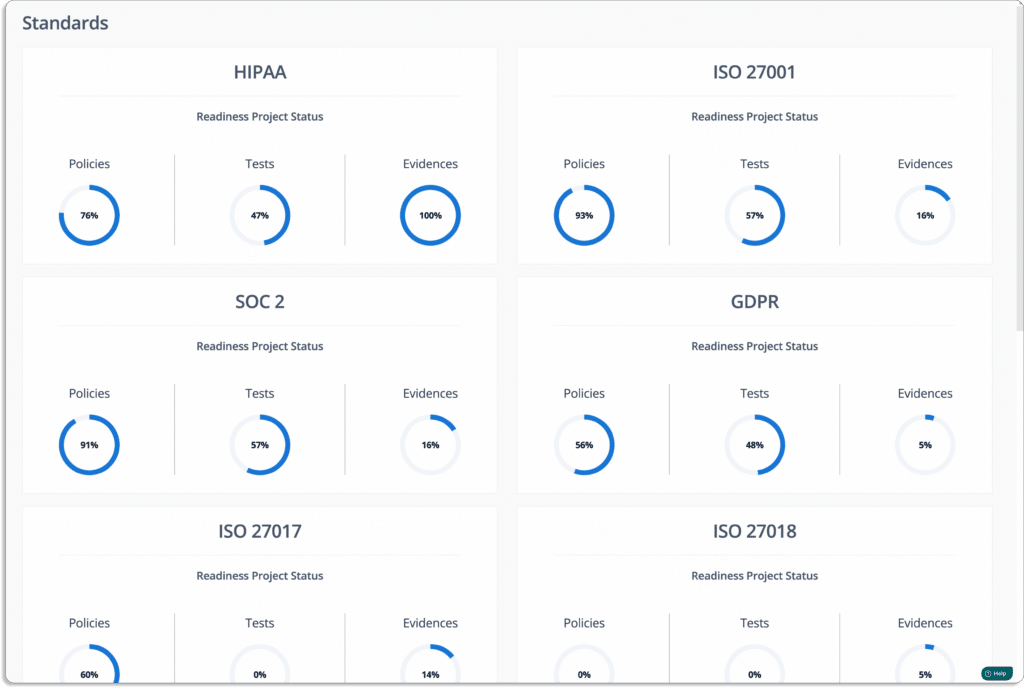
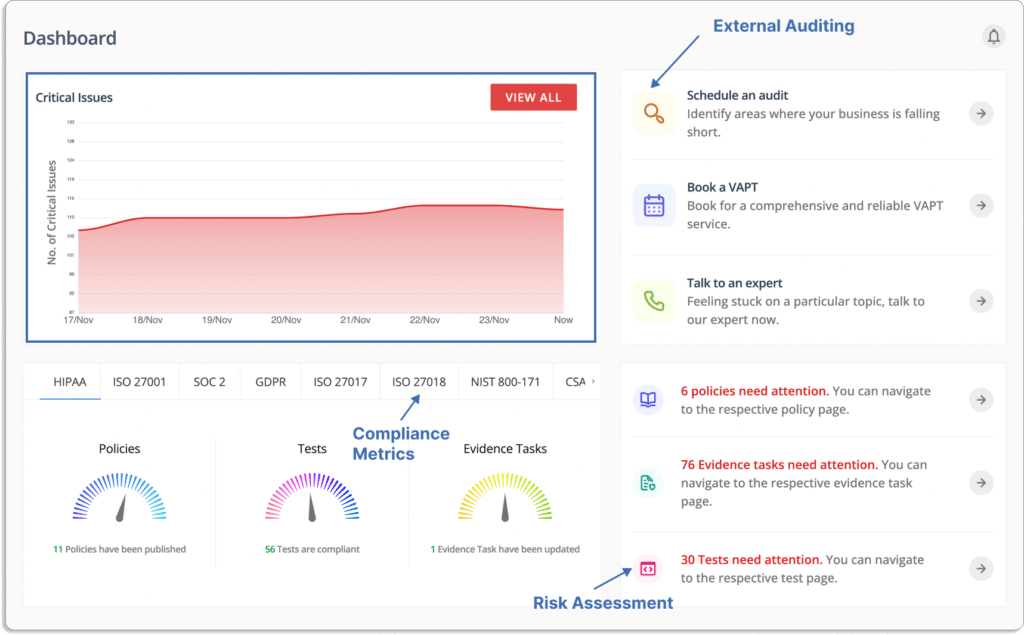
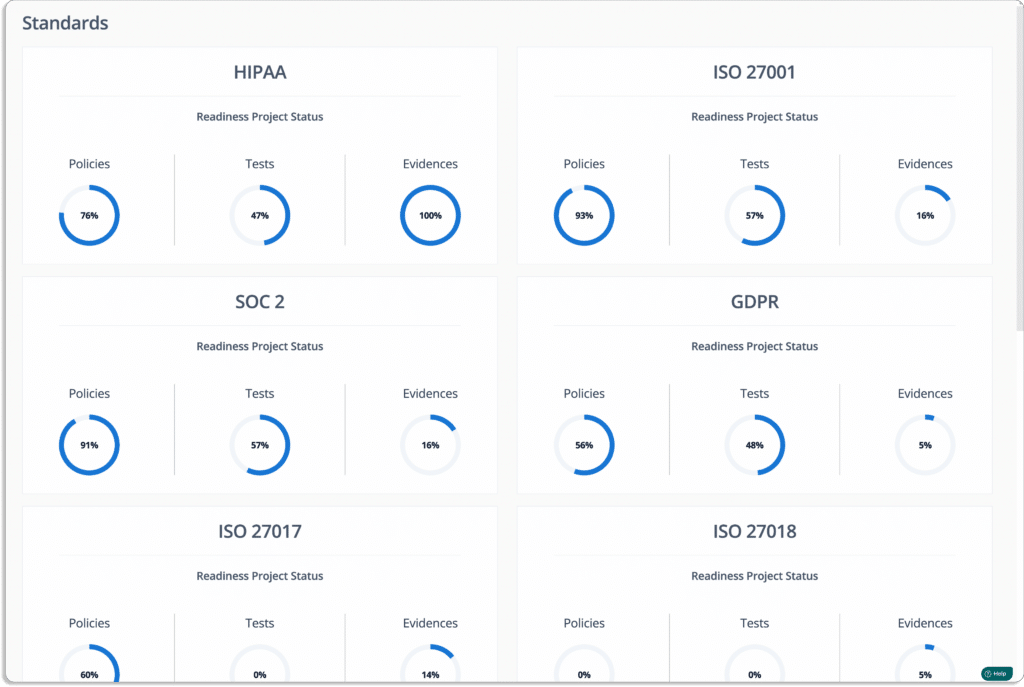
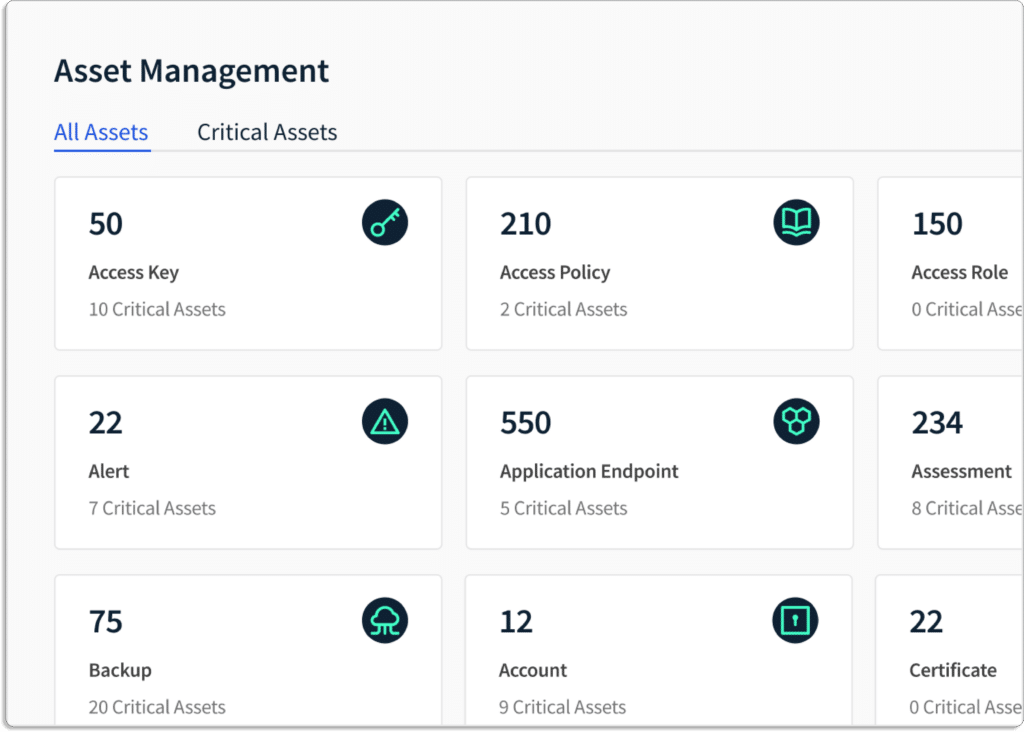
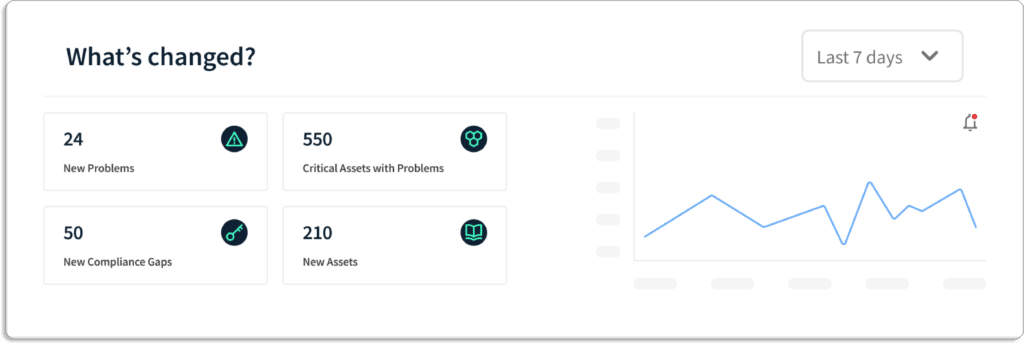
As shown in the screenshot above, this organization has:
- 58% of cloud security tests are compliant with GDPR requirements
- 38% of policies in place required for being GDPR compliant
- 22% of the required evidence has been uploaded
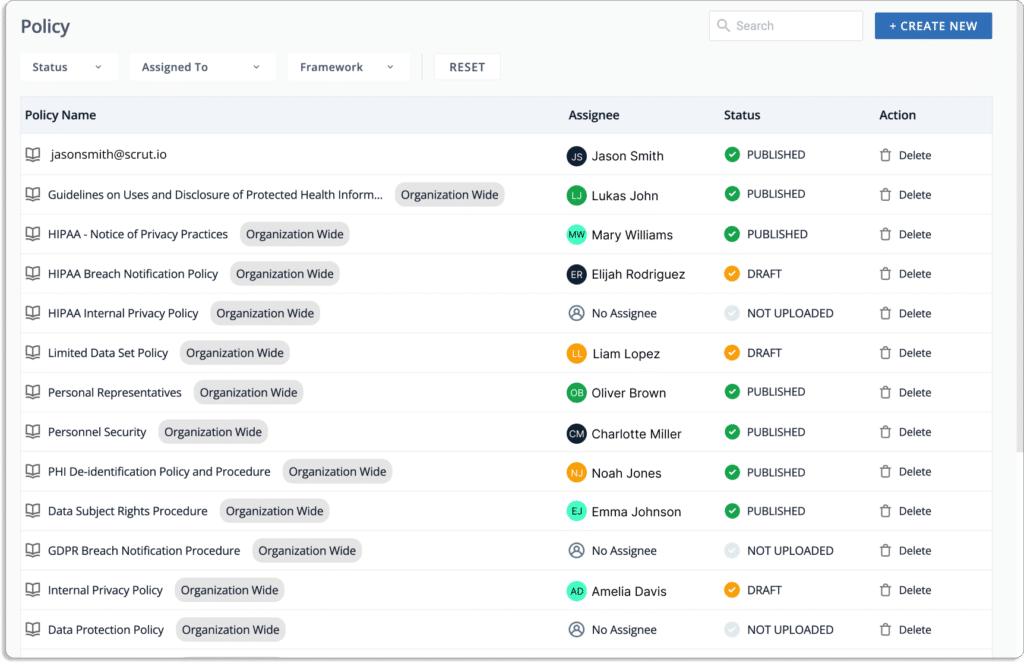
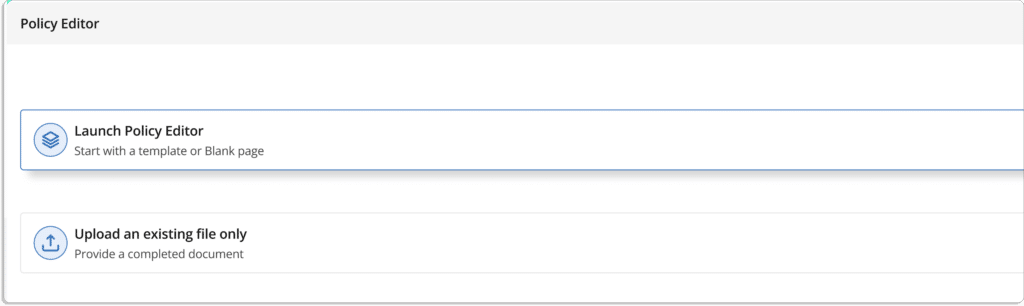
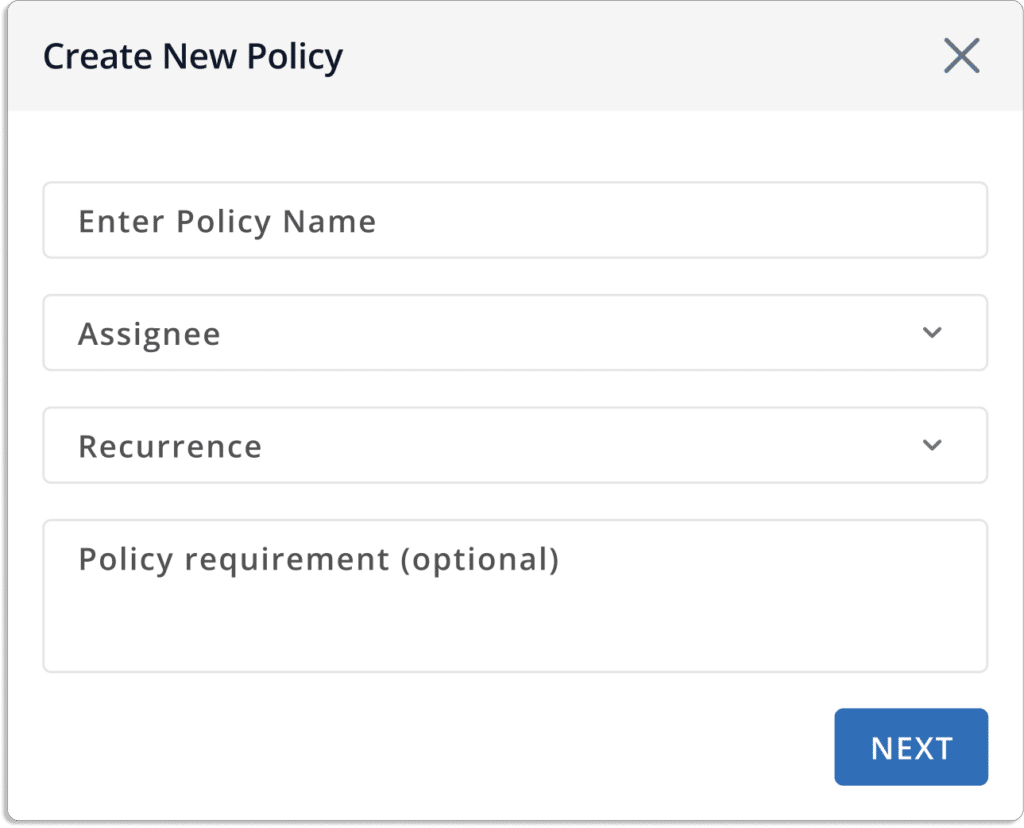
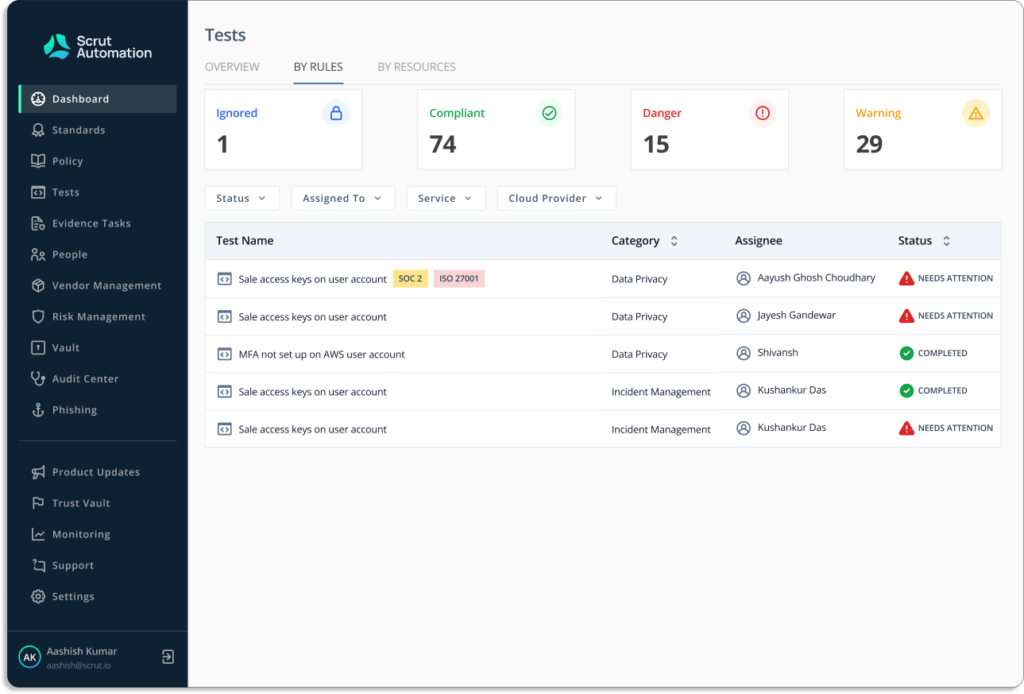
