In the modern business world, data security and privacy have become paramount concerns for businesses of all sizes and industries. Customers, partners, and stakeholders increasingly demand transparency and assurance that their data is handled with the utmost care and security. This is where SOC 2 certification comes into play.
SOC 2 certification serves as a crucial validation that a service organization has implemented robust controls to protect sensitive data, ensuring it meets industry standards and regulatory requirements.
In our earlier blogs, we saw the process of the SOC 2 audit, how to accelerate the process of the SOC 2 audit, and everything about the SOC 2 Type II audit. In this one, we will help you differentiate between SOC 2 Type I and Type II certifications and the similarities between them. We will also help you determine the circumstances that dominate the selection of one over the other.
What is SOC 2 certification?
This certification is essential for businesses that provide services involving the storage, processing, or transmission of sensitive customer data.
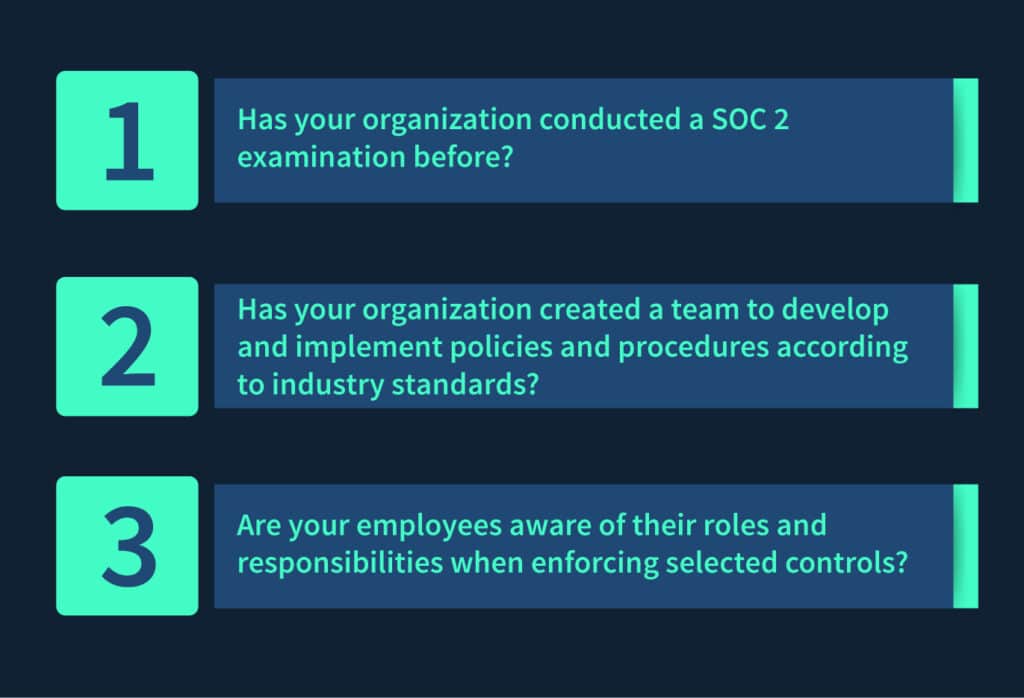
SOC 2 certification involves a rigorous audit process conducted by independent third-party auditors who evaluate a service organization’s control environment. The objective is to ensure that the organization has implemented adequate controls to protect data from unauthorized access, security breaches, and other risks.
The different types: Type I and Type II
SOC 2 Type I report:
- A SOC 2 Type 1 report evaluates the suitability of an organization’s controls as of a specific date.
- It provides a snapshot of an organization’s control environment at a single point in time.
- Type I reports are often used as a starting point for businesses looking to assess and demonstrate their commitment to security and compliance.
SOC 2 Type II report:
- A SOC 2 Type 2 report assesses the effectiveness of an organization’s controls over a period of time, typically six months or more.
- It offers a more comprehensive evaluation by verifying that controls are not only in place but also operating effectively.
- Type II reports provide a higher level of assurance to stakeholders, making them the preferred choice for businesses aiming to demonstrate a consistent commitment to security and compliance.
Why choosing the right type matters
Selecting the right type of SOC 2 report is crucial for businesses, as it directly impacts the level of assurance provided to customers, partners, and other stakeholders. Let’s compare SOC2 type 1 vs type 2 certification to know more.
- SOC 2 Type I: This report is beneficial if your organization wants to establish its commitment to security and compliance quickly. It can serve as a foundation for future Type II certification. However, it may not provide the same level of assurance as a Type II report because it only assesses controls at a specific point in time.
- SOC 2 Type II: This report is the gold standard for SOC 2 certification. It offers a more comprehensive assessment of controls over an extended period, demonstrating a sustained commitment to security and compliance. It’s often a requirement for businesses that handle sensitive data and want to win the trust of clients and partners.
Ultimately, the choice between Type I and Type II depends on your business’s needs, the expectations of your stakeholders, and the level of assurance you want to provide. In the next sections of this blog series, we’ll delve deeper into the specific criteria and processes involved in each type of SOC 2 report, helping you make an informed decision about which is right for your organization.
SOC 2 Type I certification
1. An in-depth explanation of SOC 2 Type I
SOC 2 Type I certification is the first level of certification within the SOC 2 framework. It provides a snapshot assessment of a service organization’s controls at a specific point in time, typically as of a specific date. Here’s an in-depth explanation of Type I certification:
Snapshot assessment
Firstly, Type I certification evaluates the suitability of an organization’s controls at a particular moment. It focuses on whether the controls are designed effectively to meet the specified criteria.
