In today’s digital age, cookies have become an integral part of online user experiences, allowing websites to remember user preferences, track activities, and provide personalized content. However, with the growing concerns over data privacy and protection, the General Data Protection Regulation (GDPR) was introduced to safeguard individuals’ personal data within the European Union (EU) and the European Economic Area (EEA).
Obtaining valid and compliant cookie consent is of utmost importance to protect users’ privacy and uphold their data protection rights. With the implementation of the GDPR, individuals have greater control over their personal data. Cookie consent ensures transparency and empowers users to make informed choices about how their data is collected, processed, and used. Failing to obtain valid consent may lead to severe legal consequences, such as hefty fines and reputational damage, as well as erode users’ trust in a website or organization.
By prioritizing valid and compliant cookie consent, businesses demonstrate their commitment to respecting user privacy, fostering trust, and maintaining a positive online reputation in an increasingly data-sensitive world.
In this blog, we will delve into the intricacies of GDPR cookie consent requirements and explore how websites can ensure compliance while respecting user privacy.
What are cookies and why are they important?
Cookies are small text files stored on a user’s device when they visit a website. They play a crucial role in enhancing user experiences by remembering preferences and facilitating personalized content delivery. However, some cookies are designed for online tracking purposes, enabling websites to collect and process user data, such as browsing behavior and preferences. This tracking aspect raises privacy concerns, making it essential to obtain proper consent from users before using cookies, especially those used for tracking.
What is consent and what are its implications on cookies?
Under the GDPR, “consent” is defined as a specific, informed, and unambiguous indication of a user’s agreement to the processing of their personal data. It must be freely given, revocable, and separate from other terms and conditions. This definition has significant implications for cookies, as they often involve the processing of personal data.
Consent must be obtained before any non-essential cookies, including tracking cookies, are placed or accessed on a user’s device. Additionally, websites must ensure that consent mechanisms are clear, easily accessible, and require affirmative action from the user, demonstrating a proactive choice to consent to cookie usage.
What are the different types of cookies? And what is their impact on consent requirements?
There are various types of cookies, and each has a different impact on consent requirements. For example,
1. Strictly necessary cookies
These cookies are essential for the website’s basic functionality and do not require explicit GDPR cookie consent as they are exempt from GDPR requirements.
2. Functional cookies
These cookies enhance the user experience by remembering preferences, such as language settings. While GDPR cookie consent may not be necessary for the use of these cookies, transparent information about their purpose should still be provided to users.
3. Performance cookies
These cookies gather anonymous data to analyze website performance and traffic patterns. GDPR cookie consent may be required for their use, but as long as the data remains anonymized and is not used for individual profiling, obtaining consent can be less burdensome.
4. Targeting/advertising cookies
These cookies track users across websites to build profiles for targeted advertising. Given their potential impact on user privacy, explicit GDPR cookie consent is essential before deploying such cookies.
In summary, understanding the nature of cookies and their significance in online tracking is vital in light of the GDPR’s definition of consent. Different types of cookies have varying impacts on consent requirements, but regardless of the cookie type, obtaining valid and compliant consent is essential to respecting users’ data protection rights and fostering trust in the digital environment.
What is the legal basis in GDPR for processing cookies?
Typically, there are the following legal basis in GDPR for processing cookies:
1. Consent
Consent is the primary legal basis for processing cookies that involve the collection and processing of personal data. According to the GDPR, consent must be obtained before placing non-essential cookies, such as tracking and targeting cookies, on a user’s device. This GDPR cookie consent must be specific, informed, and freely given, with users being fully aware of the purposes and consequences of cookie usage.
Websites must ensure that users have the option to provide or withdraw consent without facing any negative consequences. Additionally, GDPR cookie consent should be separate from other terms and conditions and obtained through affirmative action, such as clicking an “I agree” button.
2. Other potential legal bases for cookie processing
While consent is the primary legal basis for processing cookies under GDPR, there are other potential legal bases that might apply in certain circumstances. One such legal basis is “legitimate interest.” If the data processing is necessary for the legitimate interests pursued by the website operator or a third party, and those interests do not override the rights and freedoms of the user, legitimate interest may serve as a lawful basis for processing certain cookies.
However, the use of legitimate interest as a legal basis for cookies is subject to careful assessment and requires a balancing test between the interests of the website operator and the individual’s privacy rights.