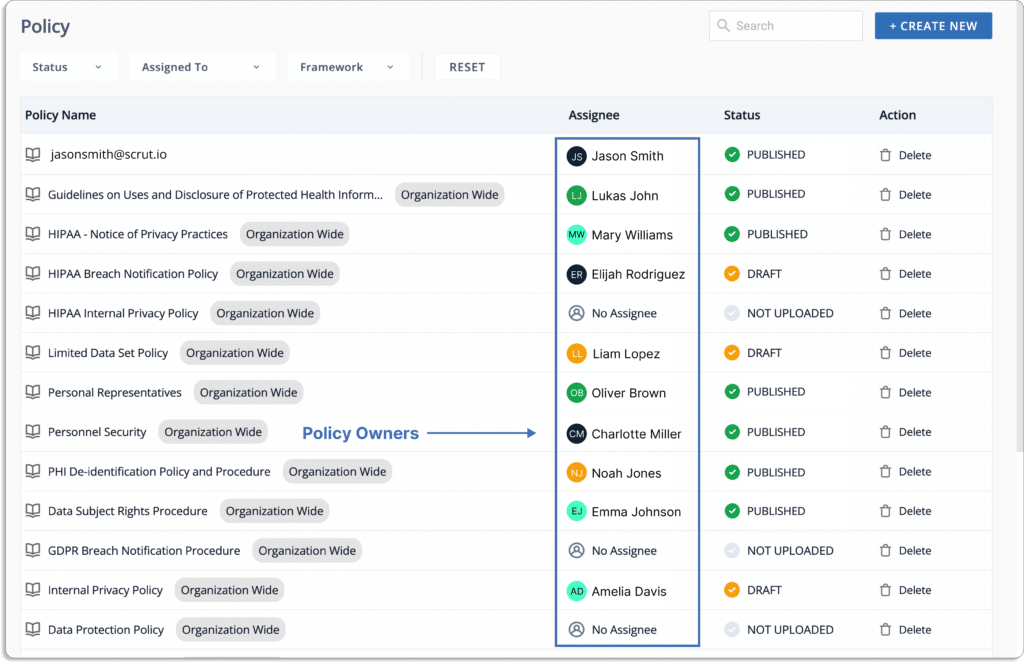
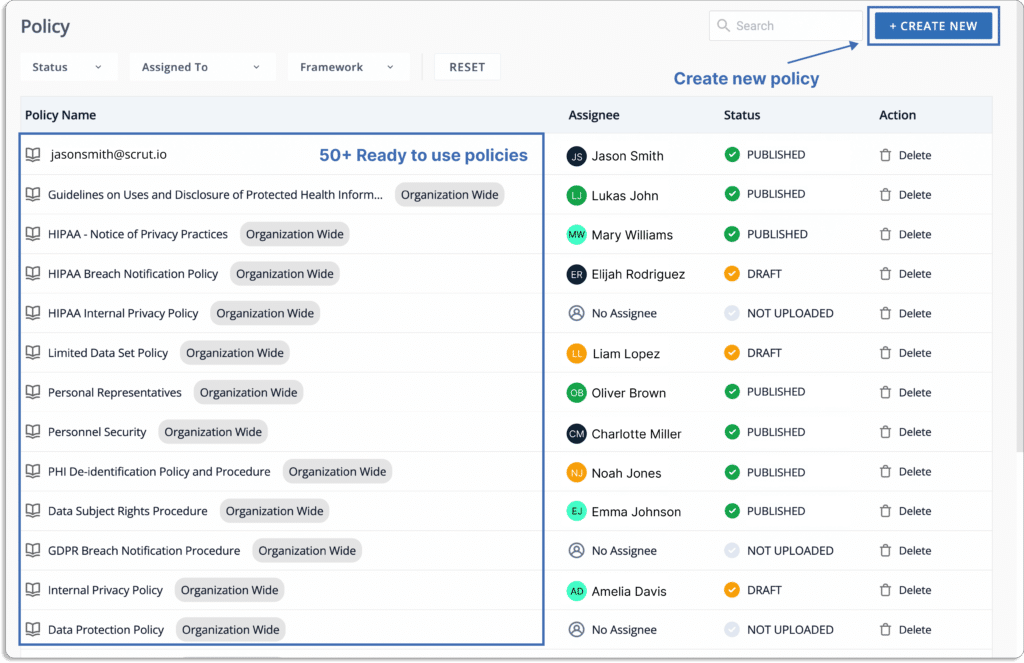
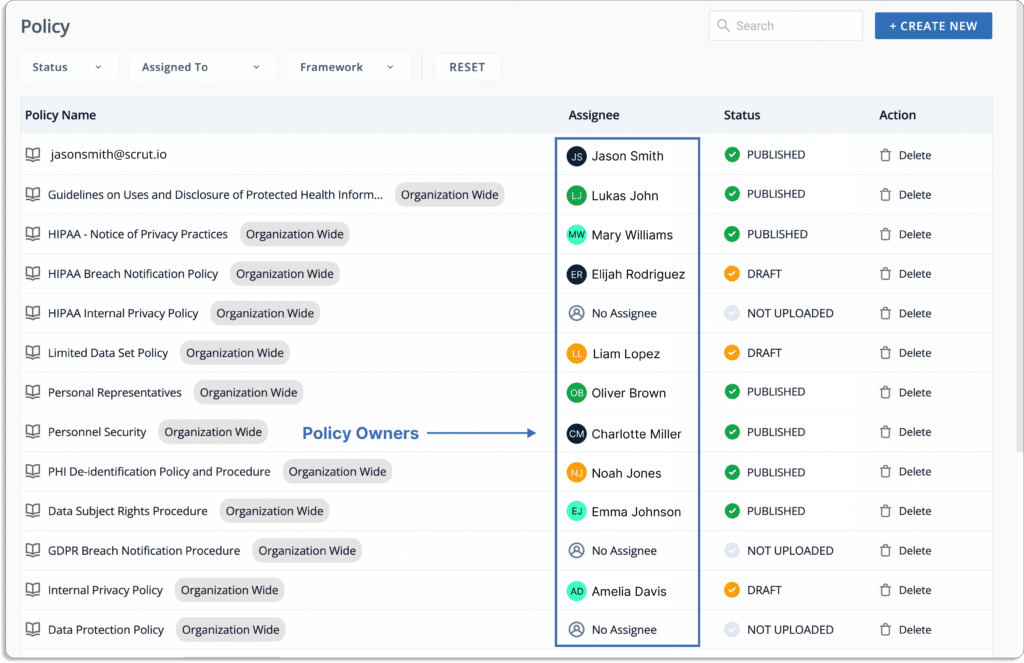
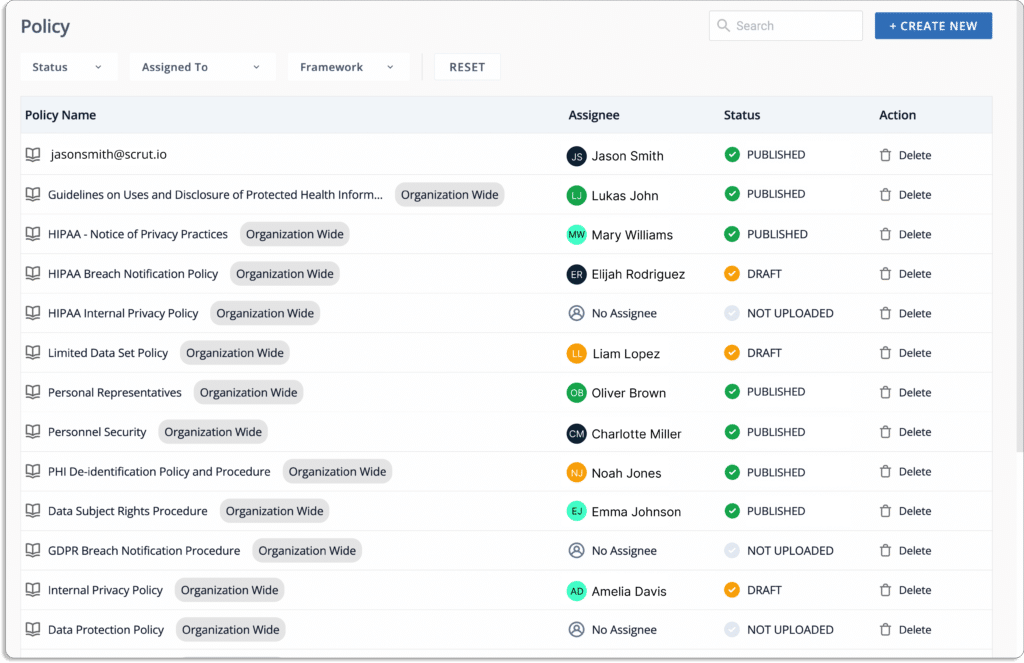
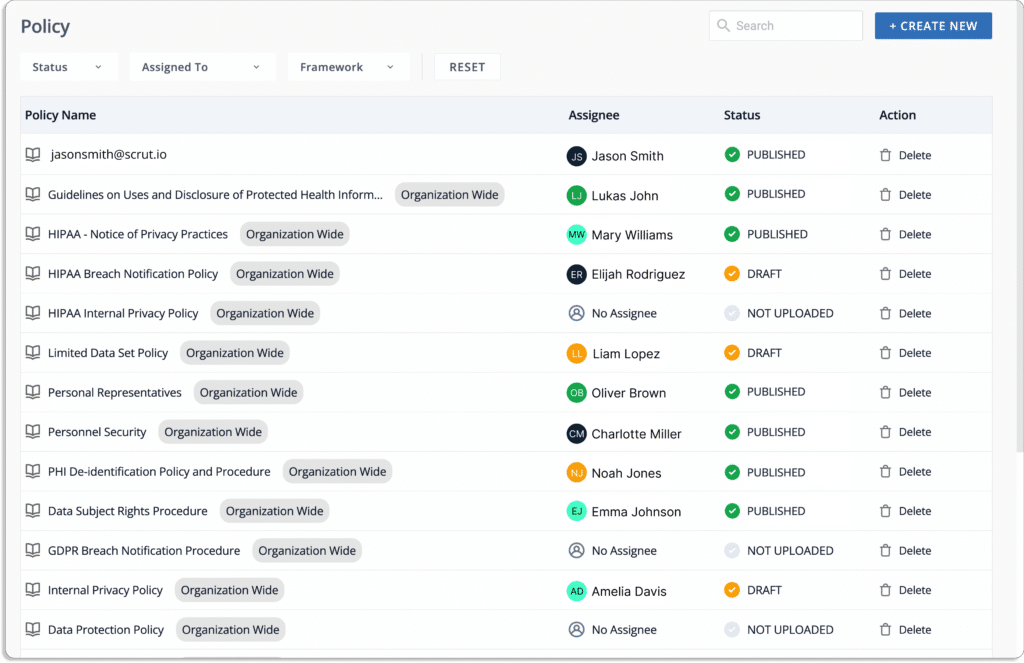
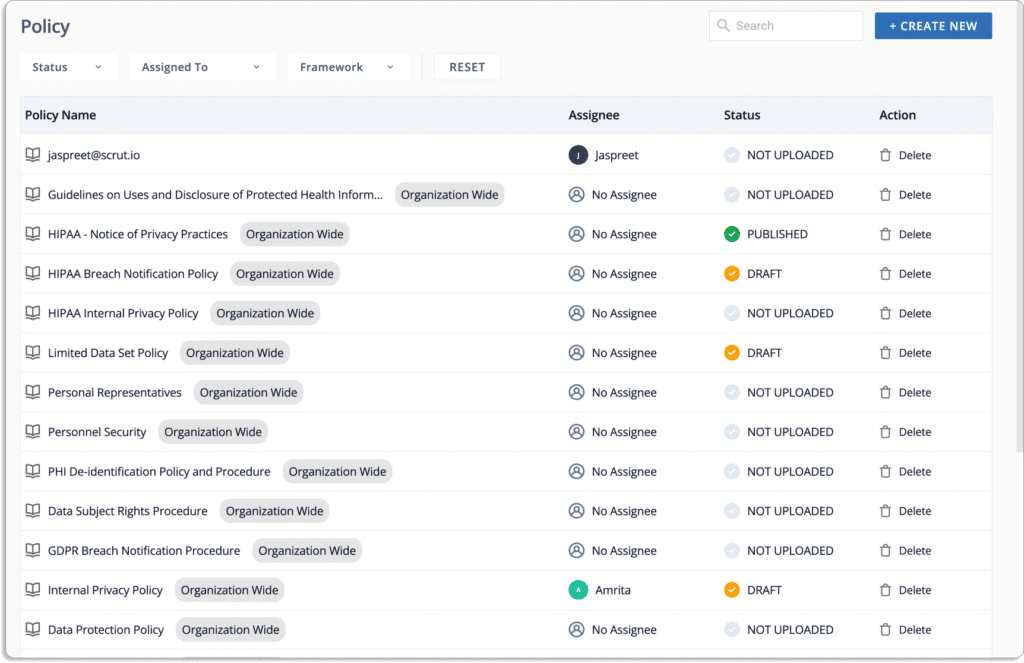
- Implement GDPR policies with Scrut
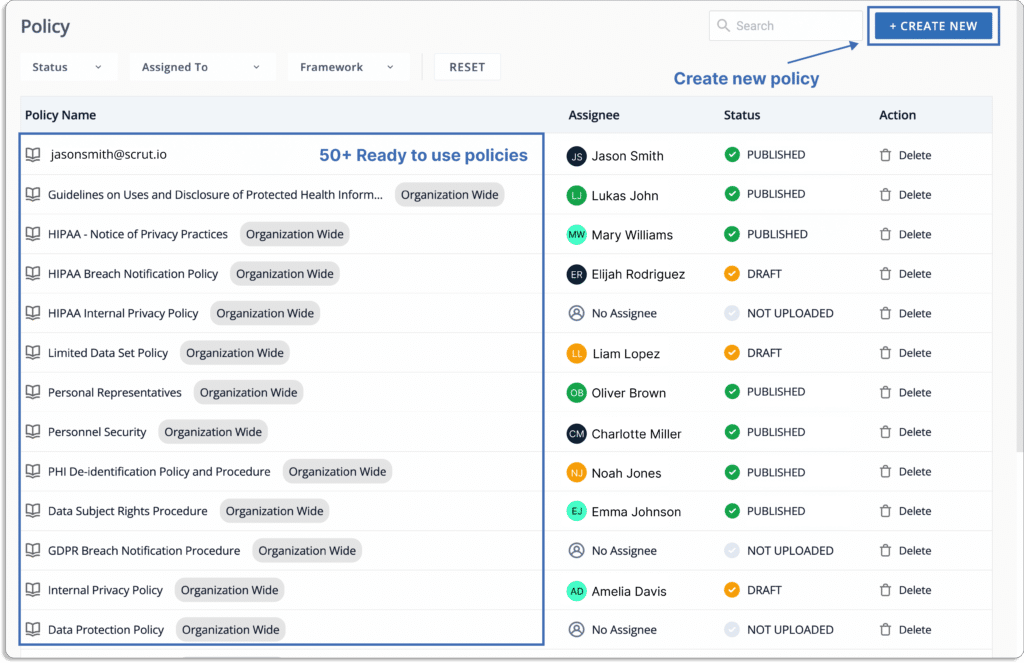
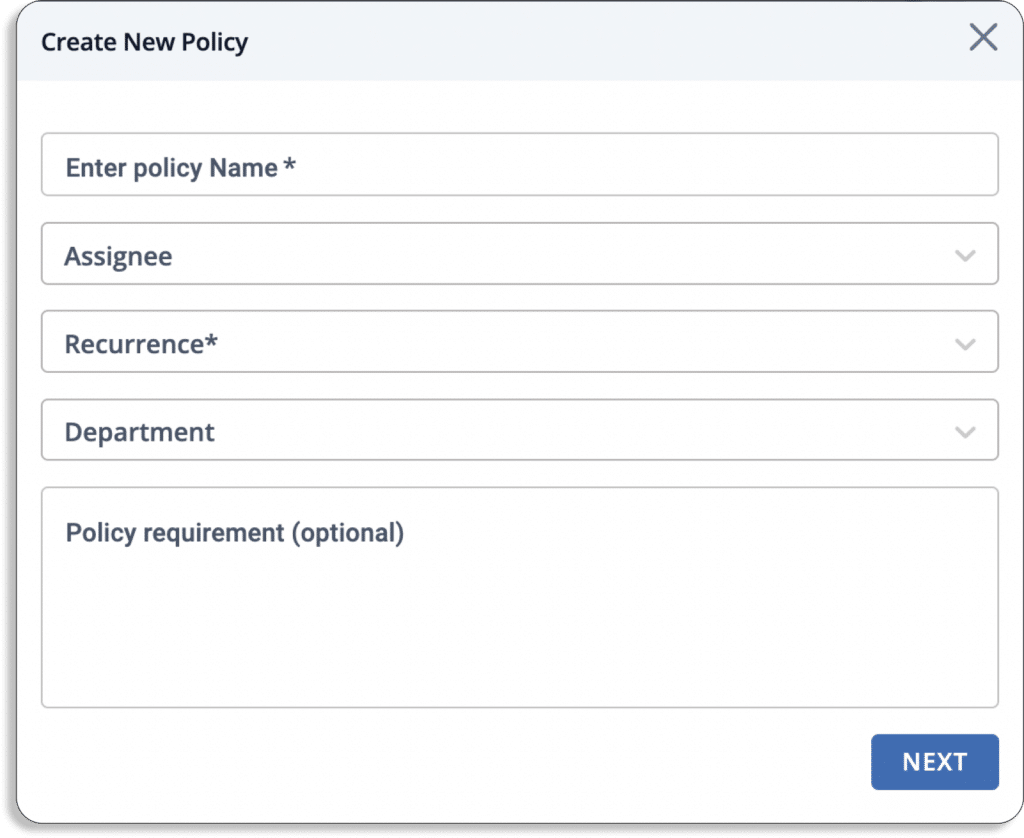
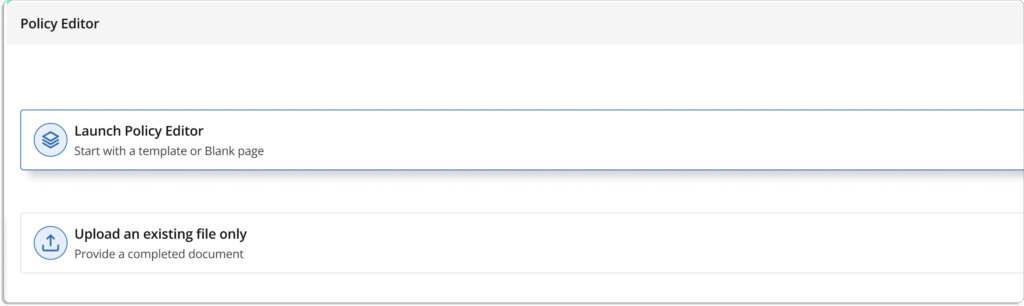
Scrut comes with ready to use policies for GDPR compliance to help you quickly get started. This saves a lot of your time.
You can use our policy library with 50+ pre-built policies or upload your own to set up your InfoSec program.
