In the digital age, where data flows freely and information is a valuable currency, safeguarding personal privacy has become paramount. This need gave rise to the General Data Protection Regulation (GDPR), a comprehensive legal framework designed to protect the fundamental rights and freedoms of individuals in relation to their personal data. Enforced on May 25, 2018, the GDPR revolutionized data protection practices globally and reshaped the way businesses handle personal data.
The GDPR is a regulation enacted by the European Union (EU) with the primary goal of harmonizing data protection laws across EU member states while granting individuals greater control over their personal data. Who does GDPR apply to? GDPR replaces the outdated Data Protection Directive of 1995 and introduces a unified set of rules applicable to all member states, eliminating the need for country-specific regulations.
Under the GDPR, personal data encompasses any information related to an identified or identifiable natural person. This includes names, email addresses, phone numbers, IP addresses, and even more sensitive data like health information or religious beliefs.
This GDPR Compliance 101 guide delves into core GDPR principles, compliance steps, and ongoing vigilance. Whether you’re a business owner, data officer, or individual, this guide equips you to navigate GDPR’s complexities effectively.
Understanding GDPR basics
The GDPR addresses the way organizations collect, process, store, and handle personal data. Its primary aim is to give individuals greater control over their personal information while harmonizing data protection laws across the EU. The regulation sets forth stringent requirements for businesses and organizations to ensure the lawful and responsible treatment of personal data.
Key components of GDPR
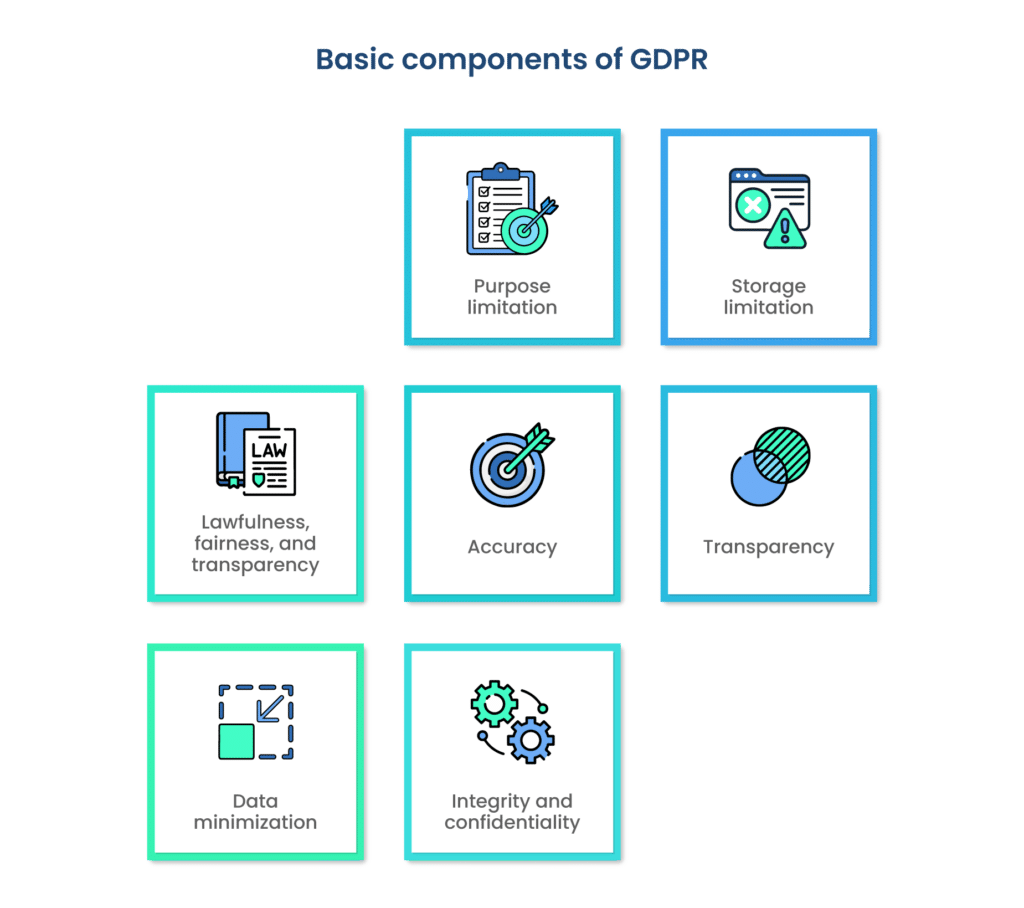
The GDPR act is based on the following key components:
1. Lawfulness, fairness, and transparency
Data processing must have a legal basis, be conducted fairly, and individuals must be informed about how their data is being processed.