Report contents
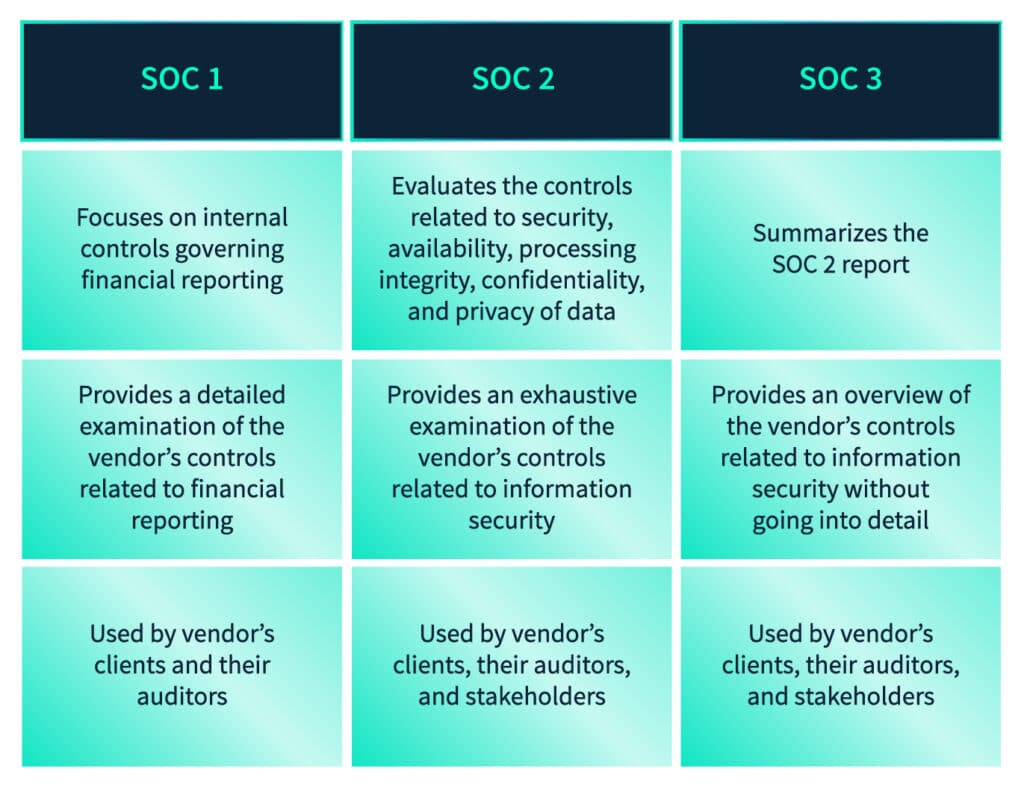
Secondly, a SOC 2 Type 1 compliance report contains a description of the service organization’s systems and controls, an assessment of whether these controls are suitably designed to meet the criteria (known as the Trust Services Criteria or TSC), and an opinion from an independent auditor.
2. Key features and benefits
Understanding the key features and benefits of SOC 2 Type 1 compliance certification is crucial for organizations considering this level of assessment. We will explore the scope, timeframe, and level of assurance it offers, helping you make an informed decision.
Scope
Type I certification assesses controls in place at a single point in time.
Objectives
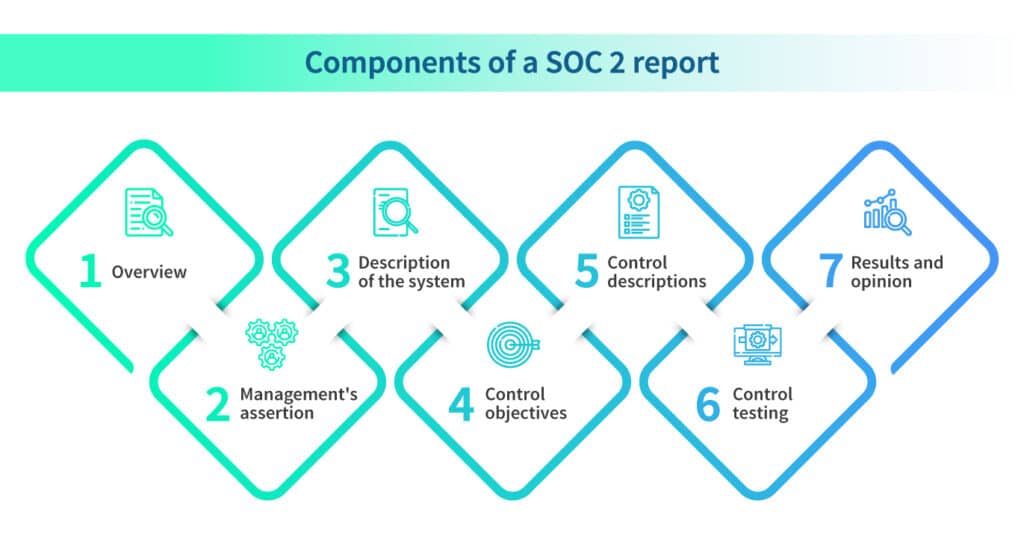
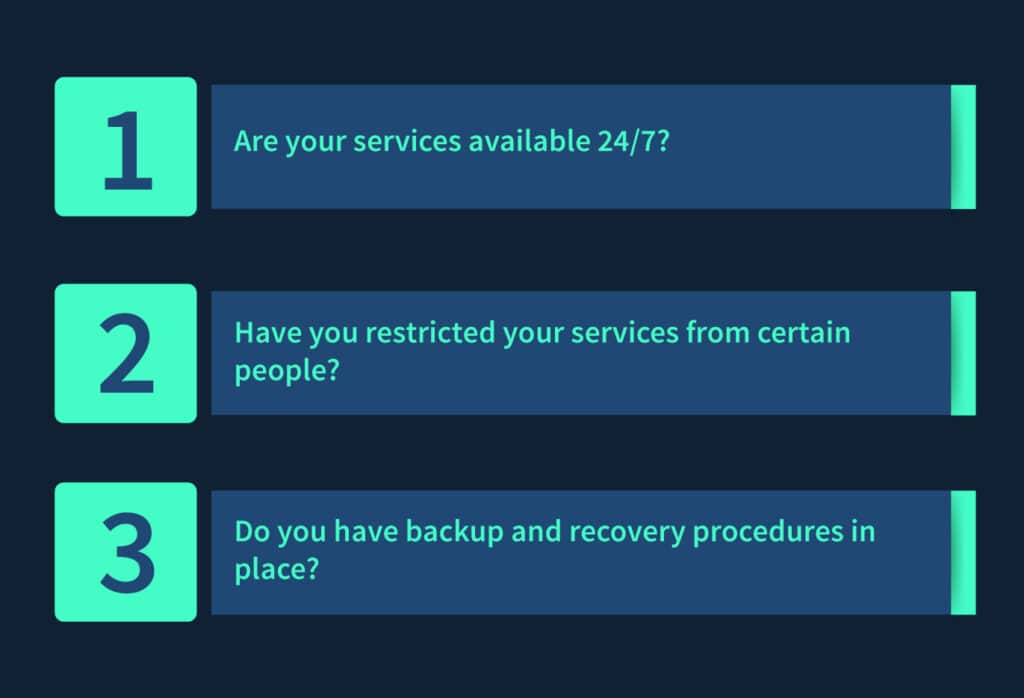
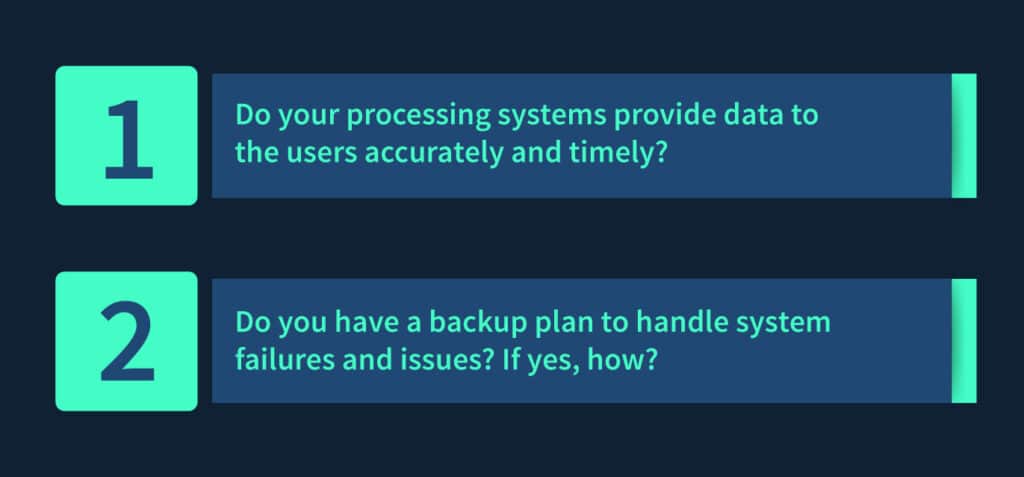
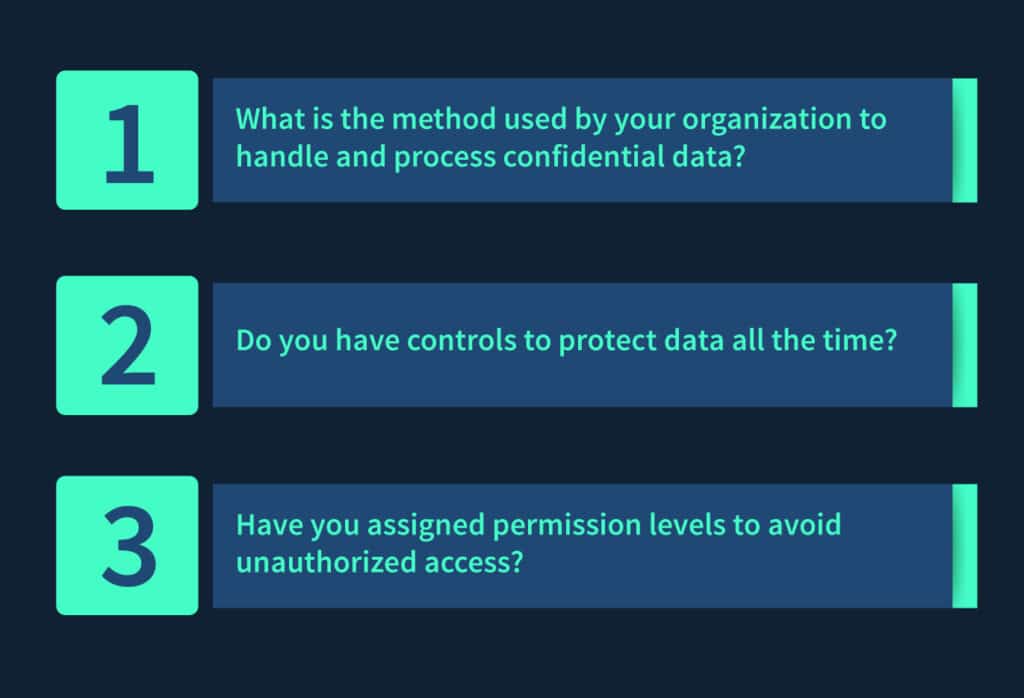
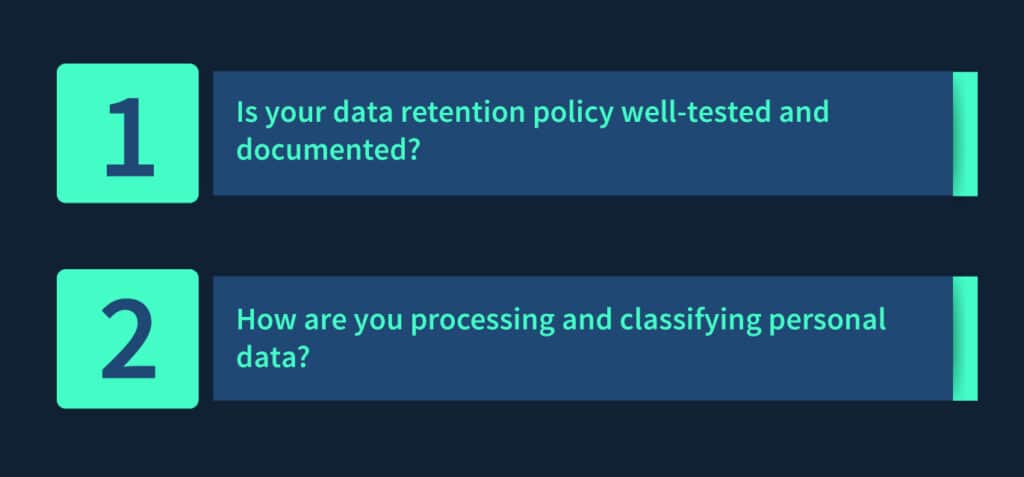
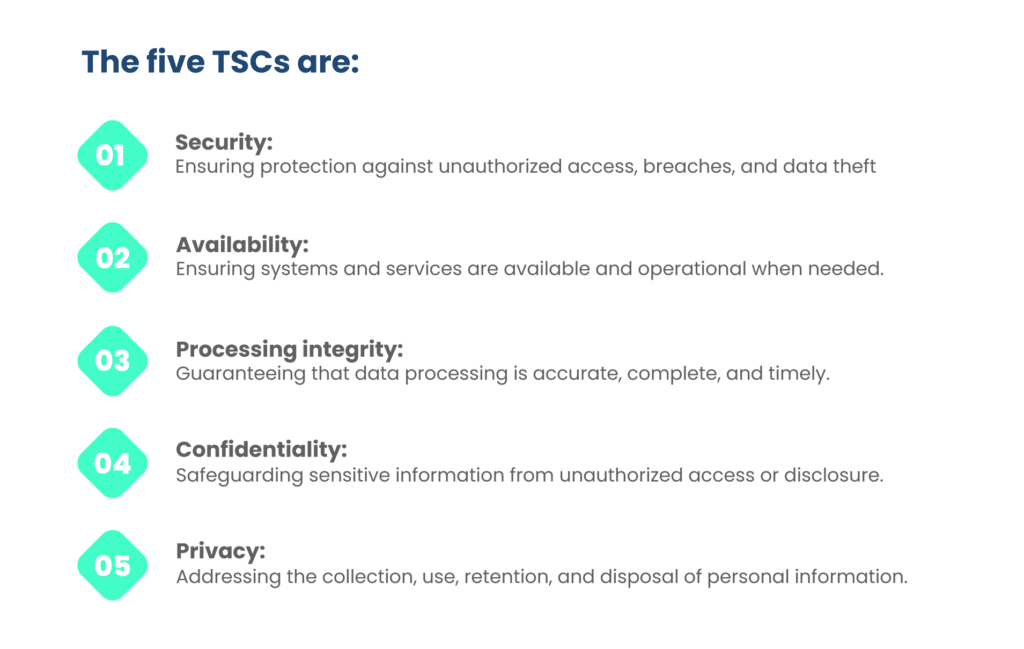
The objective is to determine whether controls are appropriately designed to meet the trust services criteria, which encompass security, availability, processing integrity, confidentiality, and privacy.
Duration
The audit process for SOC 2 Type 1 compliance certification usually covers a shorter period than Type II, focusing on the controls in place as of a specific date.
Assurance level