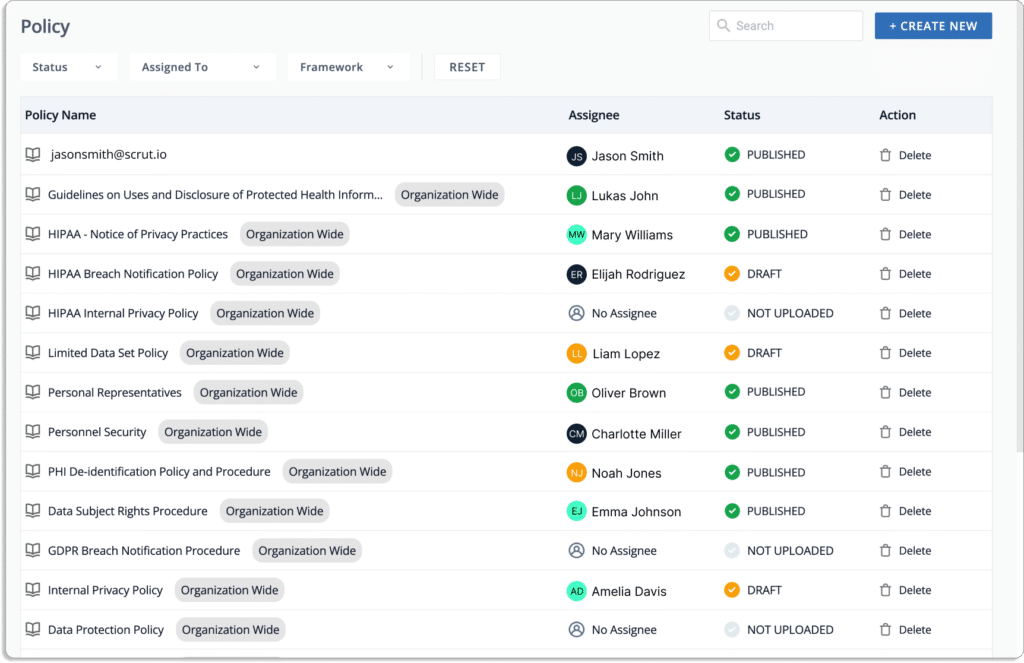
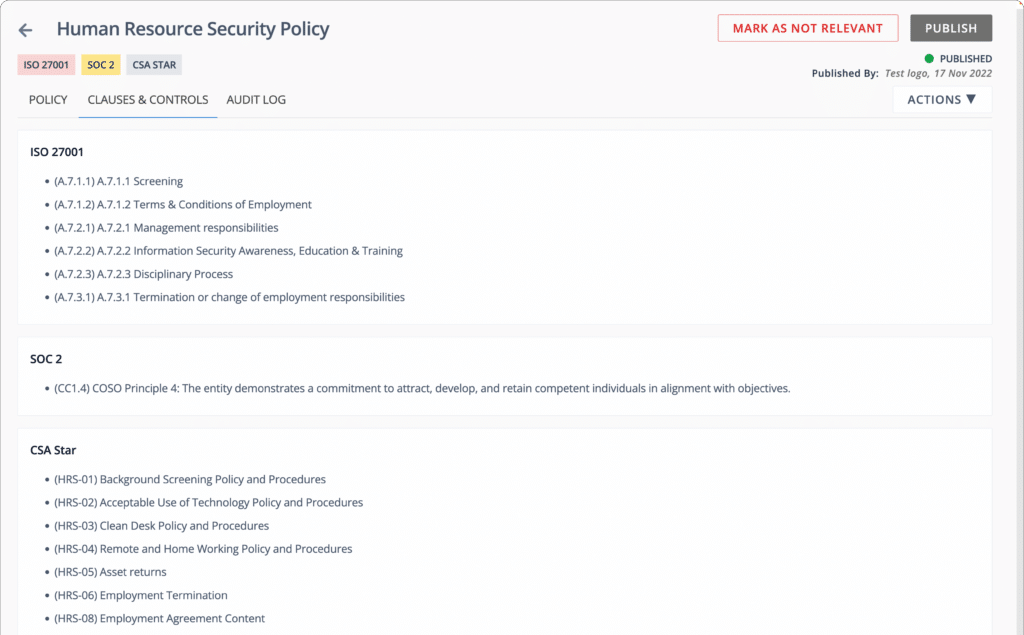
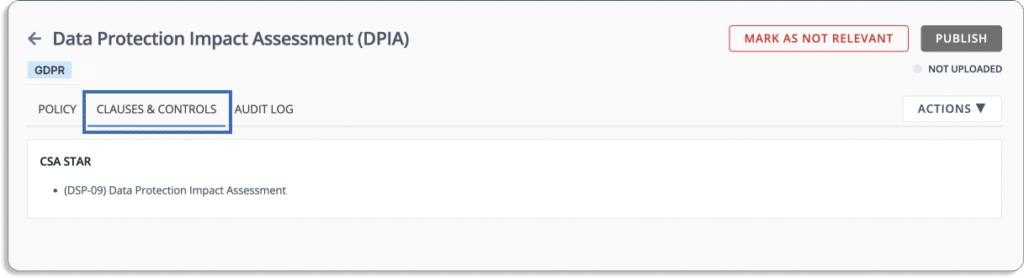
Click on each policy in the GDPR compliance requirements to see how it is mapped to specific controls, as shown in the screenshot below.
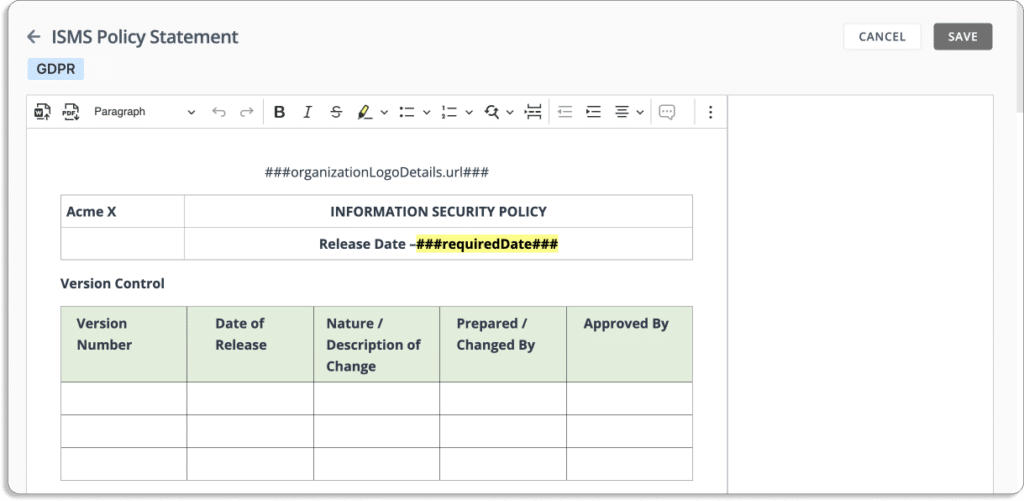
The in-built editor can also customize your policies, as per your requirements.
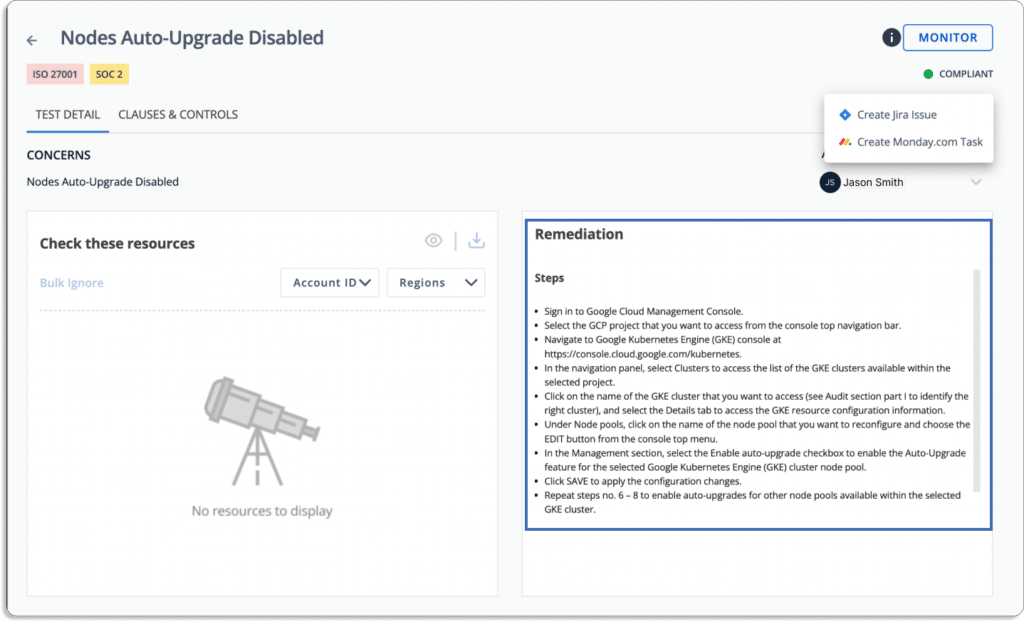
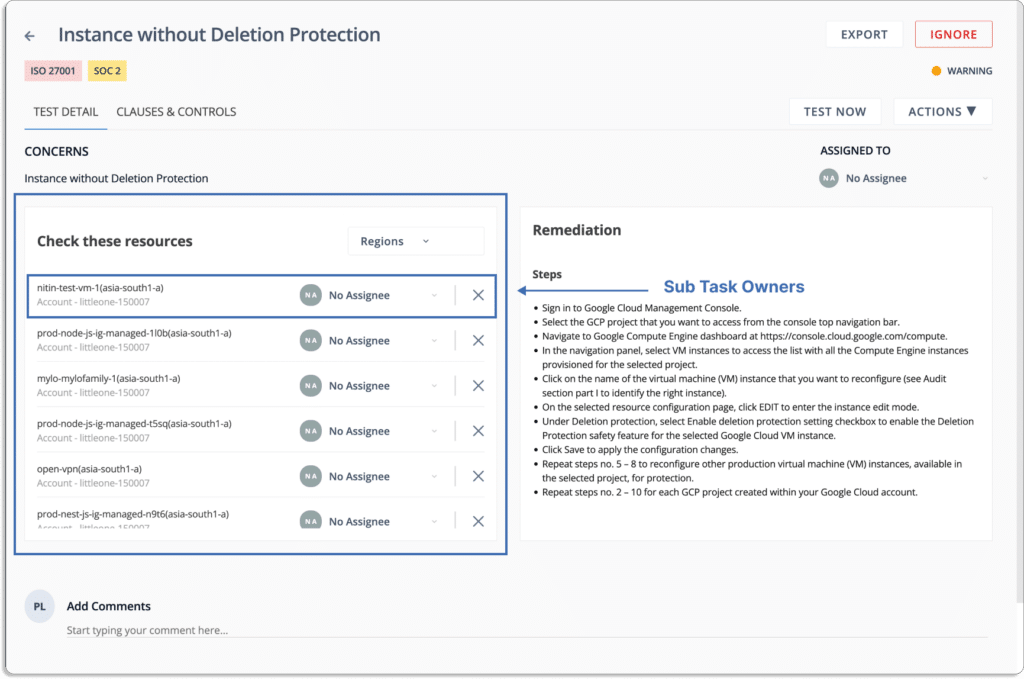
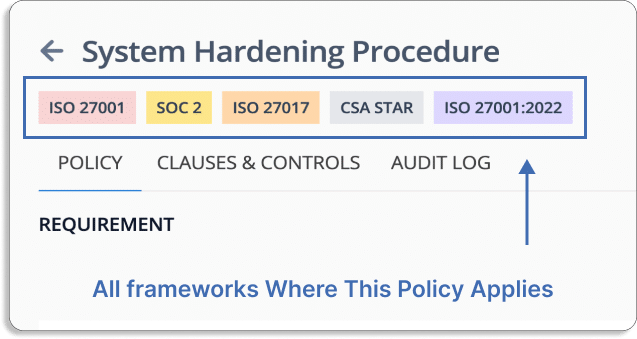
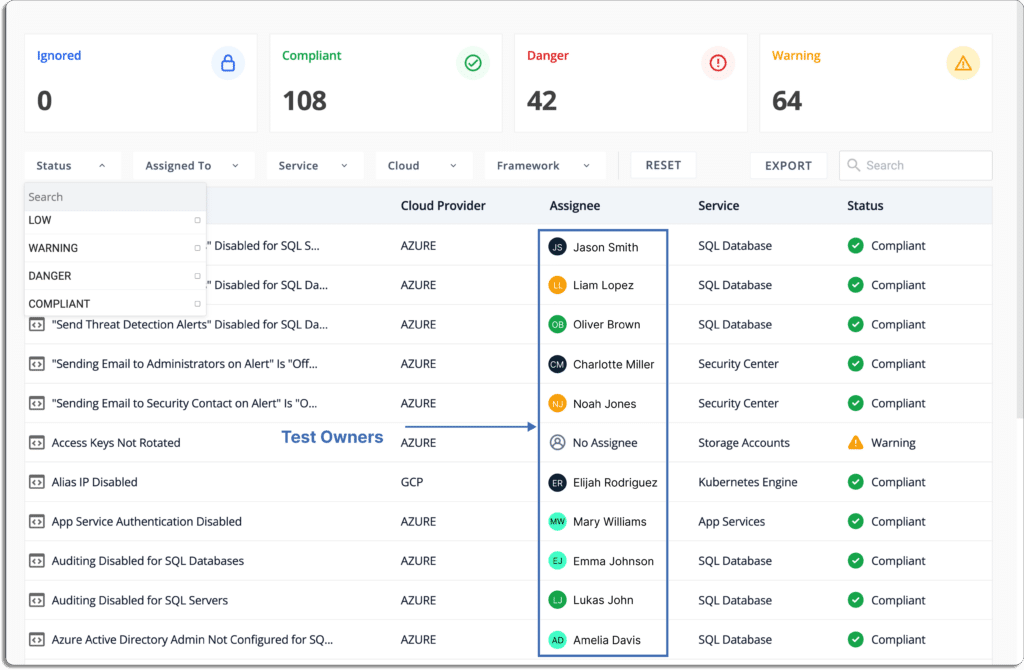
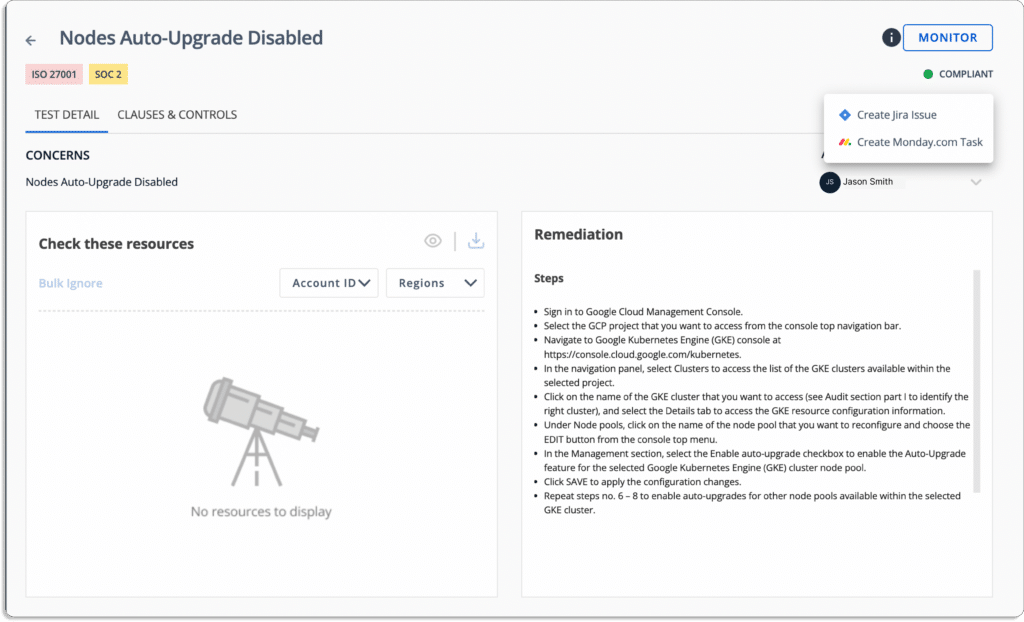
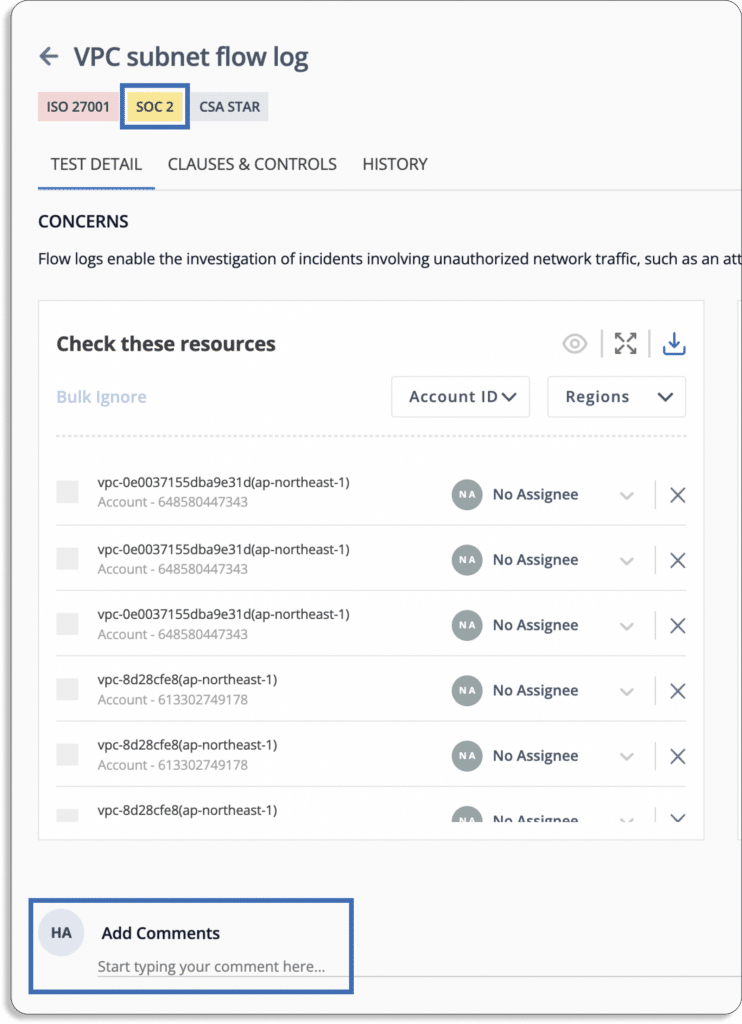
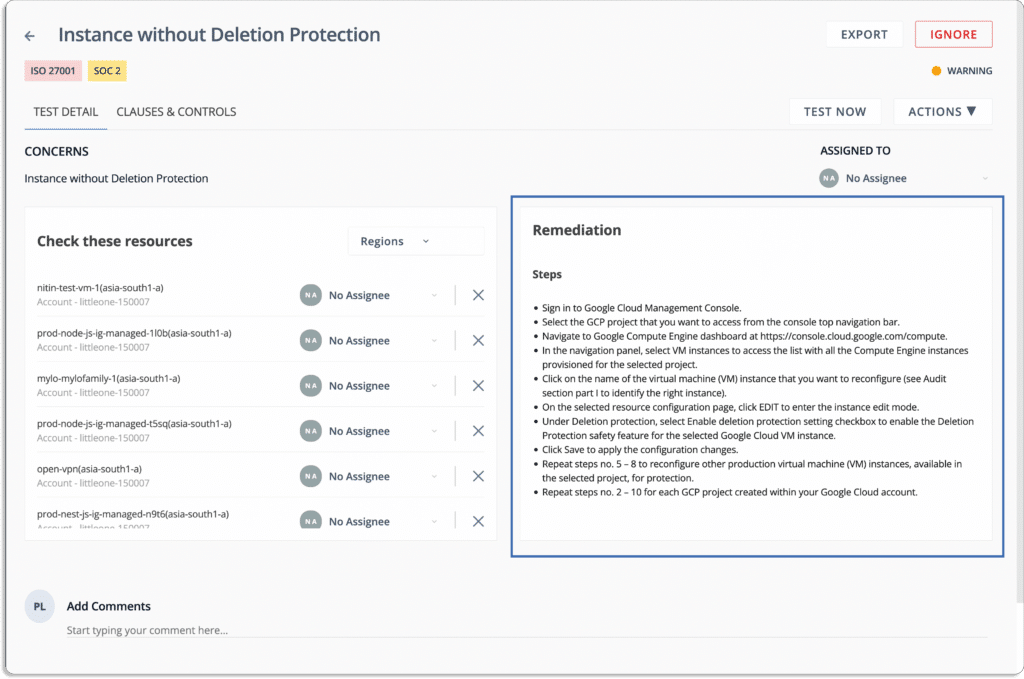
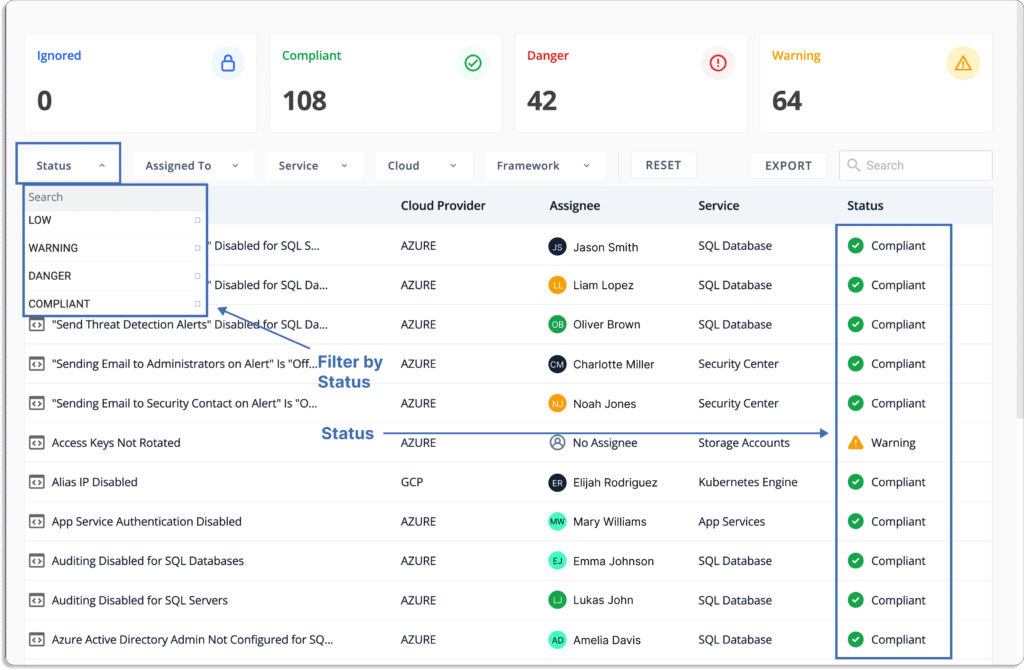
