The New York Department of Financial Services (NYDFS) enforced cybersecurity regulations for the financial sector effective March 1, 2017, granting covered entities a 180-day compliance period.
These regulations extend to banks, insurance companies, consumer lenders, and money transmitters, mandating encryption of data at rest, defined under 23 NYCRR 500.
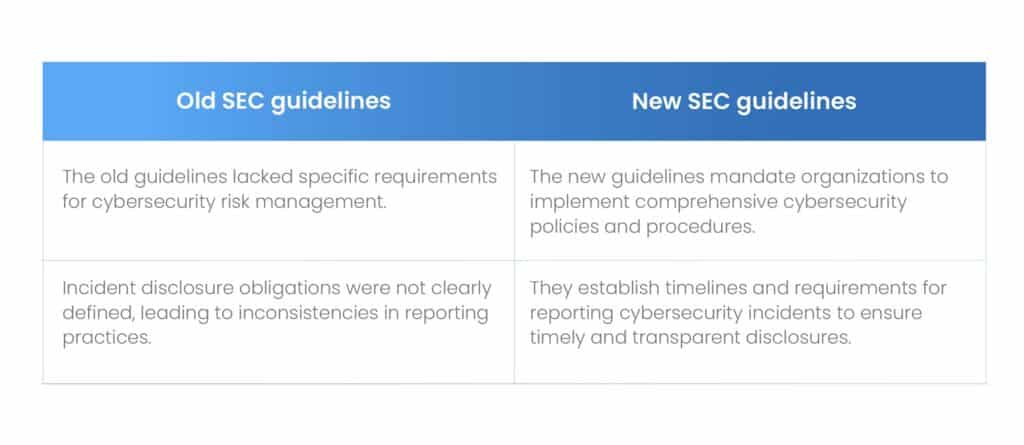
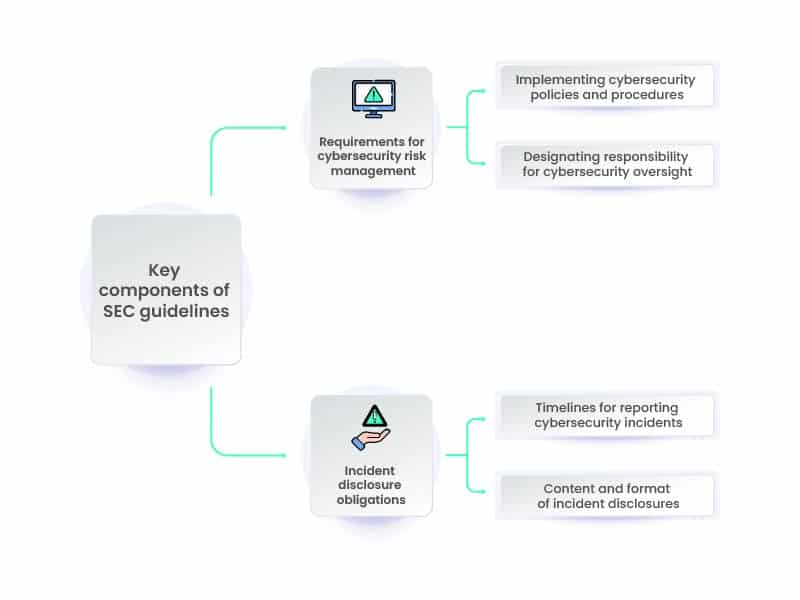
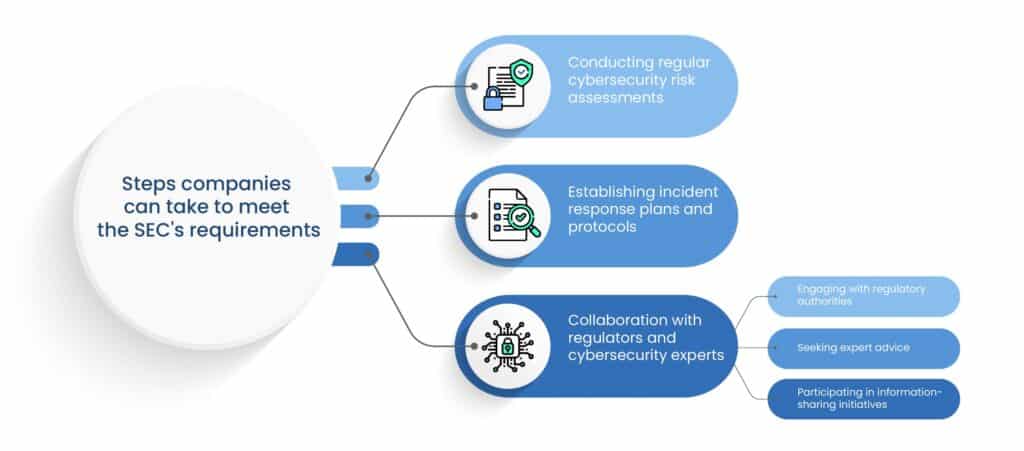
In addition to the NYDFS regulations, financial institutions must also adhere to the SEC’s new guidelines for cybersecurity management and incident disclosure, further emphasizing the critical importance of robust cybersecurity measures in the financial sector.
Compliance with this directive necessitates careful attention to detail and adherence to specific steps outlined below:
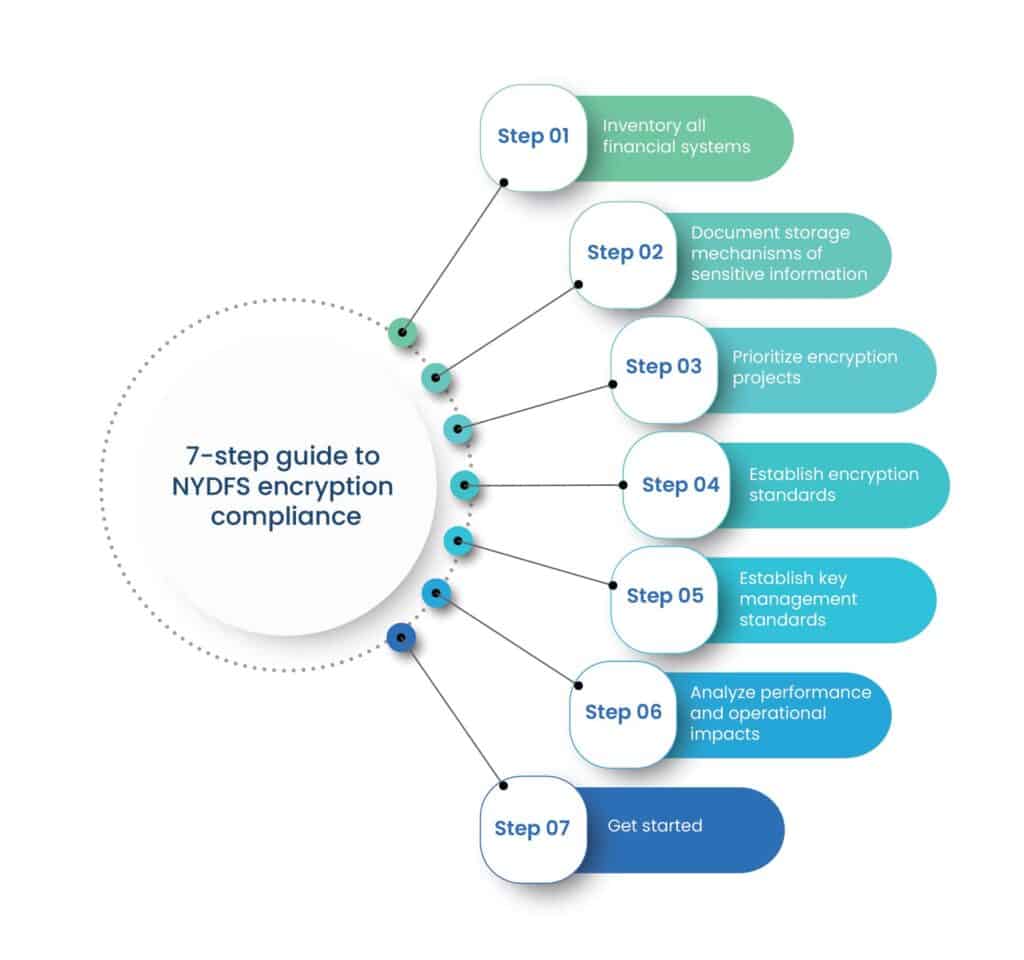
1. Inventory all financial systems
Conduct a thorough audit of all IT systems within the organization that handle financial data. This includes databases, applications, servers, and any other systems where financial information may be stored or processed. The goal is to ensure complete visibility into all systems that need to be secured and made compliant with encryption requirements.