When relying on legitimate interest as a legal basis for cookie processing, the website must demonstrate a valid legitimate interest that is not overridden by the individual’s rights and freedoms. A Legitimate Interest Assessment (LIA) should be conducted to assess the necessity and proportionality of the processing.
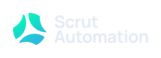
What are the key principles for GDPR-compliant cookie consent?
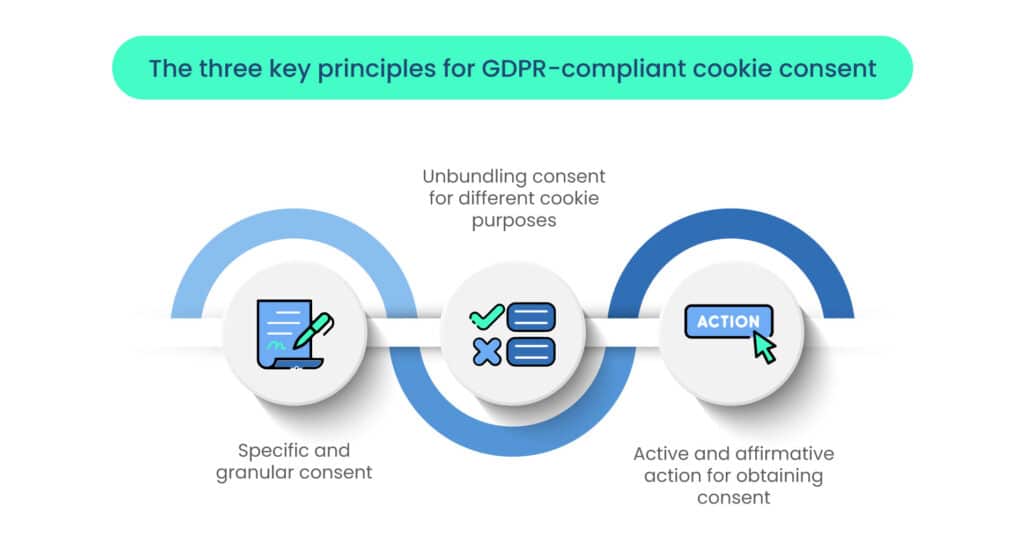
The following key principles should be considered for GDPR-compliant cookie consent:
1. Specific and granular consent
One of the fundamental principles of GDPR-compliant cookie consent is obtaining specific and granular consent from users. This means that users should have clear and detailed information about the different types of cookies used on the website and their respective purposes. Rather than using a blanket or generic consent approach, websites should provide users with a choice to consent or decline each specific category of cookies. This allows users to have more control over their data and ensures that they are fully informed about the implications of their consent.
2. Unbundling consent for different cookie purposes
To achieve transparency and compliance, GDPR cookie consent for different cookie purposes should be unbundled. This means that websites should not bundle consent for essential and non-essential cookies together or combine consent for various purposes like analytics, advertising, and social media tracking. Instead, each purpose should be presented separately, and users should be able to give or withhold consent for each purpose individually. Unbundling consent helps users make more informed decisions and avoids forcing them into accepting cookies they might not want or need.
3. Active and affirmative action for obtaining consent
GDPR-compliant cookie consent requires that users take active and affirmative actions to grant consent. This means that pre-ticked boxes or any form of passive consent (such as implied consent from continued use of the website) are not acceptable. Websites should use clear and user-friendly mechanisms, such as checkboxes or sliders, that require users to actively select their choices. Additionally, obtaining consent should be a separate and distinct step from other actions on the website, ensuring that users are not pressured into giving consent.
What are the requirements for cookie consent mechanisms?