2. Purpose limitation
Data can only be collected for specific, explicit, and legitimate purposes. It can’t be used for purposes that are incompatible with those originally stated.
3. Data minimization
Organizations should only collect and retain the minimum amount of personal data necessary to achieve their specified purposes.
4. Accuracy
Data must be accurate and kept up to date. Inaccurate data should be corrected or erased without delay.
5. Storage limitation
Personal data should be kept in a form that allows identification for no longer than is necessary for the purposes of processing.
6. Integrity and confidentiality
Data must be processed securely and protected against unauthorized or unlawful processing, as well as against accidental loss, destruction, or damage.
7. Transparency
Organizations must provide clear and easily understandable information to individuals about how their data will be used.
Definition of important terms
Data controller
An entity that determines the purposes and means of processing personal data. Controllers bear primary responsibility for ensuring GDPR compliance.
Data processor
An entity that processes personal data on behalf of the data controller. Processors are subject to certain GDPR obligations and must follow the controller’s instructions.
Data subject
The individual to whom the personal data belongs.
Personal data
Any information that relates to an identified or identifiable individual. This can include names, addresses, email IDs, IP addresses, etc.
Sensitive data
Special categories of personal data, such as racial or ethnic origin, political opinions, health information, religious beliefs, etc.
These foundational concepts, principles, and definitions underpin the GDPR’s framework. By adhering to these standards, organizations ensure the protection of individuals’ privacy and data rights in today’s interconnected digital landscape.
Principles of GDPR compliance
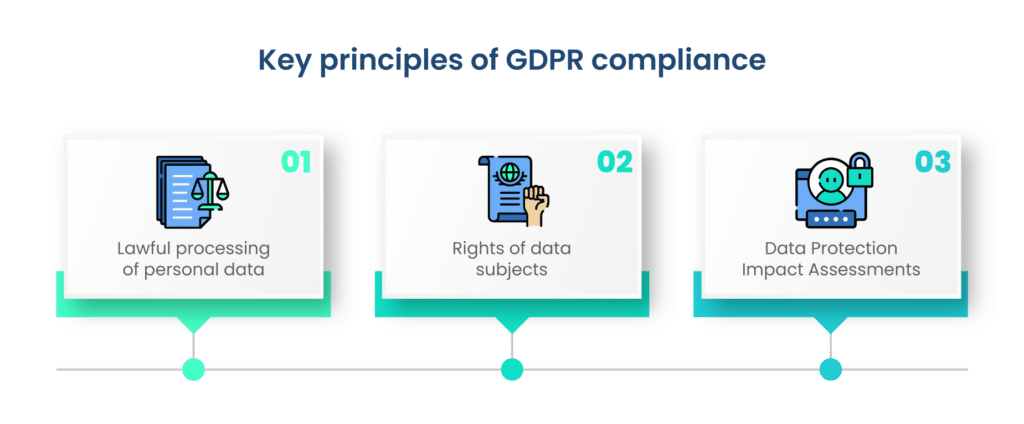
Complying with the General Data Protection Regulation (GDPR) involves adhering to a set of fundamental principles that ensure the lawful, fair, and responsible processing of personal data. These principles guide organizations in their efforts to protect individuals’ privacy rights and maintain data security.
A. Lawful processing of personal data
Processing personal data under the GDPR must have a legal basis. This means that data processing activities should fall under one of the following conditions:
- Consent: Individuals give explicit permission for their data to be processed for specific purposes.
- Contract performance: Processing is necessary to fulfill a contract with the data subject.
- Legal obligation: Processing is required to comply with a legal obligation, such as tax or regulatory requirements.
- Vital interests: Processing is necessary to protect someone’s life.