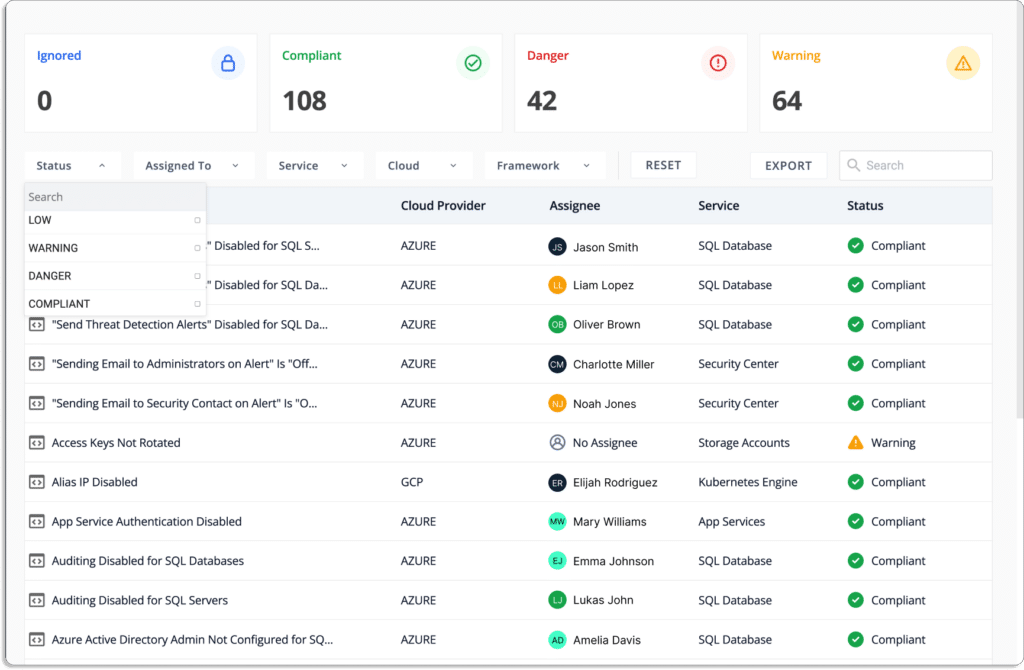
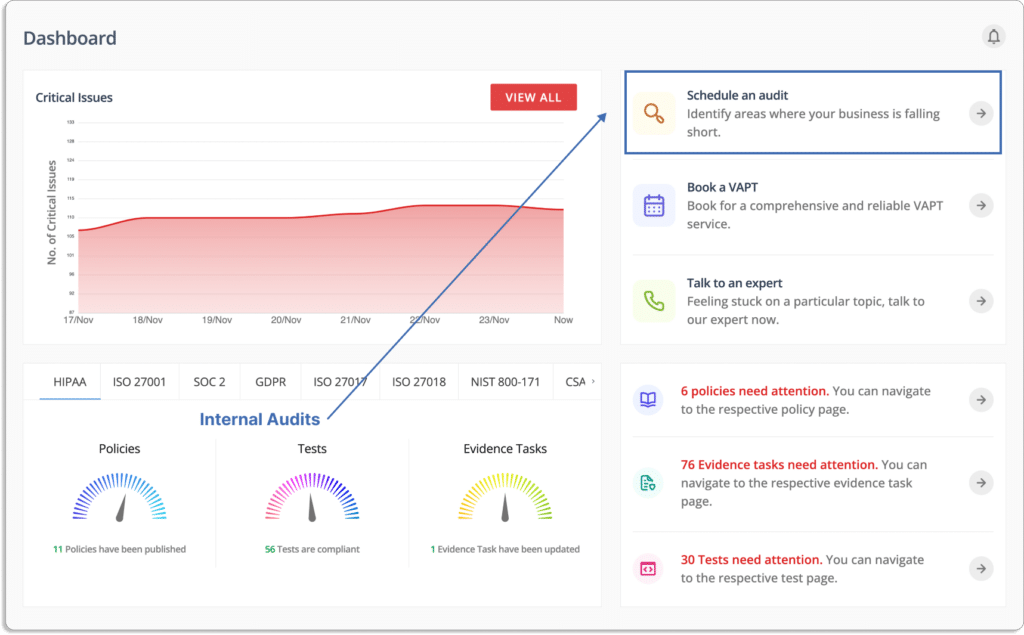
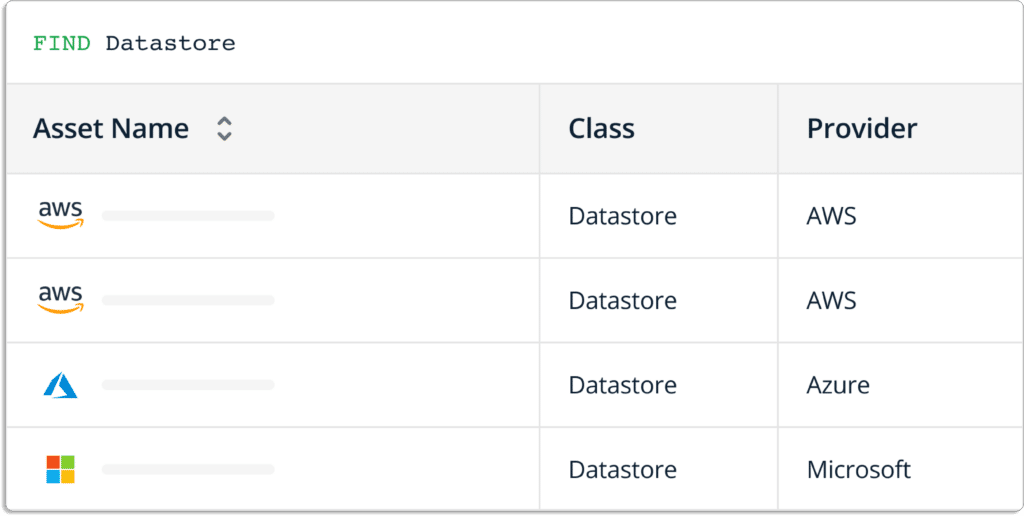
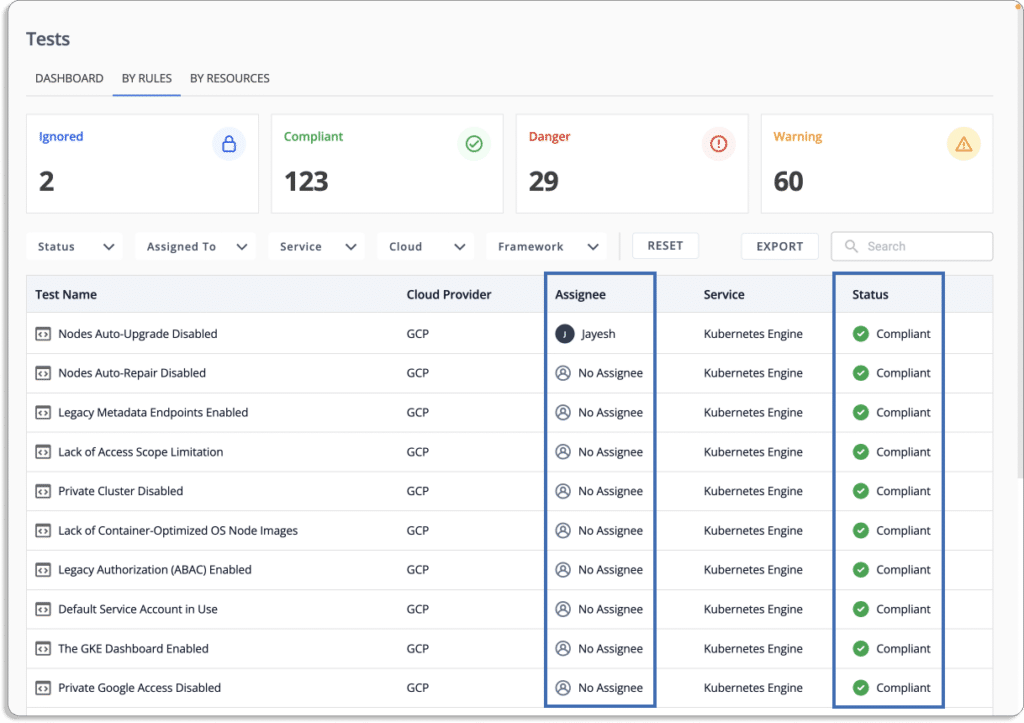
- Continous cloud monitoring
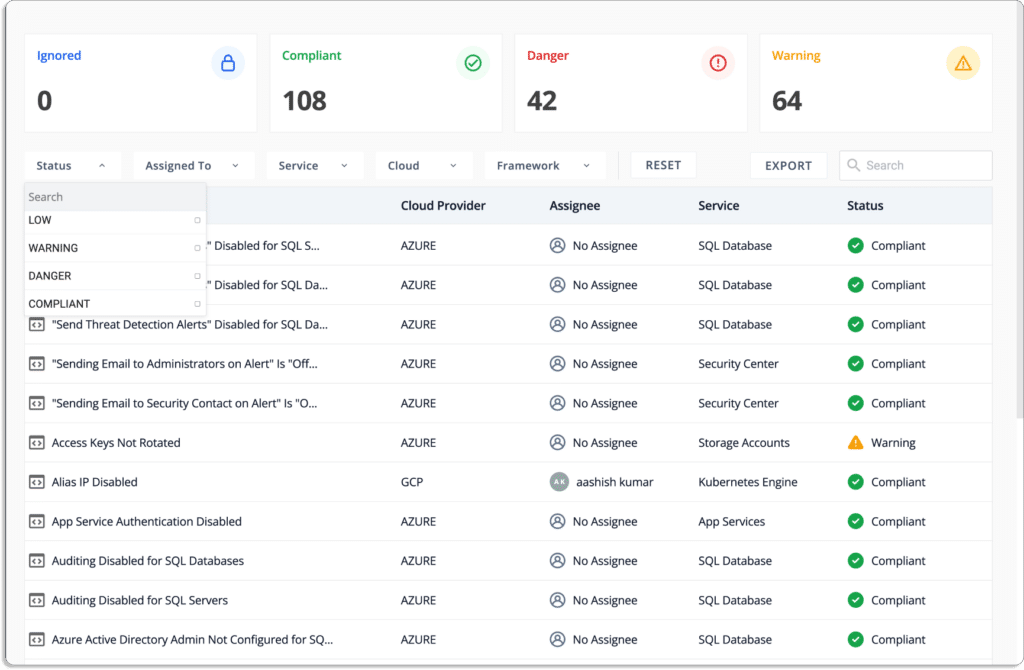
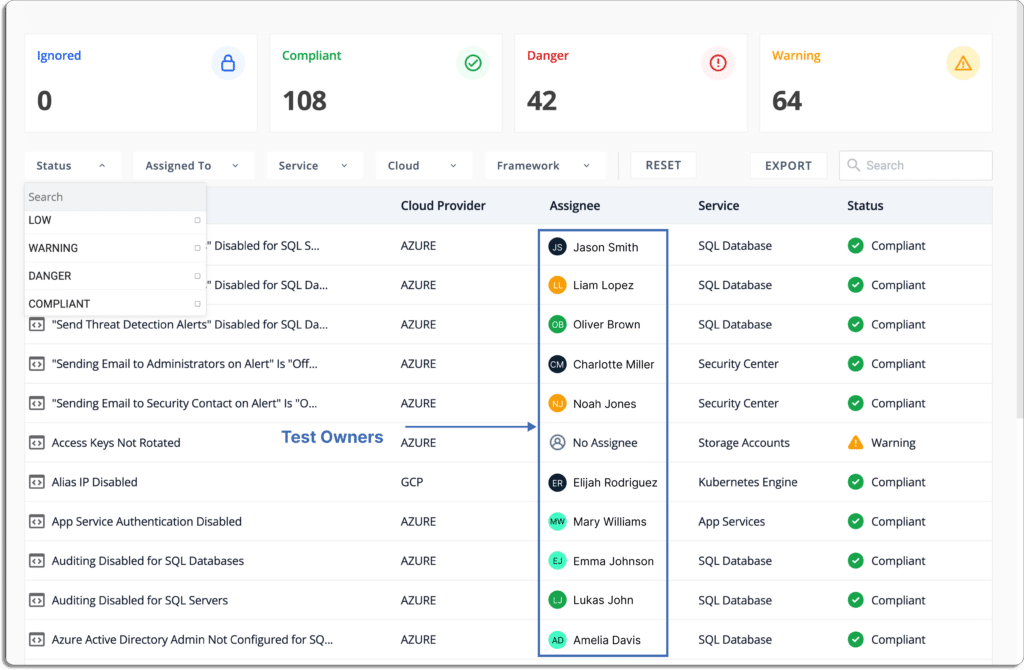
Scrut automatically tests your cloud configurations against 200+ cloud controls spanned across CIS benchmarks to ensure a strong InfoSec posture. It identifies gaps, misconfigurations, and categorizes the resources based on the criticality of the issues.
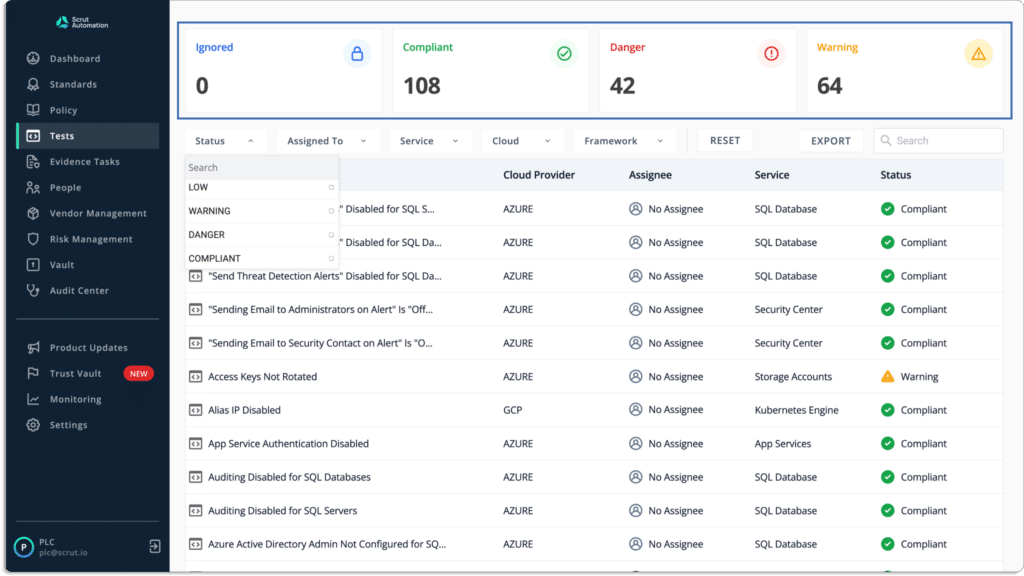
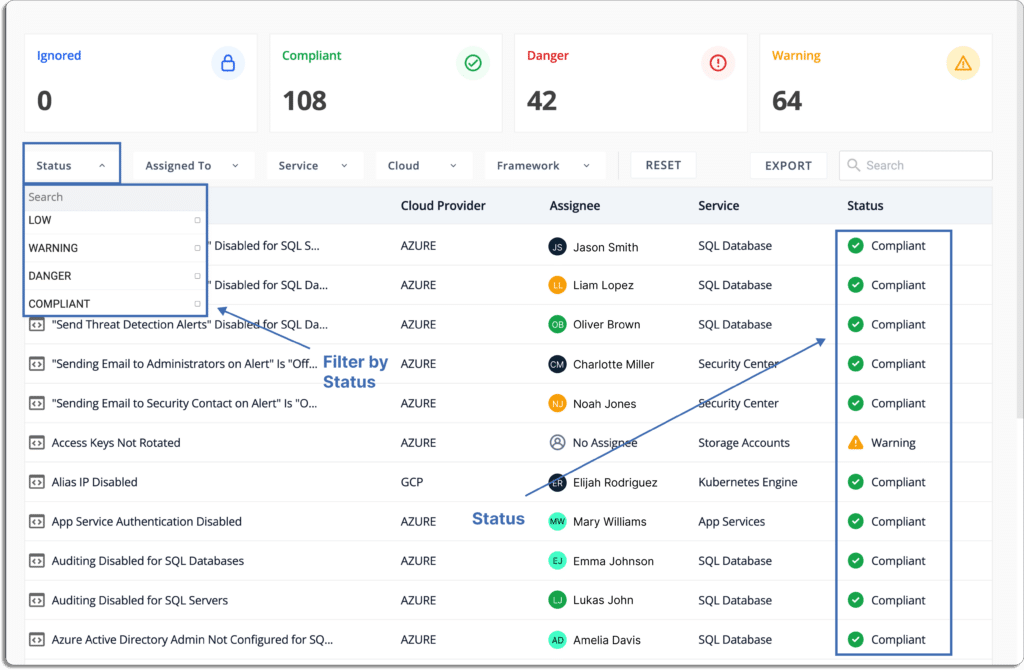
Further, the platform helps you prioritize the remediation tasks. The issues the categorized as
- Danger – The most serious issue.