2. Document storage mechanisms of sensitive information
Document the specific storage mechanisms used for Non-Public Information (NPI) within each system identified in the inventory.
This documentation should include details such as:
- The types of data stored,
- The locations of the data within the system, and
- The encryption status (if any).
This step is crucial for regulatory compliance and for planning the implementation of encryption measures.
3. Prioritize encryption projects
Prioritize systems and applications for encryption based on a risk-based approach.
Consider factors such as:
- The sensitivity of the data stored,
- The volume of data,
- The risk of exposure,
- Compliance obligations (such as NYDFS requirements), and
- The potential operational impact of implementing encryption measures.
This helps allocate resources effectively and focus on securing the most critical assets first.
4. Establish encryption standards
Adopt robust encryption standards to safeguard data at rest. NIST-compliant, 256-bit AES encryption is widely recognized as a secure and defensible encryption strategy.
Ensure that encryption measures are implemented consistently across major operating systems used within the organization.
5. Establish key management standards
Proper key management is essential for maintaining the integrity and confidentiality of encrypted data.
- Implement a secure key management system to protect encryption keys effectively.
- Ensure compliance with standards such as FIPS 140-2.
- Utilize protocols like the Key Management Interoperability Protocol (KMIP) for interoperability and security.
6. Analyze performance and operational impacts
Conduct a thorough analysis of the performance and operational impacts of implementing encryption measures.
To anticipate any potential challenges or bottlenecks, assess factors such as:
- CPU usage,
- backup procedures,
- storage requirements, and
- overall system performance
This analysis helps in optimizing encryption implementation and minimizing disruptions to business operations.
7. Get started
Overcome potential barriers and initiate encryption projects. Secure commitment from senior management, allocate adequate IT resources, and ensure alignment with organizational objectives.
Begin implementation with a clear plan and timeline, focusing on achieving compliance with NYDFS encryption requirements and enhancing the organization’s cybersecurity posture.
NYDFS cybersecurity regulation compliance challenges
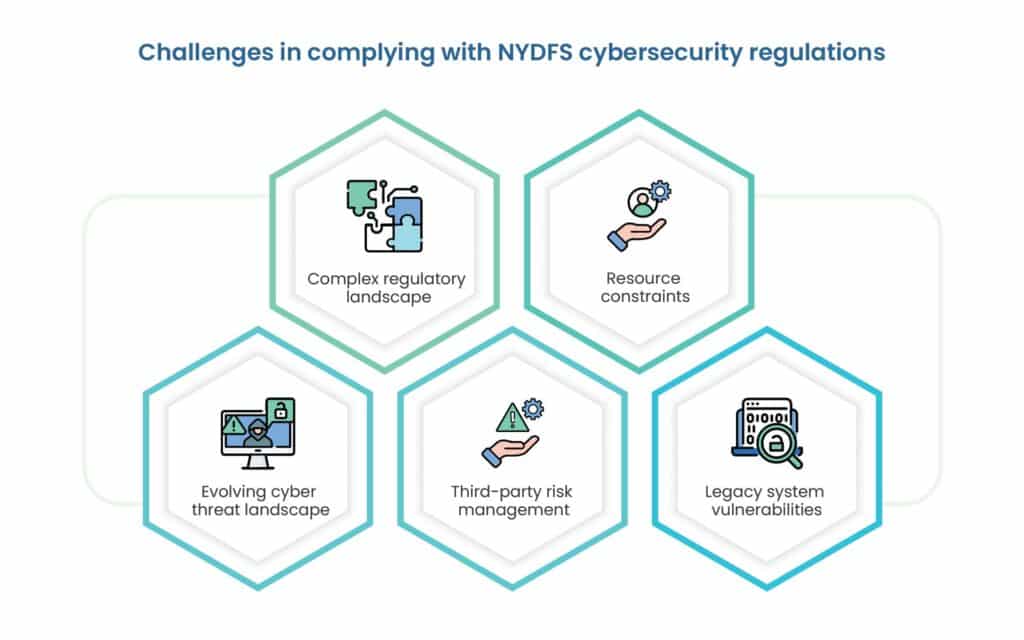
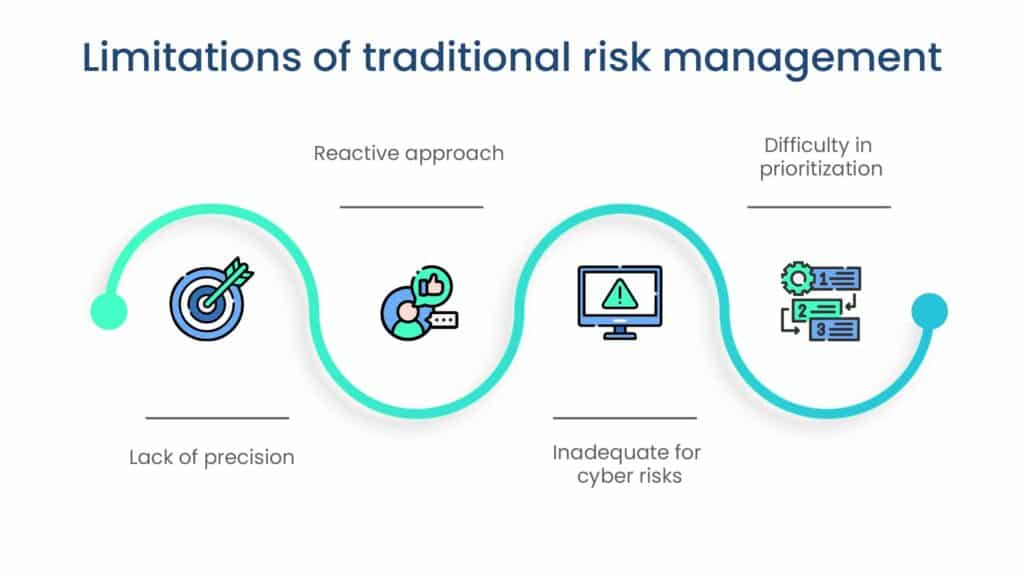
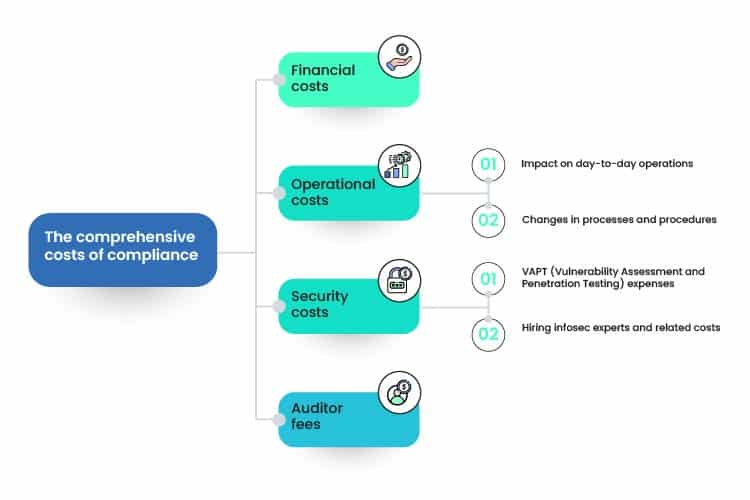
Complying with NYDFS cybersecurity regulation can pose challenges for financial institutions, including resource constraints, technology limitations, and evolving cyber threats.