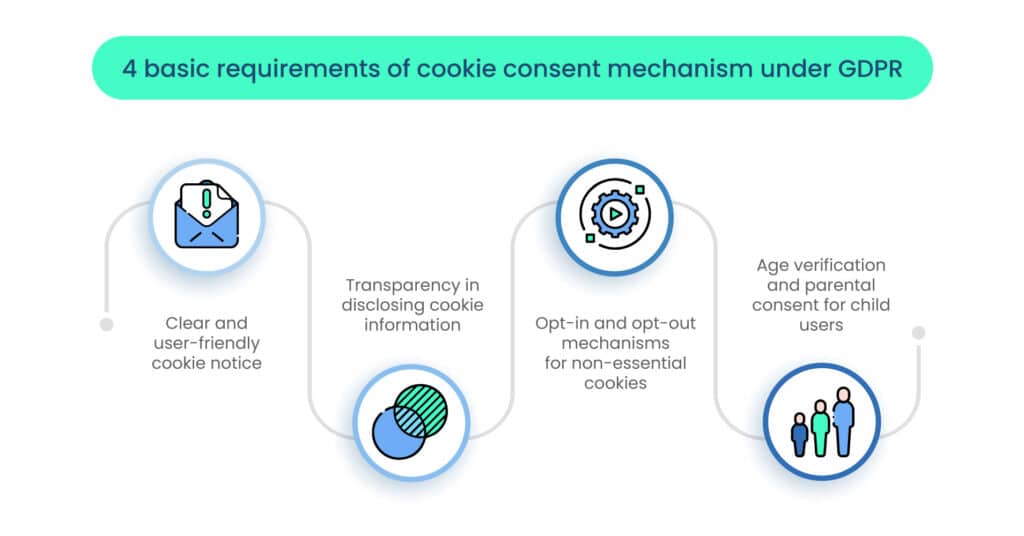
GDPR has certain requirements for cookie consent, as shown below:
1. Clear and user-friendly cookie notice
A GDPR-compliant cookie consent mechanism should include a clear and easily accessible cookie notice that informs users about the use of cookies on the website. The notice should be prominently displayed, either as a pop-up or a banner, and should provide concise yet comprehensive information about the types of cookies used, their purposes, and how long they will be stored on the user’s device. The language used in the notice should be plain and understandable to the average user, avoiding complex legal jargon.
2. Transparency in disclosing cookie information
Transparency is a fundamental aspect of obtaining valid GDPR cookie consent. Websites should disclose detailed information about each cookie’s purpose, the data it collects, and who it is shared with. This information should be provided in a cookie policy or a dedicated section within the privacy policy, easily accessible from the cookie notice. Users must be fully informed of the consequences of their consent or refusal, ensuring they can make well-informed decisions about their data.
3. Opt-in and opt-out mechanisms for non-essential cookies
For non-essential cookies, including those used for analytics, advertising, and social media tracking, websites must implement opt-in and opt-out mechanisms. By default, these cookies should be disabled until the user provides explicit consent. Opt-in mechanisms require affirmative action from the user to grant consent, such as checking a box or clicking an “I agree” button. Additionally, users should have the option to withdraw their consent and opt out of these cookies at any time, with an easy-to-use and accessible process for managing their preferences.
4. Age verification and parental consent for child users
If the website targets or knowingly collects personal data from users under the age of consent (usually 16 in most EU member states, but it can be as low as 13 in some countries), age verification and parental consent mechanisms are required. Websites must take reasonable steps to verify the user’s age and obtain verifiable parental consent before processing the personal data of children. This ensures that children’s data is handled with special care and protection in compliance with the GDPR’s specific requirements for child data privacy.
What are the requirements for consent lifespan and withdrawal?