- Warning – After you’ve addressed the “danger” issues, you can proceed to these.
- Low – These are risks with a low priority that can be addressed last.
- Ignored – You can override the ignore status.
- Compliant – Everything is fine if you are compliant. You are not required to do anything.
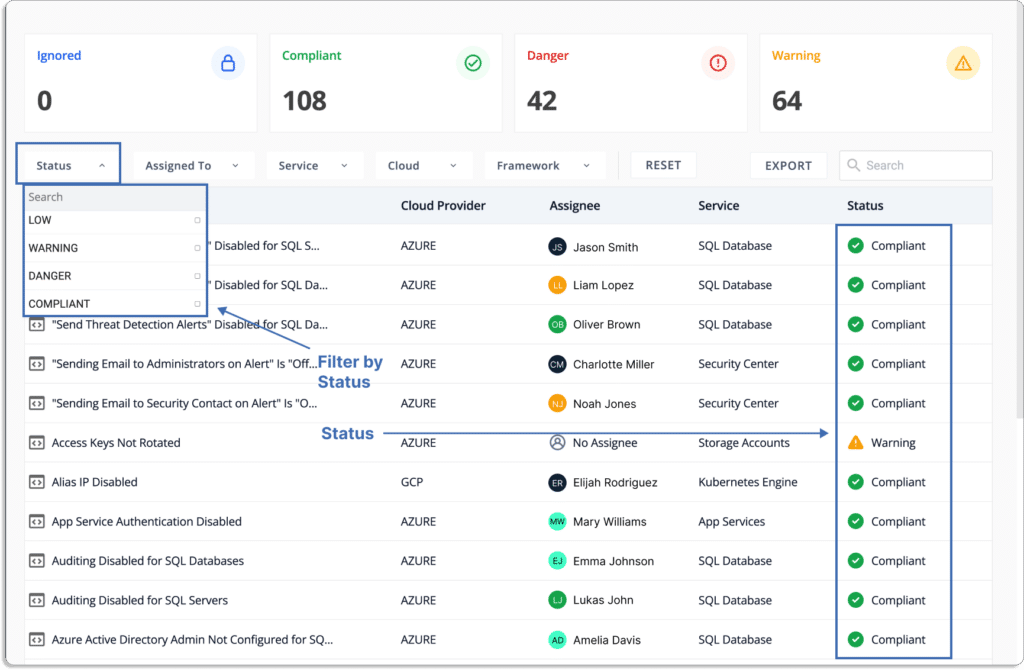
You can monitor your cloud security posture, misconfigurations, and the status of corrective actions, as shown below.
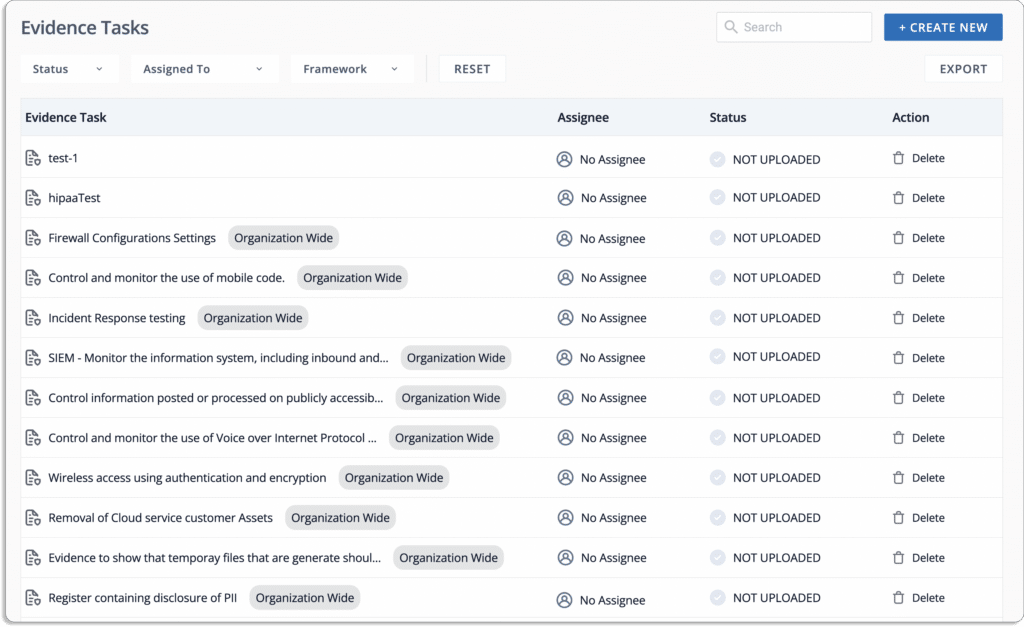
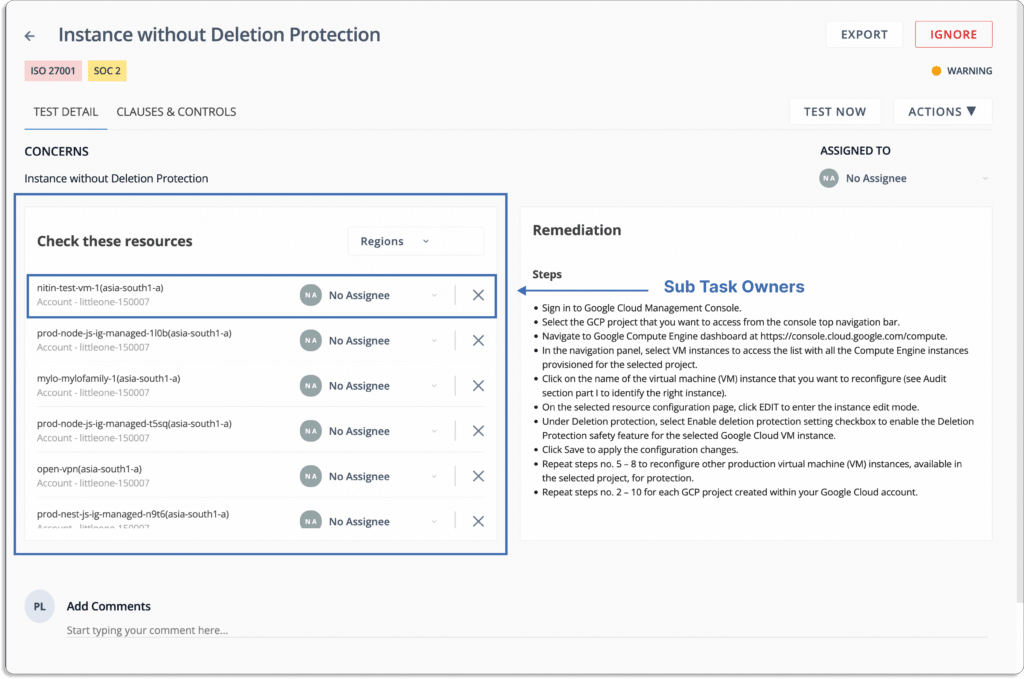
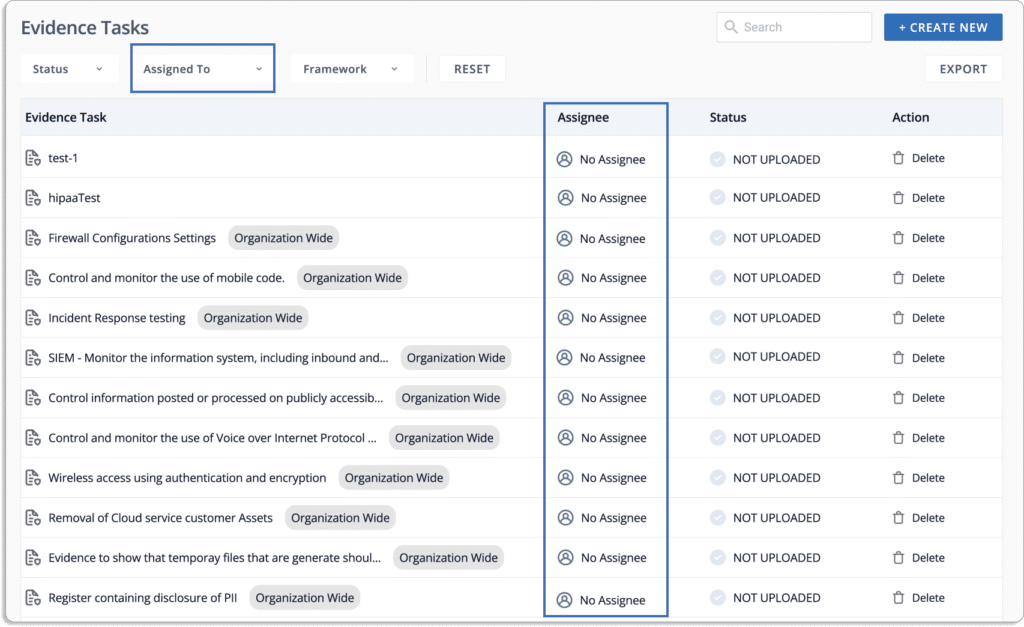
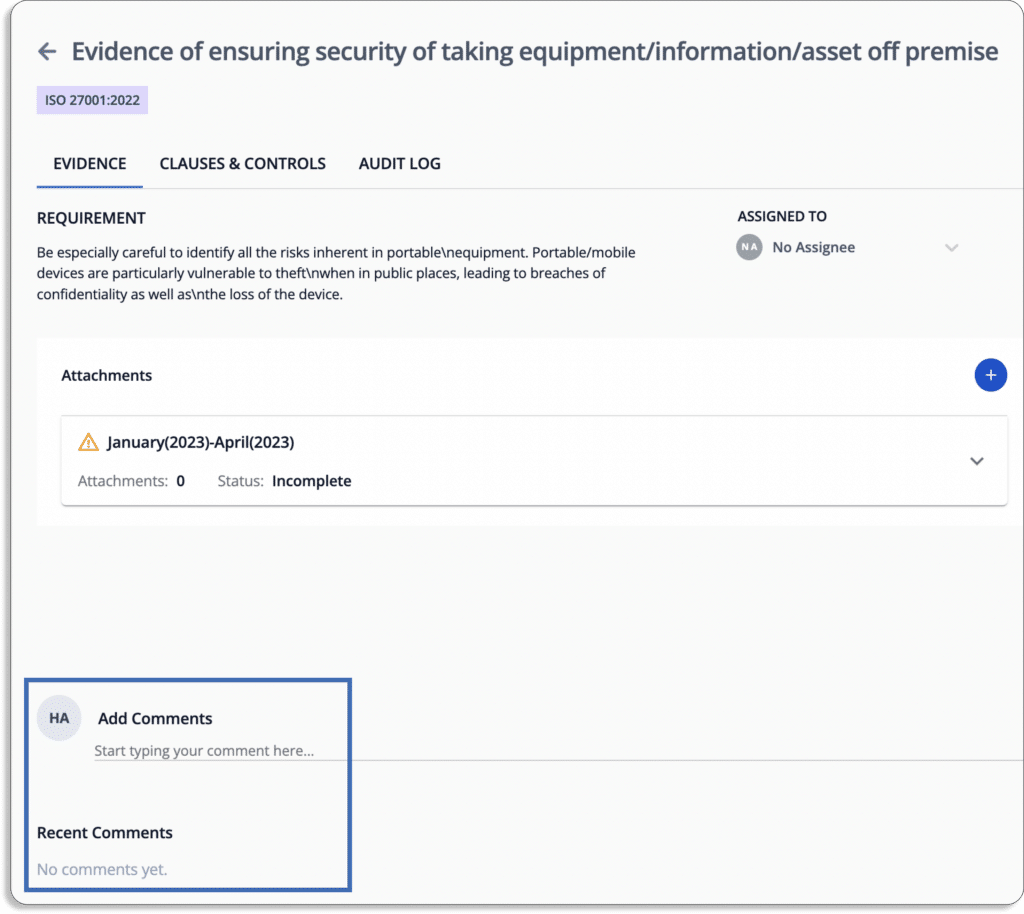
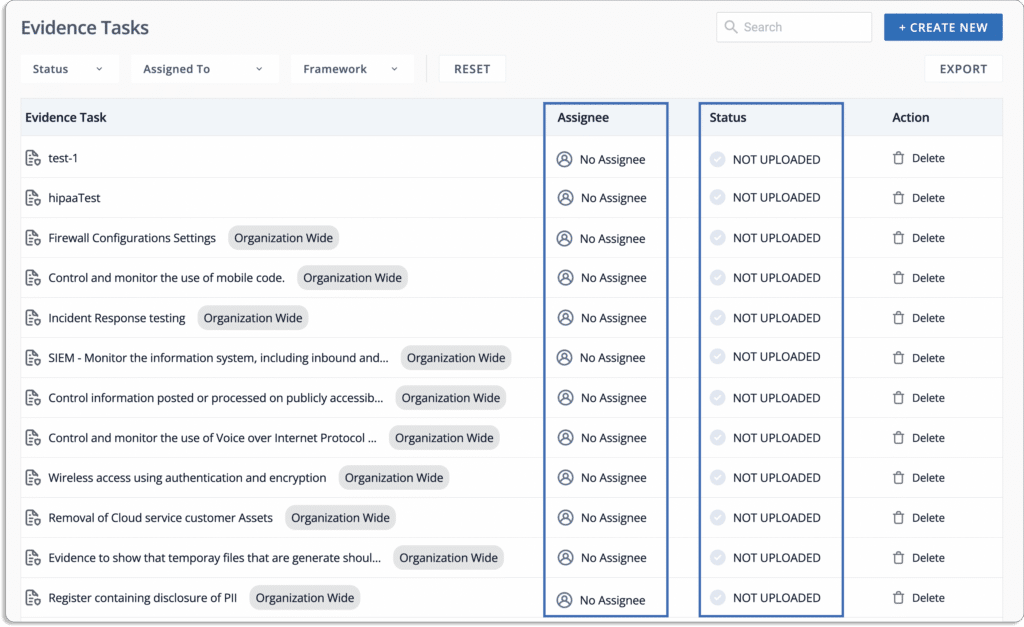
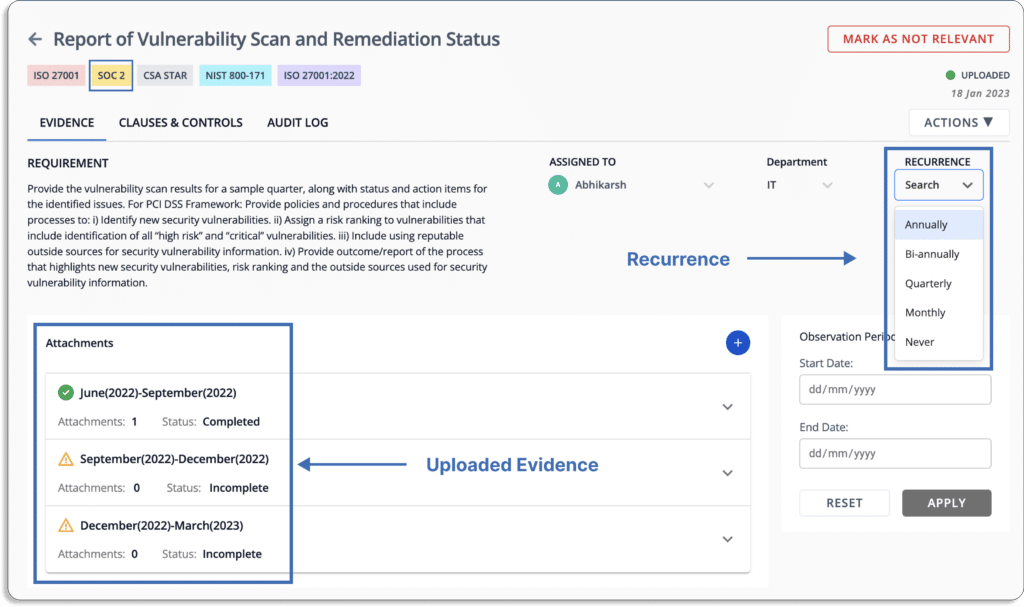
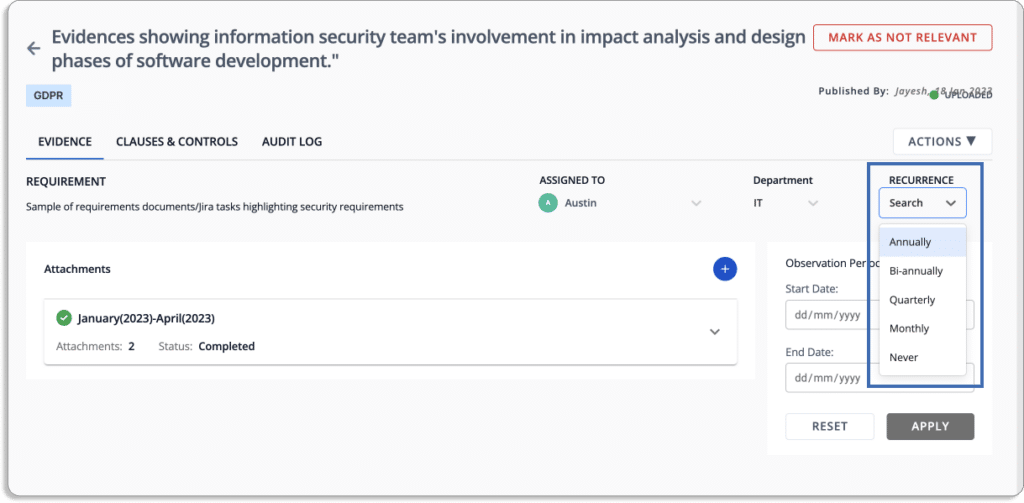
- Automate evidence collection
The tool has more than 70 integrations. Scrut reduces compliance overhead by automatically collecting the required evidence.
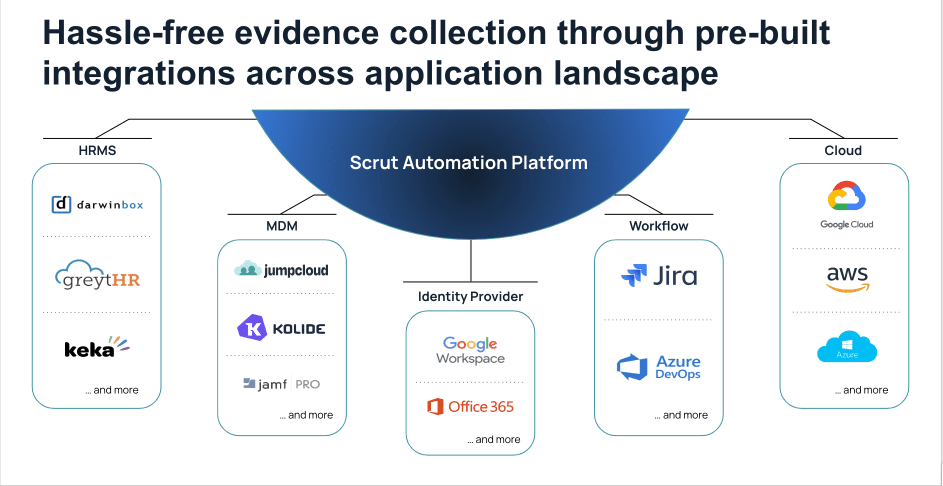
It automates over 65% of the evidence-collection tasks across your application and infrastructure landscapes against pre-mapped controls.