1. Complex regulatory landscape
Financial institutions operating in New York State encounter a complex regulatory landscape characterized by overlapping cybersecurity regulations and compliance requirements. Navigating these regulations while maintaining compliance with NYDFS cybersecurity regulations poses a significant challenge for organizations.
This necessitates:
- Thorough understanding of regulatory obligations
- Diligent compliance efforts
2. Resource constraints
Resource constraints, including limited budgets, personnel shortages, and competing priorities, present formidable challenges for financial institutions striving to achieve compliance with NYDFS cybersecurity regulation.
3. Evolving cyber threat landscape
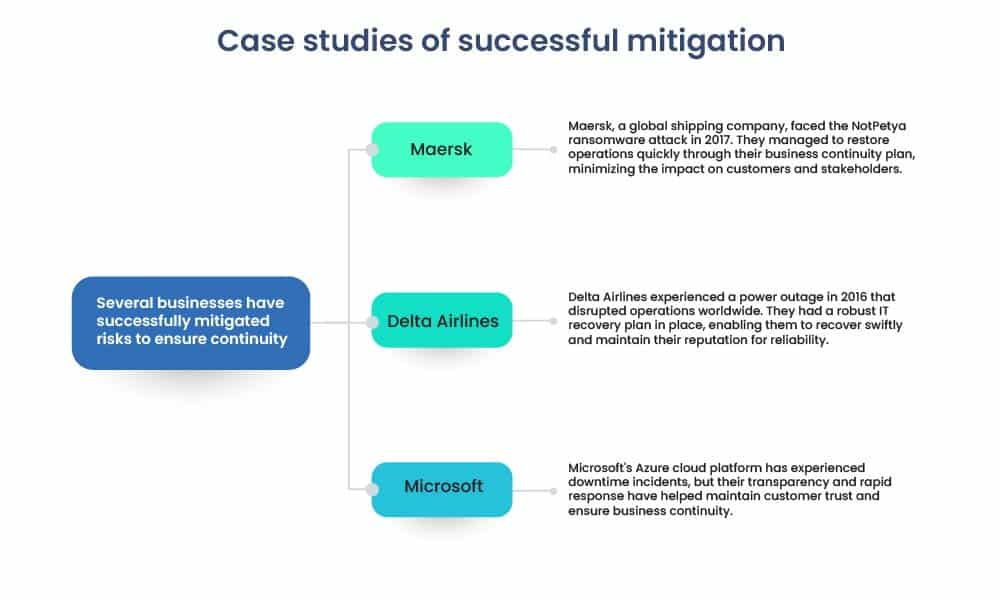
The dynamic and evolving nature of the cyber threat landscape poses ongoing challenges for financial institutions in mitigating cyber risks and maintaining compliance with NYDFS cybersecurity regulations.
Adversarial tactics continue to evolve, with cybercriminals employing increasingly sophisticated techniques to exploit vulnerabilities and evade detection.