- Public task: Processing is carried out in the public interest or official authority.
- Legitimate interests: Organizations can process data if they have a legitimate interest, provided it doesn’t override the individual’s rights and interests.
B. Rights of data subjects
The GDPR grants data subjects a range of rights to ensure they have control over their personal data:
- Right to access: Individuals can request access to their personal data held by an organization.
- Right to rectification: Data subjects can request corrections to inaccurate or incomplete data.
- Right to erasure: Also known as the “right to be forgotten,” individuals can request the deletion of their data under certain circumstances.
- Right to restriction of processing: Individuals can request limitations on the processing of their data.
- Right to data portability: Data subjects can receive their personal data in a commonly used format and transfer it to another organization.
- Right to object: Individuals can object to processing, especially for direct marketing or legitimate interest purposes.
- Rights related to automated decision-making: Individuals have the right to challenge decisions made solely by automated means.
C. Data Protection Impact Assessments (DPIAs)
A Data Protection Impact Assessment (DPIA) is a systematic process to assess and mitigate data protection risks associated with specific processing activities, particularly those involving high risks to individuals’ rights and freedoms. Organizations must conduct DPIAs for such activities and involve data protection authorities if necessary.
Adhering to these principles forms the bedrock of GDPR compliance. By ensuring the lawful processing of data, respecting data subjects’ rights, and conducting assessments to mitigate risks, organizations uphold the GDPR’s overarching goal of safeguarding personal data and privacy.
Implementing GDPR compliance
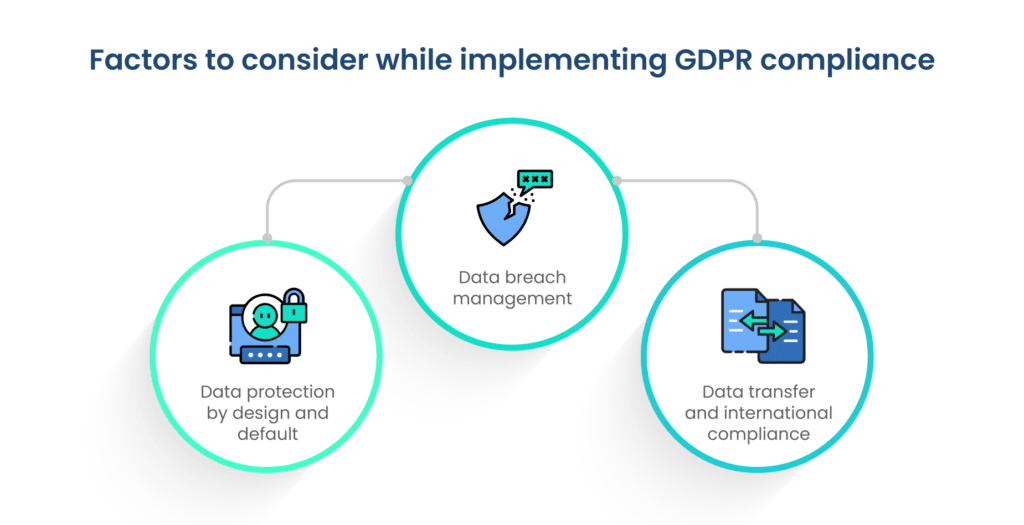
An organization can take the following steps to implement GDPR compliance.
1. Data protection by design and default
Integration of data protection into processes and systems
- Incorporate data protection considerations from the outset when designing new processes, systems, and services.
- Apply privacy-enhancing techniques to minimize data exposure and risks.
Minimizing data collection, retention, and processing
- Collect only the necessary data for specified purposes, avoiding unnecessary data gathering.
- Set clear data retention periods and delete data once its purpose has been fulfilled.
Ensuring data security and privacy through technical and organizational measures
- Implement robust security measures to protect data against unauthorized access, breaches, and cyber threats.
- Establish clear policies and procedures for data handling and train employees on best practices.
2. Data breach management
Definition of a data breach and its potential consequences
- Define what constitutes a data breach (unauthorized access, disclosure, loss, alteration, destruction of personal data) and assess potential impacts.
- Recognize that data breaches can lead to financial penalties, reputational damage, and legal actions.