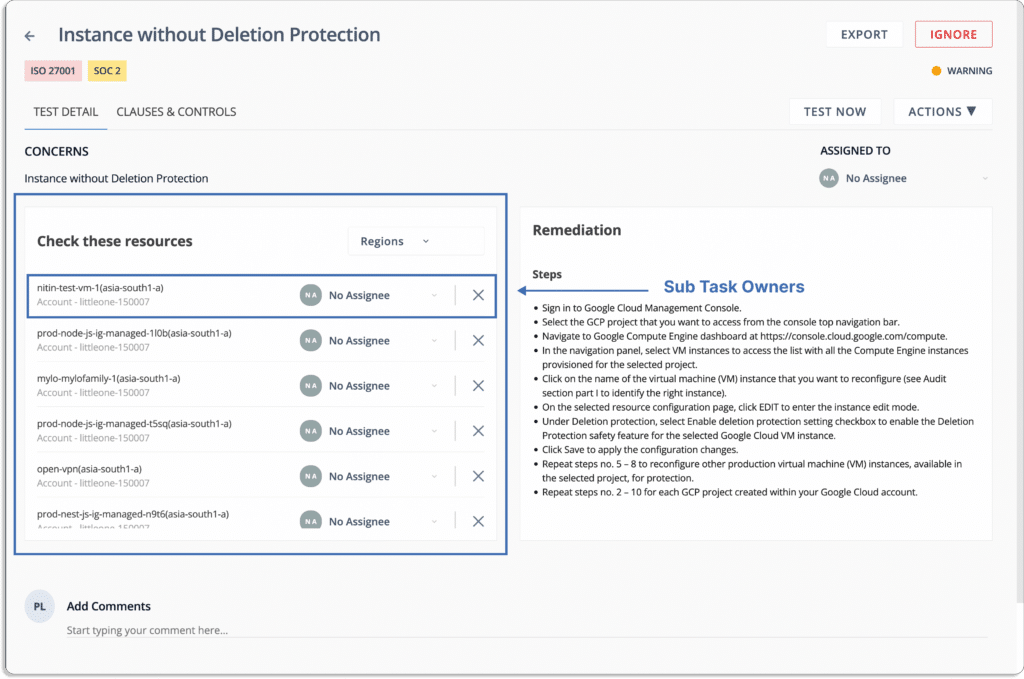
Furthermore, for the remaining evidence-collection tasks, you can assign ownership to different team members and check the status on a single screen.
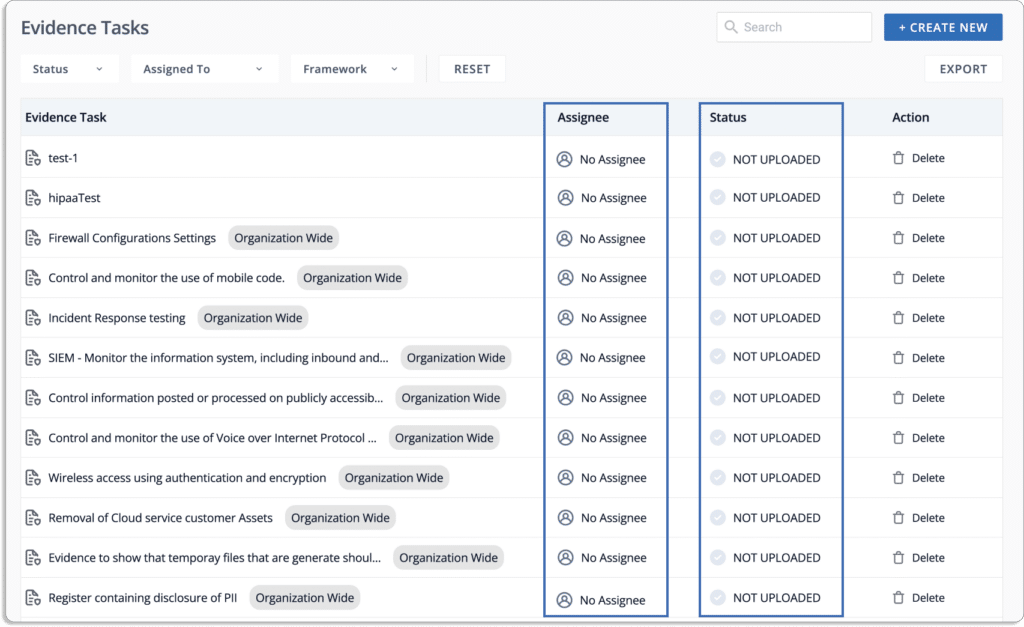
You can also set up the frequency for recurring tasks via the recurrence option.
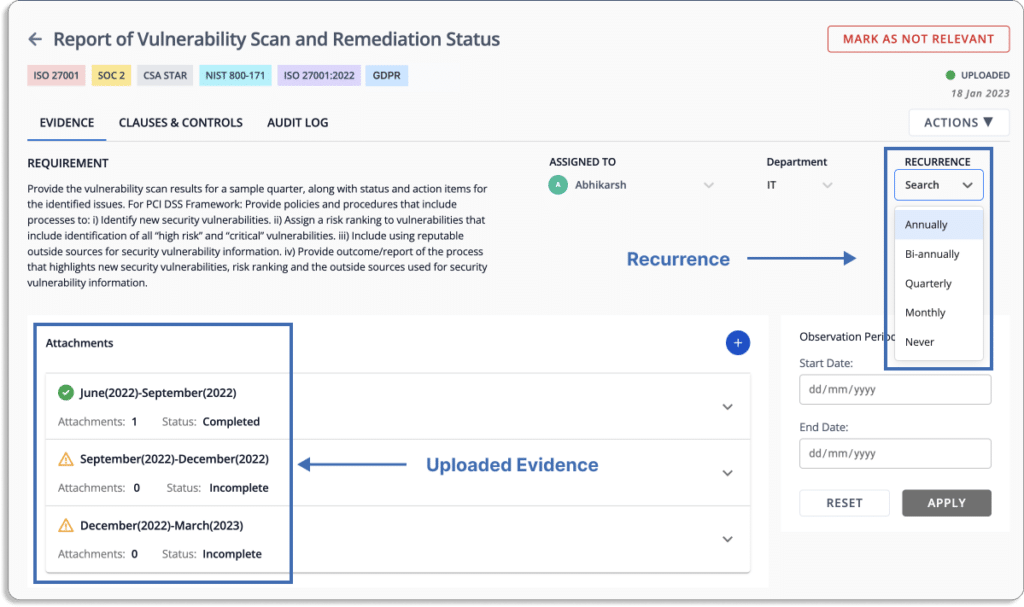
When the person responsible for uploading the evidence pieces fails to do so in time, they get reminders on their email and Slack (depending on the settings).
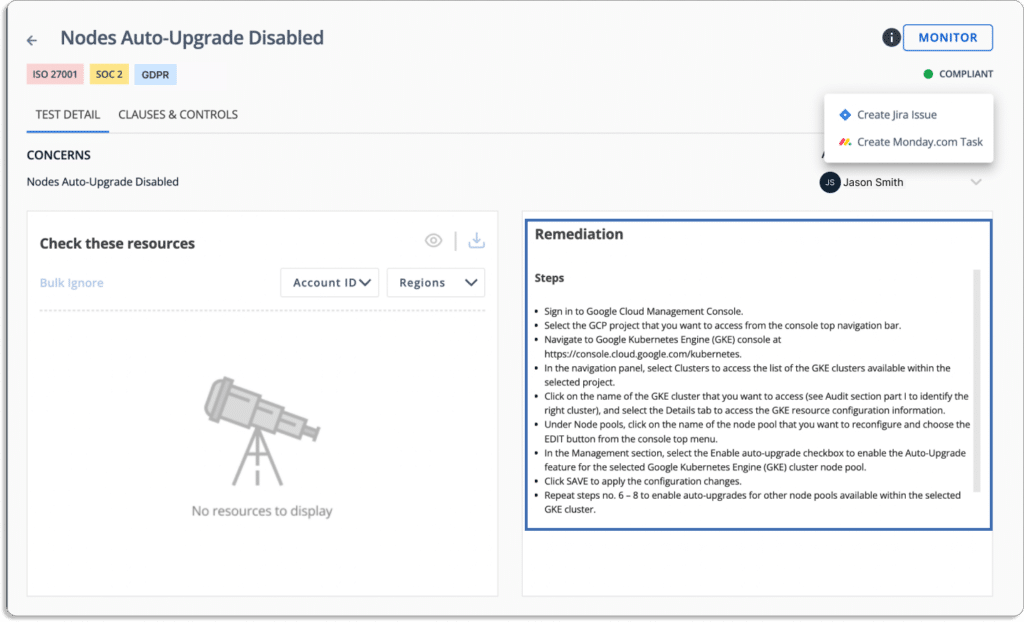
- Streamline compliance workflows
Scrut streamlines all your compliance activities. You can create, assign, and monitor tasks with your team.
Furthermore, it will automatically send reminder for various tasks like policy updates and evidence collection.
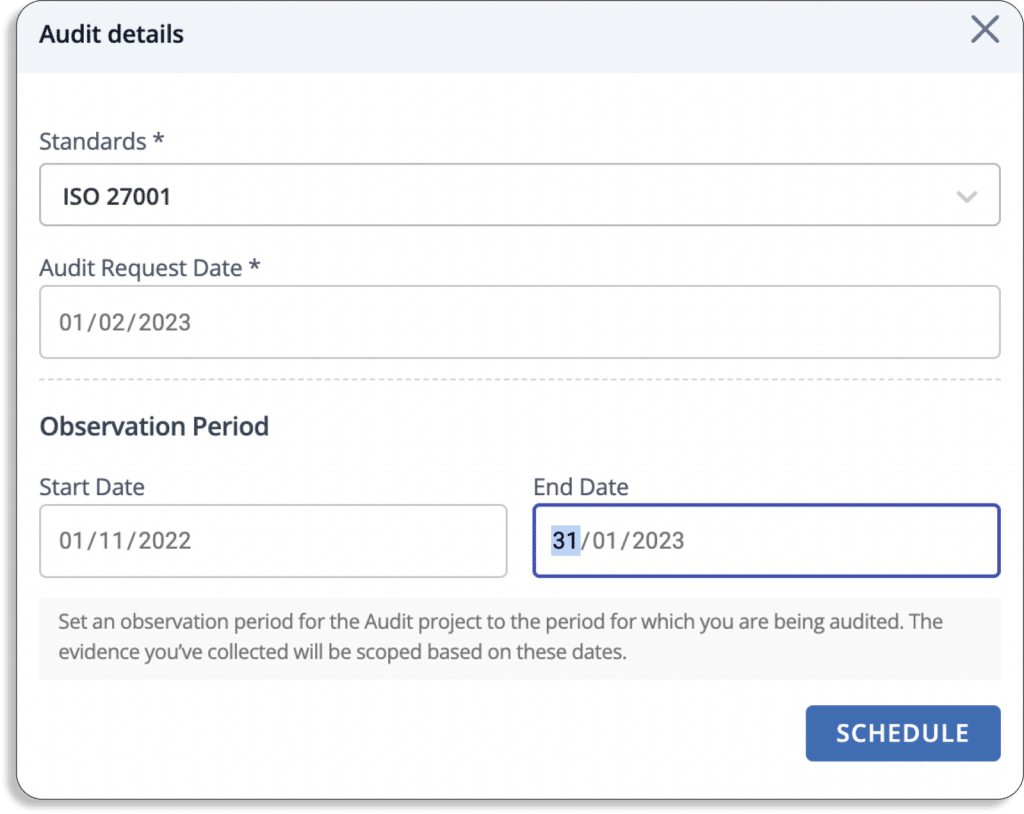
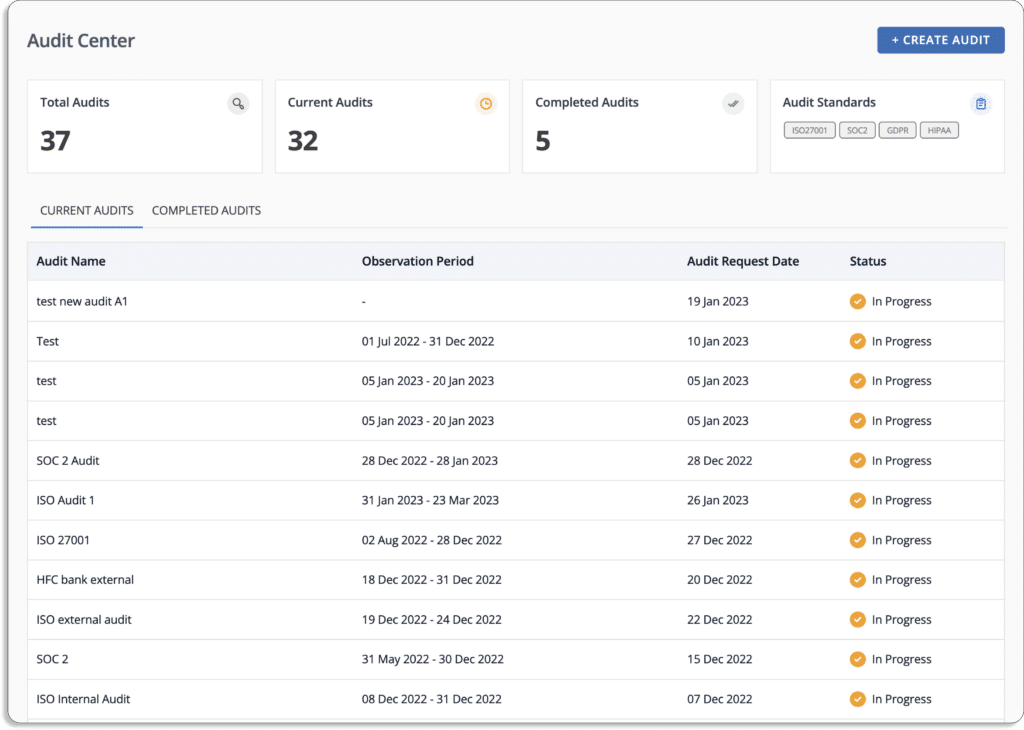
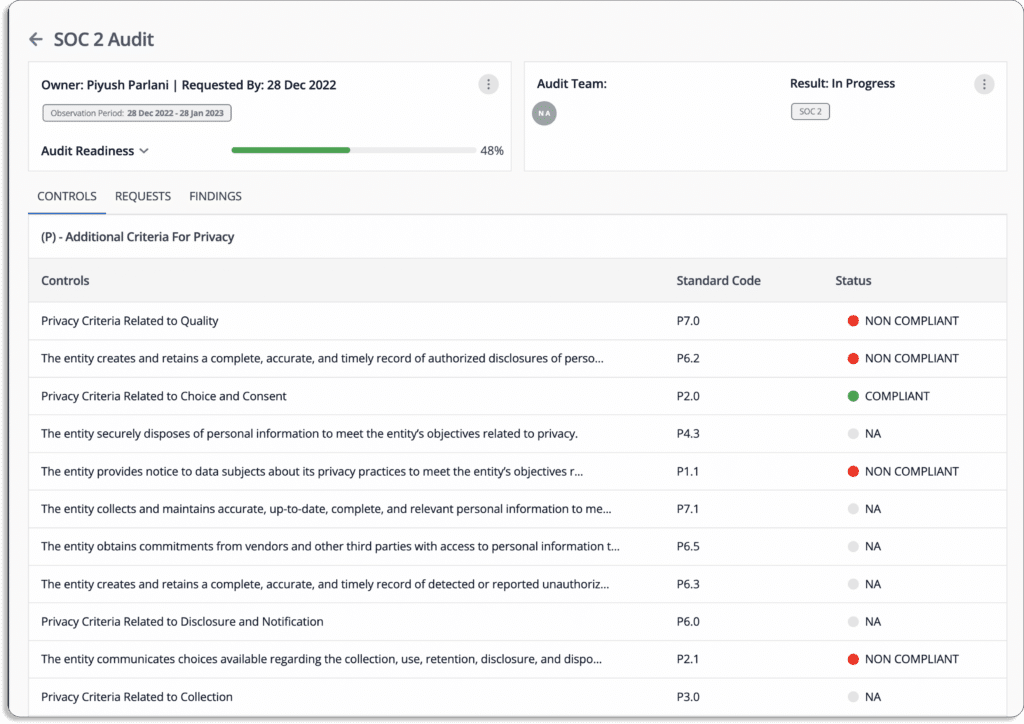
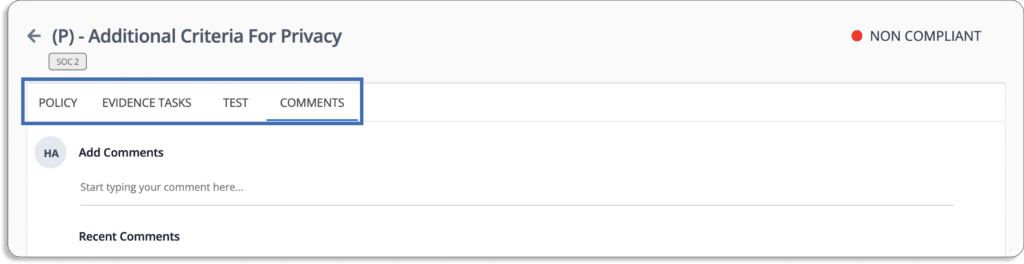
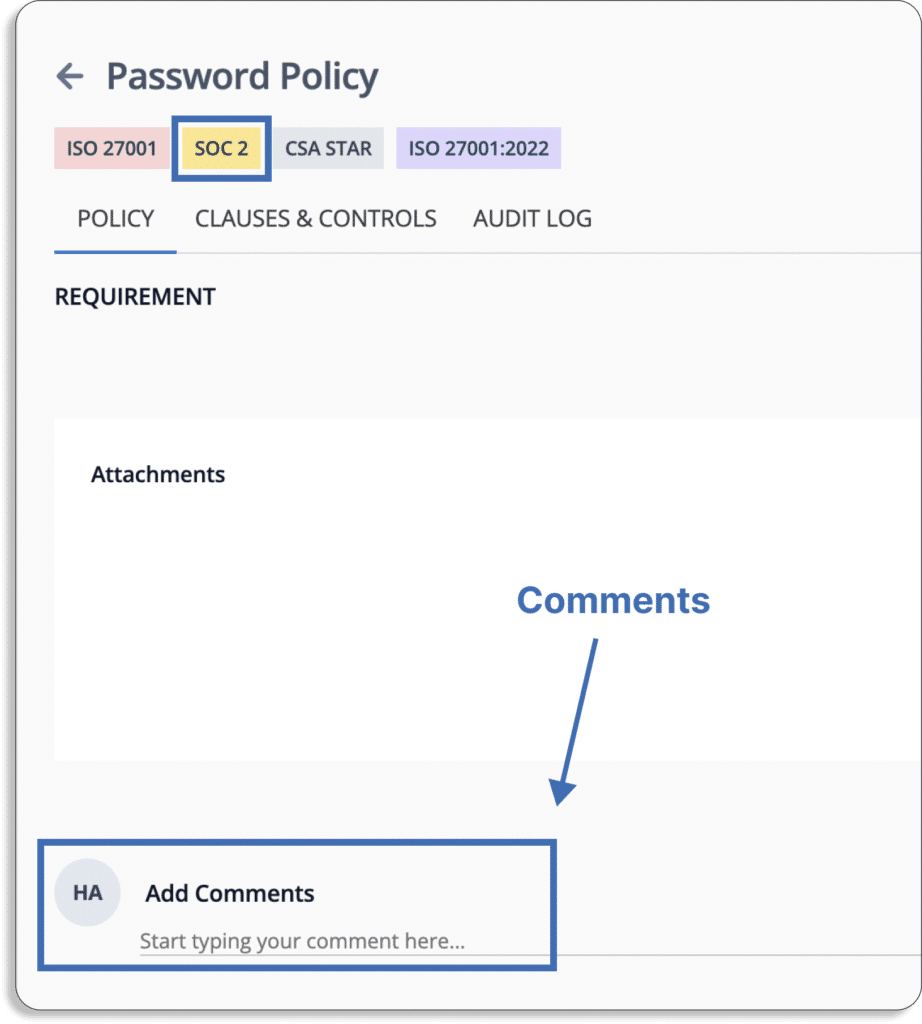
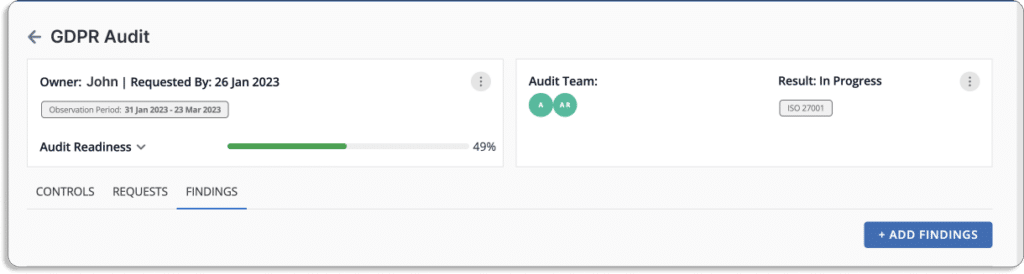
- Collaborate with the auditor on the platform for faster and painless audits
You can manage all artifacts on the platform for a smooth audit process. Scrut allows you to invite your auditors on the platform for audits.