While Type I certification demonstrates a commitment to security and compliance, it offers a lower level of assurance compared to Type II because it doesn’t assess how controls operate over time.
3. Suitable scenarios for Type I certification
Not every business situation calls for the same level of SOC 2 certification. In this section, we will explore the scenarios where SOC 2 Type I certification is the most fitting choice, highlighting the contexts in which it provides the most value.
Initial assessment
Organizations new to SOC 2 certification may start with Type I as a foundational step to assess the suitability of their controls.
Short-term needs
Businesses with short-term contractual obligations or compliance requirements may find Type I certification sufficient to meet those demands.
Demonstrating commitment
Type 1 compliance certification can help organizations show their commitment to data security and compliance, even if they plan to pursue Type II certification in the future.
4. Real-world examples and use cases
To provide practical insights, we will present real-world examples and use cases of organizations that have leveraged SOC 2 Type I certification. These case studies will showcase how different businesses have utilized this certification to achieve their goals and enhance their security posture.
SaaS startups
A startup offering Software as a Service (SaaS) may opt for Type I certification to assure early customers of their commitment to data security while they work towards a more robust Type II certification.
Data centers
Data center providers might undergo Type I certification to demonstrate their data security controls to potential clients before entering into long-term contracts.
Short-term projects
Organizations involved in short-term projects that require compliance may choose Type I certification to meet immediate contractual obligations.
SOC 2 Type 2 compliance
1. An in-depth explanation of SOC 2 Type II
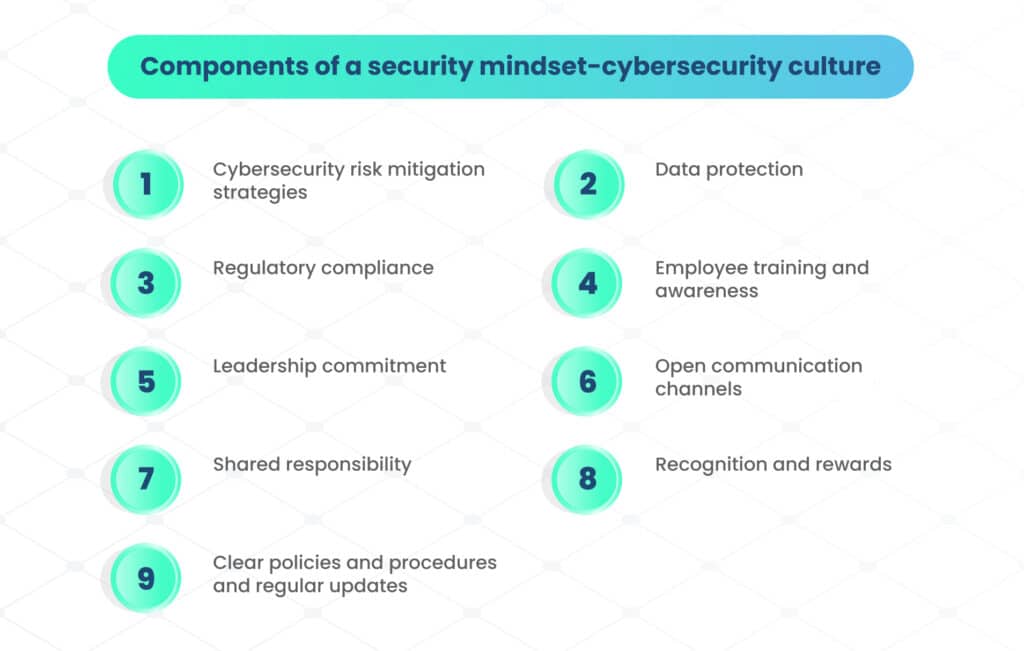
SOC 2 Type 2 is a widely recognized auditing standard developed by the American Institute of Certified Public Accountants (AICPA) to assess and report on the controls and processes of service organizations. Mainly, it specifically focuses on the security, availability, processing integrity, confidentiality, and privacy of customer data. Here’s an in-depth explanation:
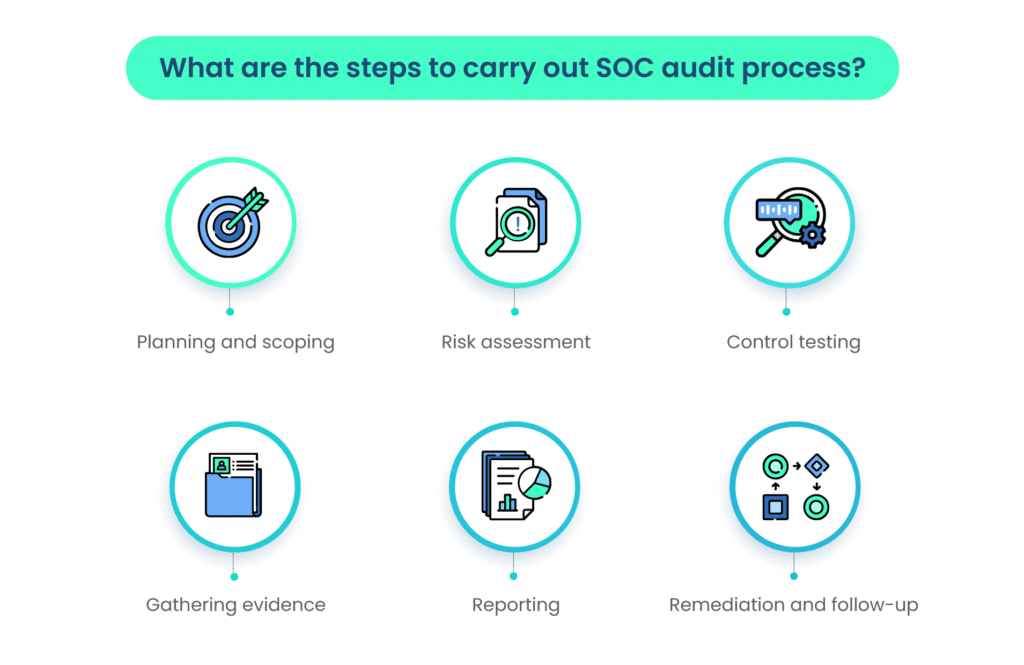
Control trust principles or criteria
SOC 2 Type 2 compliance evaluates controls related to five trust principles, called TSC, as described above.
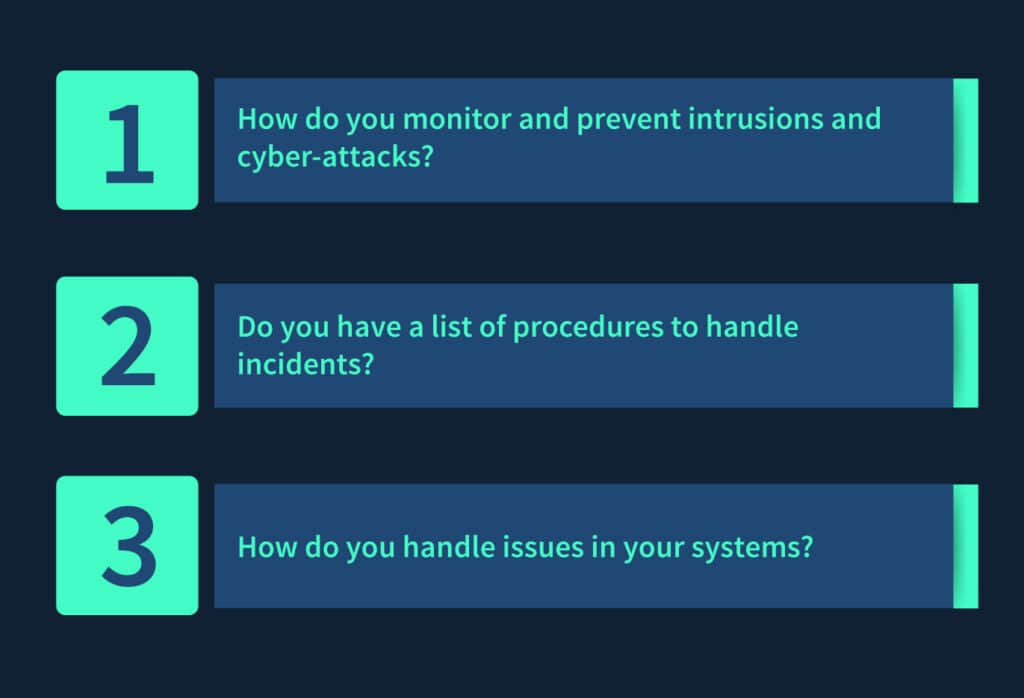
Assessment period
SOC 2 Type 2 certification involves an extended audit period, usually spanning at least six months or longer. During this time, an independent auditor assesses the effectiveness of the controls in place.
Testing of controls
Auditors conduct rigorous testing of controls over an extended period, examining not only their existence but also their operational effectiveness.
Reporting
Once the audit is complete, the service organization receives a SOC 2 Type 2 compliance report. This report includes a detailed description of the controls tested, the auditor’s findings, and an opinion on whether the controls were suitably designed and effectively operated throughout the assessment period.
2. Key features and benefits
Understanding the key features and benefits of SOC 2 Type 2 compliance certification is essential for organizations considering or currently undergoing the certification process. In this section, we will explore the scope, objectives, timeframe, and ongoing compliance requirements of SOC 2 Type II, highlighting how it offers a high level of assurance to customers and contributes to trust-building.
Scope
SOC 2 Type 2 compliance focuses on a service organization’s systems and the controls relevant to the selected trust principles.
Objectives
The primary objective is to provide assurance to customers and stakeholders that the organization’s controls are effective in safeguarding their data and ensuring service reliability.
Timeframe
The audit period for Type II certification typically covers a minimum of six months.
Ongoing Compliance: Organizations must continuously maintain and improve their controls to ensure ongoing compliance and renewal of certification.