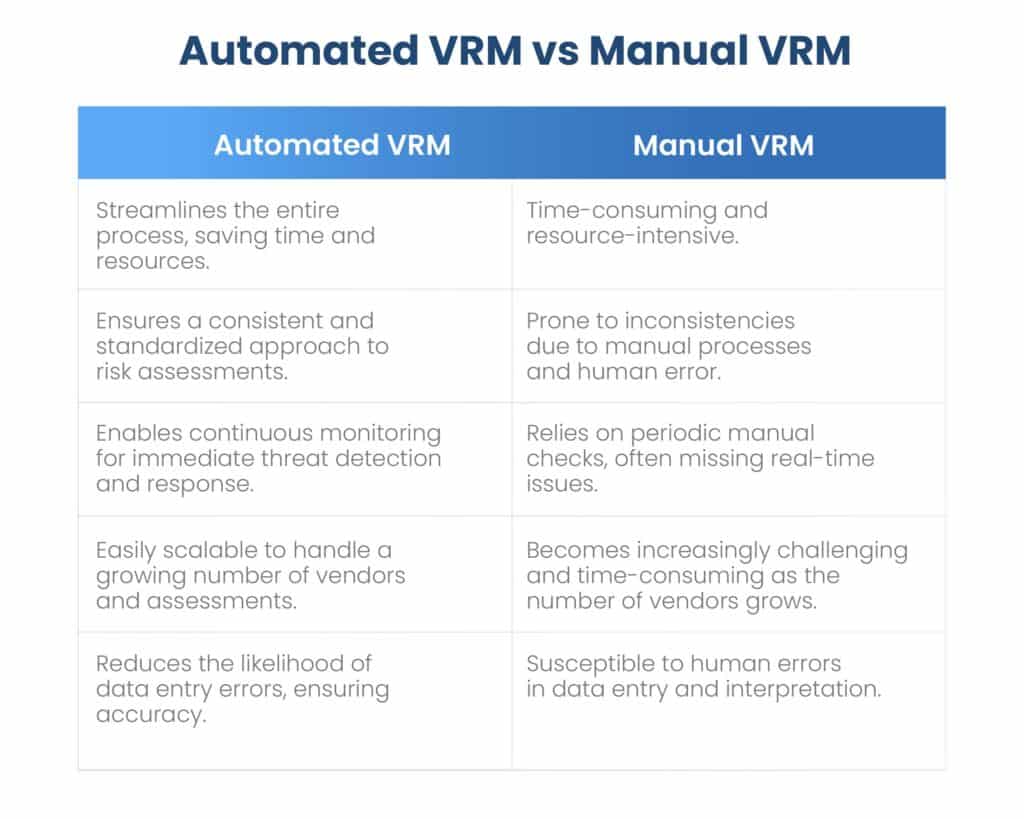
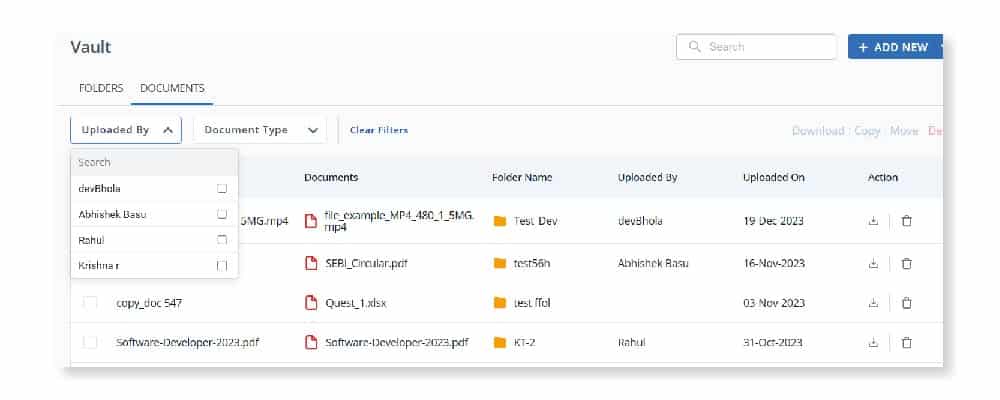
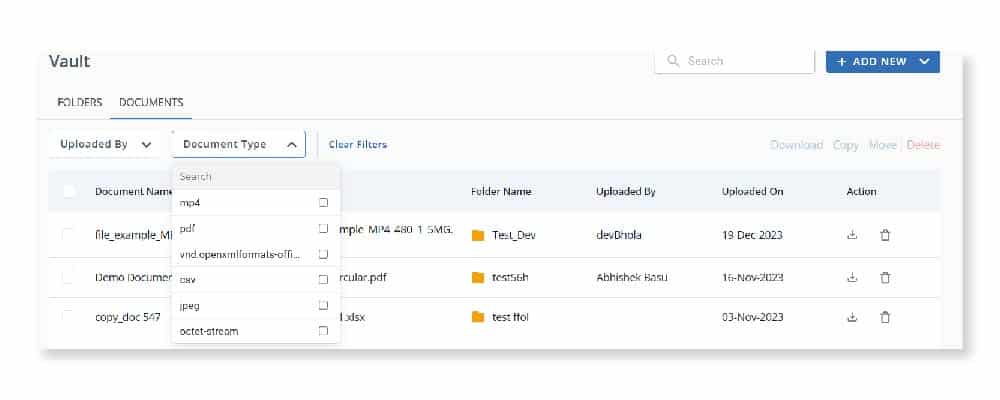
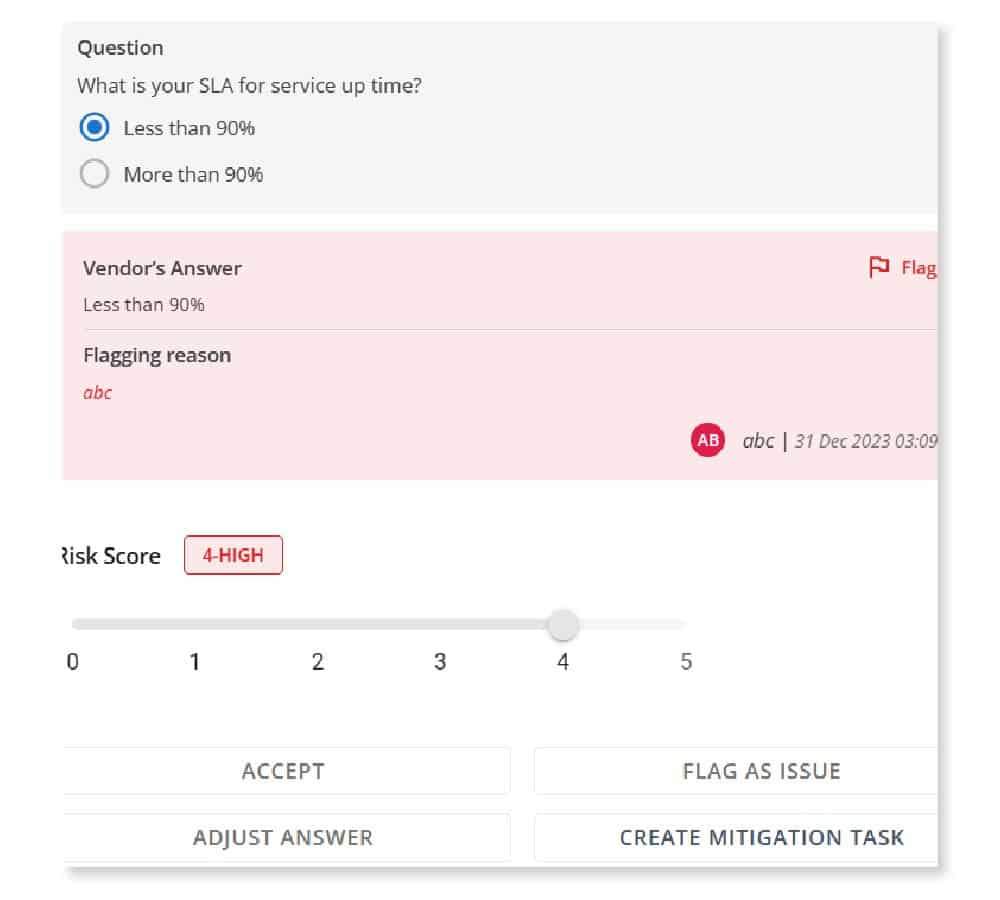
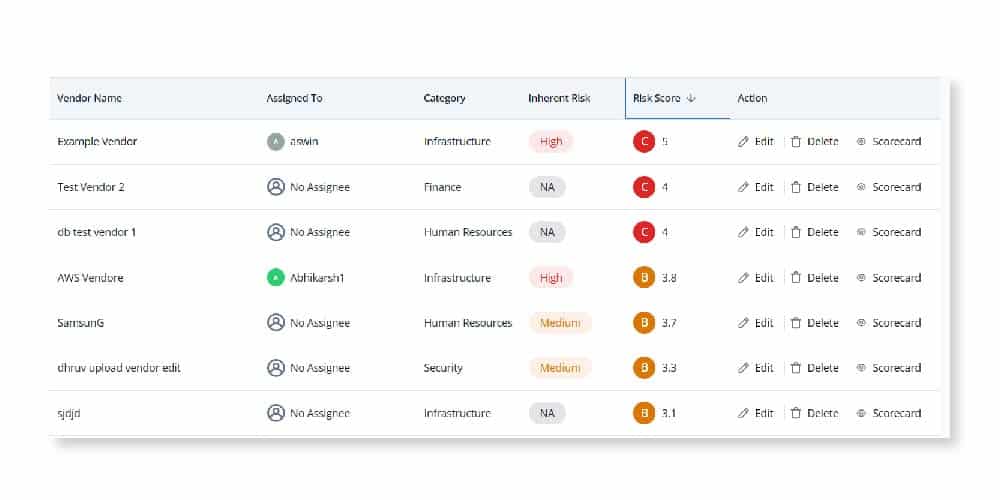
4. Third-party risk management
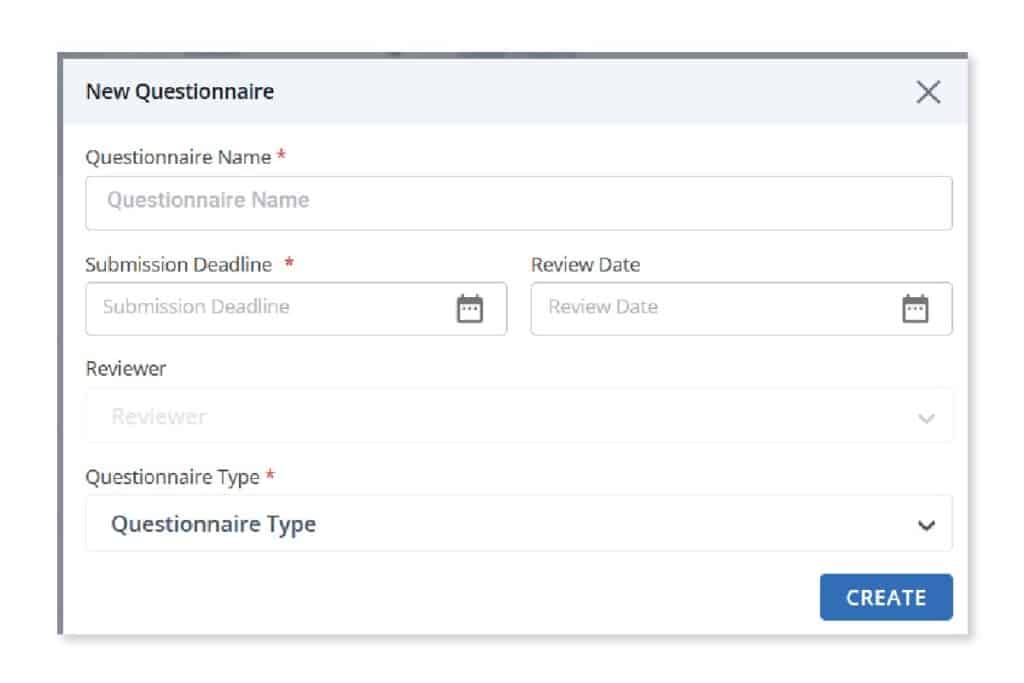
Managing third-party risks presents a significant compliance challenge for financial institutions subject to NYDFS cybersecurity regulation. The interconnected nature of the financial services industry exposes organizations to cybersecurity risks associated with third-party vendors and service providers.
To mitigate third-party risks and maintain compliance, organizations must:
- Establish robust vendor risk management programs,
- Conduct thorough due diligence, and
- Implement contractual safeguards
5. Legacy system vulnerabilities
Legacy IT systems and infrastructure pose inherent cybersecurity vulnerabilities for financial institutions, complicating compliance efforts with NYDFS cybersecurity regulations.