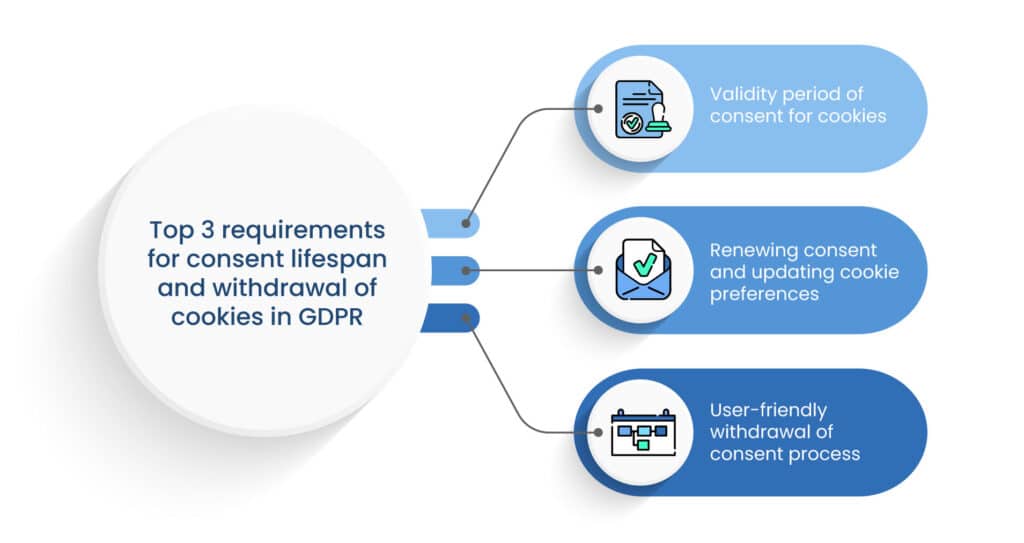
There are certain requirements for consent lifespan and withdrawal of the cookies in GDPR. These are as follows:
1. Validity period of consent for cookies
Under the GDPR, the validity period of consent for cookies should be limited and not indefinite. The specific duration of the consent validity will depend on the context and the purpose for which the GDPR cookie consent was obtained. As a best practice, websites should regularly review and reassess the need for the cookies and their associated consent to ensure that it remains relevant and up-to-date. Consent for cookies should be regularly renewed to keep it valid and in compliance with the GDPR’s principle of accountability.
2. Renewing consent and updating cookie preferences
To maintain compliance with the GDPR, websites must give users the opportunity to renew their consent periodically. This means that after the consent’s validity period has expired, websites should prompt users to review and update their cookie preferences. Additionally, if there are any significant changes to the cookie usage or purposes, websites should seek renewed consent from users before implementing those changes. This updating process should be user-friendly, clear, and easily accessible, allowing users to modify their preferences easily.
3. User-friendly withdrawal of consent process
The GDPR emphasizes that users have the right to withdraw their consent as easily as they gave it. Websites must provide a straightforward and user-friendly process for users to withdraw their consent for cookies at any time. The withdrawal process should be clearly communicated in the cookie notice or cookie policy, and users should be informed about the consequences of withdrawing their consent. Once consent is withdrawn, websites must promptly stop processing cookies for which consent has been withdrawn and delete or anonymize any associated data.
How to handle cookie consent for third-party cookies?

Third-party cookies are extremely important in today’s interwoven space. Let’s look at some of the essential features of handling third-party cookies.
1. Responsibility and liability considerations for third-party cookies
Websites that use third-party cookies should be aware that they share the responsibility and liability for the data collected through these cookies. As per the GDPR, both the website owner (first-party) and the third-party cookie provider are considered data controllers for the personal data collected by the cookies. It is essential for website owners to carefully select and vet their third-party vendors to ensure they comply with data protection regulations and handle user data responsibly. Even if the website does not directly control the third-party cookies, it is still responsible for obtaining valid consent from users for the use of those cookies.
2. Ensuring third-party cookie compliance through contractual agreements
To mitigate risks associated with third-party cookies, website owners should establish contractual agreements with third-party vendors. These agreements, commonly known as Data Processing Agreements (DPAs) or Data Sharing Agreements, should clearly outline the roles and responsibilities of each party regarding data processing and user consent.
The agreement should also include provisions ensuring that the third-party vendor complies with the GDPR and other relevant data protection laws. Additionally, the DPA should specify that the third-party vendor will only process personal data in accordance with the website owner’s instructions and for agreed-upon purposes.
3. User awareness and transparency regarding third-party cookies
Transparency is crucial when it comes to third-party cookies. Website owners must inform users about the presence of third-party cookies on their site, the purposes for which these cookies are used, and the identity of the third-party vendors involved.
This information should be provided in the cookie notice or cookie policy, along with links to the privacy policies of the third-party vendors. Users should be aware of how their data is shared and processed by these third parties and have the option to opt out if they choose.
4. Implementing robust cookie consent management
To ensure compliance with third-party cookie requirements, website owners should invest in a robust cookie consent management platform (CMP). A good CMP allows users to easily manage their consent preferences, including opting in or out of specific third-party cookies.
The CMP should offer granular controls, allowing users to choose which third-party cookies they wish to accept or reject. It should also provide clear and concise information about each third-party cookie’s purpose and the data processing involved.
What are the benefits of using CMPs to streamline your compliance efforts?