The Audit center allows the auditors to quickly go through policies, controls, evidence, and all required audit artifacts on the platform itself and leave their findings or ask if they need any clarifications.
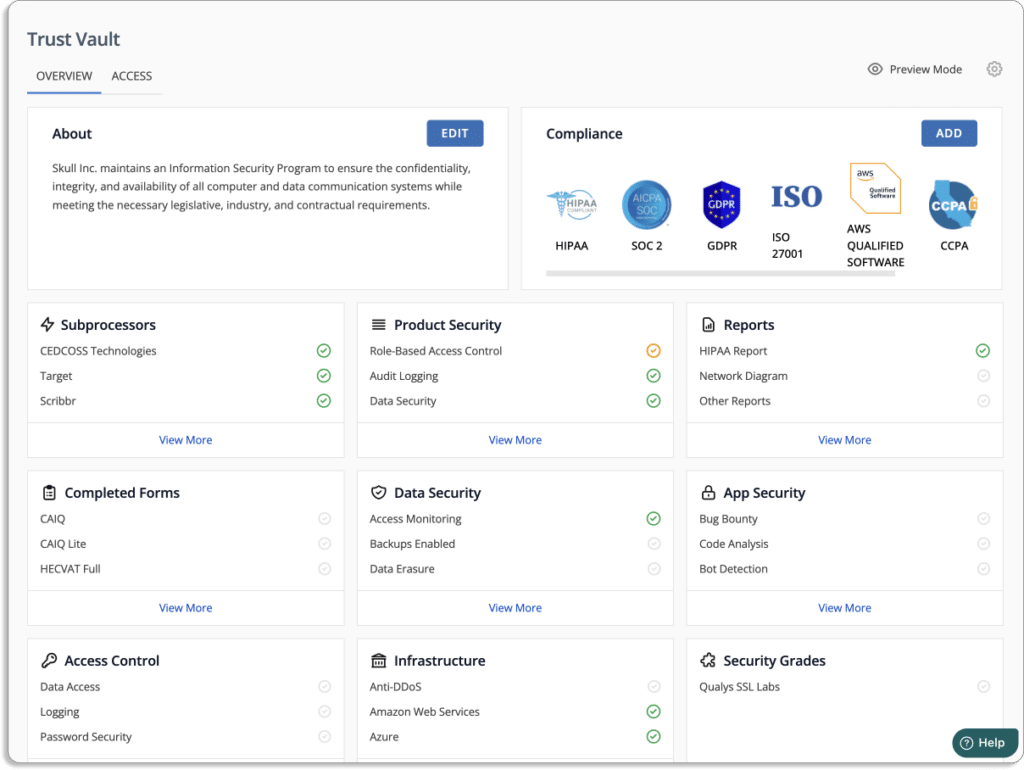
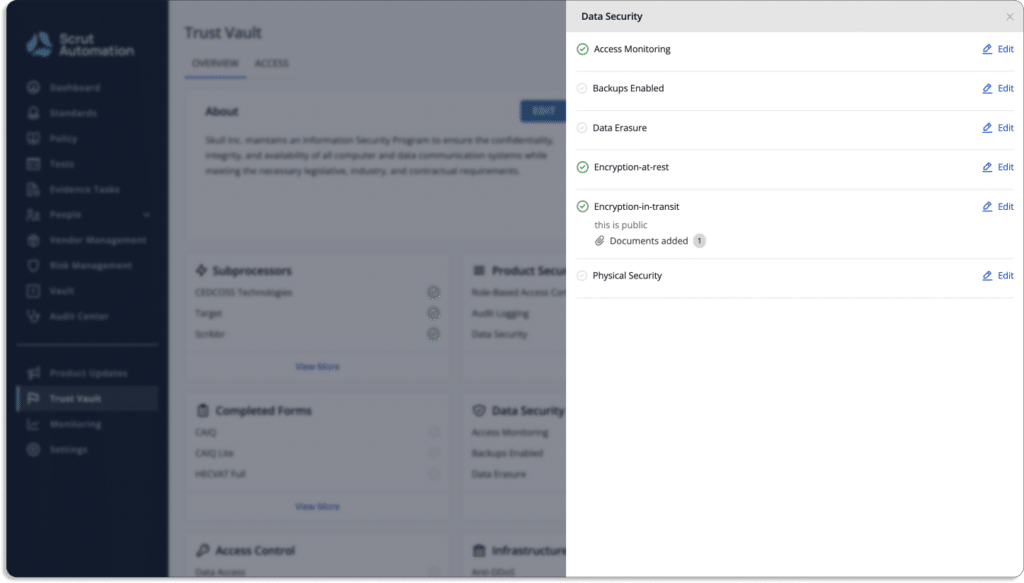
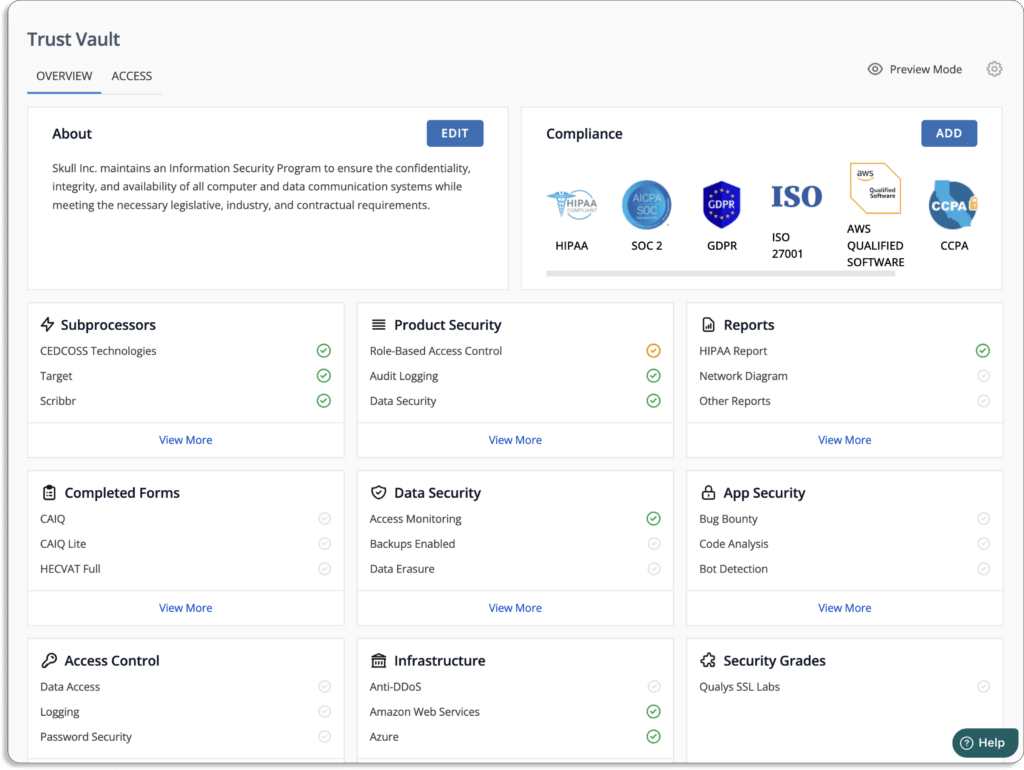
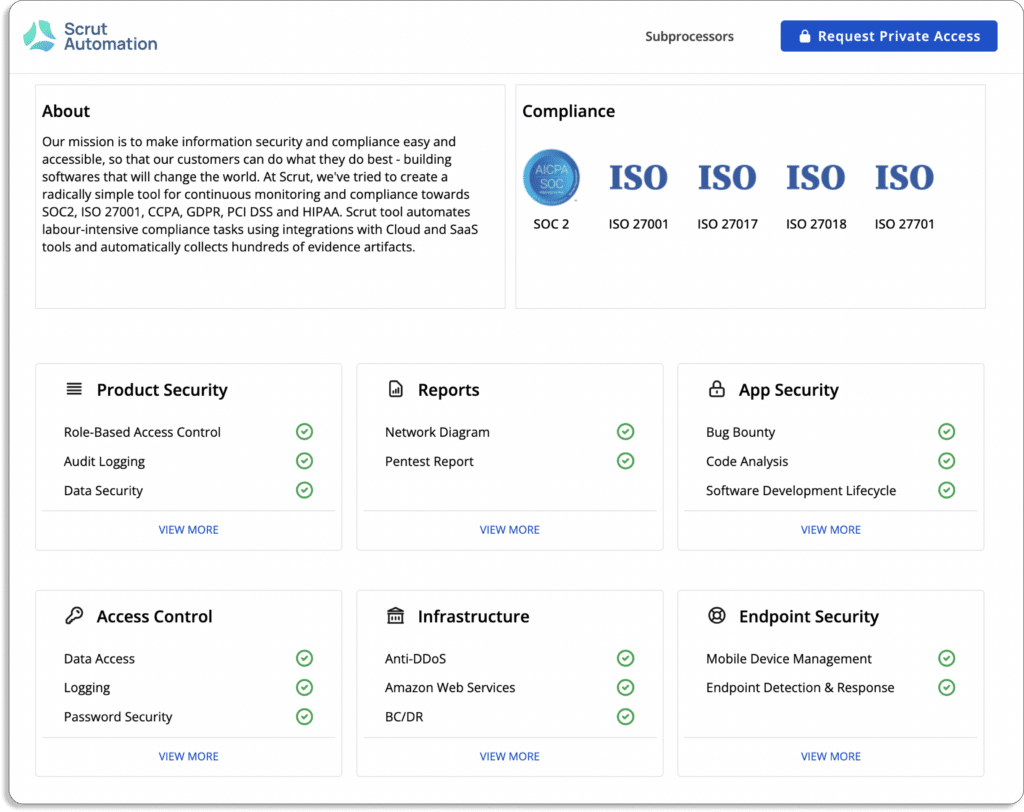
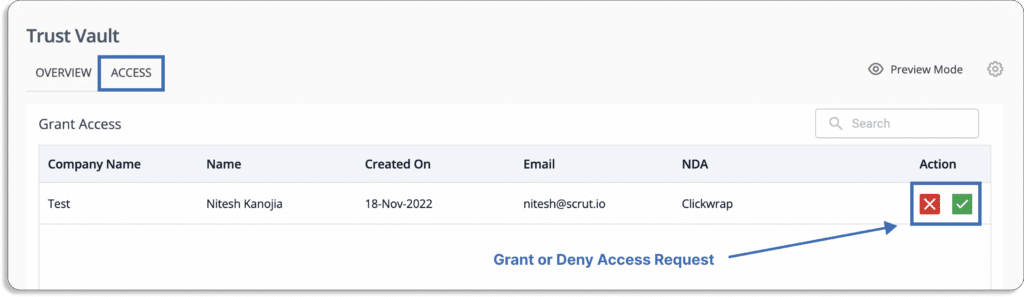
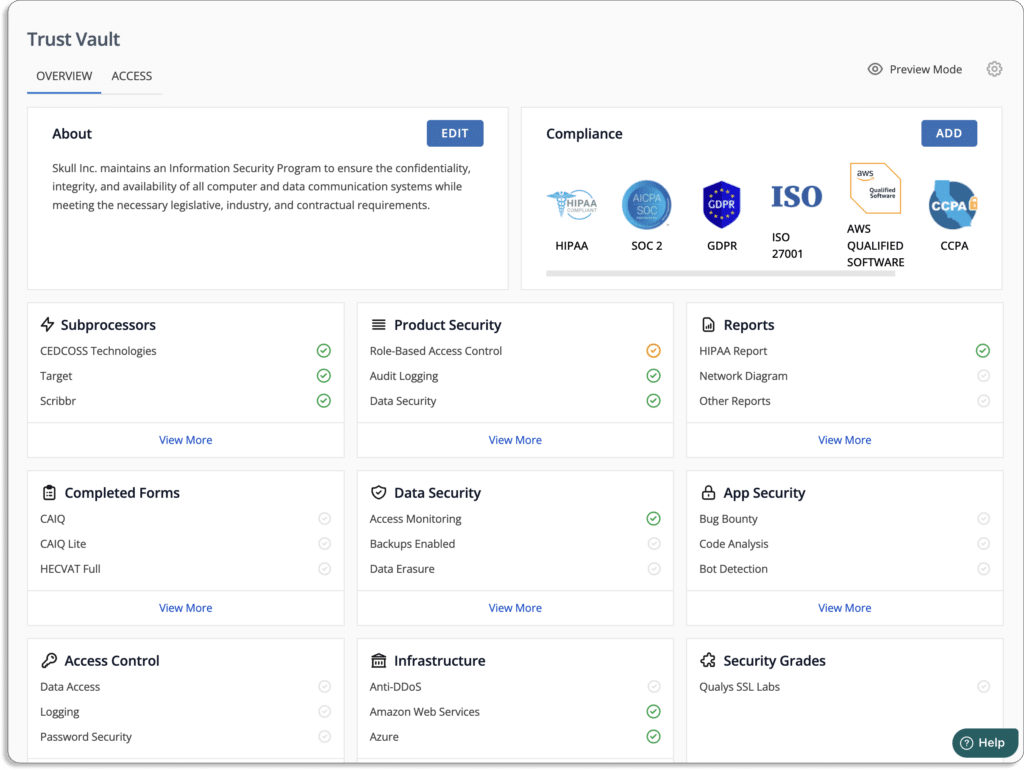
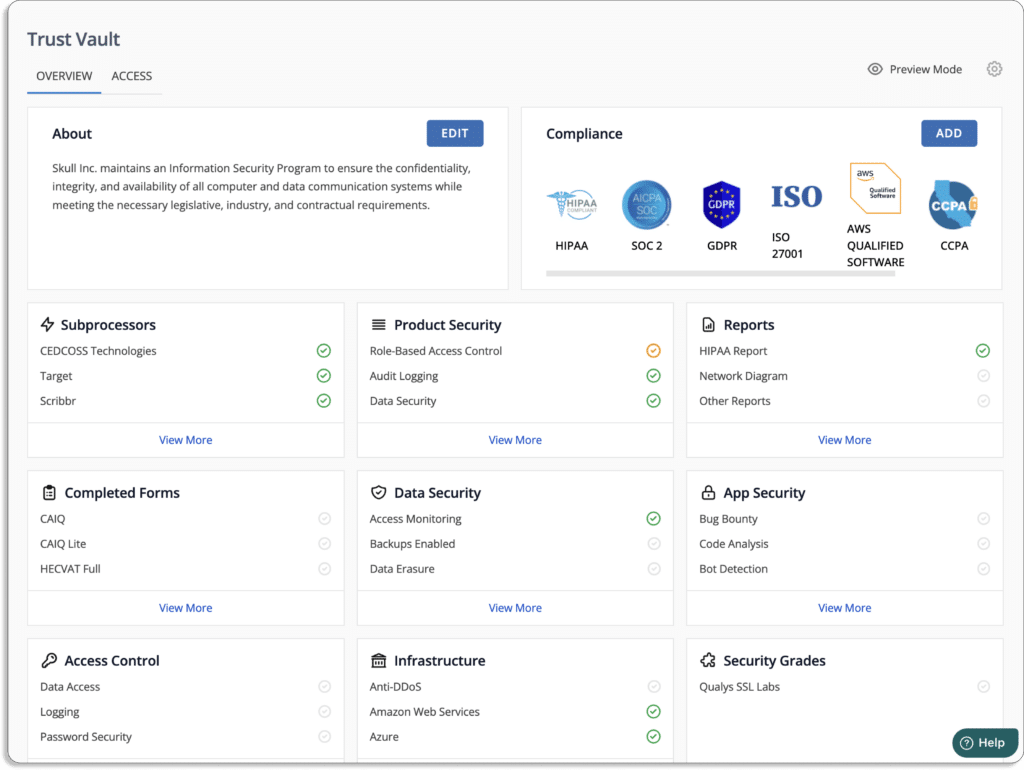
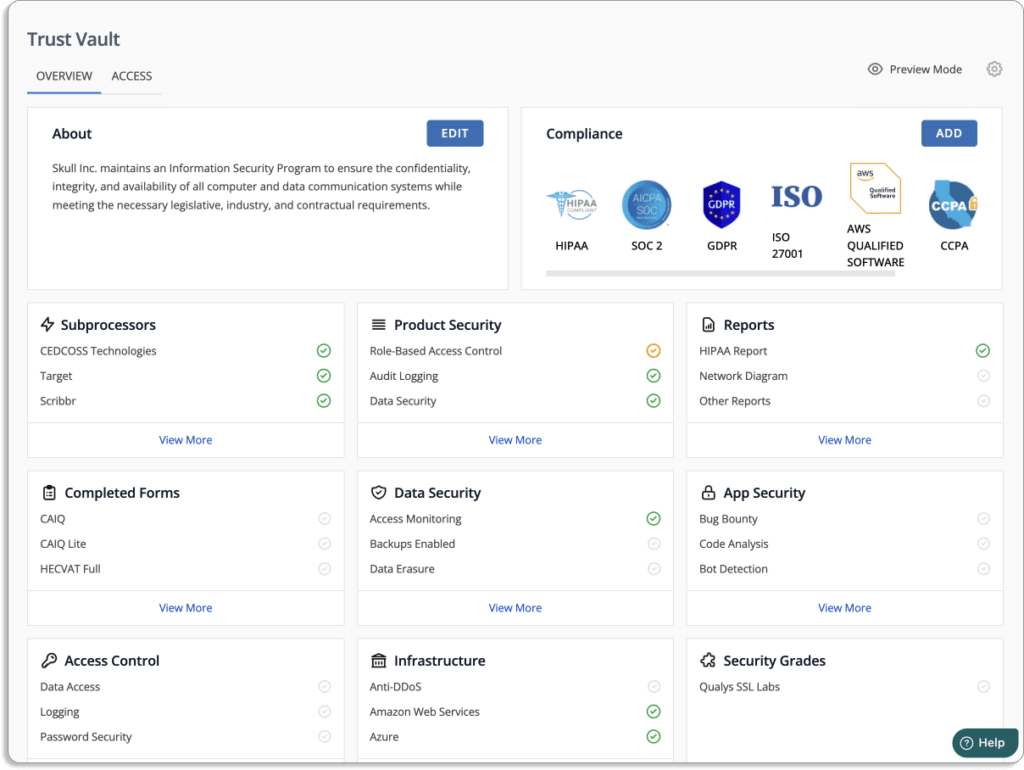
- Build trust from day 1
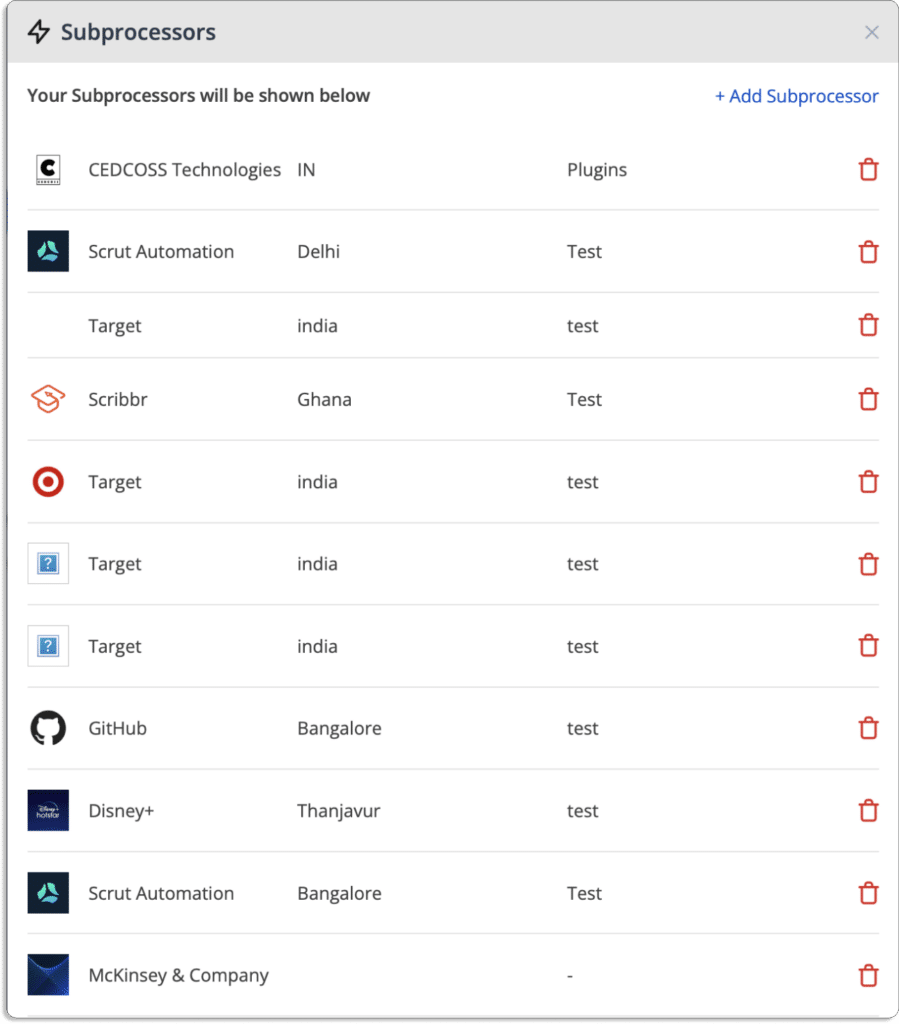
Scrut’s Trust Vault helps you build real-time security and compliance transparency by showcasing GDPR and other security certifications to key stakeholders.