Assurance level
SOC 2 Type II provides a high level of assurance regarding the service organization’s controls, making it a valuable trust-building tool for customers.
3. Suitable scenarios for Type II certification
SOC 2 Type II certification is suitable for service organizations, such as data centers, cloud service providers, SaaS companies, and managed service providers, where data security, availability, and processing integrity are critical. It is often sought by organizations handling sensitive customer information or providing critical infrastructure services.
4. Real-world Examples and Use Cases
Real-world examples and use cases provide tangible evidence of the benefits and applications of SOC 2 Type II certification. In this section, we will explore instances where prominent organizations have obtained Type II certification, showcasing its practical relevance in ensuring data security, availability, and integrity for various industries and service providers.
Cloud service providers
Companies like Amazon Web Services (AWS) and Microsoft Azure obtain SOC 2 Type II certifications to assure customers that their cloud infrastructure meets stringent security and availability standards.
Data centers
Colocation data centers, like Equinix, undergo SOC 2 Type II audits to demonstrate their commitment to protecting customer data and ensuring uninterrupted service.
SaaS providers
SaaS companies, such as Salesforce, seek SOC 2 Type II certification to give their clients confidence in the security and privacy of their data stored and processed in the cloud.
Managed service providers
Organizations offering managed IT services, like Rackspace, use SOC 2 Type II certification to prove their commitment to maintaining the integrity and availability of their clients’ systems.
SOC 2 Type 1 vs Type 2
The difference between SOC 2 type 1 and type 2 reports is shown in the table below:
| Aspect | SOC 2 Type 1 | SOC 2 Type 2 |
| Objective | Assesses controls at a specific point in time to provide assurance about their design and implementation. | Assesses controls over a period (typically 6-12 months) to provide assurance about their design, implementation, and effectiveness. |
| Timeframe | Snapshot assessment, usually for a single date. | Continuous assessment over a defined period, typically months. |
| SOC 2 Type 2 report content | Provides an opinion on the suitability of control design as of a specific date. | Provides an opinion on the suitability of control design, implementation, and operating effectiveness over a specified period. |
| Focus | Emphasizes control design and whether controls are in place. | Emphasizes control design, implementation, and how controls operate over time. |
| Use cases | Typically used for initial assessments or when a client or partner wants to evaluate control design. | Often used when ongoing monitoring and assurance are required, especially for critical services or sensitive data handling. |
| Frequency | Typically conducted annually or as needed. | Conducted at least annually but can cover a more extended period for a deeper evaluation. |
| Assurance level | Lower level of assurance, as it doesn’t assess control effectiveness. | Higher level of assurance, as it assesses control design, implementation, and effectiveness. |
| Cost and effort | Generally less costly and less time-consuming than Type 2. | Requires more effort, resources, and time due to the continuous assessment. |
| Client confidence | Provides some level of assurance but may not be sufficient for clients with stringent security requirements. | Provides a higher level of assurance and is often preferred by clients with strict security demands. |
| Continuous improvement | Limited insights into ongoing control effectiveness. | Provides valuable insights for continuous improvement by identifying control weaknesses and trends. |
SOC 2 Type 1 vs Type 2 – How to decide?
In the realm of data security and compliance, the choice between SOC 2 Type I and Type II certification is pivotal. To aid this decision, we’ll explore key factors: industry standards, client expectations, regulatory compliance, budget considerations, and risk tolerance. Each factor plays a vital role in guiding you toward the right certification path, aligning with your organization’s specific needs and long-term goals. So, let’s compare SOC 2 type 2 vs type 1.
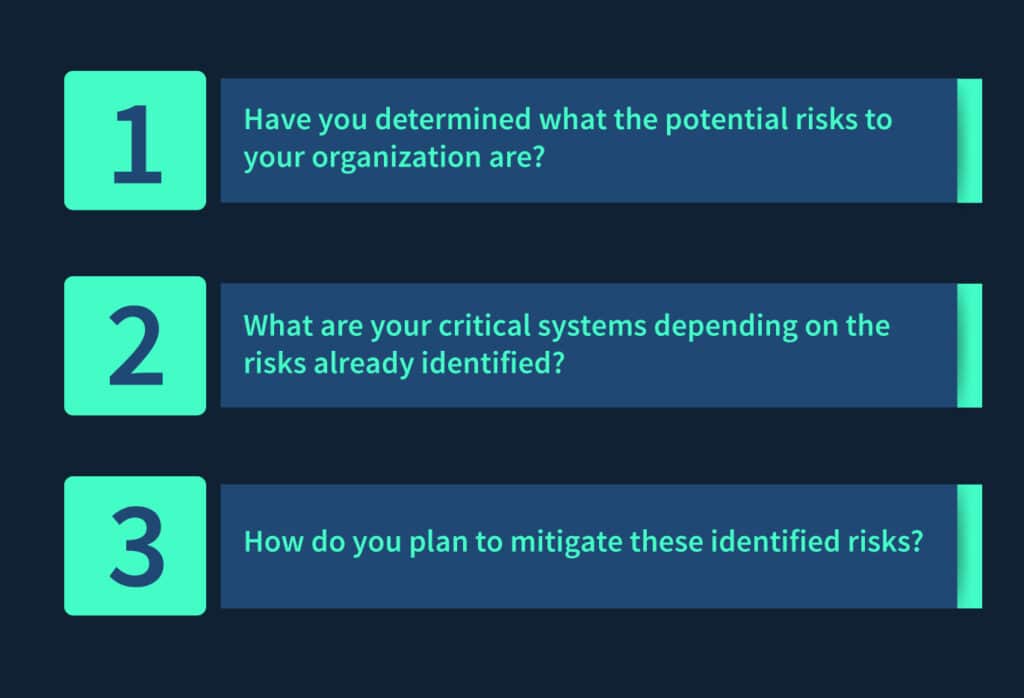
1. Assessing business needs
To make an informed decision between SOC 2 Type I and Type II certification, it’s crucial to begin by assessing your organization’s business needs.
Industry standards
- Consider the specific standards and best practices within your industry. Some sectors may have stringent requirements for data security and privacy that align with SOC 2 Type II certification.
- Evaluate whether SOC 2 certification is common or expected in your industry. If it’s a standard practice, it may be necessary to remain competitive.