Outdated software, unsupported hardware, and legacy applications may lack essential security features and receive limited or no vendor support, increasing the risk of cyber threats and regulatory non-compliance. Implementing strategies to modernize legacy systems, such as phased upgrades, virtualization, and cloud migration, can help address these vulnerabilities and enhance cybersecurity posture.
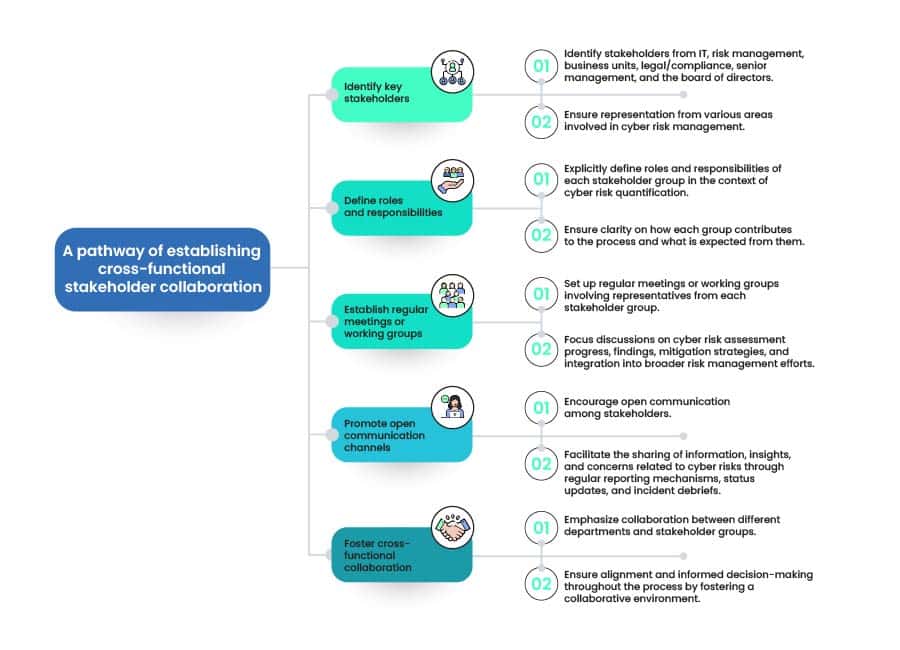
| To overcome these challenges, organizations should consider implementing best practices such as:Investing in advanced cybersecurity technologies and threat intelligence capabilities.Enhancing employee training and awareness programs to promote a culture of cybersecurity awareness.Collaborating with industry peers and third-party service providers to share cybersecurity best practices and threat intelligence.Engaging with regulators and industry associations to stay informed about emerging cybersecurity risks and regulatory developments. |
Strategies for effective compliance implementation

- Establishing a Compliance Framework
- Develop a comprehensive framework aligning policies, procedures, and controls with industry best practices and regulatory guidelines.
- Ensure systematic coverage of cybersecurity measures to meet NYDFS regulation requirements effectively.