Reporting obligations and timeline in case of a breach
- Report breaches to the relevant supervisory authority within 72 hours of becoming aware of the breach, explaining the nature and scope of the incident.
- Notify affected data subjects if the breach poses a high risk to their rights and freedoms.
Developing an effective data breach response plan
- Establish a clear and structured plan for addressing data breaches, involving relevant stakeholders and communication channels.
- Assign roles and responsibilities to handle breach detection, assessment, mitigation, and communication.
3. Data transfer and international compliance
Transferring data outside the EU/EEA: Requirements and safeguards
- Prioritize data transfers within the EU/EEA to ensure compliance with GDPR.
- If transferring data outside these regions, ensure it’s to countries with an adequate level of data protection or implement additional safeguards.
Adequacy decisions, standard contractual clauses, binding corporate rules
- Check for EU Commission’s adequacy decisions that recognize certain countries as having adequate data protection laws.
- Use standard contractual clauses approved by EU authorities when transferring data to countries without adequacy status.
- For multinational corporations, consider implementing Binding Corporate Rules to ensure consistent data protection across the organization.
By following these implementation strategies, organizations can align their practices with GDPR requirements, thereby safeguarding individuals’ personal data, preparing for potential breaches, and ensuring compliant international data transfers. These efforts foster a culture of data protection and privacy that resonates with the GDPR’s core principles.
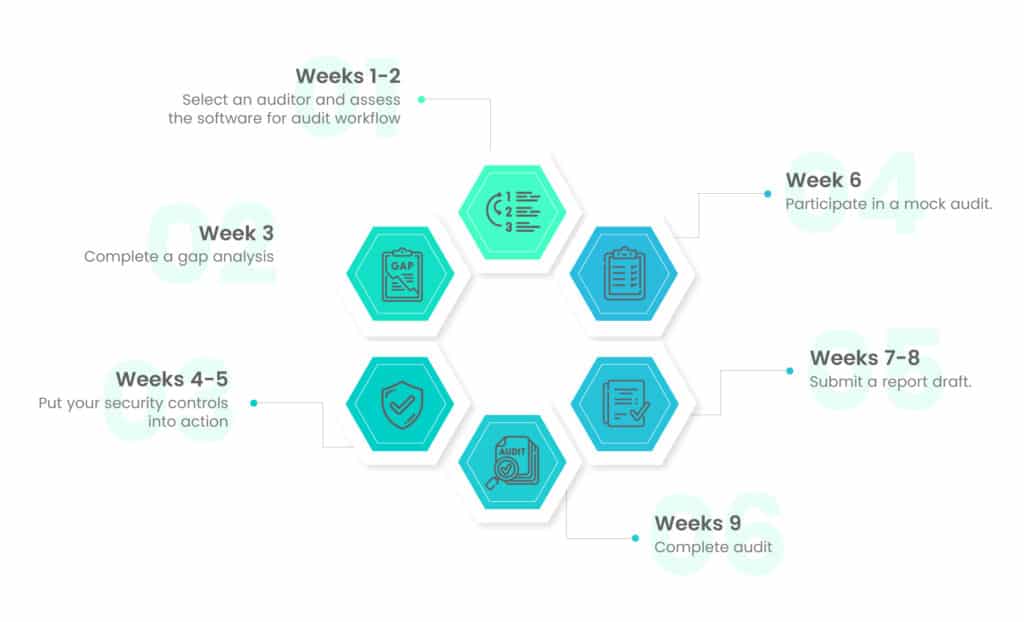
Steps to achieve GDPR compliance
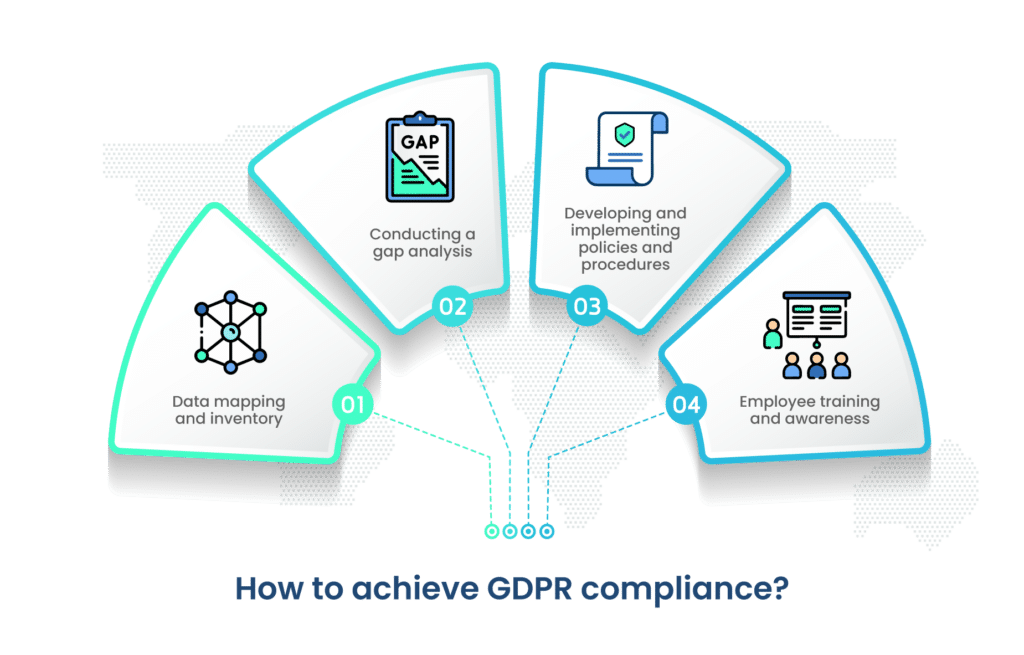
Follow the steps given below to achieve GDPR compliance
A. Data mapping and inventory
1. Identifying and categorizing personal data
- Audit all data processing activities within your organization to identify personal data types and categories.
- Categorize data based on its sensitivity and the purposes for which it’s processed.
2. Documenting data flows and storage locations
- Create visual data flow diagrams illustrating how personal data moves within your organization.
- Document where data is stored, whether in databases, cloud services, or other systems.
B. Conducting a gap analysis
1. Evaluating current practices against GDPR requirements
- Compare your organization’s data processing activities with GDPR’s principles and requirements.