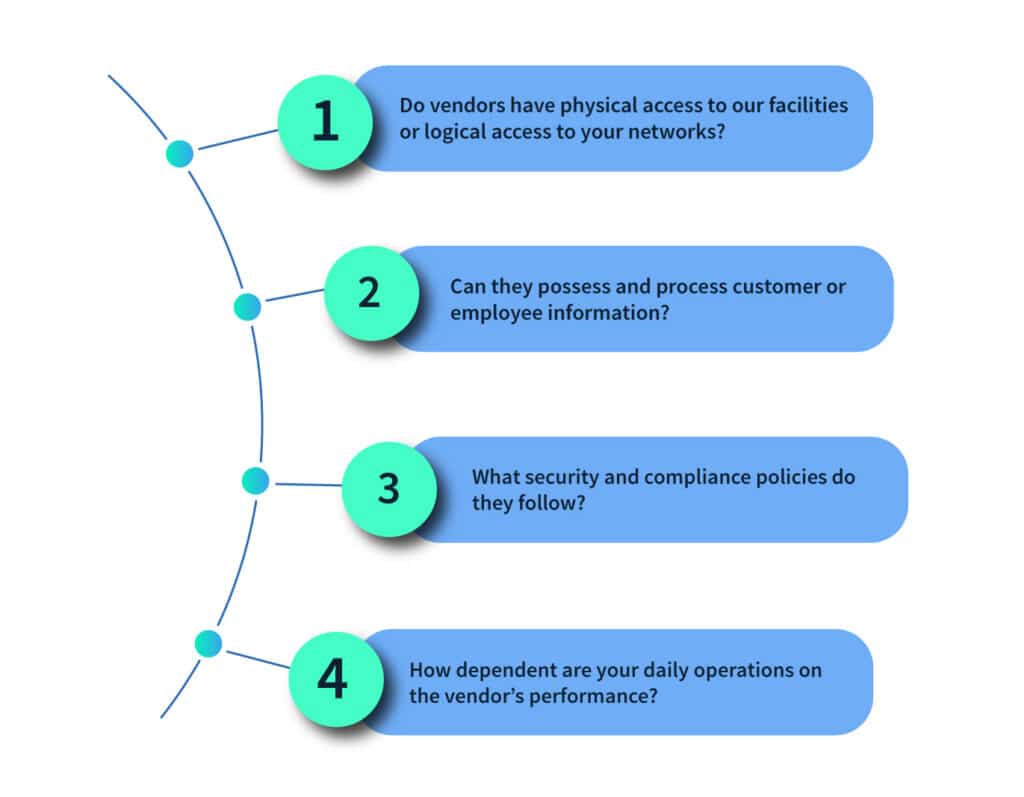
Client and stakeholder expectations
- Engage with your clients and stakeholders to understand their expectations regarding security and compliance.
- Assess whether your clients require SOC 2 reports, and if so, which type (Type I or Type II) they prefer or mandate. Aligning with client expectations can be crucial for business relationships.
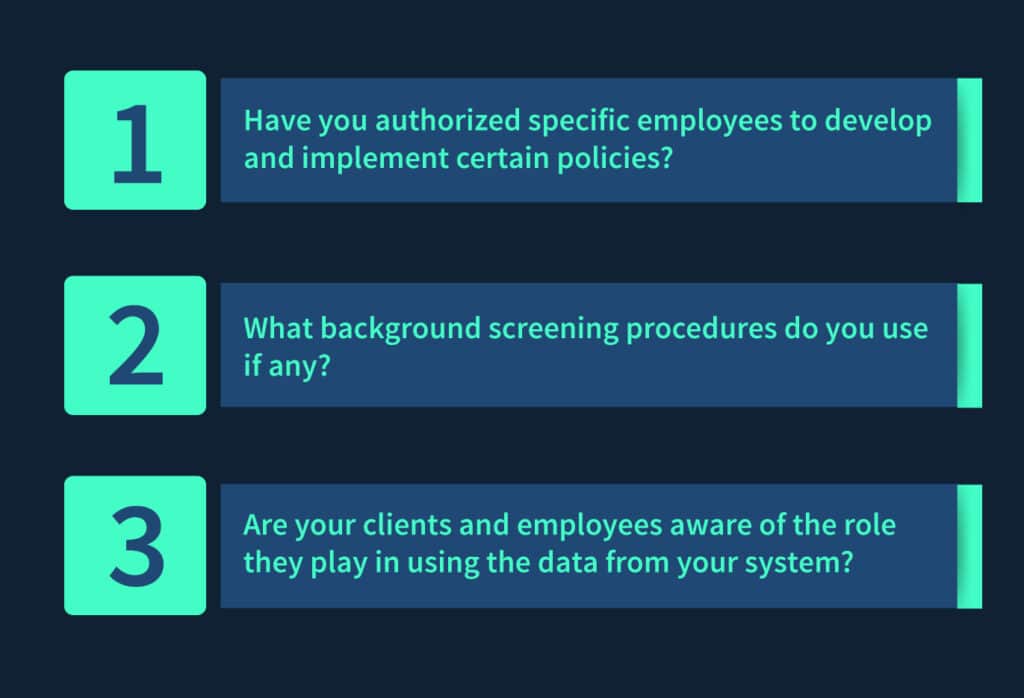
2. Regulatory compliance
Ensuring compliance with relevant regulations is a cornerstone of any certification decision, including SOC 2 Type I vs. Type II.
Meeting legal requirements
- Investigate the legal and regulatory requirements relevant to your industry and geographic location. Plus, some regulations may specifically require SOC 2 certification, and others may have broader compliance requirements.
- Ensure that your chosen SOC 2 certification aligns with and helps fulfill your legal obligations.
Future-proofing your compliance efforts
- Consider the potential for future regulatory changes. SOC 2 Type II, with its focus on ongoing control effectiveness, can provide a more robust compliance framework that adapts to evolving regulations.
- Think about how your compliance efforts today can help you stay compliant with future requirements.