Following are the advantages of using a CMP to streamline your compliance efforts
1. Simplified implementation
CMPs offer pre-built solutions that simplify the process of integrating GDPR cookie consent mechanisms into websites. They provide ready-to-use templates and code snippets, reducing the technical burden on website owners.
2. Customizable consent options
CMPs allow website owners to customize the cookie consent banner or pop-up to align with their branding and design preferences. This ensures a seamless and consistent user experience.
3. Granular consent management
CMPs enable granular consent options, allowing users to choose which types of cookies they want to enable or disable. This level of control ensures compliance with GDPR’s requirements for specific and informed consent.
4. User-friendly interface
CMPs are designed with user-friendliness in mind, making it easy for visitors to understand and manage their cookie preferences. Clear language and intuitive interfaces enhance user trust and engagement.
5. Automatic consent renewal
Many CMPs offer consent renewal features, prompting users to review and update their preferences periodically. This helps websites maintain compliance by ensuring consent remains valid and up-to-date.
6. Reporting and analytics
CMPs often provide insights and analytics on user consent preferences, allowing website owners to track and monitor the effectiveness of their cookie consent strategy.
7. Vendor management
CMPs assist in managing third-party vendors’ consent and ensure compliance with contractual agreements, minimizing the risk associated with third-party cookies.
How to evaluate the right CMP for your website?
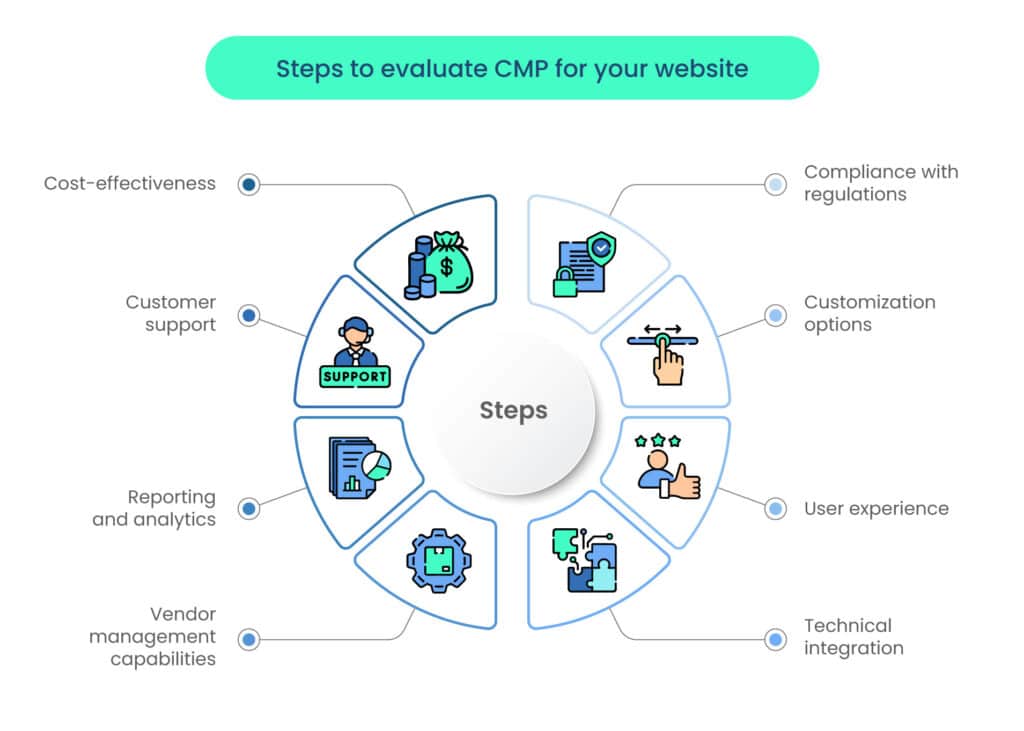
An organization should check the following before investing in CMP for their website:
1. Compliance with regulations
Ensure that the CMP is designed to comply with relevant data protection regulations, such as the GDPR. It should allow for specific consent options and support user rights, including the right to withdraw consent.
2. Customization options
Look for a CMP that provides flexibility in design and branding customization to align with your website’s look and feel.
3. User experience
Opt for a CMP that offers a user-friendly interface, clear language, and an intuitive consent management process to enhance user experience and engagement.