- Assess if your processes adhere to lawful processing, data subject rights, security, and other obligations.
2. Identifying areas of non-compliance and potential risks
- Identify gaps between current practices and GDPR standards, focusing on areas with the highest risks.
- Pinpoint vulnerabilities that could lead to breaches or non-compliance.
C. Developing and implementing policies and procedures
1. Creating a comprehensive data protection policy
- Craft a clear and concise data protection policy that outlines your organization’s commitment to GDPR compliance.
- Include the principles, rights, responsibilities, and procedures that align with GDPR standards.
2. Establishing processes for handling data subject requests, breaches, and risk assessments
- Develop processes for efficiently handling data subject access requests, rectification requests, and other rights.
- Create a data breach response plan that outlines steps to take in the event of a breach, including notification procedures.
- Implement a risk assessment process to proactively identify and mitigate potential data protection risks.
D. Employee training and awareness
1. Importance of educating employees about GDPR principles
- Educate employees about the significance of GDPR compliance and how it protects individuals’ rights.
- Highlight the potential consequences of non-compliance, including fines and reputational damage.
2. Providing training on data protection practices and compliance measures
- Offer training sessions to employees on data protection best practices, including secure data handling, encryption, and access controls.
- Ensure that employees understand their roles in GDPR compliance and know how to respond to data subjects’ requests.
By following these steps, organizations can systematically work towards GDPR compliance. Data mapping, gap analysis, policy development, and employee education collectively create a culture of data protection, enabling organizations to handle personal data responsibly and in accordance with GDPR’s principles. A GDPR software capable of all these functions should be employed for easier implementation.
Maintaining ongoing compliance
Getting a GDPR certification once is not enough. An organization needs to maintain ongoing compliance to meet GDPR requirements.
A. Regular auditing and review
1. Setting up a schedule for internal GDPR audits and reviews
- Establish a timetable for conducting regular GDPR audits to assess ongoing compliance.
- Assign responsibilities to designated individuals or teams to ensure comprehensive reviews.