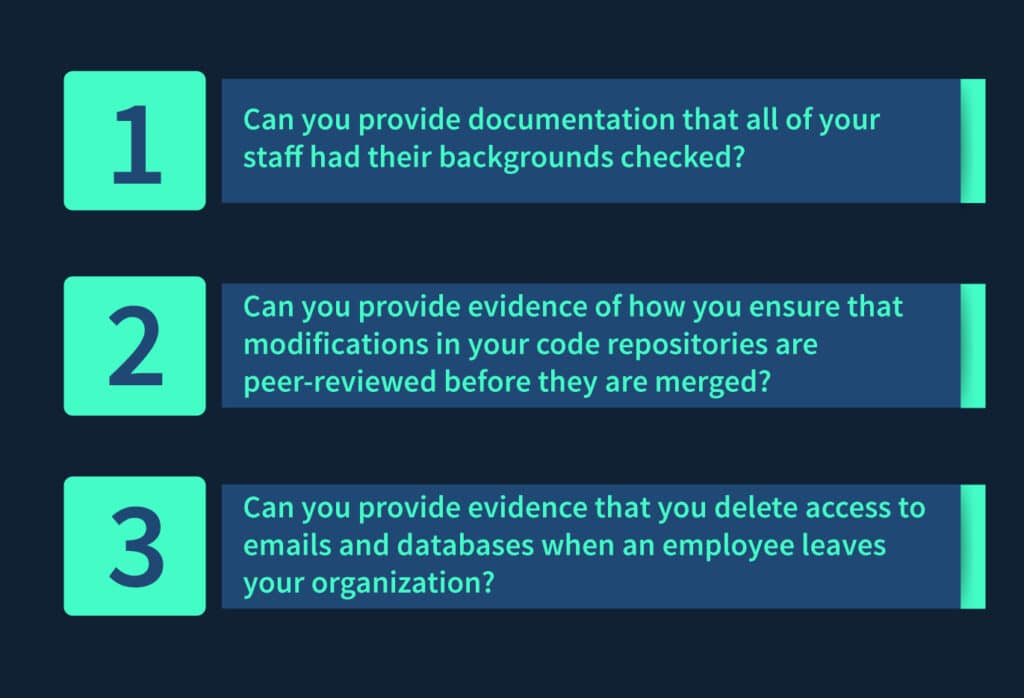
3. Budget and resource allocation
Budget considerations and resource allocation are pivotal factors to weigh when determining the most suitable SOC 2 certification type for your organization.
- Assess your budget and resource constraints. SOC 2 Type II certification typically requires more time, effort, and financial investment than Type I.
- Consider whether your organization can allocate the necessary resources for a Type II audit, including staffing, technology, and external audit fees.
4. Risk Tolerance
Understanding your organization’s risk tolerance is fundamental in choosing between SOC 2 Type I and Type II certification, as it directly impacts the level of assurance provided.
- Evaluate your organization’s risk tolerance. SOC 2 Type II provides a higher level of assurance due to its assessment of controls over an extended period.
- If your organization has a lower risk tolerance and wants to minimize the risk of control failures, Type II may be the better choice.
To sum up
In summary, choosing between SOC 2 type 1 vs SOC 2 type 2 certification depends on your organization’s specific needs, industry standards, client expectations, regulatory compliance, budget, and risk tolerance.
Type I is suitable for initial assessments and short-term needs, while Type II offers continuous assurance and is ideal for critical services or strict security requirements. Consider these factors to make an informed decision that aligns with your goals: safeguarding data and building trust in today’s data-centric business landscape.
Ready to secure your data and earn trust with SOC 2 compliance? Connect with Scrut today and take the first step toward safeguarding your organization’s sensitive information. Get started now!
FAQs
SOC 2 compliance is not mandatory for all businesses, but it may be required or expected in certain industries or by specific clients. It depends on your industry, regulatory environment, and the contractual obligations you have with clients or partners.
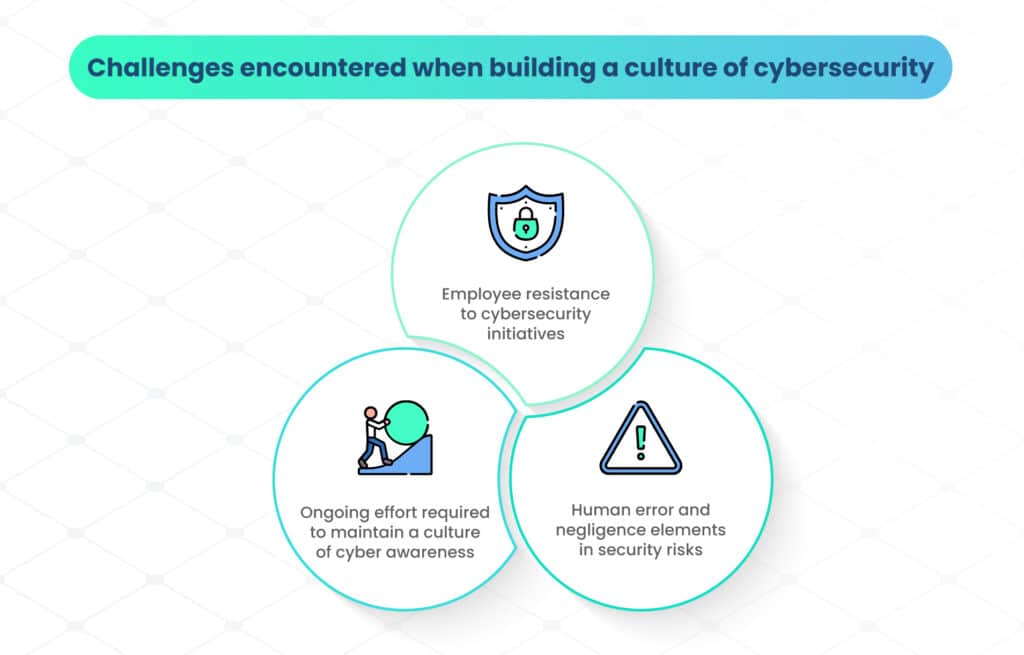
Common challenges include identifying and implementing necessary controls, ensuring consistent control operation over time, and navigating the audit process. Resource allocation and documentation can also be challenging aspects.
When selecting an auditor or assessor, consider their experience, reputation, industry knowledge, and their ability to communicate effectively with your organization. References and referrals can also be helpful in making the right choice.