4. Technical integration
Choose a CMP that seamlessly integrates with your website’s existing infrastructure and is compatible with various Content Management Systems (CMS) and platforms.
5. Vendor management capabilities
If your website uses third-party cookies, ensure that the CMP supports proper vendor management and facilitates compliance with data processing agreements.
6. Reporting and analytics
Consider a CMP that provides useful insights and analytics on user consent preferences, helping you assess the effectiveness of your GDPR cookie consent strategy.
7. Customer support
Evaluate the level of customer support provided by the CMP provider, as prompt assistance can be crucial during implementation and ongoing maintenance.
8. Cost-effectiveness
Compare the pricing and features of different CMPs to find a solution that meets your needs while fitting within your budget.
What are the best practices in cookie management for assuring compliance with GDPR?
Some of the best practices for assuring effective cookie management are as follows:
1. Conducting cookie audits and assessment of data processing activities:
Regularly conduct comprehensive cookie audits to identify all cookies used on your website and their specific purposes. Assess the legal basis for processing each type of cookie and ensure that valid GDPR cookie consent is obtained where necessary. Document the findings and maintain a record of the cookies in use. Additionally, conduct periodic assessments of your data processing activities to ensure that you are complying with the GDPR’s principles of data minimization, purpose limitation, and data accuracy.
2. Implementing technical measures for cookie consent management:
Invest in a robust and user-friendly cookie consent management platform (CMP) to effectively manage user consent and cookie preferences. The CMP should allow granular consent options, easy withdrawal of consent, and clear communication of the purposes of each cookie.
Ensure that the CMP integrates seamlessly with your website and provides transparent information about cookie usage. Implement technical measures to block the placement of non-essential cookies until users have provided their consent, and regularly update the CMP to align with changes in cookie usage and legal requirements.
3. Training employees and staff on GDPR and cookie consent obligations:
Educate all employees and staff who handle personal data, including those involved in website development, marketing, and customer support, about the GDPR’s requirements and the importance of cookie GDPR consent compliance.
Provide training on best practices for obtaining and managing cookie consent, ensuring that employees understand the significance of user privacy and data protection. Regularly update training materials to reflect changes in regulations or your organization’s data processing practices.
What are the consequences of non-compliance with GDPR?
Non-compliance with GDPR can result in the following:
1. GDPR fines and penalties for non-compliant cookie practices
Non-compliance with the GDPR’s cookie consent requirements can lead to severe financial penalties. The GDPR empowers data protection authorities to impose fines of up to 4% of the organization’s global annual turnover or €20 million (whichever is higher) for serious violations. This includes instances where cookie consent is not appropriately obtained, recorded, or managed. Organizations must understand that neglecting cookie compliance can result in significant financial losses and reputational damage.
2. Reputational damage and loss of trust with users
Beyond financial penalties, non-compliance can have long-term repercussions on an organization’s reputation and user trust. News of non-compliant cookie practices and data mishandling can spread quickly, leading to public backlash, negative media coverage, and a loss of customer trust. Rebuilding trust and recovering from reputational damage can be time-consuming and costly. By prioritizing GDPR cookie consent compliance and demonstrating a commitment to user privacy, organizations can protect their reputation and foster a positive relationship with their users.
Conclusion
In today’s digital era, GDPR cookie consent is crucial for protecting user privacy and building trust. Obtaining valid and compliant consent empowers users to control their data, ensuring transparency in data processing. Non-compliance may lead to severe fines and reputational damage. Prioritizing cookie consent demonstrates a commitment to user privacy, fostering positive online relationships. Implementing a robust CMP, conducting audits, and providing employee training are essential for GDPR compliance. By respecting user privacy and adhering to GDPR requirements, businesses can navigate data protection responsibly.
FAQs
The primary legal basis is consent. Consent must be specific, informed, and freely given for non-essential cookies, especially tracking and targeting cookies. Legitimate interest might also serve as a basis in certain cases, but it requires careful assessment and a balance between interests and privacy rights.
GDPR-compliant cookie consent involves specific, granular consent; unbundling consent for different cookie purposes; and obtaining active and affirmative action for consent.
Consent should have a limited validity period and must be renewed periodically. Users should have the option to update their preferences easily and withdraw consent at any time, with a user-friendly process.