2. Ensuring continued alignment with GDPR requirements
- Evaluate data processing activities, policies, and procedures against any changes in the organization’s processes or the regulatory landscape.
- Identify and address any areas of non-compliance or emerging risks.
B. Keeping up with regulatory changes
1. Staying informed about updates and amendments to GDPR
- Stay connected to reliable sources of information such as official EU publications, industry associations, and legal experts.
- Monitor regulatory updates to remain current on changes to GDPR provisions or interpretations.
2. Adapting compliance practices accordingly
- Regularly assess how any updates or amendments to GDPR impact your organization’s data processing practices.
- Modify policies, procedures, and practices to align with new requirements while maintaining effective data protection.
Maintaining GDPR compliance requires ongoing dedication and vigilance. By incorporating regular GDPR audits, staying abreast of regulatory developments, and adapting practices to evolving requirements, organizations can ensure that their data protection measures remain robust and responsive. This commitment not only safeguards individuals’ privacy rights but also supports the organization’s reputation and trustworthiness in the eyes of customers and stakeholders.
Conclusion
In an era dominated by digital interactions and data-driven operations, the General Data Protection Regulation (GDPR) stands as a cornerstone of modern data protection and privacy rights. As we’ve explored in this GDPR Compliance 101 guide, GDPR compliance is not merely a legal obligation but a fundamental commitment to ethical data handling and individual rights.
From understanding the core principles of lawful data processing, transparency, and security, to implementing comprehensive measures like data protection by design, breach management, and international data transfers, the journey to GDPR compliance demands dedication and meticulous attention. It’s about creating a culture within organizations that respects personal privacy, values responsible data practices, and prioritizes the security and trust of data subjects.
Yet, the story doesn’t end with achieving compliance. The true essence lies in maintaining ongoing vigilance through regular audits, adapting to regulatory changes, and fostering a continuous commitment to best practices. GDPR compliance is an ongoing journey of growth and evolution, one that reflects an organization’s dedication to protecting not only data but also its reputation and credibility.
As businesses, data controllers, processors, and individuals, embracing GDPR’s principles is a collective effort towards a safer, more secure, and privacy-respecting digital landscape. By understanding, implementing, and continuously enhancing GDPR compliance, we contribute to a world where personal data is treated with the respect and protection it deserves.
Frequently asked questions (FAQs)
GDPR enables each country’s data protection authorities to impose sanctions and fines on firms that break the law. The maximum GDPR fines can range up to €20 million or 4% of worldwide sales. Aside from fines, data protection authorities may also impose restrictions on data processing or public reprimands.
GDPR applies to the processing of personal data in the EU/EEA by controllers or businesses and processors which are the entities that process the data for the corporations, regardless of whether the processing takes place in the EU/EEA.
A Data Protection Officer (DPO) is a member of your organization who is in charge of comprehending the GDPR legislation and maintaining compliance with it. The primary point of contact for the data protection authorities is the DPO. The DPO must be someone who has an understanding of both information technology and law.
Personal data is any information relating to a recognized or identifiable living human being, while sensitive personal data is any distinct personal data that is more sensitive in nature and can cause harm to an individual if released involuntarily.
All 27 of the EU countries are subject to GDPR compliance. Iceland, Norway, and Liechtenstein, all nations that are a part of the EEA, are also considered to be GDPR countries.
The General Data Protection Regulation (GDPR) is a comprehensive data protection framework enacted by the European Union (EU) to safeguard individuals’ personal data rights. It governs how organizations collect, process, store, and handle personal data.
A data breach is a security incident that leads to the accidental or unlawful destruction, loss, alteration, unauthorized disclosure, or access to personal data. GDPR requires organizations to report significant data breaches to relevant authorities and affected individuals.
Organizations can maintain ongoing compliance by conducting regular internal audits and reviews, staying informed about regulatory changes, and adapting their practices to align with evolving GDPR requirements.
Scrut Automation is a smart and radically simple governance, risk, and compliance automation platform for growing startups and mid-market enterprises. With Scrut, compliance teams can reduce ~70% of their manual effort in continuously maintaining compliance towards SOC 2, ISO 27001, GDPR, PCI DSS, HIPAA, and CCPA. Schedule your demo today to see how it works.