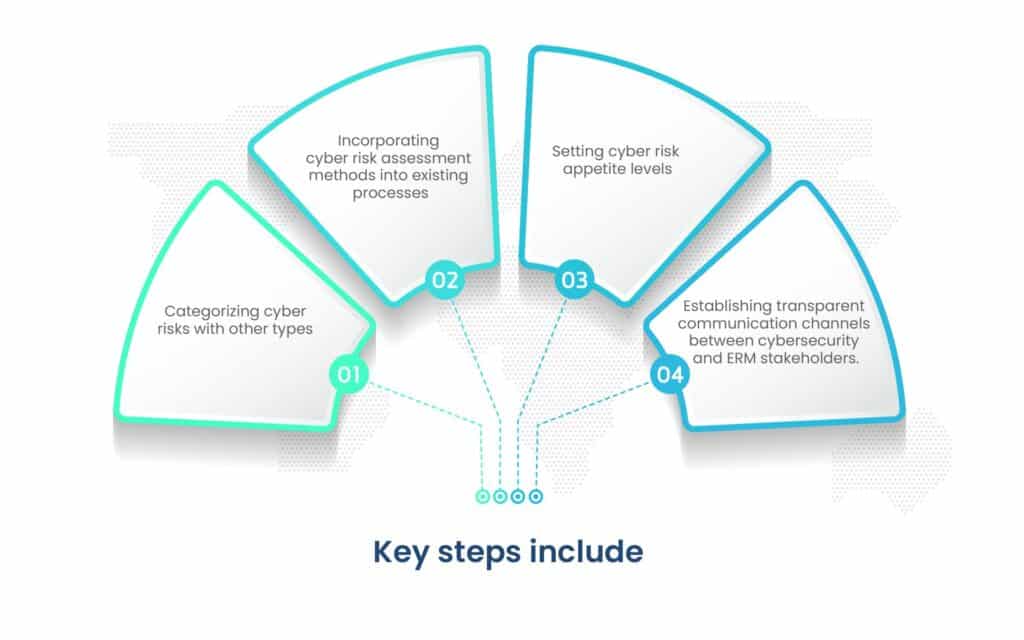
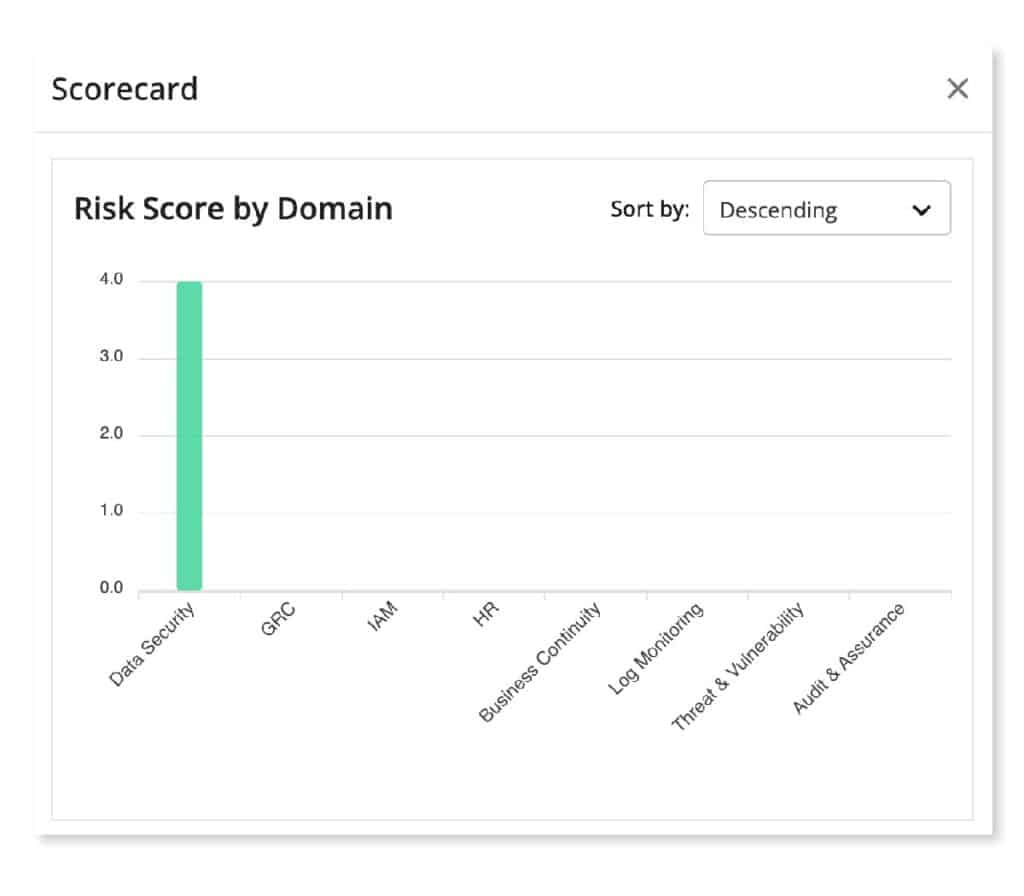
- Conducting Risk Assessments
- Identify, evaluate, and prioritize cybersecurity risks through regular risk assessments.
- Gain insights into vulnerabilities and areas for improvement to inform decision-making and resource allocation.
- Implementing Security Controls
- Deploy technical, administrative, and physical controls such as access controls, encryption protocols, and intrusion detection systems.
- Create multiple layers of security to prevent unauthorized access and protect against cyber threats.
- Enhancing Incident Response Capabilities
- Develop and test incident response plans for detection, notification, containment, eradication, and recovery.
- Regularly review, update, and communicate plans to ensure readiness to address cybersecurity incidents effectively.
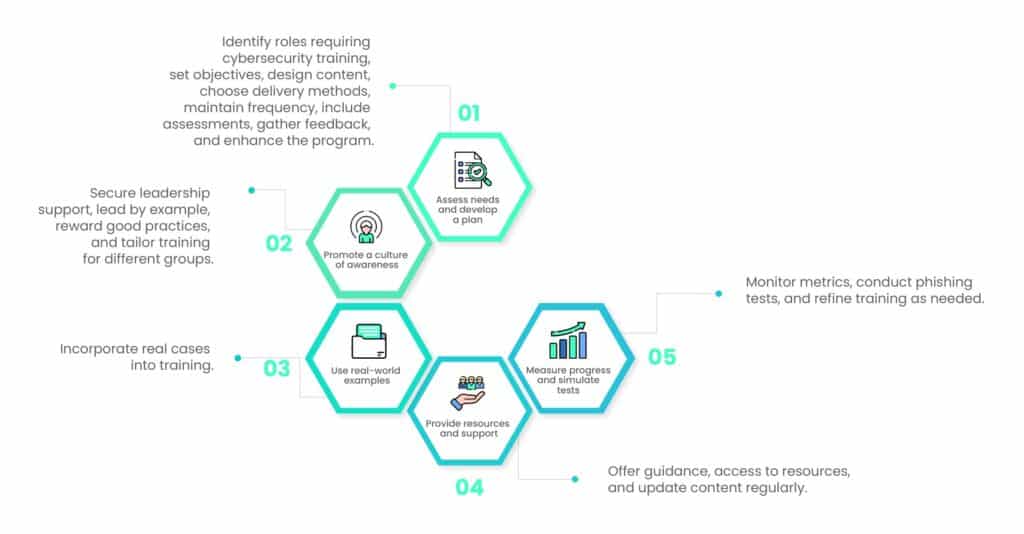
- Fostering a Culture of Cybersecurity Awareness
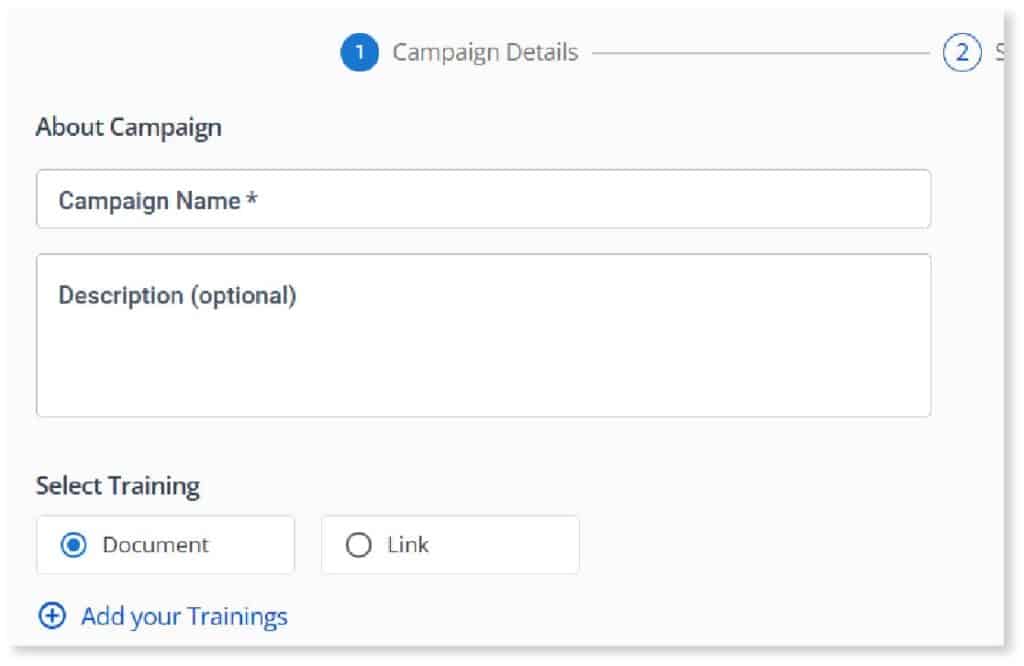
- Invest in employee training, awareness programs, and security awareness campaigns.