- Single window for all your GDPR requirements
Scrut also offers in-house GDPR compliance experts for a seamless experience.
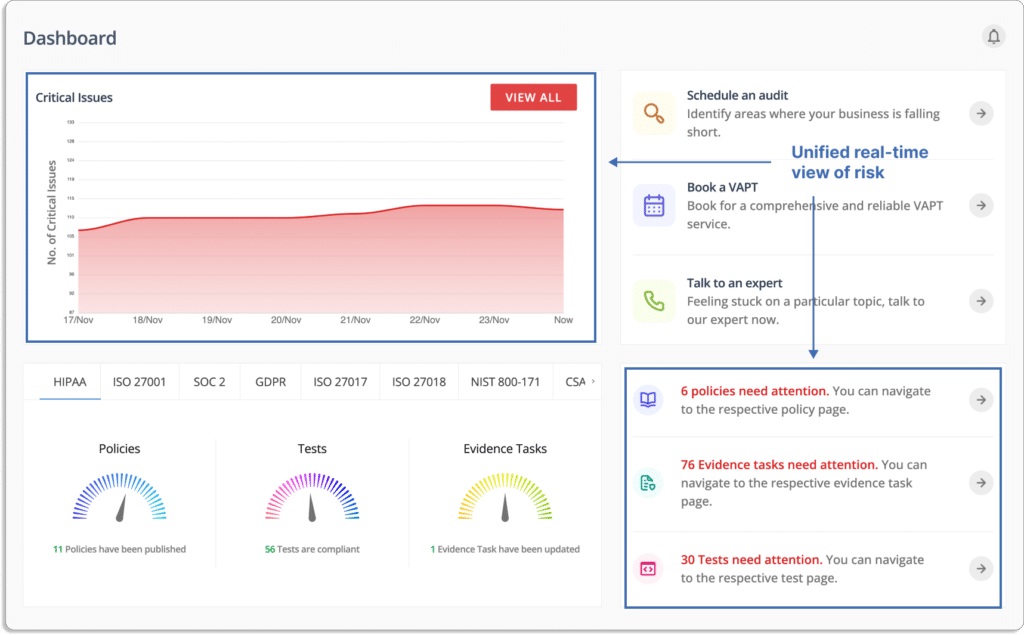
You can book the VAPT service from the platform itself. Further, you can talk to our in-house GDPR compliance experts for any queries or guidance on issues.
Besides this, Scrut manages your service level agreements (SLAs) with all the partners—and represents you during the audits. This means Scrut InfoSec experts will answer all the questions asked by the auditors during the audit.
- Automated employee training
Scrut helps in automating employee information security training. It provides exhaustive security awareness training documents, recorded sessions, and automated policy assignments that help your employee learn about InfoSec’s best practices.
The tool provides your employees with everything they need to understand potential risks, avoid slippages, and develop a secure posture.
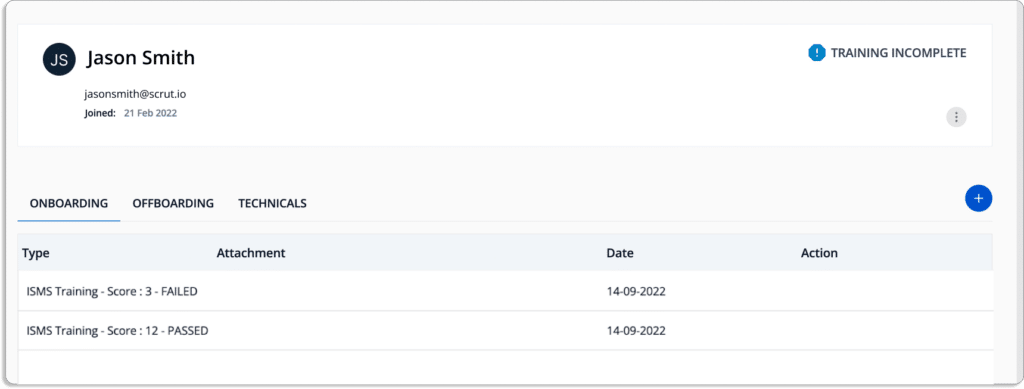
Further, you can always see the status of all employee’s training to know whether they have completed the training or not.
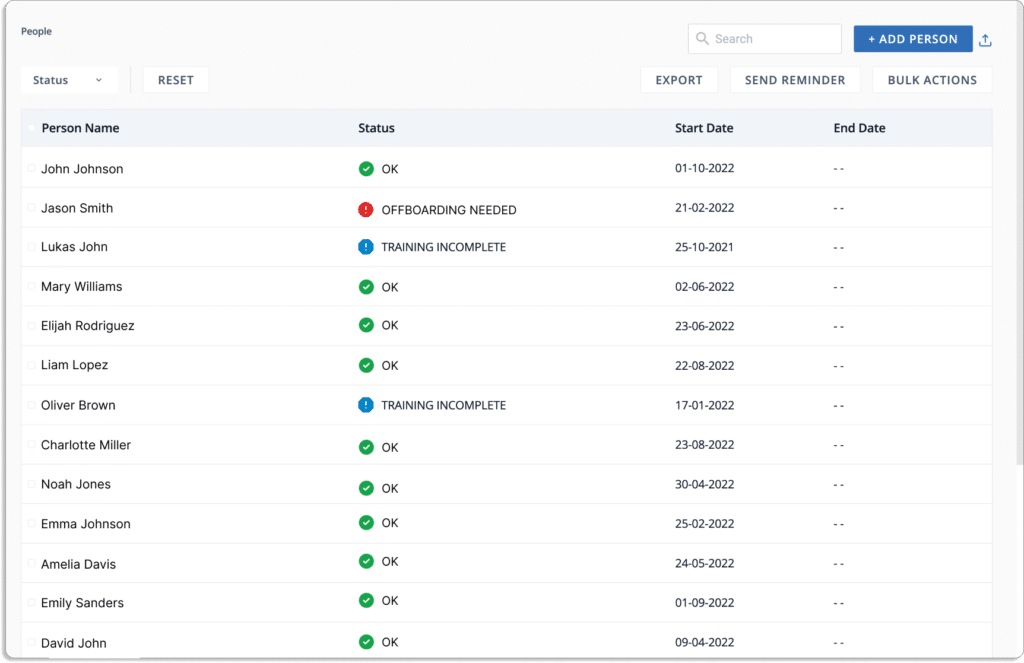
Once the employee completes training, they need to complete a quiz to evaluate their knowledge. You can setup passing score.
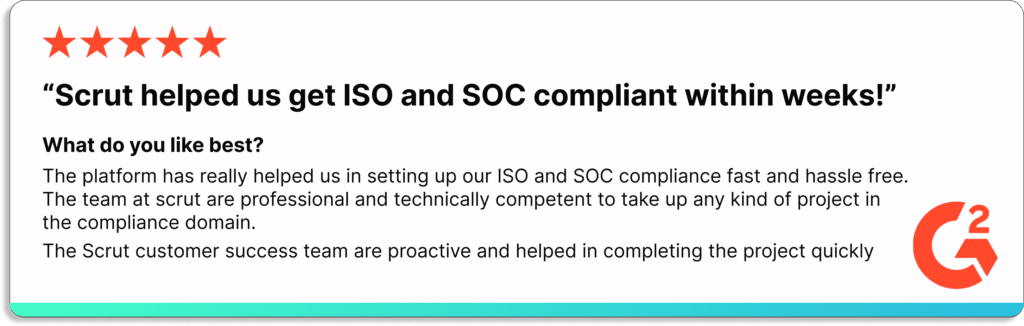
Check our customer reviews below.

Customer Rating
- G2: 5/5
2. Drata
Drata is a security and compliance automation platform that continuously monitors and collects evidence of a company’s security controls.
Drata’s security reports and trust center provide on-demand, sharable reports demonstrating your security posture. Furthermore, it provides a GDPR control library, custom control, and comes with policy templates to speed up the compliance process.
Pros
- Drata’s dashboard lets users easily see which GDPR controls map to the framework requirements and what criteria they need to meet.
- The platform’s document upload feature enables users to communicate properly with auditors.
Cons
- Integrations with Google Cloud Platform and Checkr don’t always work as expected.
Customer Rating
- G2: 4.9/5
3. Vanta
Vanta assists businesses in scaling security procedures and automating compliance with the most demanding standards, including SOC 2, ISO 27001, PCI DSS, GDPR, HIPAA, and CCPA. You can connect your tools to Vanta and fill in the gaps on your dashboard.
Pros
- Vanta collaborates with audit firms and PenTest providers, which helps streamline the process.
- The platform eliminates manual work by connecting directly with development systems, such as GitHub and GCP.
- The tool offers automated task reminders.
Cons
- Vanta misreports items and a few exceptions regarding evidence collection that needs to be worked around by the user.
- Tracking requirements like encryption does not function on Linux machines.
Customer Rating
- G2: 4.7/5
4. LogicGate
LogicGate Risk Cloud is a platform with a pre-built application suite that transforms how you manage GRC processes by combining expert-level content and service with no-code technology. The platform combines several GDPR readiness components to simplify key requirements for managing personal data. It maintains a centralized repository for tracking data breaches and remediation records.
Pros
- Users can customize workflows as per their requirements.
- Users can create forms to automate, collect, and store event details and responses.
Cons
- Users have to enter some fields manually. For example, the test plan description field.
Customer Rating
- G2: 4.6/5
5. ZenGRC
ZenGRC is a compliance management software that assists in examining your environment, data, and policies to ensure that the risk management controls are in place to protect your GDPR data. It helps to organize and manage GDPR requirements more efficiently by automating many time-consuming manual processes that would otherwise consume your time.
Pros
- It replaces the Jira tickets process with evidence collection and workflow features.
- Users can customize frameworks according to their requirements.
Cons
- There is no in-line editor in ZenGRC for editing policies on the platform.
- Users have to add custom fields to the model risks functionality.
Customer Rating
- G2: 4.4/5
6. JupiterOne
JupiterOne automates your compliance processes by building and automating policies, procedures, and controls that link security requirements to specific cyber assets in your digital environment. The platform assists organizations in streamlining their compliance requirements, regardless of security maturity level. Furthermore, it speeds up security audits and reviews by reusing controls from multiple frameworks.
Pros
- Easily integrates with your cloud service providers and other tools.
Cons
- It doesn’t allow collaboration with auditors on the platform for a smooth audit process. There is a significant barrier to learning all the distinct features.
Customer Rating
- G2: 5/5
7. Tugboat Logic (Now merged with OneTrust)
Tugboat Logic is a GDPR compliance software that continuously assists your business in getting ready for GDPR audits. The platform offers pre-built policies and controls mapped to the GDPR framework. It provides a centralized record system for assigning control to your organization’s owners. Using Tugboat Logic’s web-based console, you can assess which controls have been implemented and assign gaps to store evidence.
Pros
- Tugboat Logic’s machine learning suggested answers save a significant amount of time when answering information security questions.
- Users can publish and track policies. For example, the acceptable use policy.
Cons
- Users cannot see the questions in their question bank.
- Users cannot integrate with a component content management system such as easyDITA.
Customer Rating
- G2: 4.6/5
8. AuditBoard
AuditBoard creates an effective GDPR program by gaining a holistic view of your privacy program. The platform identifies and creates issues while testing, assigns owners to action plans, and automates follow-up. It simplifies policy management with real-time updates. Moreover, you can integrate with Microsoft Word and use standard templates to save time when creating documents.
Pros
- The platform enables users to plan tasks ahead of time.
- Users can use filters and keyword search options to find the controls easily.
Cons
- Users can view only one file at a time with AuditBoard sync.
- There is no module for third-party risk management.
- Data in survey templates is not editable.
Customer Rating
- G2: 4.8 /5
9. VComply
VComply provides a unified framework for implementing and managing data privacy regulations such as GDPR. The platform simplifies asset and data management by coordinating workflows and delegating responsibilities. It uses risk assessment to assess data privacy risks and control data., It enables organizations to consolidate content from trusted sources and map policies and processes.
Pros
- The tool provides built-in integrations with Excel to transfer existing files.
- Provides an easy follow-up process with system alerts.
- Easy to customize as per the requirements.
Cons
- VComply dashboard does not provide search filters to view the overall status better.
Customer Rating
- G2: 4.6/5
10. OneTrust
OneTrust is a compliance and governance platform that identifies GDPR-related gaps in your privacy program by assessing and developing a plan from the design stage through the data processing lifecycle. The platform creates a central inventory of data flows to keep track of your processing activities. It increases visibility into incidents, allowing you to determine what data is affected, how it is used, who has access to it, and where it flows.
Pros
- Users can configure settings as per their requirements.
- The tool automatically updates and keeps track of the compliance program.
- Users can directly send vendor security assessment questionnaires to a third-party.
Cons
- Lacks in SSO and delegated user administration.
- Once the training is complete, the testing environment cannot be accessed.
Customer Rating
- G2: 4.3/5
11. LogicManager
LogicManager is enterprise risk management software that helps businesses improve their performance through strong governance, risk management, and compliance. The platform identifies gaps in GDPR compliance by using a risk-based approach. It allows you to identify where you are currently non-compliant with GDPR and where you are most vulnerable to non-compliance.
Pros
- The owner can create forms without the assistance of experts.
- The tool streamlines programs by providing customized workflows.
Cons
- There is no undo feature for new users.
- Self-service import is not available in all areas.
Customer Rating
- G2: 4.4/5
12. Secureframe
Secureframe is the governance, risk, and compliance platform. It simplifies the GDPR compliance process by providing guidance at each step, ensuring that you remain compliant with European data privacy regulations. The platform monitors and configures your cloud infrastructure to ensure GDPR compliance. It monitors 100+ cloud services, including Google Cloud, AWS, and Azure.
Pros
- It provides a comprehensive overview of all processes, vendors, employees, to ensure that users are always updated on their compliance requirements.
- It integrates with major cloud providers, HR systems, identity providers, code repositories, etc.
Cons
- There are no automatic reminders for integrated services.
Customer Rating
- G2: 4.6/5
13. Alert Logic
Fortra’s Alert Logic provides comprehensive managed detection and response (MDR) for public clouds, on-premises, SaaS, and hybrid environments. The platform’s integrated threat management solution easily addresses your GDPR security requirements. It also detects applications and services that have missing or incorrect encryption settings.
Pros
- The tool offers comprehensive reporting, analytics, and visibility into the entire IT infrastructure.
- The platform has robust log collection and correlation capabilities that enable users to identify, investigate, and resolve incidents.
Cons
- Advanced search queries have a steep learning curve.
- The detection system occasionally raises false positives.
Customer Rating
- G2: 4.5/5
14. Wired Relations
Wired Relations is a GDPR privacy tool that enables you to automate and collaborate on your privacy workflow to gain customers’ trust. The platform has built-in tools that connect your work, prevent errors, and ensure consistency. It monitors the privacy operation with real-time insights. With Wired Relations, data can be linked across all aspects of your privacy workflow.
15. Vigilant Software
Vigilant Software GDPR Manager provides you with the visibility, automation, and record-keeping required to manage your core GDPR compliance activities. The platform includes 4 GDPR compliance modules – gap analysis, data breaches report, handling data subject access requests, and third-party management. The tool makes it simple to record and respond to DSARS by keeping track of how and when your organization responded. Furthermore, it makes breach reporting easier by allowing you to log incidents easily.