- Educate staff about cybersecurity best practices, policies, and procedures to promote vigilance and accountability.
- Engaging in Continuous Monitoring and Improvement
- Implement robust monitoring mechanisms, security controls, and performance metrics.
- Analyze security events, incident reports, and compliance metrics to identify areas for enhancement and drive continuous improvement.
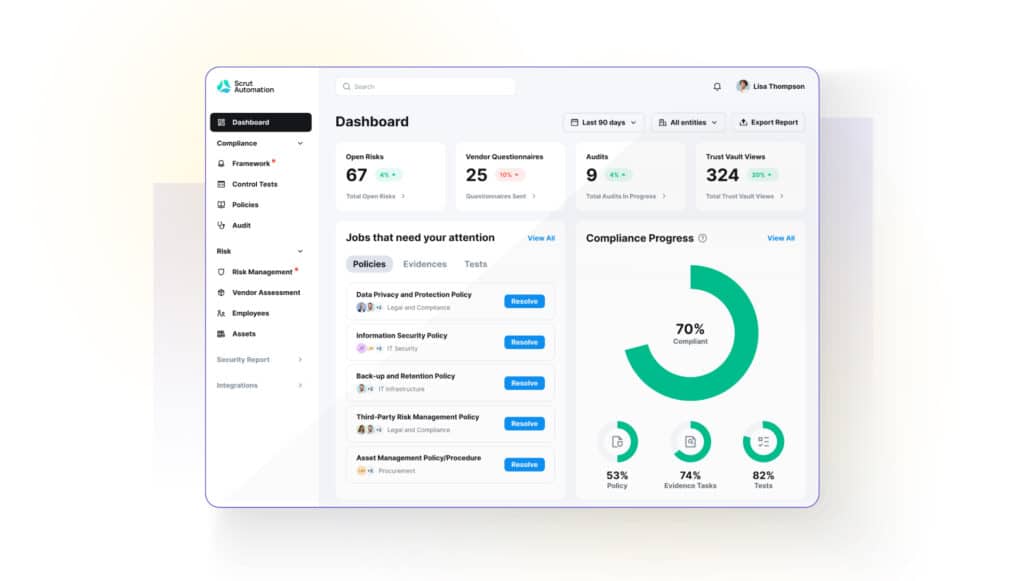
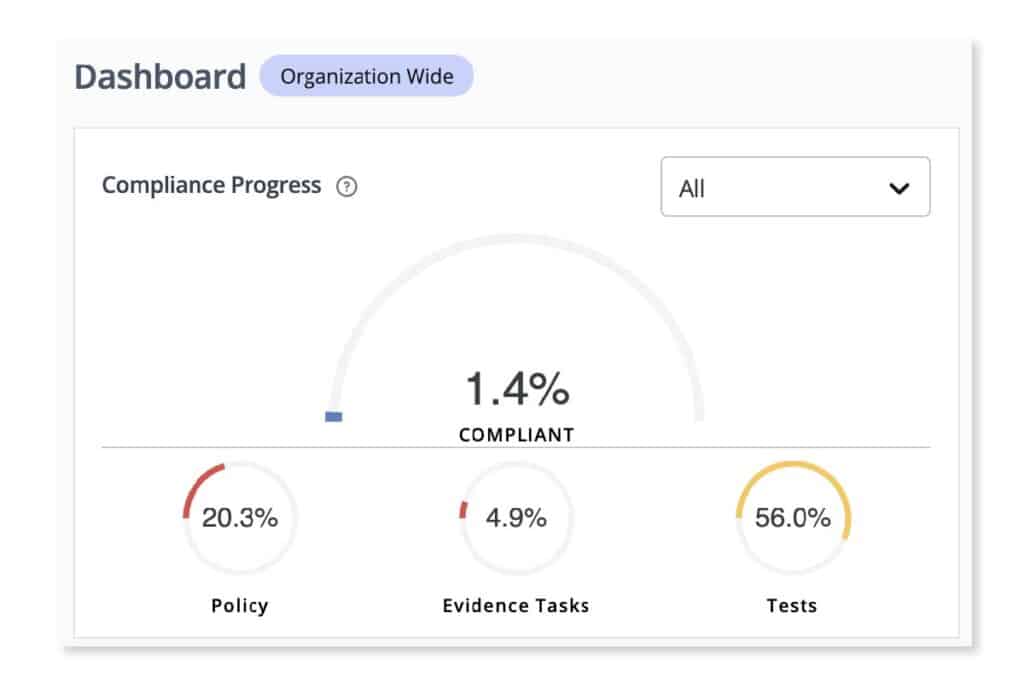
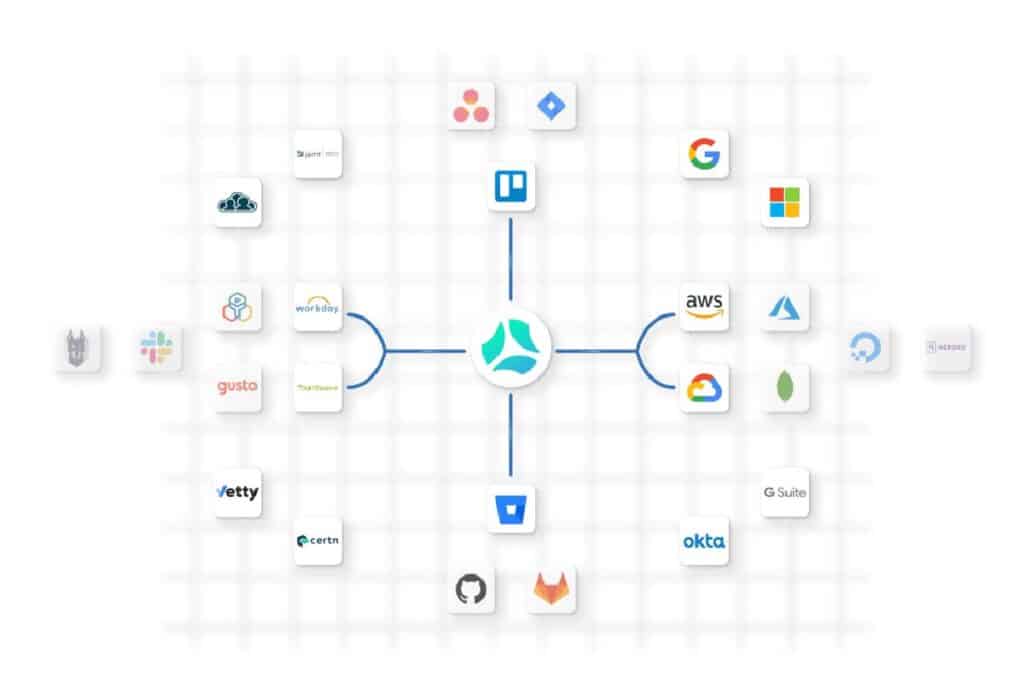
For expert assistance in compliance with cybersecurity regulations such as 23 NYCRR 500 and fortifying IBM i security, Scrut offers comprehensive solutions and resources.
Best practices for compliance
Despite the challenges associated with NYDFS cybersecurity regulation, financial institutions can adopt several best practices to facilitate compliance and strengthen their cybersecurity posture:
- Conduct comprehensive risk assessments to identify and prioritize cybersecurity risks.
- Implement robust access controls, encryption protocols, and data protection measures.
- Develop and test incident response plans to ensure readiness to detect, respond to, and recover from cybersecurity incidents.
- Enhance employee training and awareness programs to promote a culture of cybersecurity awareness and vigilance.
- Establish effective vendor risk management processes to assess, monitor, and mitigate third-party risks.
- Invest in modernizing legacy systems and infrastructure to address security vulnerabilities and improve resilience against cyber threats.
Wrapping up
In conclusion, achieving compliance with NYDFS encryption regulations is not just about meeting legal requirements; it’s about safeguarding sensitive financial data and bolstering cybersecurity measures.
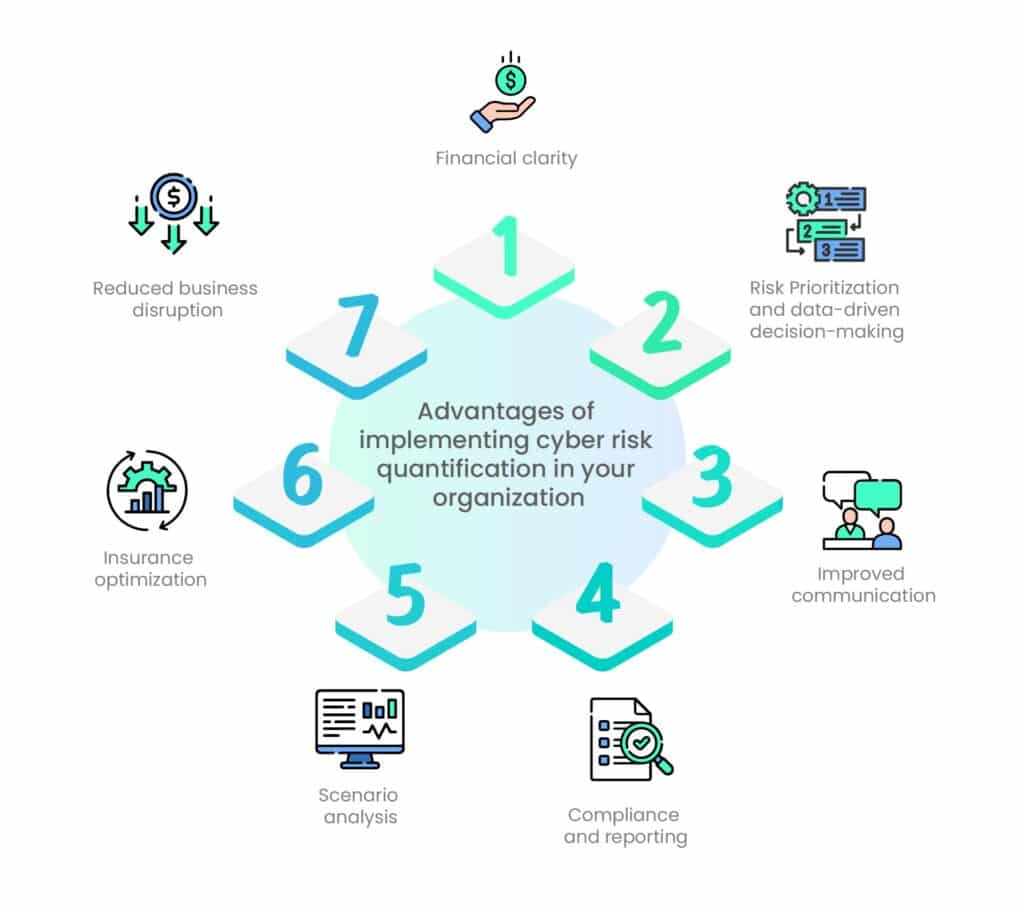
By following the 7-step approach outlined in this guide, financial institutions can establish a robust encryption framework that protects against data breaches and ensures regulatory adherence.
Act now to safeguard sensitive financial data and bolster cybersecurity. Evaluate, prioritize, and implement encryption measures today with Scrut to protect your organization from potential threats. Secure your data. Protect your business. Choose Scrut.
Frequently Asked Questions
NYDFS encryption compliance refers to adhering to the encryption requirements outlined by the New York Department of Financial Services (NYDFS) to protect sensitive financial data. It is crucial for financial institutions to comply with these regulations to mitigate the risk of data breaches, safeguard customer information, and maintain trust and integrity in the financial system.
NYDFS encryption requirements typically apply to sensitive financial data, including personally identifiable information (PII), account numbers, social security numbers, and other confidential information that could be exploited if exposed.
A comprehensive NYDFS encryption compliance program typically includes encryption of data at rest and in transit, implementation of strong access controls, regular security assessments and audits, employee training on data security best practices, incident response protocols, and documentation of encryption policies and procedures.
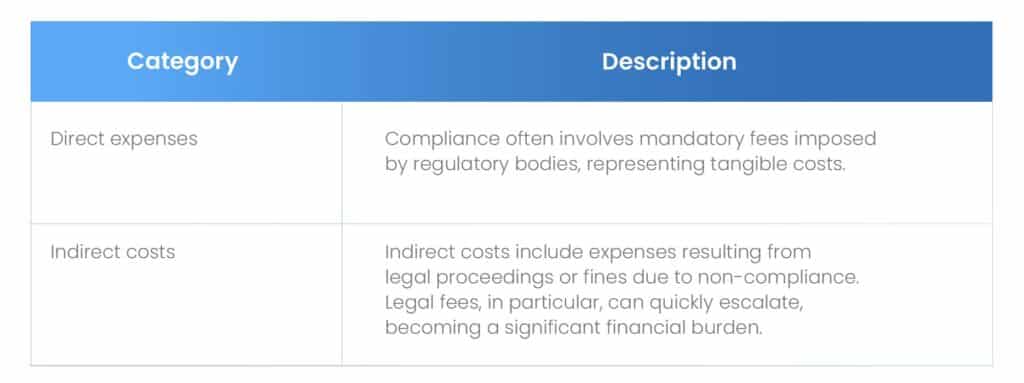
Non-compliance with NYDFS encryption regulations can result in severe penalties, including fines and sanctions imposed by the NYDFS. Additionally, data breaches resulting from inadequate encryption measures can lead to reputational damage, loss of customer trust, and legal liabilities for financial institutions.
Financial institutions can ensure compliance with NYDFS encryption requirements by conducting a comprehensive risk assessment to identify sensitive data, implementing robust encryption solutions to protect data both at rest and in transit, regularly monitoring and auditing encryption controls, maintaining documentation of encryption policies and procedures, and staying updated with evolving regulatory requirements through ongoing training and compliance initiatives.